Architecture
The main layers of the Protegrity Browser Protector product are as follows:
- Management Layer: The management layer enables centralized control through Mobile Device Management (MDM) platforms such as Microsoft Intune or Kandji.
- Service Layer: The service layer is the backbone of the browser extension, enabling secure communication, user authentication, and data tokenization.
Centralized Management with MDM Tools
Utilization of MDM tools allows administrators to deploy, configure, and manage the browser extension across multiple devices and users within an organization from a single platform.
By leveraging MDM tools, organizations can ensure consistent and secure use of Protegrity Browser Protector across their environment while minimizing administrative overhead.
The following figure shows the key components of the management layer.
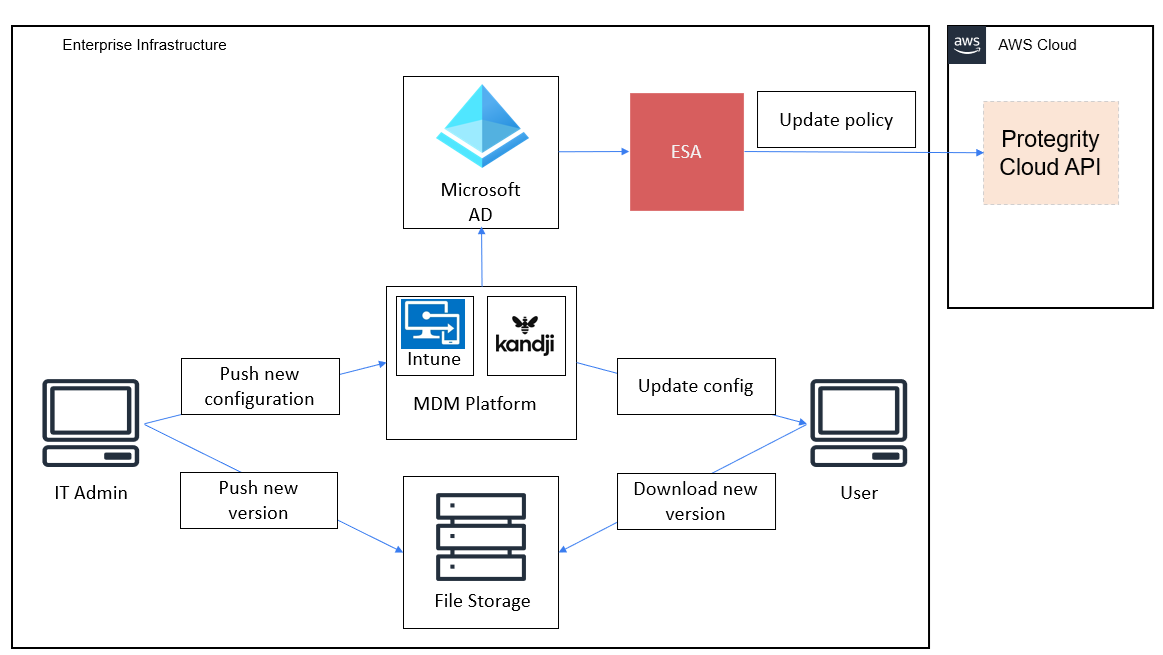
The management layer integrates an MDM platform with Azure Active Directory (Azure AD) to facilitate secure and centralized management of the browser extension across end-user devices. The core components of the Management Layer are as follows:
MDM Platform: Serves as the central system for managing and distributing the browser extension. It ensures that the extension is installed, updated, and configured consistently across all enrolled devices.
Azure AD: Provides identity and access management for users and devices. It ensures that only authorized users and devices can access the browser extension and its features, while enabling centralized control through conditional access policies.
Protegrity ESA: Acts as the central system for defining and managing cryptographic policies for the browser extension, particularly for backend systems such as the Cloud API Protector. ESA administrators define sensitive data elements, like tokenized fields, and user access policies, ensuring that cryptographic operations are governed by enterprise security standards. The ESA policies are used to safeguard sensitive information and enforce access controls.
- Integration with the Browser Configuration File: The list of data elements defined in the ESA must be configured by IT administrators in the browser extension’s configuration file. This configuration file is then distributed to end-user devices through the MDM platform, ensuring that the extension adheres to the cryptographic policies defined in the ESA.
- Seamless Policy Enforcement: By linking the ESA with the extension management layer, the organization ensures that cryptographic policies are consistently enforced across all devices, enhancing security and regulatory compliance.
File Storage Server: Hosts the browser extension code and related resources in a secure and centralized repository. This component allows IT personnel to upload new versions of the extension and push updates to end-user devices seamlessly. By integrating with the MDM platform, file storage enables efficient, automatic updates without manual intervention, minimizing disruption and ensuring operational consistency.
By combining these components, the management layer ensures that the browser extension is securely and consistently deployed, configured, and maintained across all end-user devices, while aligning with enterprise security and compliance standards.
Service Layer Components
The service layer integrates Azure Entra ID and Protegrity Cloud API to deliver secure, scalable authentication and tokenization while ensuring compliance and a seamless user experience.
The following figure shows the key components of the service layer.
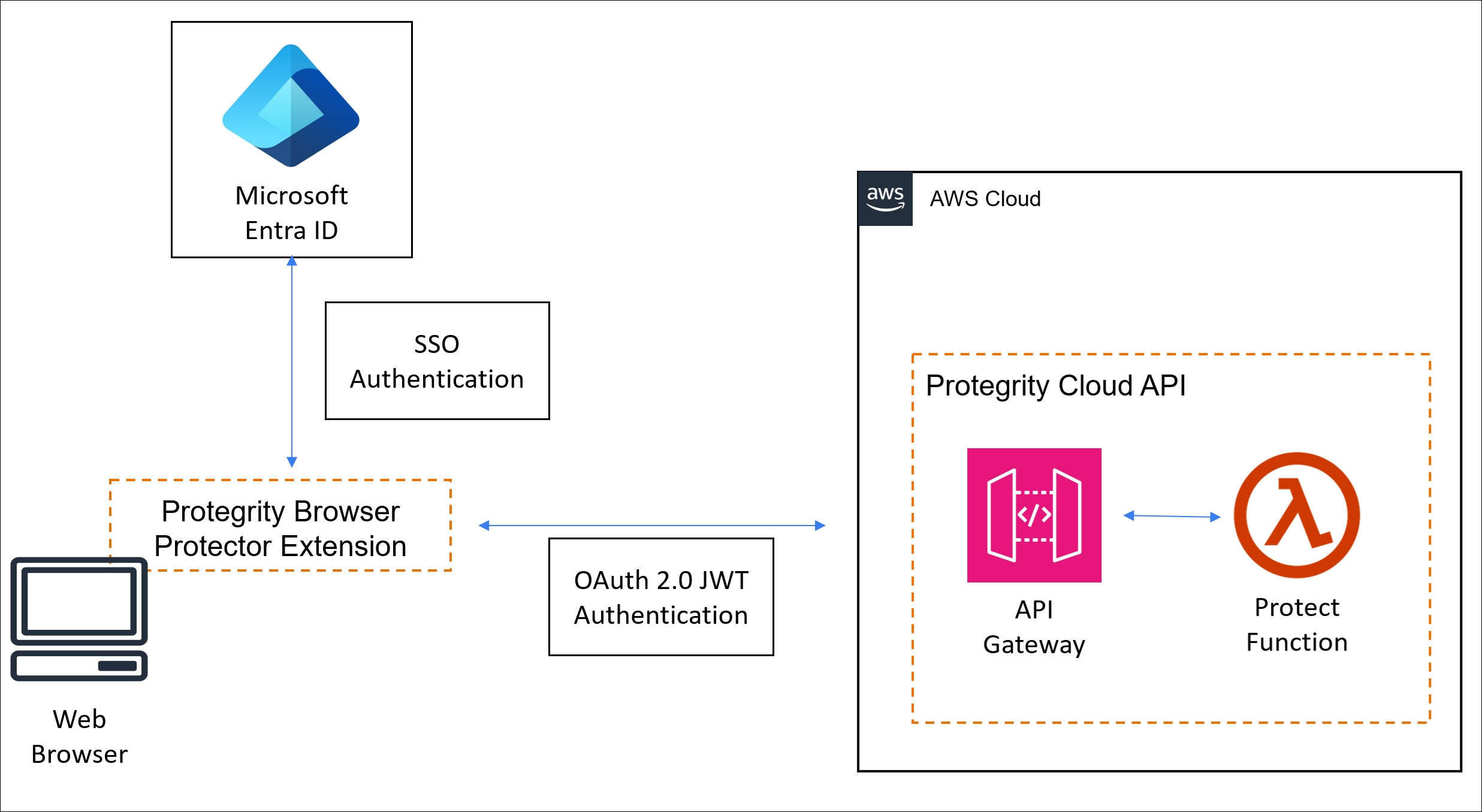
Cloud API Protector
- Performs all tokenization and cryptographic operations on the server, ensuring sensitive data remains protected before being delivered to the browser.
- Tokenized data is delivered to the browser via the web application, ensuring only non-sensitive placeholders are exposed to the client.
Browser Extension
- Enables the user to select specific tokenized text for decryption and rendering.
- Once selected, the extension requests the original data for the chosen tokens from the server, relying on ESA-managed security policies to process the data securely.
Secure Communication
- The extension uses encrypted communication channels, like HTTPS or WebSockets, to interact with the tokenization service and ESA securely.
- All sensitive data remains on the server, with the browser receiving decrypted data only for the user-selected content.
Feedback
Was this page helpful?