The Protegrity AI Team Edition Tech Preview introduces a modern, container-based approach to data protection built on a microservices architecture. It enables organizations to evaluate how Protegrity’s methods, such as, policy management, anonymization, discovery, and semantic controls, integrate into AI and analytics pipelines.
Architecture and Design Principles
Protegrity AI Team Edition delivers core Protegrity capabilities. This includes governance, discovery, protection, privacy, and semantic controls. It is provided in a lightweight, containerized form factor that emphasizes fast deployment, simplified operations, and consistent enforcement of data security policies across environments. It is designed around five engineering goals: ease of deployment, high availability, scalability, extensibility, and maintainability.
| Goal | Implementation Details |
|---|---|
| Ease of Deployment | - OpenTofu templates provision a Kubernetes environment (EKS, ECS, or Docker Compose) with minimal manual intervention. - Helm Charts deploy and configure all components for consistent, reproducible setups. - Because each component runs as a container image, upgrades and patches follow standard CI/CD workflows. |
| High Availability | - Kubernetes manages service health and redundancy automatically. - No Trusted Appliance Cluster (TAC) required. - No external load balancers required. - No manual replication required. |
| Scalability | - The system scales horizontally and vertically through Kubernetes-native scale-up and scale-down mechanisms. - Administrators can adjust resources dynamically as workloads grow or shrink without redeployment. |
| Extensibility | - New capabilities are introduced by adding new container images and Helm configurations. - Allows incremental feature expansion without redesign. |
| Maintainability | - Kubernetes simplifies lifecycle management. - Updating a container image replaces an older version automatically, avoiding downtime and manual patching. |
Core Services
All deployments include a standardized set of common services delivered by a microservices architecture provide routing, security, and audit capabilities for all features and protectors.
| Service | Description |
|---|---|
| Common Ingress Controller | The main entry point for all API and service traffic to the cluster. |
| Certificate Management | Manages and validates TLS certificates for inbound and inter-service communication. |
| Authentication and Authorization | Provides user and service credential validation with role-based access enforcement. |
| Routing to Feature Endpoints | Directs traffic to the appropriate running service or feature container. |
| Insight | Provides logging and auditing capabilities using OpenSearch for event storage and OpenDashboards for visualization and reporting. |
Feature Set
The Tech Preview release of Protegrity AI Team Edition includes a limited but functional subset of capabilities for evaluation.
The various features compatible with Protegrity AI Team Edition are provided here.
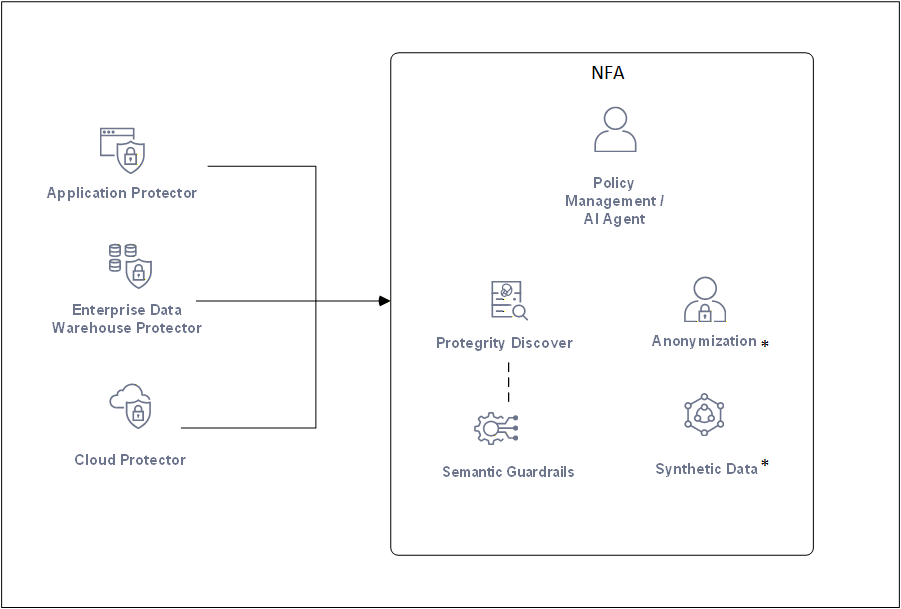
* - Available for purchase as an add-on.
| Feature | Description |
|---|---|
| Policy Management | Define and manage data protection policies that govern tokenization, masking, and anonymization. |
| Data Discovery | Automatically identify structured and unstructured sensitive data through pattern matching and machine learning classification. |
| Semantic Guardrails | Apply contextual and runtime safeguards to AI and analytics workflows to prevent data leakage or misuse. |
| Anonymization | Apply statistical privacy models such as k-anonymity, l-diversity, and t-closeness to sensitive datasets. |
| Synthetic Data | Generate tabular synthetic datasets for development, testing, and AI model validation without exposing real sensitive data. |
Protegrity Protectors
Protegrity AI Team Edition protectors enable organizations to embed data protection directly where data is processed, inside applications, analytics engines, or cloud-native data systems.
Application Protectors
Application protectors provide data protection directly within applications or runtime containers. They are suitable for teams developing secure APIs or microservices that handle sensitive data in languages such as Java, Python, or .NET.
| Name | Description | Part Number |
|---|---|---|
| Immutable Application Protector – Java Container | Protects data within Java-based containers, such as OpenShift and EKS. | ApplicationProtector_Java_RHUBI_K8S |
| Immutable Application Protector – REST Container | Provides REST-based protection services for containerized workloads. | REST_RHUBI-9-64_x86-64_K8S |
| Application Protector – Python | Protegrity Application Protector for Python environments. | ApplicationProtector_Linux-ALL-64_x86-64_PY-3.11 |
| Application Protector – Java | Standard Java runtime protector. | ApplicationProtector_Linux-ALL-64_x86-64_JRE-1.8-64 |
| Application Protector – .NET | Protegrity Application Protector for Microsoft .NET applications. | ApplicationProtector_WIN-ALL-64_x86-64_NET-STD-2.0-64 |
Cloud API Protector
The Cloud API protector extends Protegrity protection to AWS serverless and API-based workloads. It is typically used for securing transient data handled by AWS Lambda or similar function-based architectures.
| Name | Description | Part Number |
|---|---|---|
| CloudProtect – Cloud API – AWS | Protegrity CloudProtect using AWS Serverless Functions. | CP_SVRL-ALL-64_x86-64_AWS.API |
Cloud-Native Data Warehouse Protectors
Cloud-Native Data Warehouse protectors apply field-level protection inside analytics environments such as Snowflake, Redshift, and Athena. These protectors preserve query usability and analytical fidelity while maintaining data confidentiality.
| Name | Description | Part Number |
|---|---|---|
| Cloud Native Data Warehouse Protector – Snowflake | Integrates with Snowflake for secure, compliant analytics across clouds. | CP_SVRL-ALL-64_x86-64_AWS.Snowflake |
| Cloud Native Data Warehouse Protector – Redshift | Provides protection for Amazon Redshift queries and transformations. | CP_SVRL-ALL-64_x86-64_AWS.Redshift |
| Cloud Native Data Warehouse Protector – Athena | Applies protection to Amazon Athena query execution. | CP_SVRL-ALL-64_x86-64_AWS.Athena |
Big Data Protectors
Big Data protectors integrate with large-scale analytics and data lake environments to secure data during ETL, batch, or stream processing operations.
| Name | Description | Part Number |
|---|---|---|
| Big Data Protector – Amazon EMR | Provides data protection within Amazon EMR clusters. | BigDataProtector_Linux-ALL-64_x86-64_EMR-7.x-64 |
| Big Data Protector – Databricks | Enables tokenization and masking for Databricks across AWS, Azure, and GCP. | BigDataProtector_Linux-ALL-64_x86-64_AWS.Databricks-15.4-64 |
| Big Data Protector – CDP Data Hub | Supports Cloudera DataWorks Platform deployments CROSS AWS, Azure, AND GCP. | BigDataProtector_Linux-ALL-64_x86-64_AWS.Generic.CDP-Datahub-7.3-64 |
Features Included in the AI Team Edition
The following features are available with the AI Team Edition:
- Policy Management using AI Agent
- Data Discovery
- Semantic Guardrails
- Any one protector from each of the following families:
- Application protector
- Cloud protector
- Big Data protector
The following features are additional add-ons that must be purchased separately:
- Anonymization
- Synthetic Data