Protegrity Data Security Methodology
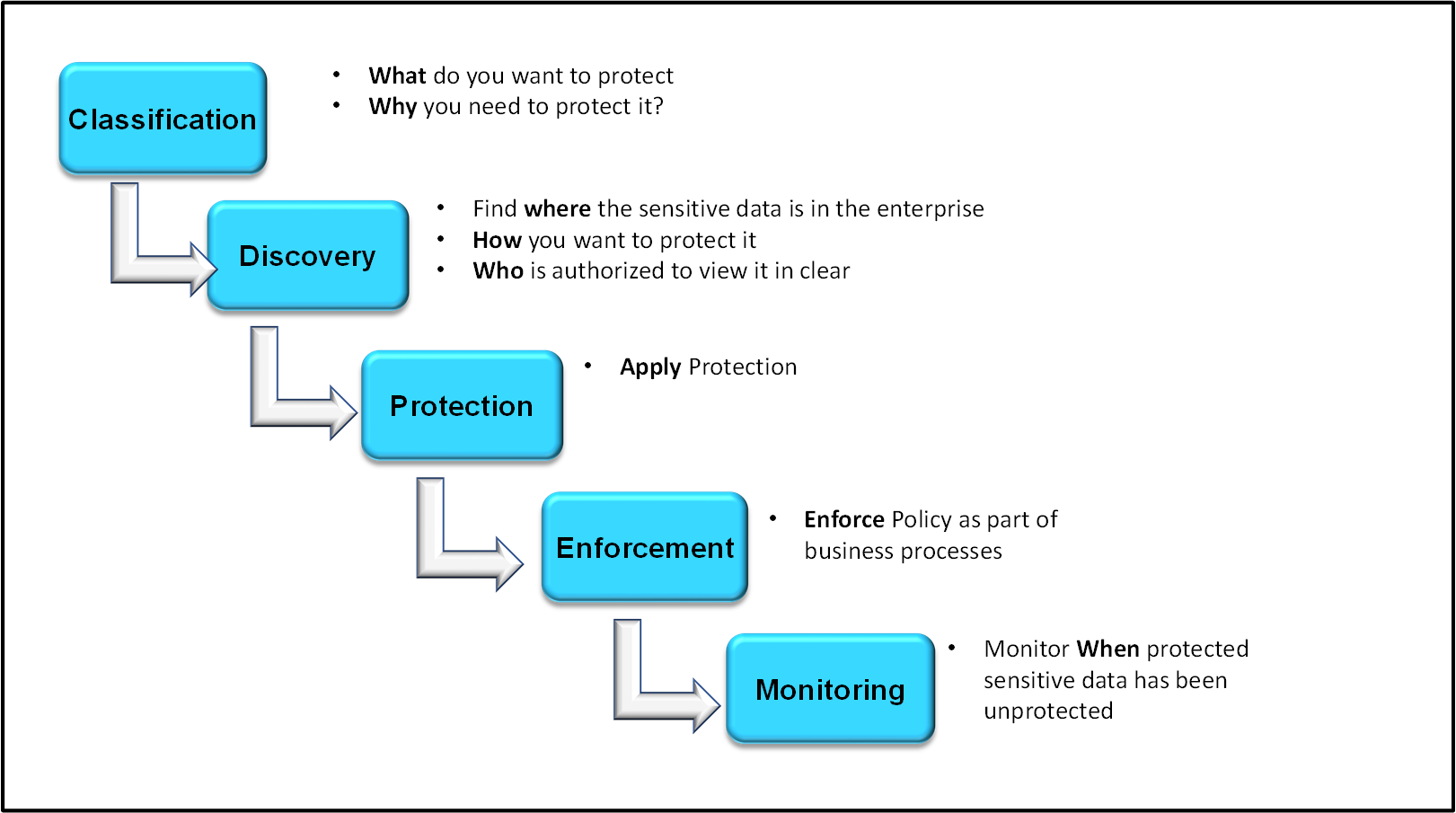
Protegrity’s Data Security Methodology consists of the following stages:
- Classification
- Discovery
- Protection
- Enforcement
- Monitoring
The following diagram summarizes each stage:
Classification
In the Classification stage, determine which data is considered sensitive for the enterprise, and why it needs to be protected. At this stage, it is important to understand the regulatory landscape in which the company is operating and the risk measurement framework associated with the privacy risk. An enterprise may need to meet certain regulatory compliance requirements or laws, such as:
- Payment Card Industry Data Security Standard (PCI DSS)
- Health Information Portability and Accessibility Act (HIPAA)
Discovery
The Discovery stage aims to answer three questions:
- Where is the data?
- How do you want to protect it?
- Who is authorized to view it in the clear?
First, identify the systems storing and processing sensitive data. Obtain this information through manual investigation by utilizing information captured through a data catalog, or by a combination of both. After the overall system architecture is known, devise an integration path using Protegrity components to provide the deepest coverage for the environment. Then, capture business rules to understand the data transformations required, and define requirements for user-level access.
The systems storing and processing sensitive data are specified as Data Stores in the Policy.
Then, decide how the sensitive data that has been identified will be protected. Identify which cryptographic algorithm or protection method matches the sensitivity and type of data in scope. Some data types may require strict protection rules, such as tokenizing credit card numbers. Conversely, some data types such as email addresses may be protected by masking or access monitoring.
The rules protecting every data type are defined as Data Elements in the Policy.
Finally, define roles to identify the users requiring access to sensitive data, and the extent of this access. As a general rule, most users in the organization will not have the authorization to see the data in the clear. Only specific groups of users will require some visibility over sensitive data to perform their job functions. During the Discovery phase, these roles are defined and mapped to the corporate directory services such as LDAP.
Protection
The Protection stage implements the Protegrity Data Security Platform in the enterprise, based on the earlier defined architectural and system requirements.
Enforcement
The Data Security Policy enforcement stage is a critical stage of the process. This is when data security becomes an integral part of the organizational work flow, ensuring its end-to-end protection and access are seamless across systems.
Monitoring
All operations on data generate audit logs that are sent near-real time to the specified collection points. The Security Administrator or Officer must monitor the logs to ensure that the rules are enforced as designed and look for any anomalies. Auditing provides an overview of how the data is being used by the organization. All system and policy-related changes are also captured and made available.
Feedback
Was this page helpful?