This section describes the procedure for installing ESA appliances on cloud platforms, such as, Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure.
This is the multi-page printable view of this section. Click here to print.
Installing Protegrity Appliances on Cloud Platforms
- 1: Installing ESA on Amazon Web Services (AWS)
- 1.1: Verifying Prerequisites
- 1.2: Obtaining the AMI
- 1.3: Loading the Protegrity Appliance from an Amazon Machine Image (AMI)
- 1.3.1: Creating an ESA Instance from the AMI
- 1.3.2: Configuring the Virtual Private Cloud (VPC)
- 1.3.3: Adding a Subnet to the Virtual Private Cloud (VPC)
- 1.3.4: Finalizing the Installation of Protegrity Appliance on the Instance
- 1.4: Backing up and Restoring Data on AWS
- 1.5: Increasing Disk Space on the Appliance
- 1.6: Best Practices for Using Protegrity Appliances on AWS
- 1.7: Running the Appliance-Rotation-Tool
- 1.8: Working with Cloud-based Applications
- 1.8.1: Configuring Access for AWS Resources
- 1.8.2: Working with CloudWatch Console
- 1.8.2.1: Integrating CloudWatch with Protegrity Appliance
- 1.8.2.2: Configuring Custom Logs on AWS CloudWatch Console
- 1.8.2.3: Toggling the CloudWatch Service
- 1.8.2.4: Reloading the AWS CloudWatch Integration
- 1.8.2.5: Viewing Logs on AWS CloudWatch Console
- 1.8.2.6: Working with AWS CloudWatch Metrics
- 1.8.2.7: Viewing Metrics on AWS CloudWatch Console
- 1.8.2.8: Disabling AWS CloudWatch Integration
- 1.8.3: Working with the AWS Cloud Utility
- 1.8.3.1: Storing Backup Files on the AWS S3 Bucket
- 1.8.3.2: Set Metrics Based Alarms Using the AWS Management Console
- 1.8.4: FAQs for AWS Cloud Utility
- 1.8.5: Working with AWS Systems Manager
- 1.8.5.1: Setting up AWS Systems Manager
- 1.8.5.2: FAQs on AWS Systems Manager
- 1.8.6: Troubleshooting for the AWS Cloud Utility
- 2: Installing ESA on Google Cloud Platform (GCP)
- 2.1: Verifying Prerequisites
- 2.2: Configuring the Virtual Private Cloud (VPC)
- 2.3: Obtaining the GCP Image
- 2.4: Converting the Raw Disk to a GCP Image
- 2.5: Loading the Protegrity ESA Appliance from a GCP Image
- 2.5.1: Creating a VM Instance from an Image
- 2.5.2: Creating a VM Instance from a Disk
- 2.5.3: Accessing the Appliance
- 2.6: Finalizing the ESA Installation on the Instance
- 2.7: Deploying the Instance of the Protegrity Appliance with the Protectors
- 2.8: Backing up and Restoring Data on GCP
- 2.9: Increasing Disk Space on the Appliance
- 3: Installing Protegrity Appliances on Azure
- 3.1: Verifying Prerequisites
- 3.2: Azure Cloud Utility
- 3.3: Setting up Azure Virtual Network
- 3.4: Creating a Resource Group
- 3.5: Creating a Storage Account
- 3.6: Creating a Container
- 3.7: Obtaining the Azure BLOB
- 3.8: Creating Image from the Azure BLOB
- 3.9: Creating a VM from the Image
- 3.10: Accessing the Appliance
- 3.11: Finalizing the Installation of Protegrity Appliance on the Instance
- 3.12: Accelerated Networking
- 3.13: Backing up and Restoring VMs on Azure
- 3.14: Deploying the ESA Instance with the Protectors
1 - Installing ESA on Amazon Web Services (AWS)
Amazon Web Services (AWS) is a cloud-based computing service. It provides several services, such as, computing power through Amazon Elastic Compute Cloud (EC2), storage through Amazon Simple Storage Service (S3), and so on.
The AWS stores Amazon Machine Images (AMIs), which are templates or virtual images containing an operating system, applications, and configuration settings.
Protegrity appliances offer flexibility and can run in the following environments:
- On-premise: The ESA is installed and runs on dedicated hardware.
- Virtualized: The ESA is installed and runs on a virtual machine.
- Cloud: The ESA is installed and runs on or as part of a Cloud-based service.
Protegrity provides AMIs that contain the ESA image, running on a customized and hardened Linux distribution.
1.1 - Verifying Prerequisites
This section describes the prerequisites and tasks for installing Protegrity appliances on AWS. In addition, it describes some best practices for using the Protegrity ESA appliances on AWS effectively.
The Full OS Backup/Restore features of the Protegrity appliances is not available on the AWS platform.
Prerequisites
The following prerequisites are essential to install the Protegrity ESA appliances on AWS:
- Login URL for the AWS account
- AWS account with the authentication credentials
- Access to the My.Protegrity portal
Hardware Requirements
As the Protegrity ESA appliances are hosted and run on AWS, the hardware requirements are dependent on the configurations provided by Amazon. However, these requirements can autoscale as per customer requirements and budget.
The minimum recommendation for an ESA appliance is 8 CPU cores and 32 GB memory. On AWS, this configuration is available in the t3a.2xlarge option.
For more information about the hardware requirements of the ESA, refer to the section System Requirements.
Network Requirements
Protegrity ESA appliances on AWS are provided with an Amazon Virtual Private Cloud (VPC) networking environment. Amazon VPC enables you to access other AWS resources, such as other instances of Protegrity appliances on AWS.
You can configure the Amazon VPC by specifying its usable IP address range. You can also create and configure subnets, network gateways, and the security settings.
For more information about the Amazon VPC, refer to the Amazon VPC documentation at: http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Introduction.html.
If you are using the ESA or the DSG appliance with AWS, then ensure that the inbound and outbound ports of the appliances are configured in the Amazon Virtual Private Cloud (VPC). This ensures that they are able to interact with the other required components.
For more information about the list of inbound and outbound ports to be configured based on the ESA or the DSG, refer Open Listening Ports.
Accessing the Internet
The following points list the ways in which you can provide or limit Internet access for an ESA instance in the VPC:
- If you need to connect the ESA to the Internet, then ensure that the ESA is on the default subnet so that it uses the Internet gateway that is included in the VPC.
- If you need to allow the ESA to initiate outbound connections to, and prevent inbound connections from the Internet, then ensure that you use a Network Address Translation (NAT) device.
- If you want to block the connection of the ESA to the Internet, then ensure that the ESA is on a private subnet.
Accessing a Corporate Network
If you need to connect the ESA to a corporate network, then ensure that you use an IPSec hardware VPN connection.
1.2 - Obtaining the AMI
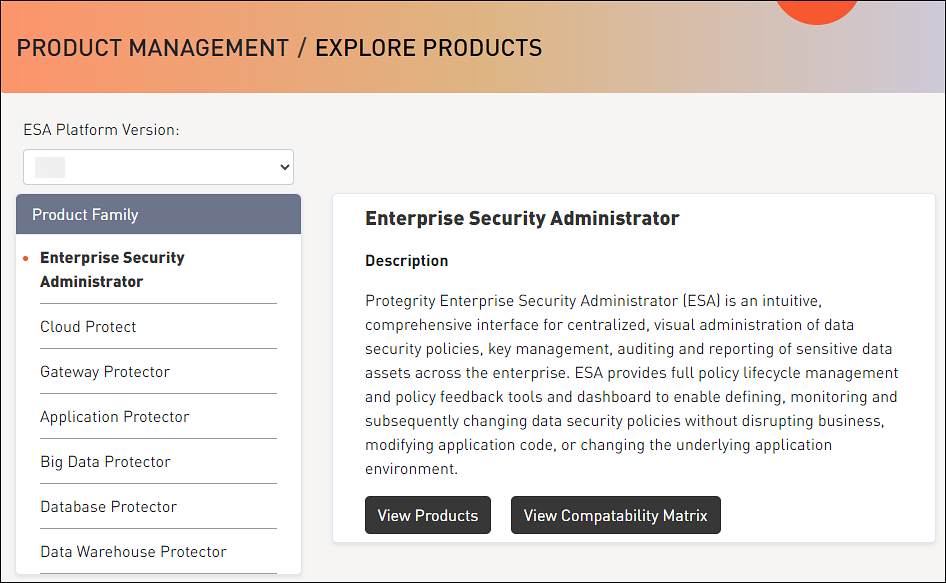
Before creating the instance on AWS, you must obtain the image from the My.Protegrity portal. On the portal, you select the required ESA version and choose AWS as the target cloud platform. You then share the product to your cloud account. The following steps describe how to share the AMI to your cloud account.
To obtain and share the AMI:
Log in to the My.Protegrity portal with your user account.
Click Product Management > Explore Products > Data Protection.
Select the required ESA Platform Version from the drop-down.
The Product Family table will update based on the selected ESA Platform Version.
The ESA Platform Versions listed in drop-down menu reflect all versions. These include versions that were either previously downloaded or shipped within the organization along with any newer versions available thereafter. Navigate to Product Management > My Product Inventory to check the list of products previously downloaded.
The images in this section consider the ESA as a reference. Ensure that you select the required image.
Select the Product Family.
The description box will populate with the Product Family details.
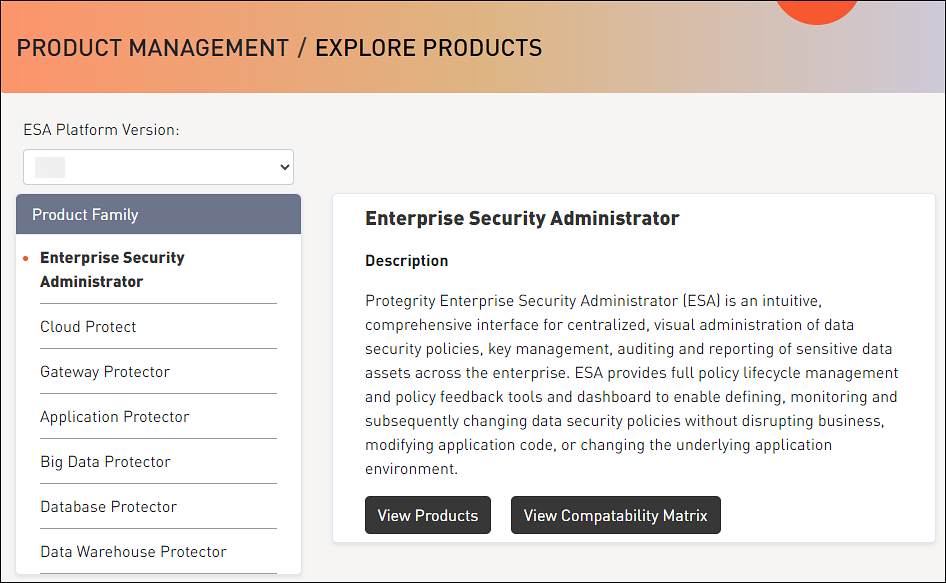
Click View Products to advance to the product listing screen.
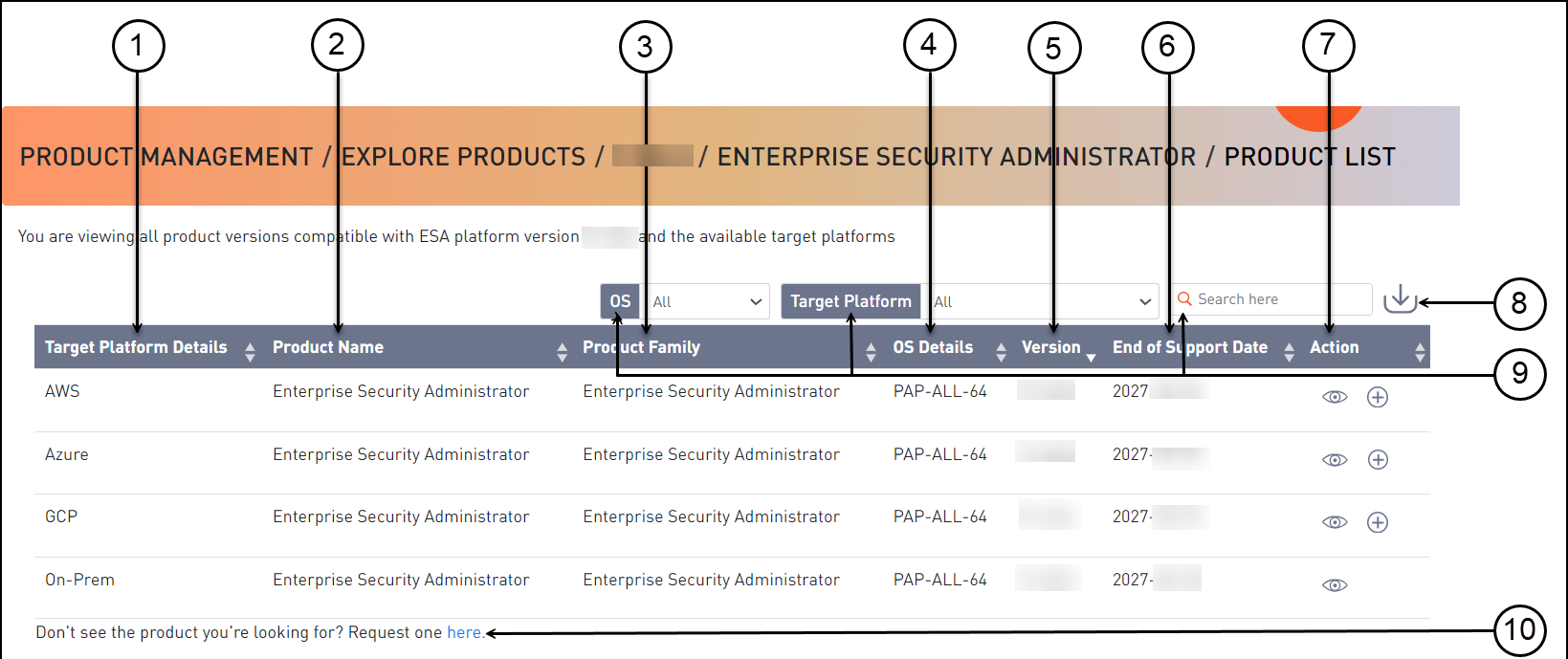
Callout Element Name Description 1 Target Platform Details Shows details about the target platform. 2 Product Name Shows the product name. 3 Product Family Shows the product family name. 4 OS Details Shows the operating system name. 5 Version Shows the product version. 6 End of Support Date Shows the final date that Protegrity will provide support for the product. 7 Action Click the View icon (  ) to open the Product Detail screen.
) to open the Product Detail screen.8 Export as CSV Downloads a .csv file with the results displayed on the screen. 9 Search Criteria Type text in the search field to specify the search filter criteria or filter the entries using the following options:- OS- Target Platform 10 Request one here Opens the Create Certification screen for a certification request. Select the AWS cloud target platform you require and click the View icon (
 ) from the Action column.
) from the Action column.The Product Detail screen appears.

Callout Element Name Description 1 Product Detail Shows the following information about the product:- Product name- Family name- Part number- Version- OS details- Hardware details- Target platform details- End of support date
- Description2 Product Build Number Shows the product build number. 3 Release Type Name Shows the type of build, such as, release, hotfix, or patch. 4 Release Date Shows the release date for the build. 5 Build Version Shows the build version. 6 Actions Shows the following options for download:- Click the Share Product icon (  ) to share the product through the cloud.- Click the Download Signature icon (
) to share the product through the cloud.- Click the Download Signature icon ( ) to download the product signature file.- Click the Download Readme icon (
) to download the product signature file.- Click the Download Readme icon ( ) to download the Release Notes.
) to download the Release Notes.7 Download Date Shows the date when the file was downloaded. 8 User Shows the user name who downloaded the build. 9 Active Deployment Select the check box to mark the software as active. Clear the check box to mark the software as inactive. This option is available only after you download a product.| |10|Product Build Number|Shows the product build number.|
Click the Share Product icon (
 ) to share the desired cloud product.
) to share the desired cloud product.If the access to the cloud products is restricted and the Customer Cloud Account details are not available, then a message appears. The message displays the information that is required and the contact information for obtaining access to cloud share.
A dialog box appears and your available cloud accounts will be displayed.
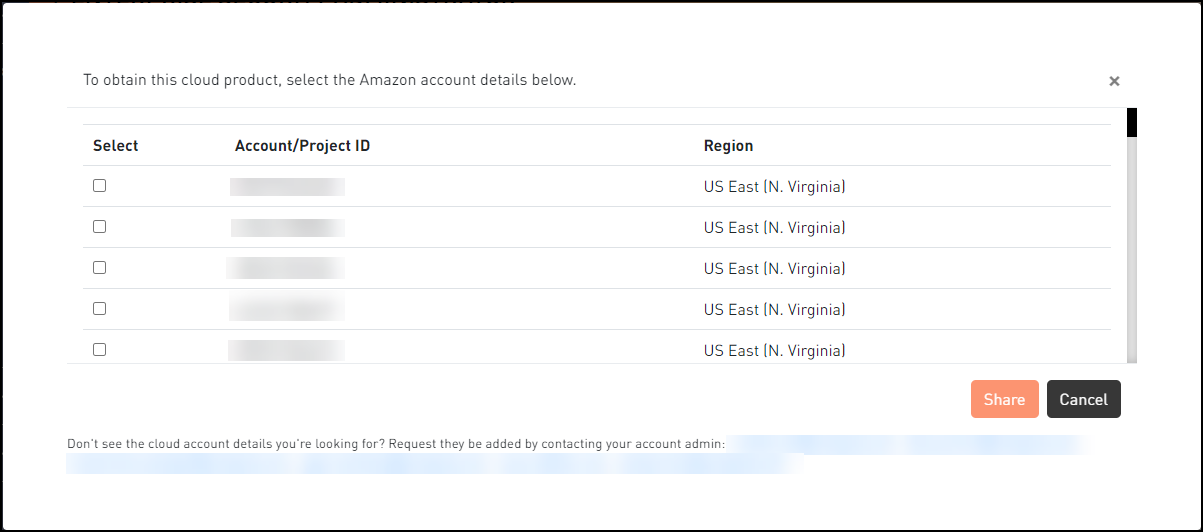
Select your required cloud account in which to share the Protegrity product.
Click Share.
A message box is displayed with the command line interface (CLI) instructions with the option to download a detailed PDF containing the cloud web interface instructions. Additionally, the instructions for sharing the cloud product are sent to your registered email address and to your notification inbox in My.Protegrity.
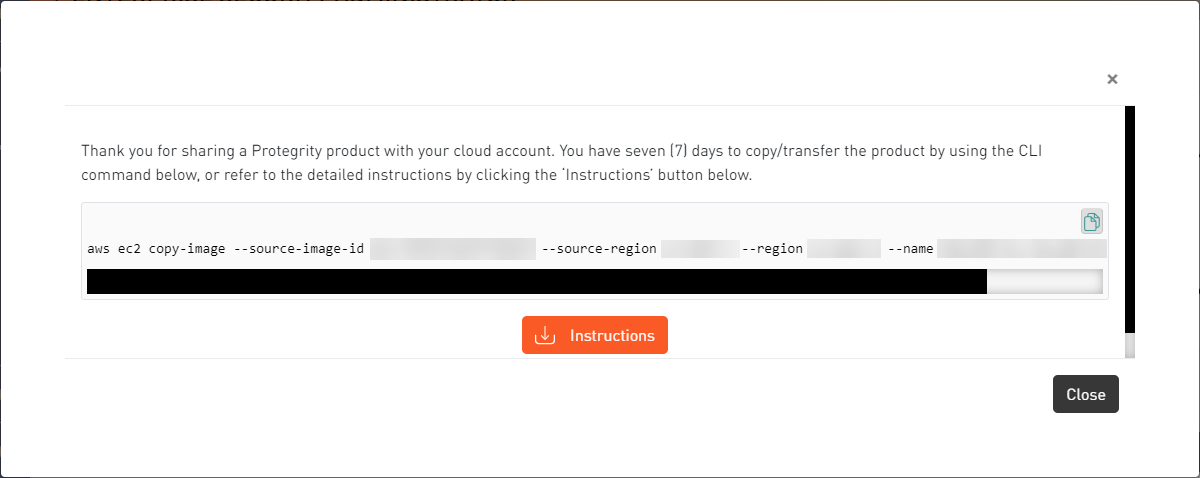
Click the Copy icon (
 ) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
The cloud sharing instruction file is saved in a
.pdfformat. You need a reader, such as, Acrobat Reader to view the file.The Cloud Product will be shared with your cloud account for seven (7) days from the original share date in the My.Protegrity portal.
After the seven (7) day time period, you need to request a new share of the cloud product through My.Protegrity.com.
1.3 - Loading the Protegrity Appliance from an Amazon Machine Image (AMI)
This section describes the tasks that need to be performed for loading the ESA appliance from an AMI, which is provided by Protegrity.
1.3.1 - Creating an ESA Instance from the AMI
Perform the following steps to create an ESA instance using an AMI.
Access AWS at the following URL:
The AWS home screen appears.
Click the Sign In to the Console button.
The AWS login screen appears.
On the AWS login screen, enter the following details:
- Account Number
- User Name
- Password
Click the Sign in button.
After successful authentication, the AWS Management Console screen appears.
Click Services.
Navigate to Compute > EC2
The EC2 Dashboard screen appears.
Contact Protegrity Support and provide your Amazon Account Number so that the required Protegrity AMIs can be made accessible to the account.
Click on AMIs under the Images section.
The AMIs that are accessible to the user account appear in the right pane.
Select the AMI of the required ESA in the right pane.
Click the Launch instance from AMI button to launch the selected ESA appliance.
The Launch an instance screen appears.
Depending on the performance requirements, choose the required instance type.
For the ESA appliance, an instance with 32 GB RAM is recommended.
If you need to configure the details of the instance, then click the Next: Configure Instance Details button.
The Configure Instance Details screen appears.
Specify the following parameters on the Configure Instance Details screen:
Number of Instances: The number of instances that you want to launch at a time.
Purchasing option: The option to request Spot instances, which are unused EC2 instances. If you select this option, then you need to specify the maximum price that you are willing to pay for each instance on an hourly basis.
Network: The VPC to launch the ESA in. If you need to create a VPC, then click the Create new VPC link. For more information about creating a VPC, refer to the section Configuring VPC.
Subnet: The Subnet to be used to launch the ESA. A subnet resides in one Availability zone.
If you need to create a Subnet, then click the Create new subnet link.
For more information about creating a subnet, refer to the section Adding a Subnet to the Virtual Private Cloud (VPC).
Auto-assign Public IP: The IP address from where your instance can be accessed over the Internet. You need to select Enable from the list.
Availability Zone: A location within a region that is designed to be isolated from failures in other Availability Zones.
IAM role: This option is disabled by default.
Shutdown behaviour: The behaviour of the ESA when an OS-level shut down command is initiated.
Enable Termination Protection: The option to prevent accidental termination of the ESA instance.
Monitoring: The option to monitor, collate, and analyze the metrics for the instance of your ESA.
If you need to add additional storage to the ESA instance, then click the Next: Add Storage button.
The Add Storage screen appears.
You can provision additional storage for the ESA by clicking the Add New Volume button. Root is the default volume for your instance.
Alternatively, you can provision additional storage for the ESA later too.
For more information on configuring the additional storage on the instance of the ESA, refer to the section Increasing Disk Space on the Appliance.
If you need to create a key-value pair, then click the Add additional tags button.
Enter the Key and Value information and select the Resource types from the drop-down.
Select the Existing Key Pair option and choose a key from the list of available key pairs.
- Alternatively, you can select the Create a new Key Pair, to create a new key pair.
- If you proceed without a key pair, then the system will not be accessible.
If you need to configure the Security Group, then click the Next: Configure Security Group button.
The Configure Security Group screen appears.
You can assign a security group from the available list.
Alternatively, you can create security group with rules for the required inbound and outbound ports.
The Summary section lists all the details related to the ESA instance. You can review the required sections before you launch your instance.
Click the Launch instance button.
The ESA instance is launched and the Launch Status screen appears.
Click the View Instances button.
The Instances screen appears listing the ESA instance.
If you need to use the instance, then access the ESA CLI Manager using the IP address of the ESA.
1.3.2 - Configuring the Virtual Private Cloud (VPC)
If you need to connect two Protegrity appliances, or to the Internet, or a corporate network using a Private IP address, then you might need to configure the VPC.
For more information about the various inbound and outbound ports to be configured in the VPC, refer to section Open Listening Ports.
Perform the following steps to configure the VPC for the instance.
Ensure that you are logged in to AWS and at the AWS Management Console screen.
On the AWS Management Console, click VPC under the Networking section.
The VPC Dashboard screen appears.
Click on Your VPCs under the Virtual Private Cloud section.
The Create VPC screen appears listing all available VPCs in the right pane.
Click the Create VPC button.
The Create VPC dialog box appears.
Specify the following parameters on the Create VPC dialog box:
- Name tag: The name of the VPC.
- CIDR block: The range of the IP addresses for the VPC in x.x.x.x/y form where x.x.x.x is the IP address and y is the /16 and /28 netmask.
- Tenancy: This parameter can be set to Default or Dedicated. If the value is set to Default, then it selects the tenancy attribute specified while launching the instance of the appliance for the VPC.
Click the Yes, Create button.
The VPC is created.
1.3.3 - Adding a Subnet to the Virtual Private Cloud (VPC)
You can add Subnets to your VPC. A subnet resides in an Availability zone. When you create a subnet, you can specify the CIDR block.
Perform the following steps to create the subnet for your VPC.
Ensure that you are logged in to AWS and at the AWS Management Console screen.
On the AWS Management Console, click VPC under the Networking section.
The VPC Dashboard screen appears.
Click Subnets under the Virtual Private Cloud section.
The create subnet screen appears listing all available subnets in the right pane.
Click the Create Subnet button.
The Create Subnet dialog box appears.
Specify the following parameters on the Create Subnet dialog box.
- Name tag: The name for the Subnet.
- VPC: The VPC for which you want to create a subnet.
- Availability Zone: The Availability zone where the subnet resides.
- CIDR block: The range of the IP addresses for the VPC in x.x.x.x/y form where x.x.x.x is the IP address and y is the /16 and /28 netmask.
Click the Yes, Create button.
The subnet is created.
1.3.4 - Finalizing the Installation of Protegrity Appliance on the Instance
When you install the ESA appliance, it generates multiple security identifiers such as, keys, certificates, secrets, passwords, and so on. These identifiers ensure that sensitive data is unique between two appliances in a network. When you receive a Protegrity appliance image, the identifiers are generated with certain values. If you use the security identifiers without changing their values, then security is compromised and the system might be vulnerable to attacks.
Rotating Appliance OS keys to finalize installation
Using the Rotate Appliance OS Keys tool, you can randomize the values of these security identifiers for an appliance. During the finalization process, you run the key rotation tool to secure your appliance.
If you do not complete the finalization process, then some features of the appliance may not be functional including the Web UI.
For example, if the OS keys are not rotated, then you might not be able to add appliances to a Trusted Appliances Cluster (TAC).
For information about the default passwords, refer to the section Launching the ESA instance on Amazon Web Services in the Release Notes 10.1.0 from the My.Protegrity.
1.3.4.1 - Logging to the AWS Instance using the SSH Client
After installing the ESA on AWS, you must log in to the AWS instance using the SSH Client.
To login to the AWS instance using the SSH Client:
Start the local SSH Client.
Perform the SSH operation on the AWS instance using the key pair utilizing the following command. Ensure that you use the local_admin user to perform the SSH operation.
ssh -i <path of the private key pair> local_admin@<IP address of the AWS instance>Press Enter.
1.3.4.2 - Finalizing an AWS Instance
You can finalize the installation of the ESA after signing in to the CLI Manager.
Before you begin
“Before finalizing the AWS instance, consider the following:
The SSH Authentication Type by default, is set to Public key. Ensure that you use the Public key for accessing the CLI. You can change the authentication type from the ESA Web UI, once the finalization is completed.
Ensure that the finalization process is initiated from a single session only. If you start finalization simultaneously from a different session, then the “Finalization is already in progress.” message appears. You must wait until the finalization of the ESA instance is successfully completed.
Ensure that the session is not interrupted. If the session is interrupted, then the ESA becomes unstable and the finalization process is not completed on that instance.
Finalizing the AWS instance
Perform the following steps to finalize the AWS instance:
Sign in to the ESA CLI Manager of the instance created using the default local admin credentials.
The following screen appears.
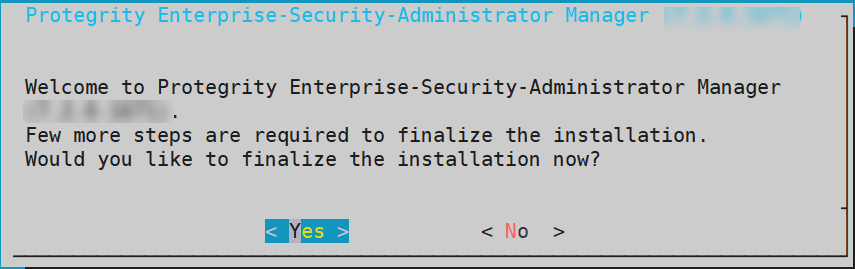
Select Yes to initiate the finalization process.
If you select No, then the finalization process is not initiated.
To manually initiate the finalization process, navigate to Tools > Finalize Installation and press ENTER.
A confirmation screen to rotate the appliance OS keys appears. Select OK to rotate the appliance OS keys.
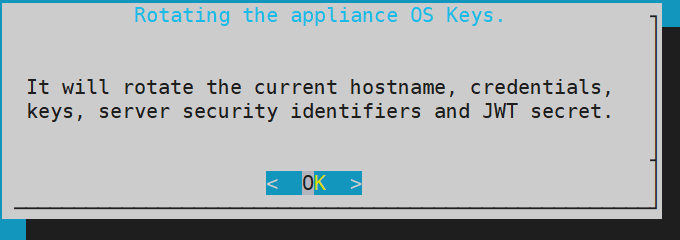
The following screen appears.
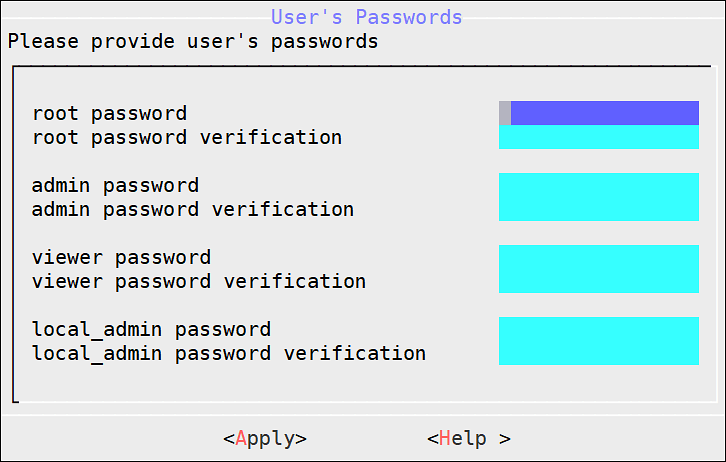
To update the user passwords, provide the credentials for the following users:
- root
- admin
- viewer
- local_admin
Select Apply.
The user passwords are updated and the appliance OS keys are rotated.
The finalization process is completed.
1.4 - Backing up and Restoring Data on AWS
A snapshot represents a state of an instance or disk at a point in time. You can use a snapshot of an instance or a disk to backup or restore information in case of failures.
Creating a Snapshot of a Volume on AWS
In AWS, you can create a snapshot of a volume.
To create a snapshot on AWS:
On the EC2 Dashboard screen, click Volumes under the Elastic Block Store section.
The screen with all the volumes appears.
Right click on the required volume and select Actions > Create Snapshot.
The Create Snapshot screen for the selected volume appears.
Enter the required description for the snapshot in the Description text box.
Select Add tag to add a tag.
Enter the tag in the Key and Value text boxes.
Click Add Tag to add additional tags.
Click Create Snapshot.
A message Create Snapshot Request Succeeded appears, along with the snapshot ID.
Ensure that you note the snapshot ID.
Ensure that the status of the snapshot is completed.
Restoring a Snapshot on AWS
On AWS, you can restore data by creating a volume of a snapshot. You then attach the volume to an EC2 instance.
Before you begin
Ensure that the status of the instance is Stopped.
Ensure that you detach an existing volume on the instance.
Restoring a Snapshot
To restore a snapshot on AWS:
On the EC2 Dashboard screen, click Snapshots under the Elastic Block Store section.
The screen with all the snapshots appears.
Right-click on the required snapshot and select Create Volume.
The Create Volume screen form appears.
Select the type of volume from the Volume Type drop-down list.
Enter the size of the volume in the Size (GiB) textbox.
Select the availability zone from the Availability Zone* drop-down list.
Click Add Tag to add tags.
Click Create Volume.
A message Create Volume Request Succeeded along with the volume id appears. The volume with the snapshot is created.
Ensure that you note the volume id.
Under the EBS section, click Volume.
The screen displaying all the volumes appears.
Right-click on the volume that is created.
The pop-up menu appears.
Select Attach Volume.
The Attach Volume dialog box appears.
Enter the Instance ID or name of the instance in the Instance text box.
Enter /dev/xvda in the Device text box.
Click Attach to add the volume to an instance.
The snapshot is added to the EC2 instance as a volume.
1.5 - Increasing Disk Space on the Appliance
After an ESA instance is created, you can increase the disk space on the appliance.Ensure that the instance is powered off before performing the following steps.
To increase disk space for the ESA on AWS:
On the EC2 Dashboard screen, click Volumes under the Elastic Block Store section.
The Create Volume screen appears.
Click the Create Volume button.
The Create Volume dialog box appears.
Enter the required size of the additional disk space in the Size (GiB) text box.
Enter the snapshot ID of the instance, for which the additional disk space is required in the Snapshot ID text box.
Click the Create button.
The required additional disk space is created as a volume.
Right-click on the additional disk, which is created.
The pop-up menu appears.
Select Attach Volume.
The Attach Volume dialog box appears.
Enter the Instance ID or name tag of the ESA to add the disk space in the Instance text box.
Click the Attach button to add the disk space to the required ESA instance.
The disk space is added to the ESA instance.
After the disk space on the ESA instance is added, navigate to Instances under the Instances section.
Right-click on the ESA instance in which the disk space was added.
Select Instance State > Start.
The ESA instance is started.
After the ESA instance is started, configure the additional storage using the CLI Manager.
For more information on configuring the additional storage on the ESA, refer to section Installation of Additional Hard Disks.
1.6 - Best Practices for Using Protegrity Appliances on AWS
There are recommended best practices for using Protegrity appliances on AWS.
Force SSH Keys
Configure the ESA to enable SSH keys and disable SSH passwords for all users.
If you need to create or join a Trusted Appliance cluster, then ensure that SSH passwords are enabled when you are creating or joining the cluster, and then disabled.
For more information about the SSH keys, refer to section Working with Secure Shell (SSH) Keys.
Install Upgrades
After you run the Appliance-rotation tool, it is recommended that you install all the latest Protegrity updates.
Configure your VPC or Security Group
To ensure successful communication between the ESA and the other entities connected to it.
For more information about the list of inbound and outbound ports for the ESA, refer to section Open Listening Ports.
1.7 - Running the Appliance-Rotation-Tool
The Appliance-rotation-tool modifies the required keys, certificates, credentials, and passwords for the appliance. This helps to differentiate the sensitive data on the appliance from other similar instances.
Before you begin
If you are configuring an ESA appliance instance, then you must run the Appliance-rotation-tool after creating the instance of the appliance.
Ensure that you do not run the appliance rotation tool when the ESA appliance OS keys are in use.
For example, you must not run the appliance rotation tool when a cluster is enabled, two-factor authentication is enabled, external users are enabled, and so on.
How to run the Appliance-Rotation-Tool
Perform the following steps to rotate the required keys, certificates, credentials, and passwords for the appliance.
To use the Appliance-rotation-tool:
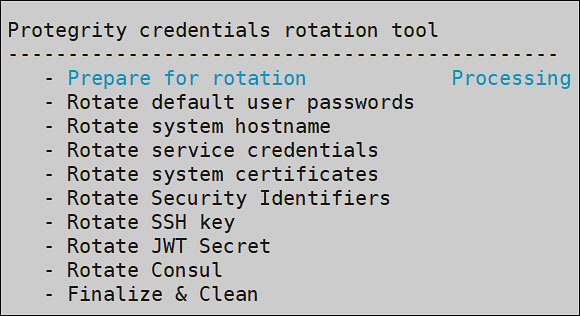
On the ESA, navigate to CLI Manager > Tools > Rotate Appliance OS Keys.
The root password dialog box appears.
Enter the root password.
Press ENTER.
The Appliance OS Key Rotation dialog box appears.
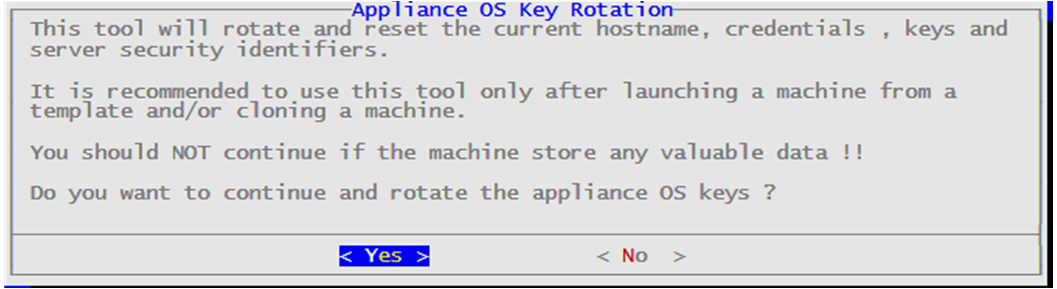
Select Yes.
Press ENTER.
The administrative credentials dialog box appears.
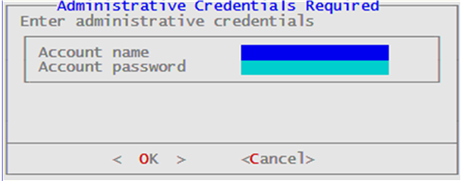
Enter the Account name and Account password on the ESA appliance.
Select OK.
To update the user passwords, provide the credentials for the users on the User’s Passwords screen. If default users such as root, admin, viewer, and local_admin have been manually deleted, they will not be listed on the User’s Passwords screen. Otherwise, to update the passwords, provide credentials for the following default users:
- root
- admin
- viewer
- local_admin
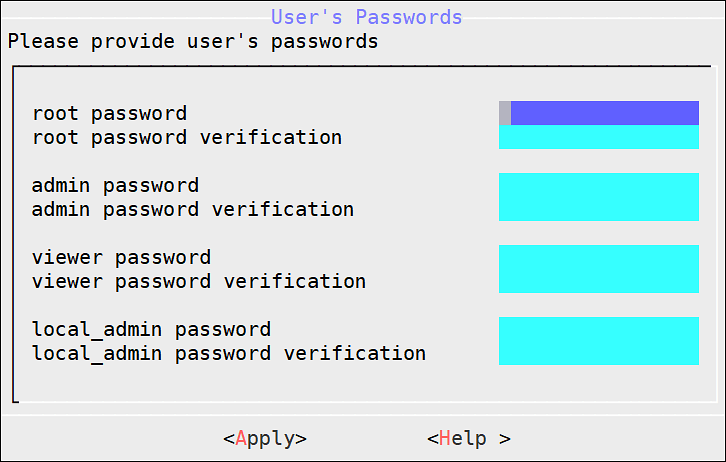
Select Apply. The user passwords are updated.
The process to rotate the required keys, certificates, credentials, and other identifiers on the ESA starts.
1.8 - Working with Cloud-based Applications
Cloud-based applications are products or services for storing data on the cloud. In cloud-based applications, the computing and processing of data is handled on the cloud. Local applications interact with the cloud services for various purposes, such as, data storage, data computing, and so on. Cloud-based applications are allocated resources dynamically and aim at reducing infrastructure cost, improving network performance, easing information access, and scaling of resources.
AWS offers a variety of cloud-based products for computing, storage, analytics, networking, and management. Using the Cloud Utility product, services such as, CloudWatch and AWS CLI are leveraged by the Protegrity appliances.
Prerequisites
The following prerequisites are essential for AWS Cloud Utility.
The Cloud Utility AWS v2.3.0 product must be installed.
From 8.0.0.0, if an instance is created on the AWS using the cloud image, then Cloud Utility AWS is preinstalled on this instance.
For more information about installing the Cloud Utility AWS v2.3.0, refer to the Protegrity Installation Guide.
If you are launching a Protegrity appliance on an AWS EC2 instance, then you must have a valid IAM Role.
For more information about IAM Role, refer to Configuring Access for AWS Resources.
If you are launching a Protegrity appliance on a non-AWS instance, such as on-premise, Microsoft Azure, or GCP instance, then the AWS Configure option must be set up.
For more information about configuring AWS credentials, refer to AWS Configure.
The user accessing the Cloud Utility AWS Tools must have AWS Admin permission assigned to the role.
For more information about AWS admin, refer to Managing Roles.
1.8.1 - Configuring Access for AWS Resources
A server might contain resources that only the authorized users can access. For accessing a protected resource, you must provide valid credentials to utilize the services of the resource. Similarly, on the AWS platform, only privileged users can access and utilize the AWS cloud applications. The Identity and Access Management (IAM) is the mechanism for securing access to your resources on AWS.
The two types of IAM mechanisms are as follows:
IAM user is an entity that represents users on AWS. To access the resources or services on AWS, the IAM user must have the privileges to access these resources. By default, you have to set up all required permissions for a user. Each IAM user can have specific defined policies. An IAM user account is beneficial as it can have special permissions or privileges associated for a user.
For more information about creating an IAM user, refer to the following link:
https://docs.aws.amazon.com/IAM/latest/UserGuide/id_users_create.html
An IAM user can access the AWS services on the required Protegrity appliance instances with the access keys. The access keys are the authentication mechanisms that authorize AWS CLI requests. The access keys can be generated when you create the IAM user account. Similar to the username and password, the access keys consist of access key ID and the secret access key. The access keys validate a user to access the required AWS services.
For more information about setting up an IAM user to use AWS Configure, refer to AWS Configure.
IAM role is the role for your AWS account and has specific permissions associated with it. An IAM role has defined permissions and privileges which can be given to multiple IAM users. For users that need same permissions to access the AWS services, you should associate an IAM role with the given user account.
If you want a Protegrity appliance instance to utilize the AWS resources, the instance must be provided with the required privileges. This is achieved by attaching an IAM role to the instance. The IAM role must have the required privileges to access the AWS resources.
For more information about creating an IAM role, refer to the following link:
https://docs.aws.amazon.com/IAM/latest/UserGuide/id_roles_create.html
For more information about IAM, refer to the following link.
https://docs.aws.amazon.com/IAM/latest/UserGuide/introduction.html
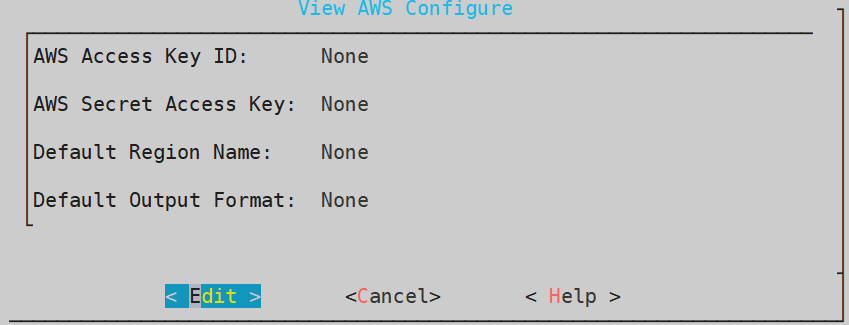
AWS Configure
The AWS Configure operation is a process for configuring an IAM user to access the AWS services on the Protegrity appliance instance. These AWS services include CloudWatch, CloudTrail, S3 bucket, and so on.
To utilize AWS resources and services, you must set up AWS Configure if you have an IAM User.
To set up AWS Configure on a non-AWS instance, such as on-premise, Microsoft Azure, or GCP instance, you must have the following:
A valid IAM User
Secret key associated with the IAM User
Access key ID for the IAM User
The AWS Region on whose servers you want to send the default service requests
For more information about the default region name, refer to the following link.
https://docs.aws.amazon.com/cli/latest/userguide/cli-chap-configure.html
If the access keys or the IAM role do not have the required privileges, then the user cannot utilize the corresponding AWS resources.
For AWS Configure, only one IAM user can be configured for an appliance at a time.
Configuring AWS Services
Below are instructions for configuring AWS services.
Before you begin
It is recommended to configure the AWS services from the Tools > Cloud Utility AWS Tools > AWS Configure menu.
On the Appliance Web UI, ensure that the AWS Admin privilege is assigned to the user role for configuring AWS on non-AWS instance.
How to configure AWS Services
To configure the AWS services:
Login to the Appliance CLI Manager.
To configure the AWS services, navigate to Tools > Cloud Utility AWS Tools > AWS Configure.
Enter the root credentials.
The following screen appears.
Select Edit and press ENTER.
Enter the AWS credentials associated with your IAM user in the AWS Access Key ID and AWS Secret Access Key text boxes.
Enter the region name in the Default Region Name text box. This field is case sensitive. Ensure that the values are entered in small-case.
For more information about the default region name, refer to the following link:
https://docs.aws.amazon.com/cli/latest/userguide/cli-chap-configure.html
Enter the output format in the Default Output Format text box. This field is case sensitive. Ensure that the values are entered in small-case.
If the field is left empty, the Default Output Format is json. However, the supported Default Output Formats are json, table, and text.
For more information about the default output format, refer to the following link:
https://docs.aws.amazon.com/cli/latest/userguide/cli-chap-configure.html
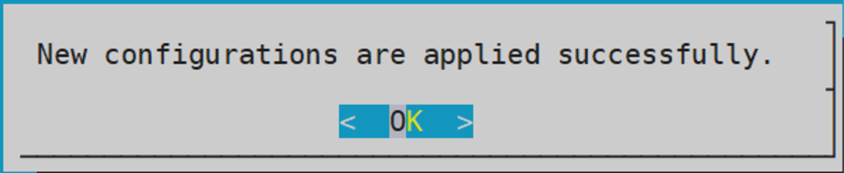
Select OK and press ENTER.
A validation screen appears.
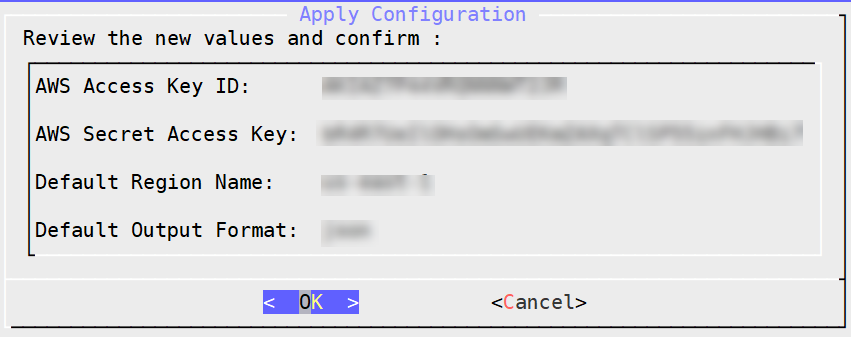
Select OK and press ENTER.
A confirmation screen appears.
Select OK.
The configurations are applied successfully.
1.8.2 - Working with CloudWatch Console
AWS CloudWatch tool is used for monitoring applications. Using CloudWatch, you can monitor and store the metrics and logs for analyzing the resources and applications.
CloudWatch allows you to collect metrics and track them in real-time. Using this service you can configure alarms for the metrics. CloudWatch provides visibility into the various aspects of your services including the operational health of your device, performance of the applications, and resource utilization.
For more information about AWS CloudWatch, refer to the following link:
https://docs.aws.amazon.com/AmazonCloudWatch/latest/monitoring/WhatIsCloudWatch.html
CloudWatch logs help you to monitor a cumulative list of all the logs from different applications on a single dashboard. This provides a central point to view and search the logs which are displayed in the order of the time when they were generated. Using CloudWatch you can store and access your log files from various sources. CloudWatch allows you to query your log data, monitor the logs which are originating from the instances and events, and retain and archive the logs.
For more information about CloudWatch logs, refer to the following link:
https://docs.aws.amazon.com/AmazonCloudWatch/latest/logs/WhatIsCloudWatchLogs.html
Prerequisites
For using AWS CloudWatch console, ensure that the IAM role or IAM user that you want to integrate with the appliance must have CloudWatchAgentServerPolicy policy assigned to it.
For more information about using the policies with the IAM Role or IAM User, refer to the following link:
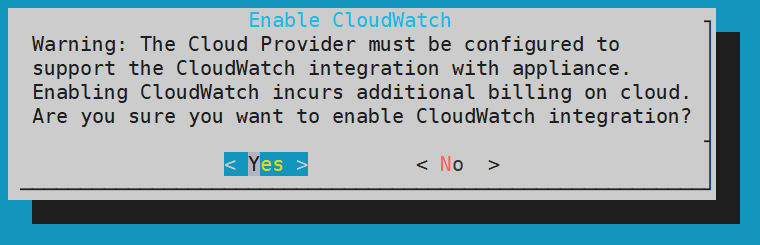
1.8.2.1 - Integrating CloudWatch with Protegrity Appliance
You must enable CloudWatch integration to use the AWS CloudWatch services. This helps you to send the metrics and the logs from the appliances to the AWS CloudWatch Console.
The following section describes the steps to enable CloudWatch integration on Protegrity appliances.
To enable AWS CloudWatch integration:
Login to the ESA CLI Manager.
To enable AWS CloudWatch integration, navigate to Tools > Cloud Utility AWS Tools > CloudWatch Integration.
Enter the root credentials.
The following screen appears.
The warning message is displayed due to the cost involved from AWS.
For more information about the cost of integrating CloudWatch, refer to the following link:
Select Yes and press ENTER.
A screen listing the logs that are being sent to the CloudWatch Console appears.
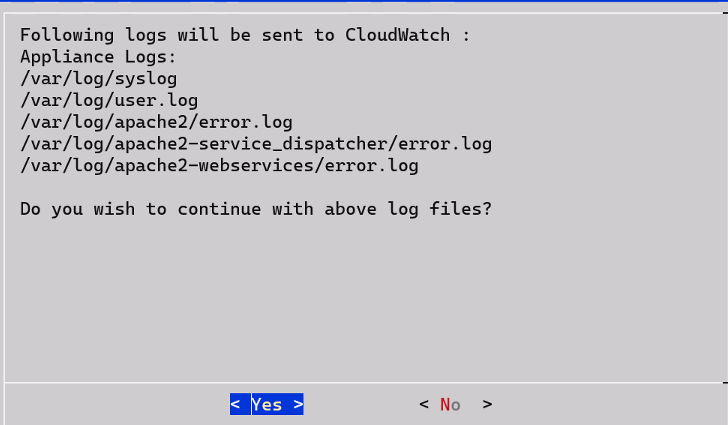
Select Yes.
Wait till the following screen appears.
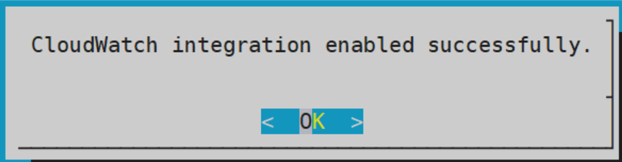
Select OK.
CloudWatch integration is enabled successfully. The CloudWatch service is enabled on the Web UI and CLI.
1.8.2.2 - Configuring Custom Logs on AWS CloudWatch Console
You can send logs from an appliance which is on-premise or launched on any of the cloud platforms, such as, AWS, GCP, or Azure. The logs are sent from the appliances and stored on the AWS CloudWatch Console. By default, the following logs are sent from the appliances:
- Syslogs
- Current events logs
- Apache2 error logs
- Service dispatcher error logs
- Web services error logs
You can send custom log files to the AWS CloudWatch Console. To send custom log files to the AWS CloudWatch Console, you must create a file in the /opt/aws/pty/cloudwatch/config.d/ directory. You can add or edit the log streams in this file to generate the custom logs with the following parameters.
You must not edit the default configuration file, appliance.conf, in the /opt/aws/pty/cloudwatch/config.d/ directory.
The following table explains the parameters that you must use to configure the log streams.
| Parameter | Description | Example |
|---|---|---|
| file_path | Location where the file or log is stored | “/var/log/appliance.log” |
| log_stream_name | Name of the log that will appear on the AWS CloudWatch Console | “Appliance_Logs” |
| log_group_name | Name under which the logs are displayed on the CloudWatch Console | - On the CloudWatch Console, the logs appear under the hostname of the ESA instance.- Ensure that you must not modify the parameter log_group_name and its value {hostname}. |
Sample configuration files
Do not edit the appliance.conf configuration file in the /opt/aws/pty/cloudwatch/config.d/ directory.
If you want to configure a new log stream, then you must use the following syntax:
[
{
"file_path": "<path_of_the_first_log_file>",
"log_stream_name": "<Name_of_the_log_stream_to_be_displayed_in_CloudWatch>",
"log_group_name": "{hostname}"
},
.
.
.
{
"file_path": "<path_of_the_nth_log_file>",
"log_stream_name": "<Name_of_the_log_stream_to_be_displayed_in_CloudWatch>",
"log_group_name": "{hostname}"
}
]
The following snippet displays the sample configuration file, configuration_filename.conf, that sends appliance logs to the AWS CloudWatch Console.
[
{
"file_path": "/var/log/syslog",
"log_stream_name": "Syslog",
"log_group_name": "{hostname}"
},
{
"file_path": "/var/log/user.log",
"log_stream_name": "Current_Event_Logs",
"log_group_name": "{hostname}"
}
]
If you configure custom log files to send to CloudWatch Console, then you must reload the CloudWatch integration or restart the CloudWatch service. Also, ensure that the CloudWatch integration is enabled and running.
For more information about Reloading AWS CloudWatch Integration, refer to Reloading AWS CloudWatch Integration.
1.8.2.3 - Toggling the CloudWatch Service
In the Protegrity appliances, the Cloudwatch service enables the transmission of logs from the appliances to the AWS CloudWatch Console. Enabling the AWS Cloudwatch Integration also enables this service with which you can start or stop the logs from being sent to the AWS CloudWatch Console. The following sections describe how to toggle the CloudWatch service for pausing or continuing log transmission. The toggling can be performed in either the CLI Manager or the Web UI.
Before you begin
Ensure that the valid AWS credentials are configured before toggling the CloudWatch service.
For more information about
Starting or Stopping the CloudWatch Service from the Web UI
If you want to temporarily stop the transmission of logs from the appliance to the AWS Console, then you can stop the CloudWatch Service.
To start or stop the AWS CloudWatch service from the Web Ui:
Login to the Appliance Web UI.
Navigate to System > Services.
Locate the CloudWatch service to start or stop. Select the appropriate icon, either Start or Stop, to perform the desired action.
- Select Stop to stop the transmission of logs and metrics.
- Select Start or Restart to start the CloudWatch service.
Starting or Stopping the CloudWatch Service from the CLI Manager
If you want to temporarily stop the transmission of logs from the appliance to the AWS Console, then you can stop the CloudWatch Service.
To start or stop the AWS CloudWatch service from the CLI Manager:
Login to the appliance CLI Manager.
Navigate to Administration > Services.
Locate the CloudWatch service to start or stop. Select the appropriate icon, either Start or Stop, to perform the desired action.
- Select Stop to stop the transmission of logs and metrics.
- Select Start to start the CloudWatch service.
1.8.2.4 - Reloading the AWS CloudWatch Integration
If you want to update the existing configurations in the /opt/aws/pty/cloudwatch/config.d/ directory, then you must reload the CloudWatch integration.
To reload the AWS CloudWatch integration:
Login to the ESA CLI Manager.
To reload CloudWatch, navigate to Tools > Cloud Utility AWS Tools > CloudWatch Integration.
Enter the root credentials.
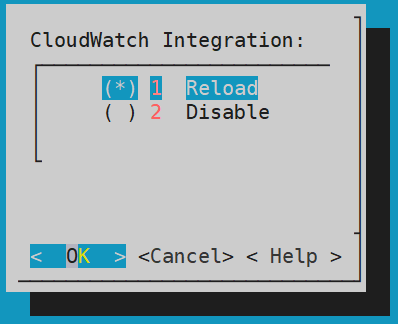
The following screen appears.
Select Reload and press ENTER.
The logs are updated and sent to the AWS CloudWatch Console.
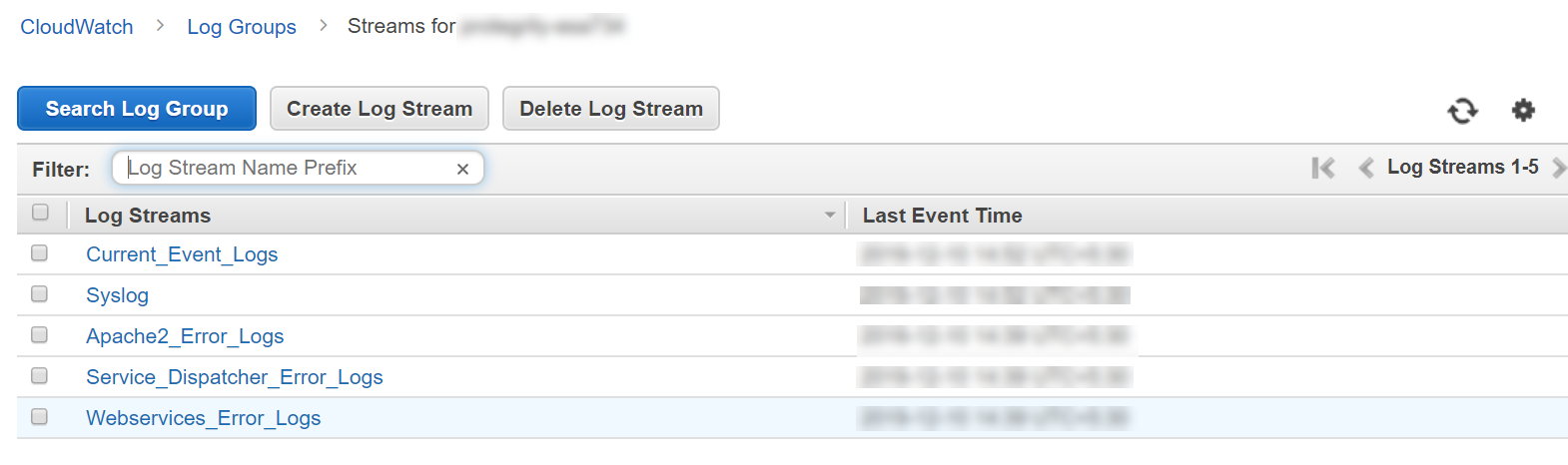
1.8.2.5 - Viewing Logs on AWS CloudWatch Console
After performing the required changes on the CLI Manager, the logs are visible on the CloudWatch Console.
To view the logs on the CloudWatch console:
Login to the AWS Web UI.
From the Services tab, navigate to Management & Governance > CloudWatch.
To view the logs, from the left pane navigate to Logs > Log groups.
Select the required log group. The name of the log group is the same as the hostname of the appliance.
To view the logs, select the required log stream from the following screen.
1.8.2.6 - Working with AWS CloudWatch Metrics
The metrics for the following entities in the appliances are sent to the AWS CloudWatch Console.
| Metrics | Description |
|---|---|
| Memory Use Percent | Percentage of the memory that is consumed by the appliance. |
| Disk I/O | Bytes and packets read and written by the appliance.You can view the following parameters:- write_bytes- read_bytes- writes- reads |
| Network | Bytes and packets sent and received by the appliance.You can view the following parameters:- bytes_sent- bytes_received- packets_sent- packets_received |
| Disk Used Percent | Percentage of the disk space that is consumed by the appliance. |
| CPU Idle | Percentage of time for which the CPU is idle. |
| Swap Memory Use Percent | Percentage of the swap memory that is consumed by the appliance. |
Unlike logs, you cannot customize the metrics that you want to send to CloudWatch. If you want to customize these metrics, then contact Protegrity Support.
1.8.2.7 - Viewing Metrics on AWS CloudWatch Console
To view the metrics on the CloudWatch console:
Login to the AWS Web UI.
From the Services tab, navigate to Management & Governance > CloudWatch.
To view the metrics, from the left pane navigate to Metrics > All metrics.
Navigate to AWS namespace.
The following screen appears.
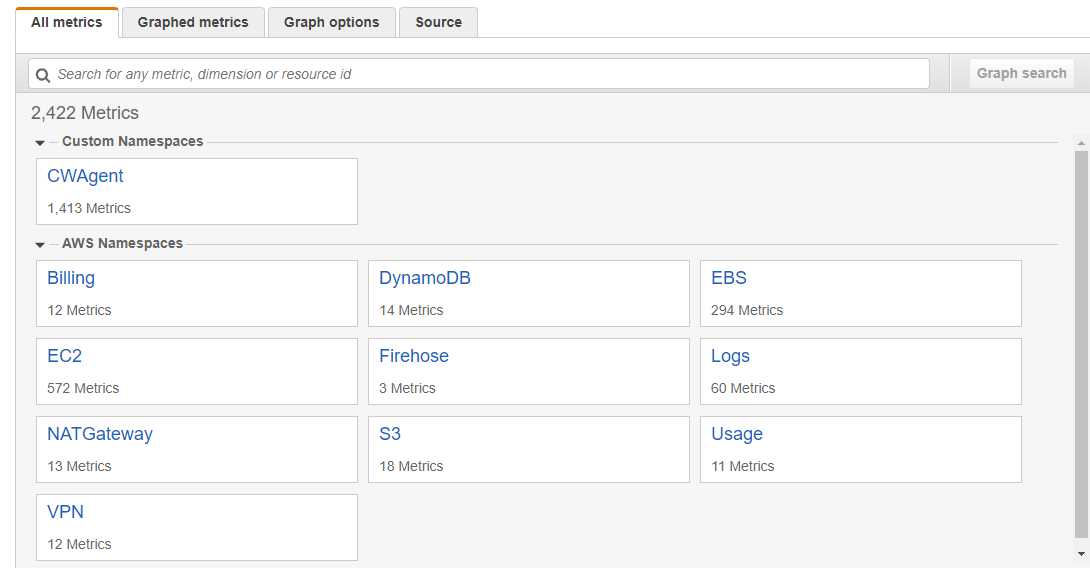
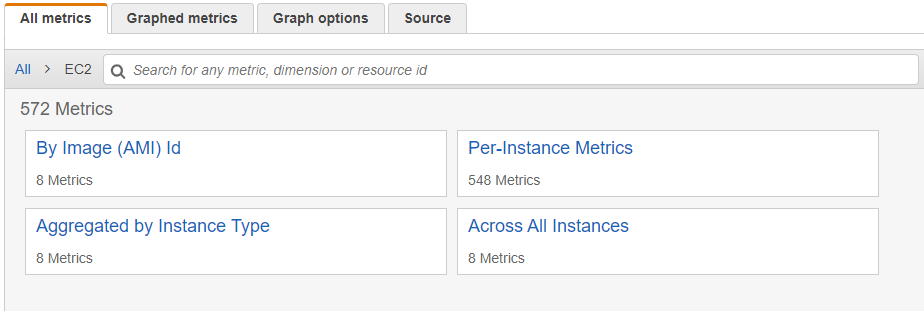
Select EC2.
Select the required metrics from the following screen.
To view metrics of the Protegrity appliances that are on-premise or other cloud platforms, such as Azure or GCP, navigate to Custom namespace > CWAgent.
The configured metrics appear.
1.8.2.8 - Disabling AWS CloudWatch Integration
If you want stop the logs and metrics that are being sent to the AWS CloudWatch Console. To disintegrate the Cloudwatch removing the service from the appliance. Then, disable the AWS CloudWatch integration from the appliance. As a result, the CloudWatch service is removed from the Services screen of the Web UI and the CLI Manager.
To disable the AWS CloudWatch integration:
Login to the ESA CLI Manager.
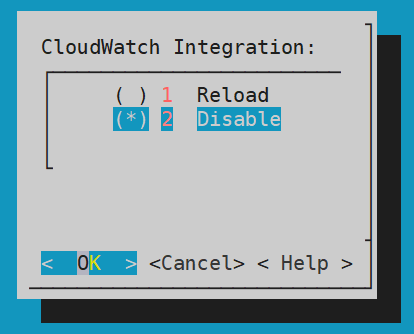
To disable CloudWatch, navigate to Tools > Cloud Utility AWS Tools > CloudWatch Integration.
The following screen appears.
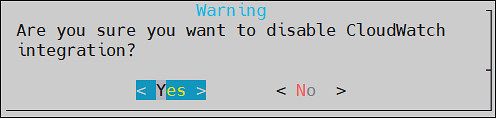
Select Disable and press ENTER.
The logs from the appliances are not updated in the AWS CloudWatch Console and the CloudWatch Integration is disabled.
A warning screen with message Are you sure you want to disable CLoudWatch integration? appears. Select Yes and press Enter.
The CloudWatch integration disabled successfully message appears. Click Ok.
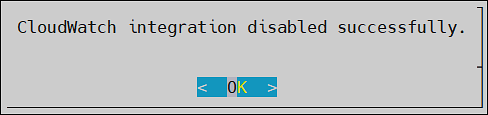
The AWS CloudWatch integration is disabled.
After disabling CloudWatch integration, you must delete the Log groups and Log streams from the AWS CloudWatch console.
1.8.3 - Working with the AWS Cloud Utility
You can work with the AWS Cloud Utility in various ways. This section contains usage examples for using the AWS Cloud Utility. However, the scope of working with Cloud Utility is not limited to the scenarios covered in this section.
The following scenarios are explained in this section:
- Encrypting and storing the backed up files on the AWS S3 bucket.
- Setting metrics-based alarms using the AWS Management Console.
1.8.3.1 - Storing Backup Files on the AWS S3 Bucket
If you want to store backed up files on the AWS S3 bucket, you can use the Cloud Utility feature. You can transit these files from the Protegrity appliance to the AWS S3 bucket.
The following tasks are explained in this section:
- Encrypting the backed up .tgz files using the AWS Key Management Services (KMS).
- Storing the encrypted files in the AWS S3 bucket.
- Retrieving the encrypted files stored in the S3 bucket.
- Decrypting the retrieved files using the AWS KMS.
- Importing the decrypted files on the Protegrity appliance.
About the AWS S3 bucket and usage
The AWS S3 bucket is a cloud resource which helps you to securely store your data. It enables you to keep the data backup at multiple locations, such as, on-premise and on cloud. For easy accessibility, you can backup and store data of one machine and import the same data to another machine, using the AWS S3 bucket. It also provides an additional layer of security by helping you encrypt the data before uploading it to the cloud.
Using the OS Console option in the CLI Manager, you can store your backed up files in the AWS S3 bucket. You can encrypt your files using the the AWS Key Management Services (KMS) before storing it in the AWS S3 bucket.
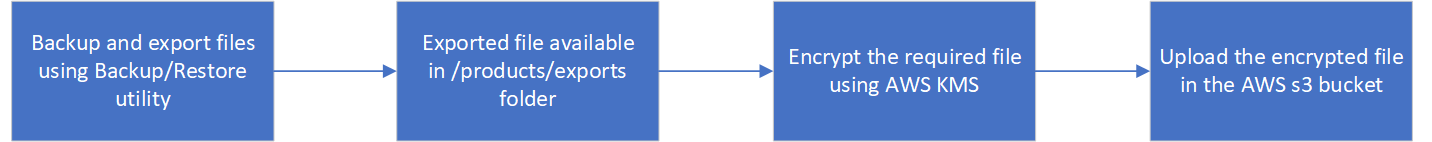
The following figure shows the flow for storing your data on the AWS S3 bucket.
Prerequisites
Ensure that you complete the following prerequisites for uploading the backed up files to the S3 bucket:
The Configured AWS user or the attached IAM role must have access to the S3 bucket.
For more information about configuring access to the AWS resources, refer to Configuring access for AWS resources.
The Configured AWS user or the attached IAM role must have AWSKeyManagementServicePowerUser permission to use the KMS.
For more information about configuring AWS resources, refer to Configuring access for AWS resources.
For more information about KMS, refer to the following link.
https://docs.aws.amazon.com/kms/latest/developerguide/iam-policies.html
The backed up .tgz file should be present in the /products/exports folder.
For more information about exporting the files, refer to Export Data Configuration to Local File.
You must have the KMS keys present in the AWS Key Management Service.
For more information about KMS keys, refer to the following link:
https://docs.aws.amazon.com/kms/latest/developerguide/getting-started.html.
Encrypting and Storing Files
To encrypt and upload the exported file from /products/exports to the S3 bucket:
Login to the Appliance CLI manager.
To encrypt and upload files, navigate to Administration > OS Console.
Enter the root credentials.
Change the directory to /products/exports using the following command.
cd /products/exportsEncrypt the required file using the aws-encryption-cli command.
aws-encryption-cli --encrypt --input <file_to_encrypt> --master-keys key=<Key_ID> region=<region-name> --output <encrypted_output_filename> --metadata-output <metadata_filename> --encryption-context purpose=<purpose_for_performing encryption>Parameter Description file_to_encrypt The backed up file that needs to be encrypted before uploading to the S3 bucket. Key_ID The key ID of the KMS key that needs to be used for encrypting the file. region-name The region where the KMS key is stored. encrypted_output_filename The name of the file after encryption. metadata_filename The name of the file where the metadata needs to be stored. purpose_for_performing encryption The purpose of encrypting the file. For more information about encrypting data using the KMS, refer to the following link.
https://docs.aws.amazon.com/cli/latest/reference/kms/encrypt.html
The file is encrypted.
Upload the encrypted file to the S3 bucket using the following command.
aws s3 cp <encrypted_output_filename> <s3Uri>The file is uploaded in the S3 bucket.
For example, if you have an encrypted file test.enc and you want to upload it to your personal bucket, mybucket, in s3 bucket, then use the following command:
aws s3 cp test.enc s3://mybucket/test.encFor more information about the S3 bucket, refer to the following link:
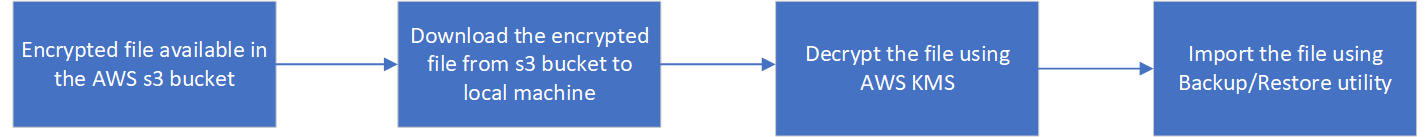
Decrypting and Importing Files
To decrypt and import the files from the S3 bucket:
Login to the Appliance CLI manager.
To decrypt and import the file, navigate to Administration > OS Console.
Enter the root credentials.
Change the directory to /products/exports using the following command:
cd /products/exportsDownload the encrypted file using the following command:
aws s3 cp <s3Uri> <local_file_name(path)>For example, if you want to download the file test.txt to your local machine as test2.txt, then use the following command:
aws s3 cp s3://mybucket/test.txt test2.txtDecrypt the downloaded file using the following command:
aws-encryption-cli --decrypt --input <file_to_decrypt> --output <decrypted_file_name> --metadata-output <metadata_filename>Parameter Description file_to_decrypt The backed up file that needs to be decrypted after downloading from the S3 bucket. decrypted_output_filename The name with which the file is saved after decryption. metadata_filename The name of the file where the metadata needs to be stored. Ensure that the metadata_filename must be the same filename which is used during encryption of the file.
The file is decrypted.
For more information about decrypting the downloaded file, refer to the following link.
Import the decrypted file to the local machine.
For more information about importing the decrypted file, refer to Import Data/Configurations from a File.
1.8.3.2 - Set Metrics Based Alarms Using the AWS Management Console
If you want to set alarms and alerts for your machine, using Protegrity appliances, you can send logs and metrics to the AWS Console. The AWS Management Console enables you to set alerts and configure SNS events as per your requirements.
You can create alerts based on the following metrics:
- Memory Use Percent
- Disk I/O
- Network
- Disk Used Percent
- CPU Idle
- Swap Memory Use Percent
Prerequisite
Ensure that the CloudWatch integration is enabled.
For more information about enabling the CloudWatch integration, refer to Enabling AWS CloudWatch Integration.
Creating an SNS Event
The following steps explain how to create an SNS event for an email-based notification.
To create an SNS event:
Login to the Amazon Management Console.
To create an SNS event, navigate to Services > Application Integration > Simple Notification Services > Topics.
Select Create topic.
The following screen appears.
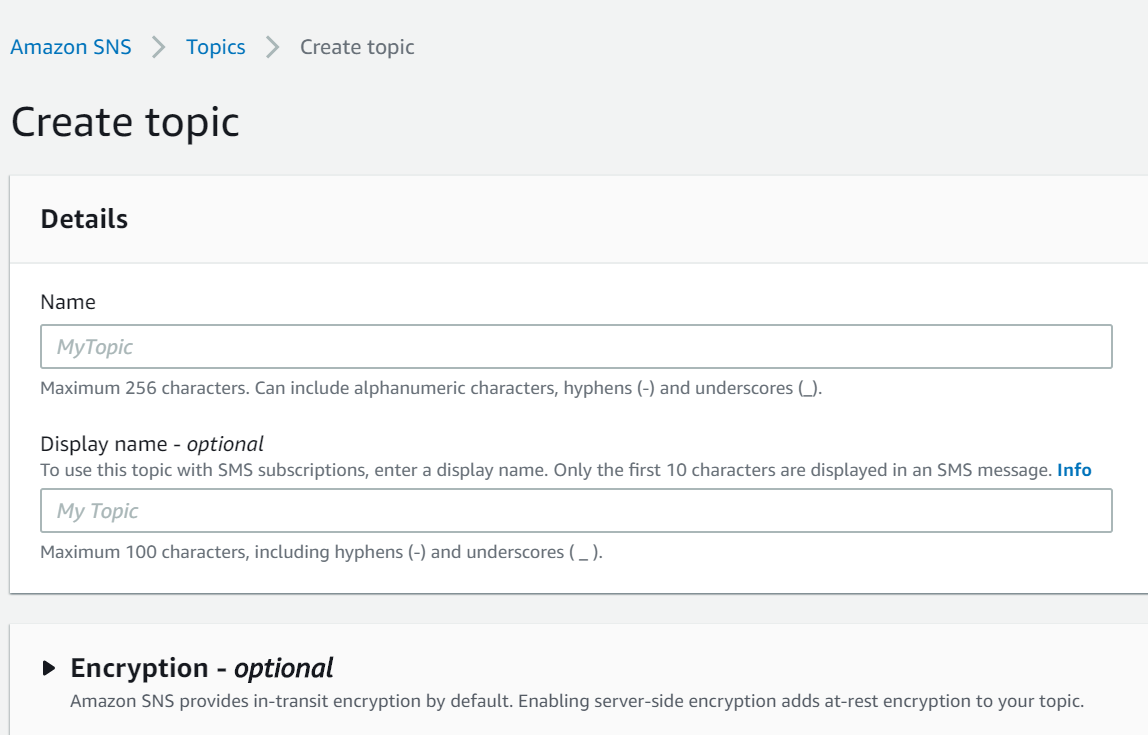
Enter the required Details.
Click Create topic.
The following screen appears.
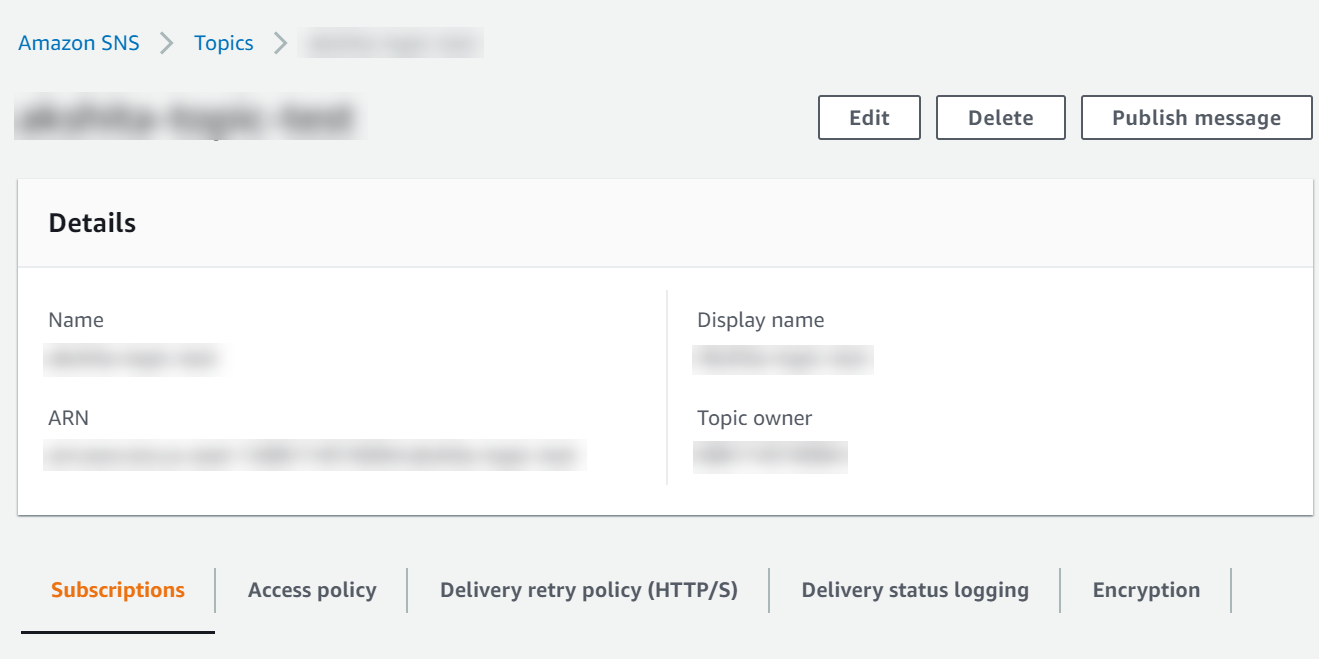
Ensure that you remember the Amazon Resource Name (ARN) associated to your topic.
For more information about the ARN, refer to the following link.
https://docs.aws.amazon.com/general/latest/gr/aws-arns-and-namespaces.html
The topic is created.
From the left pane, click Subscriptions.
Click Create subscription.
Enter the Topic ARN of the topic created in the above step.
From the Protocol field, select Email.
In the Endpoint, enter the required email address where you want to receive the alerts.
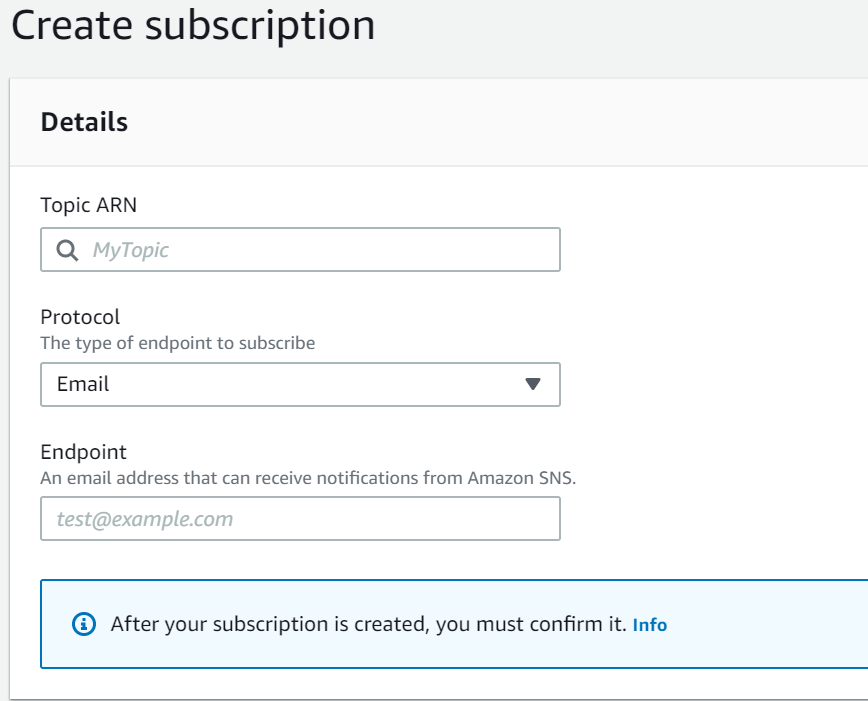
Enter the optional details.
Click Create subscription.
An SNS event is created and a confirmation email is sent to the subscribed email address.
To confirm the email subscription, click the Confirm Subscription link from the email received on the registered email address.
Creating Alarms
The following steps explain the procedure to set an alarm for CPU usage.
To create an alarm:
Login to the Amazon Management Console.
To create an alarm, navigate to Services > Management & Governance > CloudWatch.
From the left pane, select Alarms > In alarm.
Select Create alarm.
Click Select metric.
The Select metric window appears.
From the Custom Namespaces, select CWAgent.
Select cpu, host.
Select the required metric and click Select metric.
Configure the required metrics.
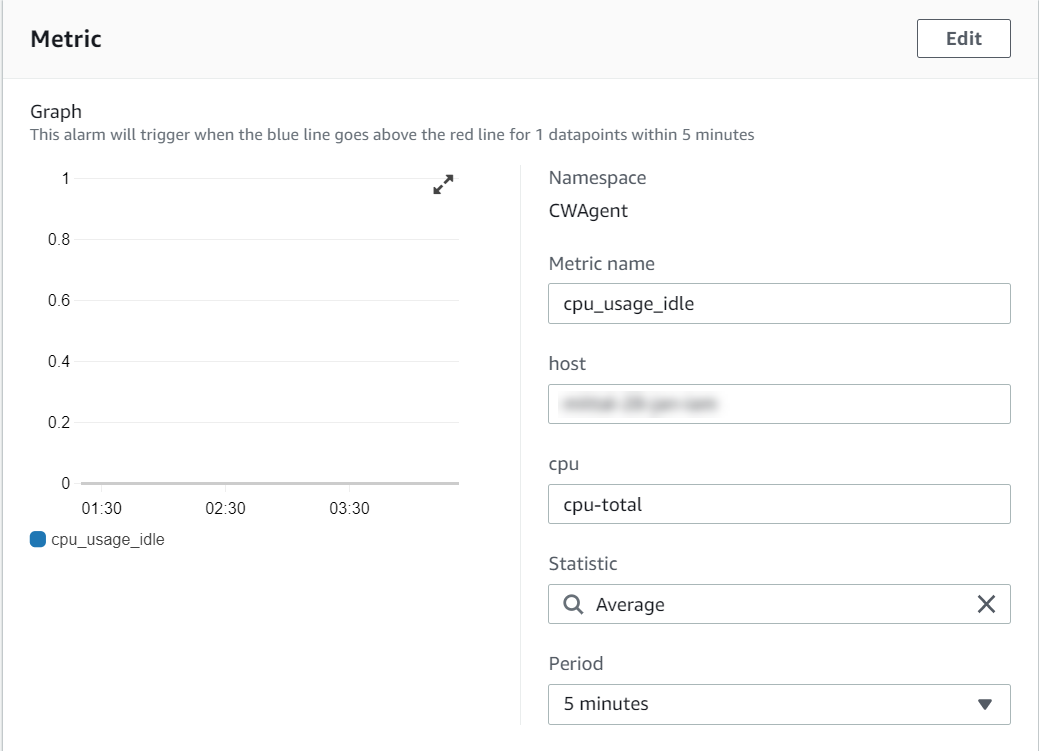
Configure the required conditions.
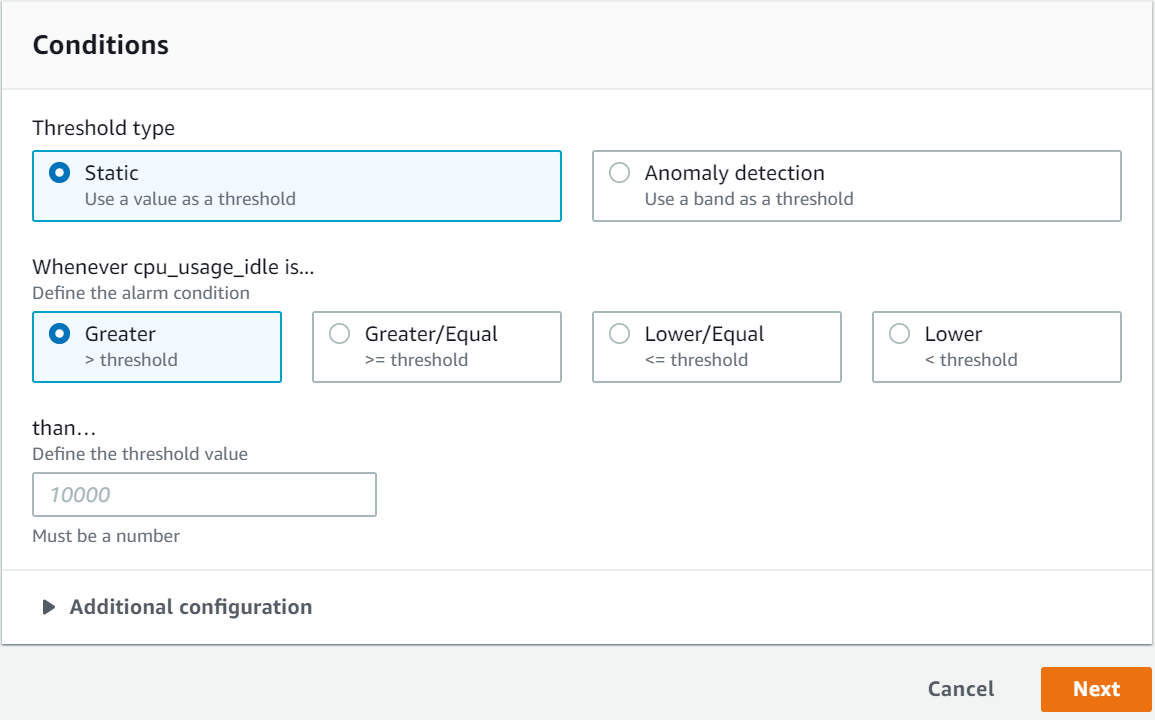
Click Next.
The Notification screen appears.
Select the alarm state.
From Select SNS topic, choose Select an existing SNS topic.
Enter the required email type in Send a notification to… dialog box.
Select Next.
Enter the Name and Description.
Select Next.
Preview the configuration details and click Create alarm.
An alarm is created.
1.8.4 - FAQs for AWS Cloud Utility
This section lists the FAQs for the AWS Cloud Utility.
Where can I install the AWS Cloud/CloudWatch/Cloud Utilities?
AWS Cloud Utility can be installed on any appliance-based product. It is compatible with the ESA and the DSG that are installed on-premise or on cloud platforms, such as, AWS, Azure, or GCP.
If an instance is created on the AWS using the cloud image, then Cloud Utility AWS is preinstalled on this instance.
Which version of AWS CLI is supported by the AWS Cloud Utility product v2.3.0?
AWS CLI 2.15.41 is supported by the Cloud Utility AWS product v2.3.0.
What is the Default Region Name while configuring AWS services?
The Default Region Name on whose servers you want to send the default service requests.
For more information about Default Region Name, refer to the following link: https://docs.aws.amazon.com/cli/latest/userguide/cli-chap-configure.html
Can I configure multiple accounts for AWS on a single appliance?
No, you cannot configure multiple accounts for AWS on a single appliance.
How to determine the Log group name?
The Log group name is same as the hostname of the appliance.
Can I change the Log group name?
No, you cannot change the Log group name.
Can I change the appliance hostname after enabling CloudWatch integration?
If you change the appliance hostname after enabling CloudWatch integration, then:
- A new Log Group is created with the updated hostname.
- Only the new logs will be present in the updated Log Group.
- The new Log Group consists of only the updated logs files.
- It is recommended to manually delete the previous Log Group from the AWS CloudWatch Console.
Are there any configuration files for AWS CloudWatch?
Yes, there are configuration files for CloudWatch. The configuration files are present in /opt/aws/pty/cloudwatch/config.d/ directory.
The config.json file for cloud watch is present in /opt/aws/pty/cloudwatch/config.json file.
It is recommended not to edit the default configuration files.
What happens if I enable CloudWatch integration with a corrupt file?
The invalid configuration file is listed in a dialog box.
The logs corresponding to all other valid configurations will be sent to the AWS CloudWatch Console.
What happens if I edit the only default configuration files, such as, /opt/aws/pty/cloudwatch/config.d/, with invalid data for CloudWatch integration?
In this case, only metrics will be sent to the AWS CloudWatch Console.
How can I export or import the CloudWatch configuration files?
You can export or import the CloudWatch configuration files either through the CLI Manager or through the Web UI.
For more information about exporting or importing the configuration files through the CLI manager, refer to Exporting Data Configuration to Local File.
For more information about exporting or importing the configuration files through the Web UI, refer to Backing Up Data.
What are the compatible Output Formats while configuring the AWS?
The following Default Output Formats are compatible:
- json
- table
- text
If I use an IAM role, what is the Default Output Formats?
The Default Output Format is json.
If I disable the CloudWatch integration, why do I need to delete Log Groups and Log Streams manually?
You should delete Log Groups and Log Streams manually because this relates to the billing cost.
Protegrity will only disable sending logs and metrics to the CloudWatch Console.
How can I check the status of the CloudWatch agent service?
You can view the status of the of the CloudWatch service using one of the following.
On the Web UI, navigate to System > Services.
On the CLI Manager, navigate to Administration > Services.
On the CLI Manager, navigate to Administration > OS Console and run the following command:
/etc/init.d/cloudwatch_service status
Can I customize the metrics that i want to send to the CloudWatch console?
No, you cannot customize the metrics to send to the CloudWatch console. If you want to customize the metrics, then contact Protegrity Support.
How often are the metrics collected from the appliances?
The metrics are collected at 60 seconds intervals from the appliance.
How much does Amazon CloudWatch cost?
For information about the billing and pricing details, refer to https://aws.amazon.com/cloudwatch/pricing/.|
Can I provide the file path as <foldername/>* to send logs to the folder?
No, you can not provide the file path as <foldername/>*.
Regex is not allowed in the CloudWatch configuration file. You must specify the absolute file path.
Can I configure AWS from OS Console?
No, you can not. If you configure AWS from the OS Console it will change the expected behaviour of the AWS Cloud Utility.
What happens to the custom configurations if I uninstall or remove the AWS Cloud Utility product?
The custom configurations are retained.
What happens to CloudWatch if I delete AWS credentials from ESA after enabling CloudWatch integration?
You can not change the status of the CloudWatch service. You must reconfigure the ESA with valid AWS credentials to perform the CloudWatch-related operations.
Why some of the log files are world readable?
The files with the .log extension present in the /opt/aws/pty/cloudwatch/logs/state folder are not log files. These files are used by the CloudWatch utility to monitor the logs.
Why is the CloudWatch service stopped when the patch is installed? How do I restart the service?
As the CloudWatch service is stopped when the patch is installed, it remains in the stopped state after the Cloud Utility Patch (CUP) installation. So, we must restart the CloudWatch service manually.To restart the CloudWatch service manually, perform the following steps.
- Login to the OS Console.
- Restart the CloudWatch service using the following command.
/etc/init.d/cloudwatch_service restart
1.8.5 - Working with AWS Systems Manager
The AWS Systems Manager allows you to manage and operate the infrastructure on AWS. Using the Systems Manager console, you can view operational data from multiple AWS services and automate operational tasks across the AWS services.
For more information about AWS Systems Manager, refer to the following link:
https://docs.aws.amazon.com/systems-manager/latest/userguide/what-is-systems-manager.html
Prerequisites
Before using the AWS Systems Manager, ensure that the IAM role or IAM user to integrate with the appliance has a policy assigned to it. You can attach one or more IAM policies that define the required permissions for a particular IAM role.
For more information about the IAM role, refer to section Configuring Access for AWS Instances.
For more information about creating an IAM instance profile for Systems Manager, refer to the following link:
https://docs.aws.amazon.com/systems-manager/latest/userguide/setup-instance-profile.html
1.8.5.1 - Setting up AWS Systems Manager
You must set up AWS Systems Manager to use the Systems Manager Agent (SSM Agent).
You can set up Systems Manager for:
- An AWS instance
- A non-AWS instance or an on-premise platform
After the SSM Agent is installed in an instance, ensure that the auto-update option is disabled, as we do not support auto-update. If the SSM Agent gets auto updated, the service will get corrupted.
For more information about automatic updates for SSM Agent, refer to the following link:
Setting up Systems Manager for AWS Instance
To set up Systems Manager for an AWS instance:
Assign the IAM Role created in the section Prerequisites.
For more information about attaching an IAM role to an instance, refer to the following link:
https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/iam-roles-for-amazon-ec2.html#attach-iam-role
Start the Amazon SSM-Agent from the Services menu or run the following command to start the SSM-Agent.
/etc/init.d/amazon-ssm-agent start
Setting up Systems Manager for non-AWS Instance
To set up Systems Manager for non-AWS instance:
Create a hybrid activation for the Linux instances.
For more information about creating a managed instance activation for a hybrid environment, refer to the following link:
https://docs.aws.amazon.com/systems-manager/latest/userguide/sysman-managed-instance-activation.html
Important: After you successfully complete the activation, an Activation Code and Activation ID appears. Copy this information and save it. If you lose this information, then you must create a new activation.
Login to the CLI as an admin user and open the OS Console.
Using the Activation Code and Activation ID obtained in Step 1, run the following command to activate and register the SSM-Agent.
amazon-ssm-agent -register -code <activation-code> -id <activation-id> -region <region>Here
<region>is the identifier of the instance region.Note the instance-id. This will be used to perform operations from SSM-Agent.
For more information on how to register a managed instance, refer to the following link:
Start the Amazon SSM-Agent from the Services menu or run the following command to start the SSM-Agent.
/etc/init.d/amazon-ssm-agent start
1.8.5.2 - FAQs on AWS Systems Manager
This section lists the FAQs on AWS Systems Manager.
What can I do when there is a problem with starting the service or the service is automatically updated?
Uninstall and reinstall the Cloud Utility AWS product.
For more information on installing and uninstalling the services, refer Add/Remove Services.
What is the name of the service?
The service name is Amazon SSM-Agent.
What can I do if the AWS Systems Manager shows a permission denied message after attaching the correct IAM Role?
Restart the service after attaching the IAM role for new permissions to take effect.
Is the Amazon SSM-Agent service available in the Services menu in the Web UI and the CLI?
Yes.
Can I manage the Amazon SSM-Agent service from the Menu option in the Web UI?
Yes, you can start or stop and restart the Amazon SSM Agent service from the Menu option in the Web UI.
1.8.6 - Troubleshooting for the AWS Cloud Utility
This section lists the troubleshooting for the AWS Cloud Utility.
While using AWS services the following error appears: UnknownRegionError("No default region found...”)
Issue: The service is unable to retrieve the AWS Region from the system.
Workaround: The service is region specific. Include the region name in the command.
region=<region-name>
The CloudWatch service was running and the service has stopped after restarting the system.
Issue: The CloudWatch Service Mode is set to Manual
Workaround: You should restart the service manually.
If the CloudWatch Service Mode is set to Automatic, then wait until all the services start.
The CloudWatch integration is enabled, but the log group/log stream is not created or logs are not being updated.
Issue: This issue occurs because the associated IAM Role or IAM User does not have required permissions to perform CloudWatchrelated operations.
To verify the error, check the log file by using a text editor.
/var/log/amazon/amazoncloudwatch-agent/amazoncloudwatch-agent.log
You can see one of the following errors:
E! WriteToCloudWatch failure, err: AccessDenied: User: arn:aws:sts:**** is not authorized to perform: cloudwatch:PutMetricDataE! cloudwatchlogs: code: AccessDeniedException, message: User: arn:aws:sts:**** is not authorized to perform: logs:PutLogEventsE! CreateLogStream / CreateLogGroup AccessDeniedException: User: arn:aws:sts:**** is not authorized to perform: logs:CreateLogStream
Workaround: Assign CloudWatchAgentServerPolicy permissions to the associated IAM Role or IAM User and restart the service.
I can see the error message: Unable to locate valid credentials for CloudWatch
Issue: The error message can be because of one of the following reasons:
- If you are using an AWS instance, then the IAM Role is not configured for the AWS instance.
- If you are using a non-AWS instance, then the IAM User is configured with invalid AWS
Workaround: On AWS instance, navigate to the AWS console and attach the IAM role to the instance.
For more information about attaching the IAM role, refer https://aws.amazon.com/blogs/security/easily-replace-or-attach-an-iam-role-to-an-existing-ec2-instance-by-using-the-ec2-console/.
On non-AWS instance, to configure the IAM user with valid credentials, navigate to Tools > CloudWatch Utility AWS Tools > AWS Configure.
I am unable to see AWS Tools section under Tools in the CLI Manager
Issue: The AWS Admin role is not assigned to the instance.
Workaround: For more information about the AWS Admin role, refer Managing Roles.
I can see one of the following error messages: CloudWatch Service started failed or CloudWatch Service stopped failed
Issue: The ESA is configured with invalid AWS credentials.
Workaround: You must reconfigure the ESA with valid AWS credentials.
2 - Installing ESA on Google Cloud Platform (GCP)
The Google Cloud Platform (GCP) is a cloud computing service offered by Google, which provides services for compute, storage, networking, cloud management, security, and so on. The following products are available on GCP:
- Google Compute Engine provides virtual machines for instances.
- Google App Engine provides a Software Developer Kit (SDK) to develop products.
- Google Cloud Storage is a storage platform to store large data sets.
- Google Container Engine is a cluster-oriented container to develop and manage Docker containers.
Protegrity provides the images for GCP that contain either the Enterprise Security Administrator (ESA), or the Data Security Gateway (DSG).
This section describes the prerequisites and tasks for installing Protegrity ESA appliances on GCP. In addition, it describes some best practices for using the Protegrity ESA appliances on GCP effectively.
2.1 - Verifying Prerequisites
This section describes the prerequisites including the hardware, software, and network requirements for installing and using ESA on GCP.
Prerequisites
The following prerequisite is essential to install the Protegrity ESA appliances on GCP:
- A GCP account and the following information:
- Login URL for the GCP account
- Authentication credentials for the GCP account
- Access to the My.Protegrity portal
Hardware Requirements
As the Protegrity ESA appliances are hosted and run on GCP, the hardware requirements are dependent on the configurations provided by GCP. The actual hardware configuration depends on the actual usage or amount of data and logs expected. However, these requirements can autoscale as per customer requirements and budget.
The minimum recommendation for an ESA is 8 CPU cores and 32 GB memory. On GCP, this configuration is available under the Machine type drop-down list in the n1-standard-8 option.
For more information about the hardware requirements of ESA, refer to section System Requirements.
Network Requirements
The Protegrity ESA appliances on GCP are provided with a Google Virtual Private Cloud (VPC) networking environment. The Google VPC enables you to access other instances of Protegrity resources in your project.
You can configure the Google VPC by specifying the IP address range. You can also create and configure subnets, network gateways, and the security settings.
For more information about the Google VPC, refer to the VPC documentation at: https://cloud.google.com/vpc/docs/vpc
If you are using the ESA or the DSG appliance with GCP, then ensure that the inbound and outbound ports of the appliances are configured in the VPC.
For more information about the list of inbound and outbound ports, refer to the section Open Listening Ports.
2.2 - Configuring the Virtual Private Cloud (VPC)
You must configure your Virtual Private Cloud (VPC) to connect to different Protegrity appliances,such as, ESA and DSG.
To configure a VPC:
Ensure that you are logged in to the GCP Console.
Navigate to the Home screen.
Click the navigation menu on the Home screen.
Under Networking, navigate to VPC network > VPC networks.
The VPC networks screen appears.
Click CREATE VPC NETWORK.
The Create a VPC network screen appears.
Enter the name and description of the VPC network in the Name and Description text boxes.
Under the Subnets area, click Custom to add a subnet.
Enter the name of the subnet in the Name text box.
Click Add a Description to enter a description for the subnet.
Select the region where the subnet is placed from the Region drop-down menu.
Enter the IP address range for the subnet in the IP address range text box.
For example, 10.1.0.0/99.
Select On or Off from the Private Google Access options to set access for VMs on the subnet to access Google services without assigning external IP addresses.
Click Done. Additionally, click Add Subnet to add another subnet.
Select Regional from the Dynamic routing mode option.
Click Create to create the VPC.
The VPC is added to the network.
Adding a Subnet to the Virtual Private Cloud (VPC)
You can add a subnet to your VPC.
To add a subnet:
Ensure that you are logged in to the GCP Console.
Under Networking, navigate to VPC network > VPC networks.
The VPC networks screen appears.
Select the VPC.
The VPC network details screen appears.
Click EDIT.
Under Subnets area, click Add Subnet.
The Add a subnet screen appears.
Enter the subnet details.
Click ADD.
Click Save.
The subnet is added to the VPC.
2.3 - Obtaining the GCP Image
Before creating the instance on GCP, you must obtain the image from the My.Protegrity portal. On the portal, you select the required ESA version and choose GCP as the target cloud platform. You then share the product to your cloud account. The following steps describe how to share the image to your cloud account.
To obtain and share the image:
Log in to the My.Protegrity portal with your user account.
Click Product Management > Explore Products > Data Protection.
Select the required ESA Platform Version from the drop-down.
The Product Family table will update based on the selected ESA Platform Version.
The ESA Platform Versions listed in drop-down menu reflect all versions. These include versions that were either previously downloaded or shipped within the organization along with any newer versions available thereafter. Navigate to Product Management > My Product Inventory to check the list of products previously downloaded.
The images in this section consider the ESA as a reference. Ensure that you select the required image.
Select the Product Family.
The description box will populate with the Product Family details.
Click View Products to advance to the product listing screen.
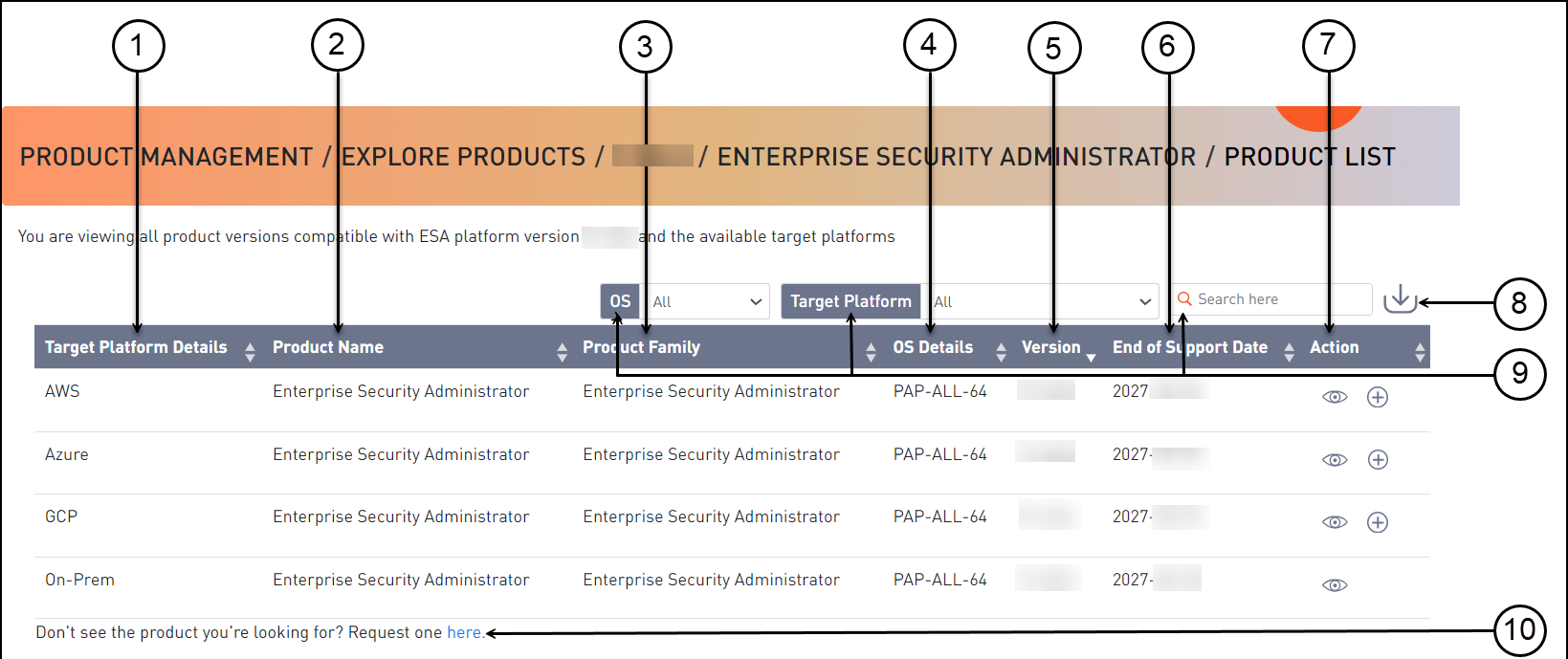
Callout Element Name Description 1 Target Platform Details Shows details about the target platform. 2 Product Name Shows the product name. 3 Product Family Shows the product family name. 4 OS Details Shows the operating system name. 5 Version Shows the product version. 6 End of Support Date Shows the final date that Protegrity will provide support for the product. 7 Action Click the View icon (  ) to open the Product Detail screen.
) to open the Product Detail screen.8 Export as CSV Downloads a .csv file with the results displayed on the screen. 9 Search Criteria Type text in the search field to specify the search filter criteria or filter the entries using the following options:- OS- Target Platform 10 Request one here Opens the Create Certification screen for a certification request. Select the GCP cloud target platform you require and click the View icon (
 ) from the Action column.
) from the Action column.The Product Detail screen appears.

Callout Element Name Description 1 Product Detail Shows the following information about the product:- Product name- Family name- Part number- Version- OS details- Hardware details- Target platform details- End of support date
- Description2 Product Build Number Shows the product build number. 3 Release Type Name Shows the type of build, such as, release, hotfix, or patch. 4 Release Date Shows the release date for the build. 5 Build Version Shows the build version. 6 Actions Shows the following options for download:- Click the Share Product icon (  ) to share the product through the cloud.- Click the Download Signature icon (
) to share the product through the cloud.- Click the Download Signature icon ( ) to download the product signature file.- Click the Download Readme icon (
) to download the product signature file.- Click the Download Readme icon ( ) to download the Release Notes.
) to download the Release Notes.7 Download Date Shows the date when the file was downloaded. 8 User Shows the user name who downloaded the build. 9 Active Deployment Select the check box to mark the software as active. Clear the check box to mark the software as inactive. This option is available only after you download a product.| |10|Product Build Number|Shows the product build number.|
Click the Share Product icon (
 ) to share the desired cloud product.
) to share the desired cloud product.If the access to the cloud products is restricted and the Customer Cloud Account details are not available, then a message appears. The message displays the information that is required and the contact information for obtaining access to cloud share.
A dialog box appears and your available cloud accounts will be displayed.
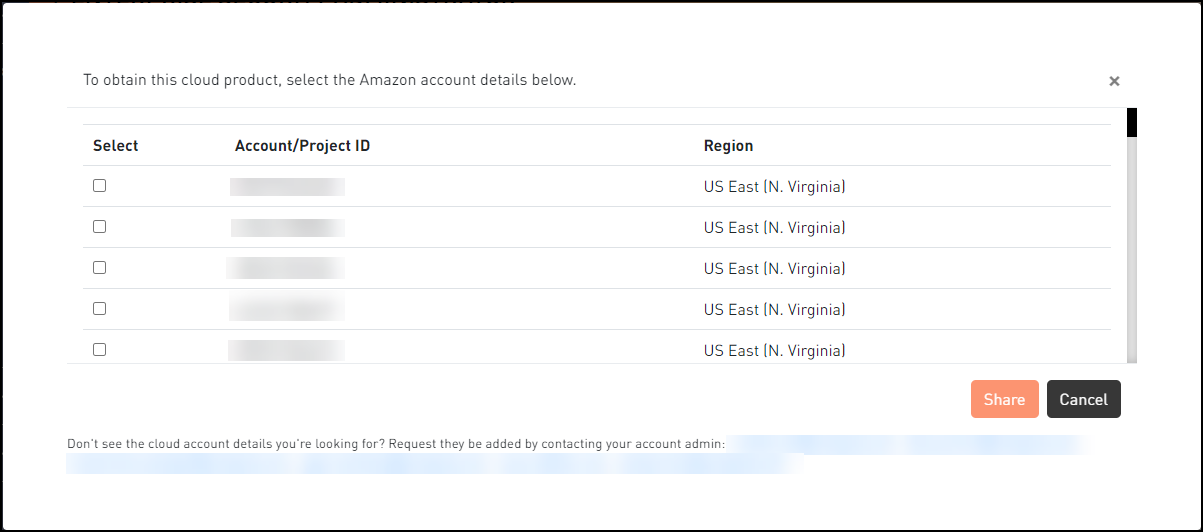
Select your required cloud account in which to share the Protegrity product.
Click Share.
A message box is displayed with the command line interface (CLI) instructions with the option to download a detailed PDF containing the cloud web interface instructions. Additionally, the instructions for sharing the cloud product are sent to your registered email address and to your notification inbox in My.Protegrity.
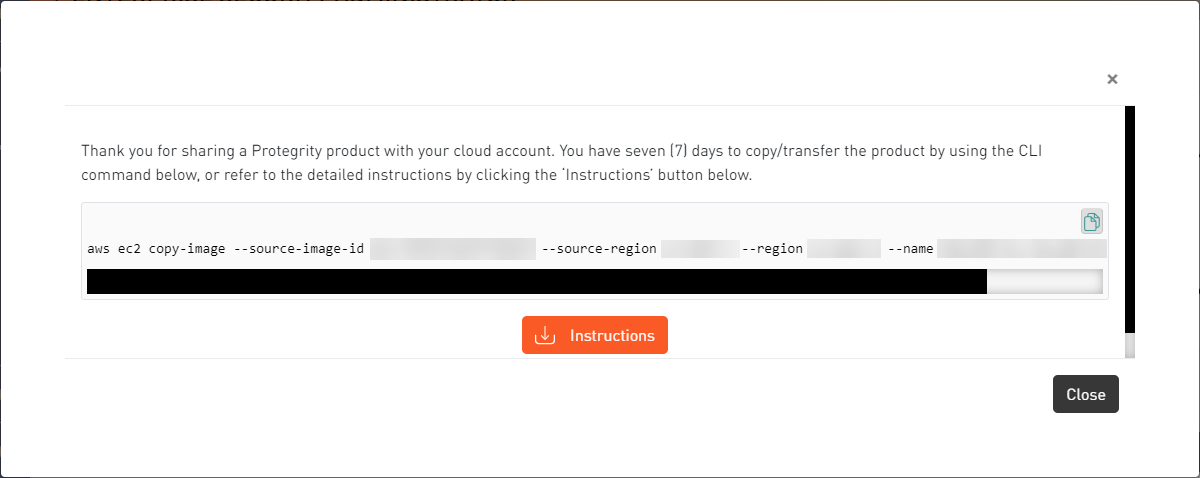
Click the Copy icon (
 ) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
The cloud sharing instruction file is saved in a
.pdfformat. You need a reader, such as, Acrobat Reader to view the file.The Cloud Product will be shared with your cloud account for seven (7) days from the original share date in the My.Protegrity portal.
After the seven (7) day time period, you need to request a new share of the cloud product through My.Protegrity.com.
2.4 - Converting the Raw Disk to a GCP Image
After obtaining the image from Protegrity, you can proceed to create a virtual image. However, the image provided is available as disk in a raw format. This must be converted to a GCP specific image before you create an instance. The following steps provide the details of converting the image in a raw format to a GCP-specific image.
To convert the image:
Login to the GCP Console.
Run the following command.
gcloud compute images create <Name for the new GCP Image > --source-uri gs://<Name of the storage location where the raw image is obtained>/<Name of the GCP image>>For example,
gcloud compute images create esa80 --source-uri gs://stglocation80/esa-pap-all-64-x86-64-gcp-8-0-0-0-1924.tar.gzThe raw image is converted to a GCP-specific image. You can now create an instance using this image
2.5 - Loading the Protegrity ESA Appliance from a GCP Image
This section describes the tasks that you must perform to load the Protegrity ESA appliance from an image that is provided by Protegrity. You must create a VM instance using the image provided in the following two methods:
- Creating a VM instance from the Protegrity ESA appliance image provided.
- Creating a VM instance from a disk that is created with an image of the Protegrity ESA appliance.
2.5.1 - Creating a VM Instance from an Image
This section describes how to create a Virtual Machine (VM) from an ESA image provided to you.
To create a VM from an image:
Ensure that you are logged in to the GCP.
Click Compute Engine.The Compute Engine screen appears.
Click CREATE INSTANCE.The Create an instance screen appears.
Enter the following information:
- Name: Name of the instance
- Description: Description for the instance
Select the region and zone from the Region and Zone drop-down menus respectively.
Under the Machine Type area, select the processor and memory configurations based on the requirements.
Click Customize to customize the memory, processor, and core configuration.
Under the Boot disk area, click Change to configure the boot disk.
The Boot disk screen appears.
Click Custom Images.
Under the Show images from drop-down menu, select the project where the image of the ESA is provided.
Select the image for the root partition.
Select the required disk type from the Boot disk type drop-down list.
Enter the size of the disk in the Size (GB) text box.
Click Select.
The disk is configured.
Under the Identity and API access area, select the account from the Service Account drop-down menu to access the Cloud APIs.
Depending on the selection, select the access scope from the Access Scope option.
Under the Firewall area, select the Allow HTTP traffic or Allow HTTPS traffic checkboxes to permit HTTP or HTTPS requests.
Click Networking to set the networking options.
Enter data in the Network tags text box.
Click Add network interface to add a network interface.
If you want to edit a network interface, then click the edit icon (
 ).
).
Click Create to create and start the instance.
2.5.2 - Creating a VM Instance from a Disk
You can create disks using the image provided for your account. You must create a boot disk using the OS image. After creating the disk, you can attach it to an instance.
This section describes how to create a disk using an image. Using this disk, you then create a VM instance.
Creating a Disk from the GCP Image
Perform the following steps to create a disk using an image.
Before you begin
Ensure that you have access to the Protegrity ESA appliance images.
How to create a disk using a GCP Image
To create a disk of the Protegrity ESA appliance:
Access the GCP domain at the following URL: https://cloud.google.com/
The GCP home screen appears.
Click Console.
The GCP login screen appears.
On the GCP login screen, enter the following details:
- User Name
- Password
Click Sign in.
After successful authentication, the GCP management console screen appears.
Click Go to the Compute Engine dashboard under the Compute Engine area.
The Dashboard screen appears
Click Disks on the left pane.
The Disks screen appears.
Click CREATE DISK to create a new disk.
The Create a disk screen appears.
Enter the following details:
- Name: Name of the disk
- Description: Description for the disk
Select one of the following options from the Type drop-down menu:
- Standard persistent disk
- SSD persistent disk
Select the region and zone from the Region and Zone drop-down menus respectively.
Select one of the following options from the Source Type option:
Image: The image of the Protegrity ESA appliance that is provided.
Select the image from the Source Image drop-down menu.
Snapshot: The snapshot of a disk.
Blank: Create a blank disk.
Enter the size of the disk in the Size (GB) text box.
Select Google-managed key from the Encryption option.
Click Create.
The disk is created.
Creating a VM Instance from a Disk
This section describes how to create a VM instance from a disk that is created from an image.
For more information about creating a disk, refer to section Creating a Disk from the GCP Image.
To create a VM instance from a disk:
Ensure that you are logged in to the GCP Console.
Click Compute Engine.
The Compute Engine screen appears.
Click CREATE INSTANCE.
The Create an instance screen appears.
Enter information in the following text boxes:
- Name
- Description
Select the region and zone from the Region and Zone drop-down menus respectively.
Under the Machine Type section, select the processor and memory configuration based on the requirements.
Click Customize to customize your memory, processor and core configuration.
Under Boot disk area, click Change to configure the boot disk.
The Boot disk screen appears.
- Click Existing Disks.
- Select the required disk created with the Protegrity ESA appliance image.
- Click Select.
Under Firewall area, select the Allow HTTP traffic or Allow HTTPS traffic checkboxes to permit HTTP or HTTPS requests.
Click Create to create and start the instance.
2.5.3 - Accessing the Appliance
After setting up the virtual machine, you can access the ESA through the IP address that is assigned to the virtual machine. It is recommended to access the ESA with the administrative credentials.
If the number of unsuccessful password attempts exceed the defined value in the password policy, the account gets locked.
For more information on the password policy for the admin and viewer users, refer here, and for the root and local_admin OS users, refer here.
2.6 - Finalizing the ESA Installation on the Instance
When you install the ESA, it generates multiple security identifiers such as, keys, certificates, secrets, passwords, and so on. These identifiers ensure that sensitive data is unique between two appliances in a network. When you receive a Protegrity ESA appliance image, the identifiers are generated with certain values. If you use the security identifiers without changing their values, then security is compromised and the system might be vulnerable to attacks.
Rotating Appliance OS keys to finalize installation
Using the Rotate Appliance OS Keys, you can randomize the values of these security identifiers for an ESA. During the finalization process, you run the key rotation tool to secure your ESA.
If you do not complete the finalization process, then some features of the ESA may not be functional including the Web UI.
For example, if the OS keys are not rotated, then you might not be able to add appliances to a Trusted Appliances Cluster (TAC).
For information about the default passwords, refer the Release Notes 10.1.0.
Finalizing ESA Installation
You can finalize the installation of the ESA after signing in to the CLI Manager.
Before you begin
Ensure that the finalization process is initiated from a single session only. If you start finalization simultaneously from a different session, then the Finalization is already in progress. message appears. You must wait until the finalization of the instance is successfully completed.
Additionally, ensure that the ESA session is not interrupted. If the session is interrupted, then the instance becomes unstable and the finalization process is not completed on that instance.
To finalize ESA installation:
Sign in to the ESA CLI Manager of the instance created using the default administrator credentials.
The following screen appears.
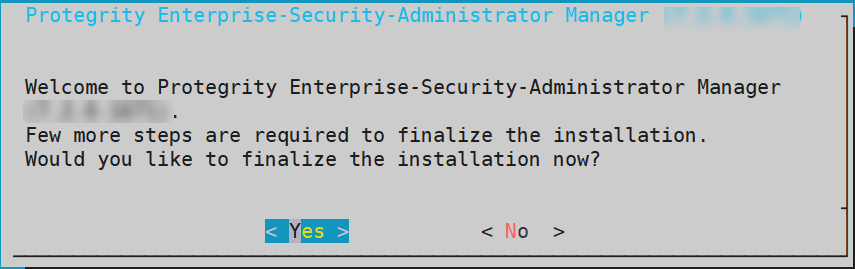
Select Yes to initiate the finalization process.
The screen to enter the administrative credentials appears.
If you select No, then the finalization process is not initiated.
To manually initiate the finalization process, navigate to Tools > Finalize Installation and press ENTER.
Enter the credentials for the admin user and select OK.
A confirmation screen to rotate the appliance OS keys appears.
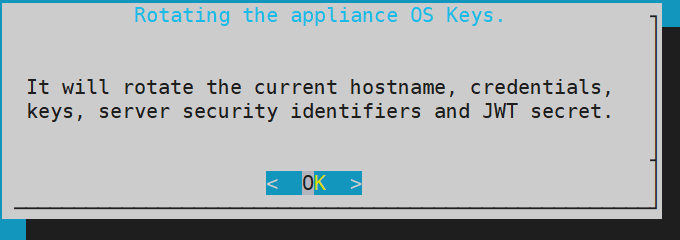
Select OK to rotate the appliance OS keys.
The following screen appears.
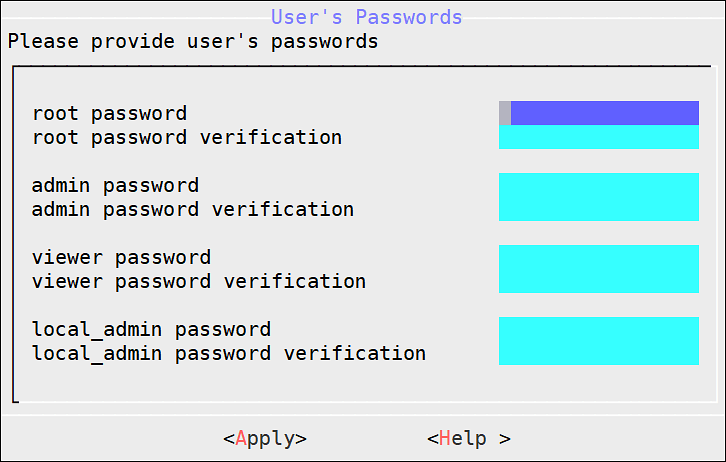
To update the user passwords, provide the credentials for the following users:
- root
- admin
- viewer
- local_admin
Select Apply.
The user passwords are updated and the appliance OS keys are rotated.
The finalization process is completed.
2.7 - Deploying the Instance of the Protegrity Appliance with the Protectors
You can configure the various protectors that are a part of the Protegrity Data Security Platform with the instance of the ESA appliance running on AWS.
Depending on the Cloud-based environment which hosts the protectors, the protectors can be configured with the instance of the ESA appliance in one of the following ways:
- If the protectors are running on the same VPC as the instance of the ESA appliance, then the protectors need to be configured using the internal IP address of the ESA appliance within the VPC.
- If the protectors are running on a different VPC than that of the instance of the ESA appliance, then the VPC of the instance of the ESA needs to be configured to connect to the VPC of the protectors.
2.8 - Backing up and Restoring Data on GCP
You can use a snapshot of an instance or a disk to backup or restore information in case of failures. A snapshot represents a state of an instance or disk at a point in time.
Creating a Snapshot of a Disk on GCP
This section describes the steps to create a snapshot of a disk.
To create a snapshot on GCP:
On the Compute Engine dashboard, click Snapshots.
The Snapshots screen appears.
Click Create Snapshot.
The Create a snapshot screen appears.
Enter information in the following text boxes.
- Name - Name of the snapshot.
- Description – Description for the snapshot.
Select the required disk for which the snapshot is to be created from the Source Disk drop-down list.
Click Add Label to add a label to the snapshot.
Enter the label in the Key and Value text boxes.
Click Add Label to add additional tags.
Click Create.
Ensure that the status of the snapshot is set to completed.
Ensure that you note the snapshot id.
Restoring from a Snapshot on GCP
This section describes the steps to restore data using a snapshot.
Before you begin
Ensure that a snapshot of the disk was created before beginning this process.
How to restore data using a snapshot
To restore data using a snapshot on GCP:
Navigate to Compute Engine > VM instances.
The VM instances screen appears.
Select the required instance.
The screen with instance details appears.
Stop the instance.
After the instance is stopped, click EDIT.
Under the Boot Disk area, remove the existing disk.
Click Add Item.
Select the Name drop-down list and click Create a disk.
The Create a disk screen appears.
Under Source Type area, select the required snapshot.
Enter the other details, such as, Name, Description, Type, and Size (GB).
Click Create.
The snapshot of the disk is added in the Boot Disk area.
Click Save.
The instance is updated with the new snapshot.
2.9 - Increasing Disk Space on the Appliance
After creating an instance on GCP, you can add a disk to your appliance.
To add a disk to a VM instance:
Ensure that you are logged in to the GCP Console.
Click Compute Engine.
The Compute Engine screen appears.
Select the instance.
The VM instance details screen appears.
Click EDIT.
Under Additional disks, click Add new disk.
Enter the disk name in the Name field box.
Select the disk permissions from the Mode option.
If you want to delete the disk or keep the disk after the instance is created, select the required option from the Deletion rule option.
Enter the disk size in GB in the Size (GB) field box.
Click Done.
Click Save.
The disk is added to the VM instance.
3 - Installing Protegrity Appliances on Azure
Azure is a cloud computing service offered by Microsoft, which provides services for compute, storage, and networking. It also provides software, platform, and infrastructure services along with support for different programming languages, tools, and frameworks.
The Azure cloud platform includes the following components:
3.1 - Verifying Prerequisites
This section describes the prerequisites, including the hardware and network requirements, for installing and using Protegrity ESA appliances on Azure.
Prerequisites
The following prerequisites are essential to install the Protegrity ESA appliances on Azure:
- Sign in URL for the Azure account
- Authentication credentials for the Azure account
- Working knowledge of Azure
- Access to the My.Protegrity portal
Before you begin:
Ensure that you use the following order to create a virtual machine on Azure:
| Order | Description |
|---|---|
| 1 | Create a Resource Group |
| 2 | Create a Storage Account |
| 3 | Create a Container |
| 4 | Obtain the Azure BLOB |
| 5 | Create an image from the BLOB |
| 6 | Create a VM from the image |
Hardware Requirements
As the Protegrity ESA appliances are hosted and run on Azure, the hardware requirements are dependent on the configurations provided by Microsoft. However, these requirements can change based on the customer requirements and budget. The actual hardware configuration depends on the actual usage or amount of data and logs expected.
The minimum recommendation for an ESA appliance is 8 CPU cores and 32 GB memory. This option is available under the Standard_D8s_v3 option on Azure.
For more information about the hardware requirements of ESA, refer here.
Network Requirements
The Protegrity ESA appliances on Azure are provided with an Azure virtual networking environment. The virtual network enables you to access other instances of Protegrity resources in your project.
For more information about configuring Azure virtual network, refer here.
3.2 - Azure Cloud Utility
The Azure Cloud Utility is an appliance component that is available for supporting features specific to Azure Cloud Platform. For Protegrity ESA appliances, this component must be installed to utilize the services of Azure Accelerated Networking and Azure Linux VM agent. If you are utilizing the Azure Accelerated Networking or Azure Linux VM agent, then it is recommended to not uninstall this component.
When you upgrade or install the ESA from an Azure v10.1.0 blob, the Azure Cloud Utility is installed automatically in the appliance.
3.3 - Setting up Azure Virtual Network
The Azure virtual network is a service that provides connectivity to the virtual machine and services on Azure. You can configure the Azure virtual network by specifying usable IP addresses. You can also create and configure subnets, network gateways, and security settings.
For more information about setting up Azure virtual network, refer to the Azure virtual network documentation at:
https://docs.microsoft.com/en-us/azure/virtual-network/virtual-networks-overview
If you are using the ESA or the DSG appliance with Azure, ensure that the inbound and outbound ports of the appliances are configured in the virtual network.
For more information about the list of inbound and outbound ports, refer to section Open Listening Ports.
3.4 - Creating a Resource Group
Resource Groups in Azure are a collection of multiple Azure resources, such as virtual machines, storage accounts, virtual networks, and so on. The resource groups enable managing and maintaining the resources as a single entity.
For more information about creating resource groups, refer to the Azure resource group documentation at:
https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-portal
3.5 - Creating a Storage Account
Azure storage accounts contain all the Azure storage data objects, such as disks, blobs, files, queues, and tables. The data in the storage accounts are scalable, secure, and highly available.
For more information about creating storage accounts, refer to the Azure storage accounts documentation at:
https://docs.microsoft.com/en-us/azure/storage/common/storage-quickstart-create-account
3.6 - Creating a Container
The data storage objects in a storage account are stored in a container. Similar to directories in a file system, the container in Azure contain BLOBS. You add a container in Azure to store the ESA BLOB.
For more information about creating a container, refer to the following link:
https://docs.microsoft.com/en-us/azure/storage/blobs/storage-quickstart-blobs-portal
3.7 - Obtaining the Azure BLOB
In Azure, you can share files across different storage accounts. The ESA that is packaged as a BLOB, is shared across storage accounts on Azure. A BLOB is a data type that is used to store unstructured file formats. Azure supports BLOB storage to store unstructured data, such as audio, text, images, and so on. The BLOB of the ESA is shared by Protegrity to the client’s storage account.
Before creating the instance on Azure, you must obtain the BLOB from the My.Protegrity portal. On the portal, you select the required ESA version and choose Azure as the target cloud platform. You then share the product to your cloud account. The following steps describe how to share the BLOB to your cloud account.
Before creating the instance on AWS, you must obtain the image from the My.Protegrity portal. On the portal, you select the required ESA version and choose AWS as the target cloud platform. You then share the product to your cloud account. The following steps describe how to share the AMI to your cloud account.
To obtain and share the BLOB:
Log in to the My.Protegrity portal with your user account.
Click Product Management > Explore Products > Data Protection.
Select the required ESA Platform Version from the drop-down.
The Product Family table will update based on the selected ESA Platform Version.
The ESA Platform Versions listed in drop-down menu reflect all versions. These include versions that were either previously downloaded or shipped within the organization along with any newer versions available thereafter. Navigate to Product Management > My Product Inventory to check the list of products previously downloaded.
The images in this section consider the ESA as a reference. Ensure that you select the required image.
Select the Product Family.
The description box will populate with the Product Family details.
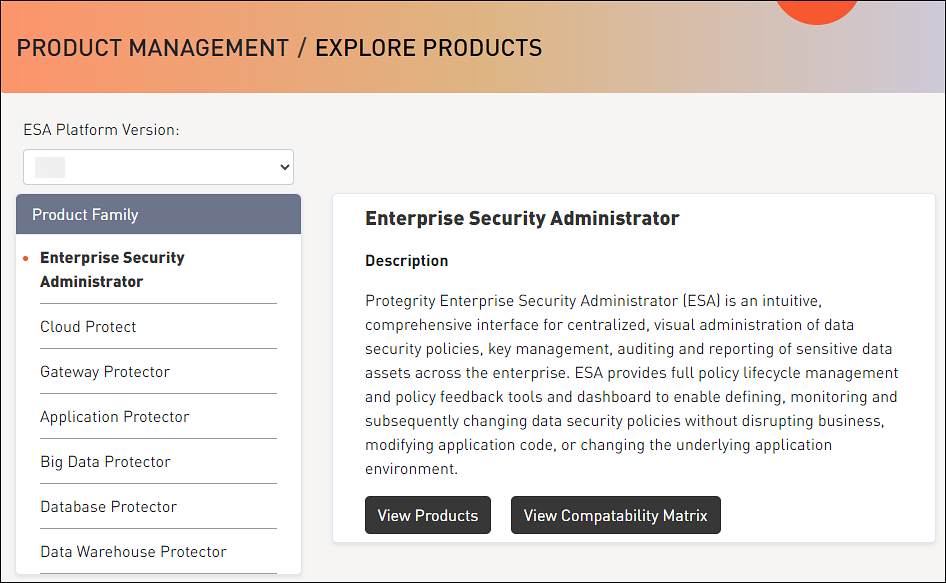
Click View Products to advance to the product listing screen.
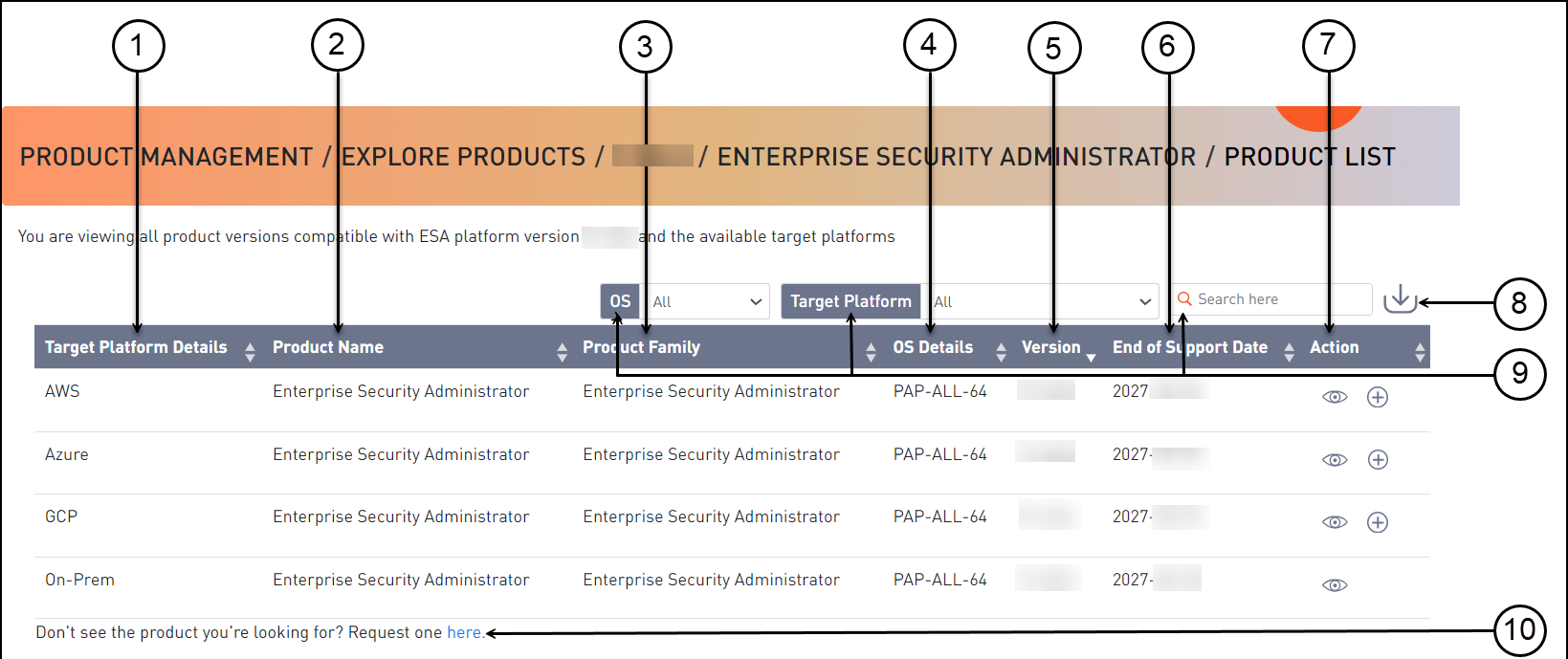
Callout Element Name Description 1 Target Platform Details Shows details about the target platform. 2 Product Name Shows the product name. 3 Product Family Shows the product family name. 4 OS Details Shows the operating system name. 5 Version Shows the product version. 6 End of Support Date Shows the final date that Protegrity will provide support for the product. 7 Action Click the View icon (  ) to open the Product Detail screen.
) to open the Product Detail screen.8 Export as CSV Downloads a .csv file with the results displayed on the screen. 9 Search Criteria Type text in the search field to specify the search filter criteria or filter the entries using the following options:- OS- Target Platform 10 Request one here Opens the Create Certification screen for a certification request. Select the Azure cloud target platform you require and click the View icon (
 ) from the Action column.
) from the Action column.The Product Detail screen appears.

Callout Element Name Description 1 Product Detail Shows the following information about the product:- Product name- Family name- Part number- Version- OS details- Hardware details- Target platform details- End of support date
- Description2 Product Build Number Shows the product build number. 3 Release Type Name Shows the type of build, such as, release, hotfix, or patch. 4 Release Date Shows the release date for the build. 5 Build Version Shows the build version. 6 Actions Shows the following options for download:- Click the Share Product icon (  ) to share the product through the cloud.- Click the Download Signature icon (
) to share the product through the cloud.- Click the Download Signature icon ( ) to download the product signature file.- Click the Download Readme icon (
) to download the product signature file.- Click the Download Readme icon ( ) to download the Release Notes.
) to download the Release Notes.7 Download Date Shows the date when the file was downloaded. 8 User Shows the user name who downloaded the build. 9 Active Deployment Select the check box to mark the software as active. Clear the check box to mark the software as inactive. This option is available only after you download a product.| |10|Product Build Number|Shows the product build number.|
Click the Share Product icon (
 ) to share the desired cloud product.
) to share the desired cloud product.If the access to the cloud products is restricted and the Customer Cloud Account details are not available, then a message appears. The message displays the information that is required and the contact information for obtaining access to cloud share.
A dialog box appears and your available cloud accounts will be displayed.
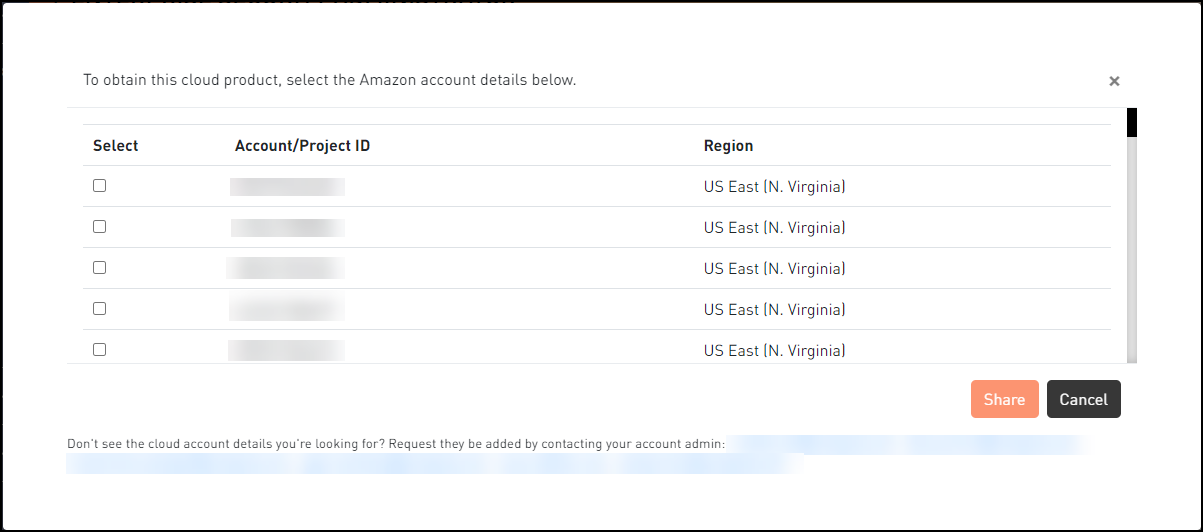
Select your required cloud account in which to share the Protegrity product.
Click Share.
A message box is displayed with the command line interface (CLI) instructions with the option to download a detailed PDF containing the cloud web interface instructions. Additionally, the instructions for sharing the cloud product are sent to your registered email address and to your notification inbox in My.Protegrity.
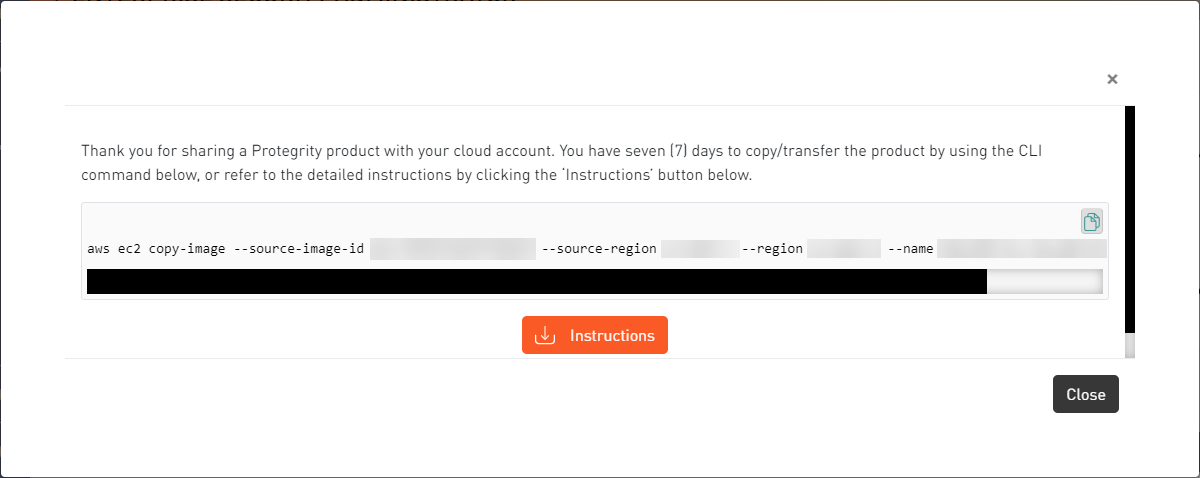
Click the Copy icon (
 ) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
) to copy the command for sharing the cloud product and run the command in CLI. Alternatively, click Instructions to download the detailed PDF instructions for cloud sharing using the CLI or the web interface.
The cloud sharing instruction file is saved in a
.pdfformat. You need a reader, such as, Acrobat Reader to view the file.The Cloud Product will be shared with your cloud account for seven (7) days from the original share date in the My.Protegrity portal.
After the seven (7) day time period, you need to request a new share of the cloud product through My.Protegrity.com.
3.8 - Creating Image from the Azure BLOB
After you obtain the BLOB from Protegrity, you must create an image from the BLOB. The following steps describe the parameters that must be selected to create an image.
To create an image from the BLOB:
Log in to the Azure portal.
Select Images and click Create.
Enter the details in the Resource Group, Name, and Region text boxes.
In the OS disk option, select Linux.
In the VM generation option, select Gen 1.
In the Storage blob drop-down list, select the Protegrity Azure BLOB.
Enter the appropriate information in the required fields and click Review + create.
The image is created from the BLOB.
3.9 - Creating a VM from the Image
After obtaining the image, you can create a VM from it. For more information about creating a VM from the image, refer to the following link.
To create a VM:
Login in to the Azure homepage.
Click Images.
The list of all the images appear.
Select the required image.
Click Create VM.
Enter details in the required fields.
Select SSH public key in the Authentication type option. Do not select the Password based mechanism as an authentication type. Protegrity recommends not using this type as a security measure.
In the Username text box, enter the name of a user. Be aware, this user will not have SSH access to the ESA appliance. Refer to the following section Created OS user and SSH access to appliance for more details.
This user is added as an OS level user in the ESA appliance. Ensure that the following usernames are not provided in the Username text box:
Select the required SSH public key source.
Enter the required information in the Disks, Networking, Management, and Tags sections.
Click Review + Create.
The VM is created from the image.
After the VM is created, you can access the ESA from the CLI Manager or Web UI.
Created OS user and SSH access to appliance
The OS user that is created in step 7 does not have SSH access to the ESA appliance. If you want to provide SSH access to this user, login to the appliance as another administrative user and toggle SSH access. In addition, update the user to permit Linux shell access (/bin/sh).
3.10 - Accessing the Appliance
After setting up the virtual machine, you can access the ESA appliance through the IP address that is assigned to the virtual machine. It is recommended to access the ESA with the administrative credentials.
If the number of unsuccessful password attempts exceed the defined value in the password policy, then the account gets locked.
For more information on the password policy for the admin and viewer users, refer here, and for the root and local_admin OS users, refer here.
3.11 - Finalizing the Installation of Protegrity Appliance on the Instance
When you install the ESA, it generates multiple security identifiers such as, keys, certificates, secrets, passwords, and so on. These identifiers ensure that sensitive data is unique between two appliances in a network. When you receive a Protegrity appliance image, the identifiers are generated with certain values. If you use the security identifiers without changing their values, then security is compromised and the system might be vulnerable to attacks.
Rotating Appliance OS keys to finalize installation
Using Rotate Appliance OS Keys, you can randomize the values of these security identifiers for an ESA appliance. During the finalization process, you run the key rotation tool to secure your ESA appliance.
If you do not complete the finalization process, then some features of the ESA appliance may not be functional including the Web UI.
For example, if the OS keys are not rotated, then you might not be able to add ESA appliances to a Trusted Appliances Cluster (TAC).
For information about the default passwords, refer the Release Notes 10.1.0.
Finalizing ESA Installation
You can finalize the installation of the ESA after signing in to the CLI Manager.
Before you begin
Ensure that the finalization process is initiated from a single session only. If you start finalization simultaneously from a different session, then the Finalization is already in progress. message appears. You must wait until the finalization of the instance is successfully completed.
Additionally, ensure that the ESA appliance session is not interrupted. If the session is interrupted, then the instance becomes unstable and the finalization process is not completed on that instance.
To finalize ESA installation:
Sign in to the ESA CLI Manager of the instance created using the default administrator credentials.
The following screen appears.
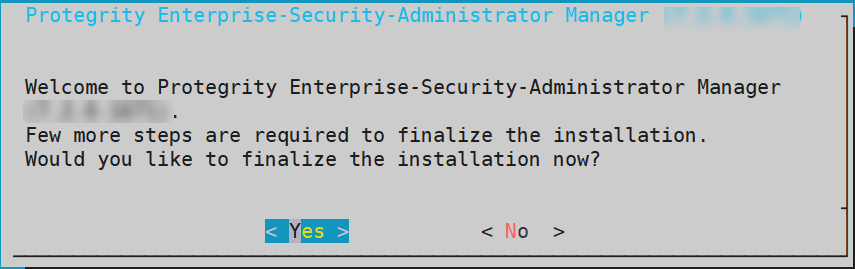
Select Yes to initiate the finalization process.
The screen to enter the administrative credentials appears.
If you select No, then the finalization process is not initiated.
To manually initiate the finalization process, navigate to Tools > Finalize Installation and press ENTER.
Enter the credentials for the admin user and select OK.
A confirmation screen to rotate the appliance OS keys appears.
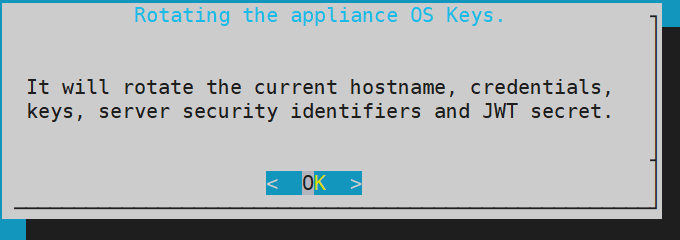
Select OK to rotate the appliance OS keys.
The following screen appears.
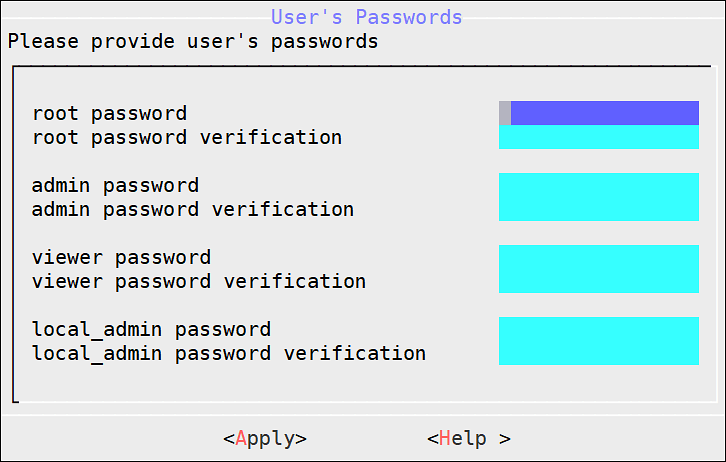
To update the user passwords, provide the credentials for the following users:
- root
- admin
- viewer
- local_admin
Select Apply.
The user passwords are updated and the appliance OS keys are rotated.
The finalization process is completed.
3.12 - Accelerated Networking
Accelerated networking is a feature provided by Microsoft Azure which enables the user to improve the performance of the network. This is achieved by enabling Single-root input/output virtualization (SR-IOV) to a virtual machine.
In a virtual environment, SR-IOV specifies the isolation of PCIe resources to improve manageability and performance. The SR-IOV interface helps to virtualize, access, and share the PCIe resources, such as, the connection ports for graphic cards, hard drives, and so on. This successfully reduces the latency, network jitters and CPU utilization.
As shown in figure below, the virtual switch is an integral part of a network for connecting the hardware and the virtual machine. The virtual switch helps in enforcing the policies on the virtual machine. These policies include access control lists, isolation, network security controls, and so on, and are implemented on the virtual switch. The network traffic routes through the virtual switch and the policies are implemented on the virtual machine. This results in higher latency, network jitters, and higher CPU utilization.
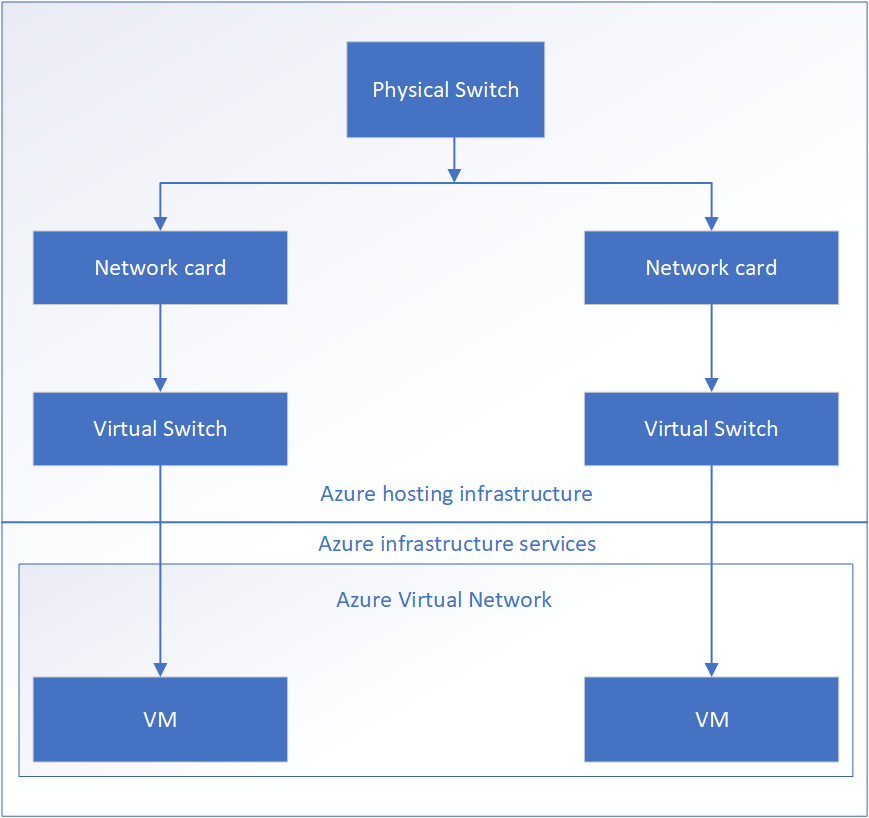
However, in an accelerated network, the policies are applied on the hardware. The network traffic only routes through the network cards directly forwarding it to the virtual machine. The policies are applied on the hardware instead of the virtual switch. This helps the network traffic to bypass the virtual switch and the host while maintaining the policies applied at the host. Reducing the layers of communication between the hardware and the virtual machine helps to improve the network performance.
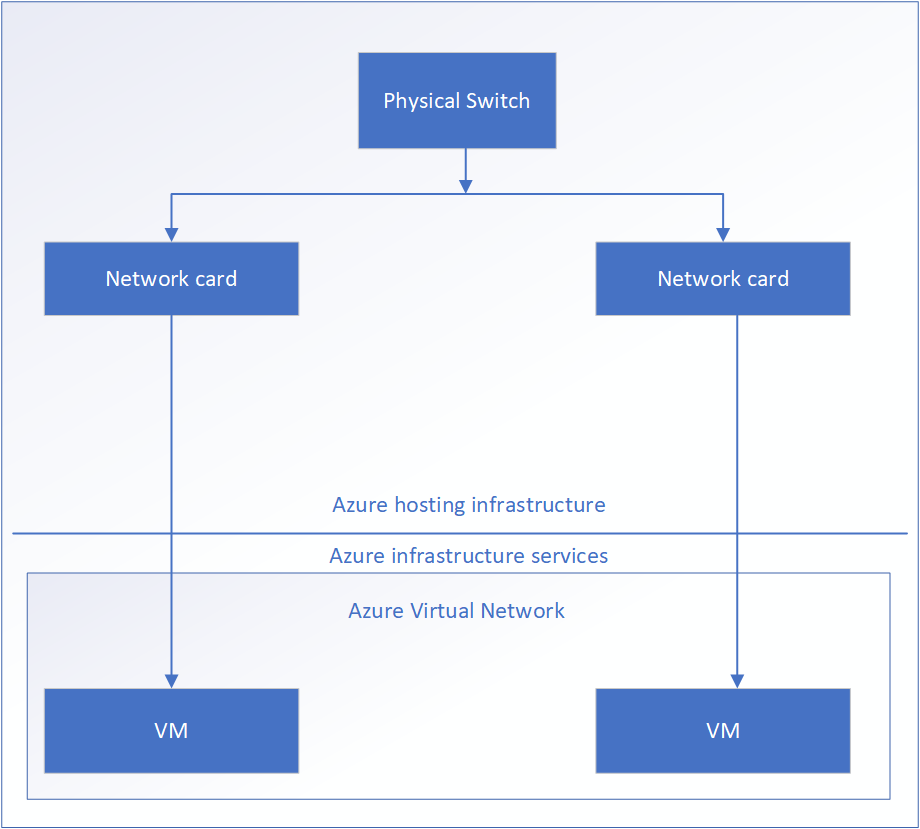
Following are the benefits of accelerated networking:
- Reduced Latency: Bypassing the virtual switch from the data path increases the number of packets which are processed in the virtual machine.
- Reduced Jitter: Bypassing the virtual switch and host from the network reduces the processing time for the policies. The policies are directly implemented on the virtual machine thereby reducing the network jitters caused by the virtual switch.
- CPU Utilization: Applying the policies to the hardware and implementing them directly on the virtual machine reduces the workload on the CPU to process these policies.
Prerequisites
The following prerequisites are essential to enable or disable the Azure Accelerated Networking feature.
A machine with the Azure CLI should be configured. This must be a separate Windows or Linux machine.
For more information about installing the Azure CLI, refer to the following link.
https://docs.microsoft.com/en-us/cli/azure/install-azure-cli?view=azure-cli-latest
The Protegrity ESA appliance must be in the stop (deallocated) state.
The virtual machine must use the supported instance size.
For more information about the supported series of virtual machines for the accelerated networking feature, refer to the Supported Instance Sizes for Accelerated Networking.
Supported Instance Sizes for Accelerated Networking
There are several series of instance sizes used on the virtual machines that support the accelerated networking feature.
These include the following:
- D/DSv2
- D/DSv3
- E/ESv3
- F/FS
- FSv2
- Ms/Mms
The most generic and compute-optimized instance sizes for the accelerated networking feature is with 2 or more vCPUs. However, on the systems with supported hyperthreading features, the accelerated networking feature must have instance sizes with 4 or more vCPUs.
For more information about the supported instance sizes, refer to the following link.
Creating a Virtual Machine with Accelerated Networking Enabled
If you want to enable accelerated networking while creating the instance, then it is achieved only from the Azure CLI. The Azure portal does not provide the option to create an instance with accelerated networking enabled.
For more information about creating a virtual machine with accelerated networking, refer to the following link.
To create a virtual machine with the accelerated networking feature enabled:
From the machine on which the Azure CLI is installed, login to Azure using the following command.
az loginCreate a virtual machine using the following command.
az vm create --image <name of the Image> --resource-group <name of the resource group> --name <name of the new instance> --size <configuration of the instance> --admin-username <administrator username> --ssh-key-values <SSH key path> --public-ip-address "" --nsg <Azure virtual network> --accelerated-networking trueFor example, the table below lists values to create a virtual machine with the following parameters.
Parameter Value Name of the image ProtegrityESAAzure name-of-resource-group MyResourcegroup size Standard_DS3_v2 admin-username admin nsg TierpointAccessDev ssh-key-value ./testkey.pub The virtual machine is created with the accelerated networking feature enabled.
Enabling Accelerated Networking
Perform the following steps to enable the Azure Accelerated Networking feature on the Protegrity ESA appliance.
To enable accelerated networking:
From the machine on which the Azure CLI is installed, login to Azure using the following command.
az loginStop the Protegrity ESA appliance using the following command.
az vm deallocate --resource-group <ResourceGroupName> --name <InstanceName>Parameter Description ResourceGroupName Name of the resource group where the instance is located. InstanceName Name of the instance that you want to stop. Enable accelerated networking on your virtual machine’s network card using the following command.
az network nic update --name <nic-name> --resource-group <ResourceGroupName> --accelerated-networking trueParameter Description nic-name Name of the network interface card attached to the instance where you want to enable accelerated networking. ResourceGroupName Name of the resource group where the instance is located. Start the ESA.
Disabling Accelerated Networking
Perform the following steps to disable the Azure Accelerated Networking features on the Protegrity ESA appliance.
To disable accelerated networking:
From the machine on which the Azure CLI is installed, login to Azure using the following command.
az loginStop the ESA using the following command.
az vm deallocate --resource-group <ResourceGroupName> --name <InstanceName>Parameter Description ResourceGroupName Name of the resource group where the instance is located. InstanceName Name of the instance that you want to stop. Disable accelerated networking on your virtual machine’s network card using the following command.
az network nic update --name <nic-name> --resource-group <ResourceGroupName> --accelerated-networking falseParameter Description nic-name Name of the network interface card attached to the instance where you want to enable accelerated networking. ResourceGroupName Name of the resource group where the instance is located. Start the ESA.
Troubleshooting and FAQs for Azure Accelerated Networking
This section lists the Troubleshooting and FAQs for the Azure Accelerated Networking feature.
What is the recommended number of virtual machines required in the Azure virtual network?
It is recommended to have at least two or more virtual machines in the Azure virtual network.
Can I stop or deallocate my machine from the Web UI?
Yes. You can stop or deallocate your machine from the Web UI. Navigate to the Azure instance details page and click Stop from the top ribbon.
Can I uninstall the Cloud Utility Azure if the accelerated networking feature is enabled?
It is recommended to disable the accelerated networking feature before uninstalling the Cloud Utility Azure.
How do I verify that the accelerated networking is enabled on my machine?
Perform the following steps:
Login to the CLI manager.
Navigate to Administration > OS Console.
Enter the root credentials.
Verify that the Azure Accelerated Networking feature is enabled by using the following commands.
# lspci | grep “Virtual Function”Confirm the Mellanox VF device is exposed to the VM with the lspci command.
The following is a sample output:
001:00:02.0 Ethernet controller: Mellanox Technologies MT27500/MT27520 Family [ConnectX-3/ConnectX-3 Pro Virtual Function]
# ethtool -S ethMNG | grep vfCheck for activity on the virtual function (VF) with the ethtool -S eth0 | grep vf_ command. If you receive an output similar to the following sample output, accelerated networking is enabled and working. The value of the packets and bytes should not be zero`
vf_rx_packets: 992956 vf_rx_bytes: 2749784180 vf_tx_packets: 2656684 vf_tx_bytes: 1099443970 vf_tx_dropped: 0
How do I verify from the Azure Web portal that the accelerated networking is enabled on my machine?
Perform the following steps:
- From the Azure Web portal, navigate to the virtual machine’s details page.
- From the left pane, navigate to Networking.
- If there are multiple NICs, then select the required NIC.
- Verify that the accelerated networking feature is enabled from the Accelerated Networking field.
Can I use the Cloud Shell on the Azure portal for enabling or disabling the accelerated networking feature?
Yes, you can use the Cloud Shell for enabling or disabling the accelerated networking. For more information about the pricing of the cloud shell, refer to the following link.
https://azure.microsoft.com/en-in/pricing/details/cloud-shell
How can I enable the accelerated networking feature using the Cloud Shell?
Perform the following steps to enable the accelerated networking feature using the Cloud Shell:
From the Microsoft Azure portal, launch the Cloud Shell.
Stop the ESA using the following command.
az vm deallocate --resource-group <ResourceGroupName> --name <InstanceName>Enable accelerated networking on your virtual machine’s network card using the following command.
az network nic update --name <nic-name> --resource-group <ResourceGroupName> --accelerated-networking trueStart the ESA.
How can I disable the accelerated networking feature using the Cloud Shell?
Perform the following steps to disable the accelerated networking feature using the Cloud Shell:
From the Microsoft Azure portal, launch the Cloud Shell.
Stop the ESA using the following command.
az vm deallocate --resource-group <ResourceGroupName> --name <InstanceName>Enable accelerated networking on your virtual machine’s network card using the following command.
az network nic update --name <nic-name> --resource-group <ResourceGroupName> --accelerated-networking falseStart the ESA.
Are there any specific regions where the accelerated networking feature is supported?
The accelerated networking feature is supported in all public Azure regions and Azure government clouds. For more information about the supported regions, refer to the following link:
https://docs.microsoft.com/en-us/azure/virtual-network/create-vm-accelerated-networking-cli#regions
Is it necessary to stop (deallocate) the machine to enable or disable the accelerated networking feature?
Yes. It is necessary to stop (deallocate) the machine to enable or disable the accelerated networking feature.This is because if the machine is not in the stop (deallocate) state, then it may cause the value of the vf packets to freeze. This results in an unexpected behaviour of the machine.
Is there any additional cost for using the accelerated networking feature?
No. There is no additional cost required for using the accelerated networking feature. For more information about the costing, contact Protegrity Support.
3.13 - Backing up and Restoring VMs on Azure
On Azure, you can prevent unintended loss of data by backing up your virtual machines. Azure allows you to optimize your backup by providing different levels of consistency. Similarly, the data on the virtual machines can be easily restored to a stable state. You can back up a virtual machine using the following two methods:
- Creating snapshots of the disk
- Using recovery services vaults
This following sections describe how to create and restore backups using the two mentioned methods.
Backing up and Restoring using Snapshots of Disks
The following sections describe how to create snapshots of disks and recover them on virtual machines. This procedure of backup and recovery is applicable for virtual machines that are created from disks and custom images.
Creating a Snapshot of a Virtual Machine on Azure
To create a snapshot of a virtual machine:
Sign in to the Azure homepage.
On the left pane, select Virtual machines.
The Virtual machines screen appears.
Select the required virtual machine and click Disks.
The details of the disk appear.
Select the disk and click Create Snapshot.
The Create Snapshot screen appears.
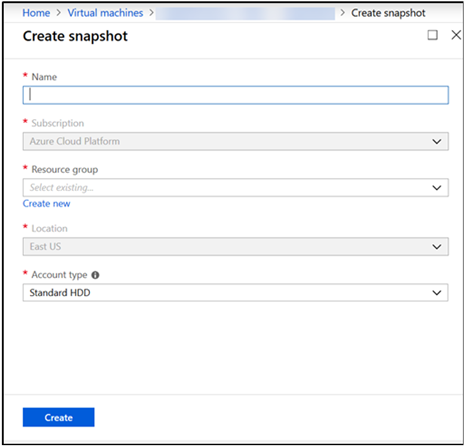
Enter the following information:
- Name: Name of the snapshot
- Subscription: Subscription account for Azure
Select the required resource group from the Resource group drop-down list.
Select the required account type from the Account type drop-down list.
Click Create.
The snapshot of the disk is created.
Restoring from a Snapshot on Azure
This section describes the steps to restore a snapshot of a virtual machine on Azure.
Before you begin
Ensure that the snapshot of the machine is taken.
How to restore from a snapshot on Azure
To restore a virtual machine from a snapshot:
On the Azure Dashboard screen, select Virtual Machine.
The screen displaying the list of all the Azure virtual machines appears.
Select the required virtual machine.
The screen displaying the details of the virtual machine appears.
On the left pane, under Settings, click Disks.
Click Swap OS Disk.
The Swap OS Disk screen appears.
Click the Choose disk drop-down list and select the snapshot created.
Enter the confirmation text and click OK.
The machine is stopped and the disk is successfully swapped.
Restart the virtual machine to verify whether the snapshot is available.
Backing up and Restoring using Recovery Services Vaults
Recovery services vault is an entity that stores backup and recovery points. They enable you to copy the configuration and data from virtual machines. The benefit of using recovery services vaults is that it helps organize your backups and minimize the overhead of management. It comes with enhanced capabilities of backing up data without compromising on data security. These vaults also allow you to create backup polices for virtual machines, thus ensuring integrity and protection. Using recovery services vaults, you can retain recovery points of protected virtual machines to restore them at a later point in time.
For more information about Recovery services vaults, refer to the following link:
https://docs.microsoft.com/en-us/azure/backup/backup-azure-recovery-services-vault-overview
Before you begin
This process of backup and restore is applicable only for virtual machines that are created from a custom image.
Creating Recovery Services Vaults
Before starting with the backup procedure, you must create a recovery services vault.
Before you begin
Ensure that you are aware about the pricing and role-based access before proceeding with the backup.
For more information about the pricing and role-based access, refer to the following links:
To create a recovery services vault:
Sign in to the Azure homepage.
On the Azure Dashboard screen, search Recovery Services vaults.
The screen displaying all the services vaults appears.
Click Add.
The Create Recovery Services vault screen appears.
Populate the following fields:
- Subscription: Account name under which the recovery services vault is created.
- Resource group: Associate a resource group to the vault.
- Vault name: Name of the vault.
- Region: Location where the data for recovery vault must be stored.
The Welcome to Azure Backup screen appears on the right pane.
Click Review + create .
The recovery services vault is created.
Backing up Virtual Machine using Recovery Services Vault
This section describes how to create a backup of a virtual machine using a Recovery Services Vault. For more information about the backup, refer to the link, https://docs.microsoft.com/en-us/azure/backup/backup-azure-vm-backup-faq
To create a backup of a virtual machine:
Sign in to the Azure homepage.
On the left pane, select Virtual machines.
The Virtual machines screen appears.
Select the required virtual machine.
On the left pane, under the Operations tab, click Backup.
The Welcome to Azure Backup screen appears on the right pane.
From the Recovery Services vault option, choose Select existing and select the required vault.
In the backup policy, you specify the frequency, backup schedule, and so on. From the Choose backup policy option, select a policy from the following options:
- DailyPolicy: Retain the daily backup taken at 9.00 AM UTC for 180 days.
- DefaultPolicy: Retain the daily backup taken at 10.30 AM UTC for 30 days.
- Create backup policy: Customize the backup policy as per your requirements.
Click Enable backup.
A notification stating that backup is initiated appears.
On the Azure Dashboard screen, search Recovery Services vaults.
The screen displaying all the services vaults appears.
Select the required services vault.
The screen displaying the details of the virtual machine appears.
On the center pane, under Protected items, click Backup items.
The screen displaying the different management types vault appears.
Select the required management type.
After the backup is completed, the list displays the virtual machine for which the backup was initiated.
Restoring a Virtual Machine using Recovery Services Vaults
In Azure, when restoring a virtual machine using Recovery Services vaults, you have the following two options:
- Creating a virtual machine: Create a virtual machine with the backed up information.
- Replacing an existing: Replace an existing disk on the virtual machine with the backed up information.
Restoring by Creating a Virtual Machine
This section describes how to restore a backup on a virtual machine by creating a virtual machine.
Before you begin
Ensure that the backup process for the virtual machine is completed.
How to restore by creating a virtual machine
To restore a virtual machine by creating a virtual machine:
On the Azure Dashboard screen, search Recovery Services vaults.
The screen displaying all the services vaults appears.
Select the required services vault.
The screen displaying the details of the services vault appears.
On the center pane, under Protected items, click Backup items.
The screen displaying the different management types vault appears.
Select the required management type.
The virtual machines for which backup has been initiated appears.
Select the virtual machine.
The screen displaying the backup details, and restore points appear.
Click Restore VM.
The Select Restore point screen appears.
Choose the required restore point and click OK.
The Restore Configuration screen appears.
If you want to create a virtual machine, click Create new.
Populate the following fields for the respective options:
- Restore type: Create a new virtual machine without overwriting an existing backup.
- Virtual machine name: Name for the virtual machine.
- Resource group: Associate vault to a resource group.
- Virtual network: Associate vault to a virtual network.
- Storage account: Associate vault to a storage account.
Click OK.
Click Restore.
The restore process is initiated. A virtual machine is created with the backed up information.
Restoring a Virtual Machine by Restoring a Disk
This section describes how to restore a backup on a virtual machine by restoring a disk on a virtual machine.
Before you begin
Ensure that the backup process for the virtual machine is completed. Also, ensure that the VM is stopped before performing the restore process.
How to restore a virtual machine by creating a virtual machine
To restore a virtual machine by creating a virtual machine:
On the Azure Dashboard screen, search Recovery Services vaults.
The screen displaying all the services vaults appears.
Select the required services vault.
The screen displaying the details of the services vault appears.
On the center pane, under Protected items, click Backup items.
The screen displaying the different management types vault appears.
Select the required management type.
The virtual machines for which backup has been initiated appears.
Select the virtual machine.
The screen displaying the backup details, and restore points appear.
Click Restore VM.
The Select Restore point screen appears.
Choose the required restore point and click OK.
The Restore Configuration screen appears.
Click Replace existing.
Populate the following fields:
- Restore type: Replace the disk from a selected restore point.
- Staging location: Temporary location used during the restore process.
Click OK.
Click Restore.
The restore process is initiated. The backup is restored by replacing an existing disk on the machine with the disk containing the backed up information.
3.14 - Deploying the ESA Instance with the Protectors
You can configure the various protectors that are a part of the Protegrity Data Security Platform with an instance of the ESA appliance running on Azure.
Depending on the cloud-based environment that hosts the protectors, the protectors can be configured with the instance of the ESA appliance in one of the following ways:
- If the protectors are running on the same virtual network as the instance of the ESA appliance, then the protectors need to be configured using the internal IP address of the ESA appliance within the virtual network.
- If the protectors are running on a different virtual network than that of the ESA appliance, then the virtual network of the ESA instance needs to be configured to connect to the virtual network of the protectors.