This is the multi-page printable view of this section. Click here to print.
AWS
- 1: Cloud API
- 1.1: Overview
- 1.2: Architecture
- 1.3: Installation
- 1.3.1: Prerequisites
- 1.3.2: Pre-Configuration
- 1.3.3: Protect Service Installation
- 1.3.4: Policy Agent Installation
- 1.3.5: Audit Log Forwarder Installation
- 1.3.6:
- 1.3.7:
- 1.3.8:
- 1.3.9:
- 1.4: REST API
- 1.4.1: Authorization
- 1.4.2: HTTP Status Codes
- 1.4.3: Payload Encoding
- 1.4.4: TLS Mutual Authentication
- 1.4.5: v1 Specification
- 1.4.6: Legacy Specification
- 1.5: Performance
- 1.6: Audit Logging
- 1.7: No Access Behavior
- 1.8: Known Limitations
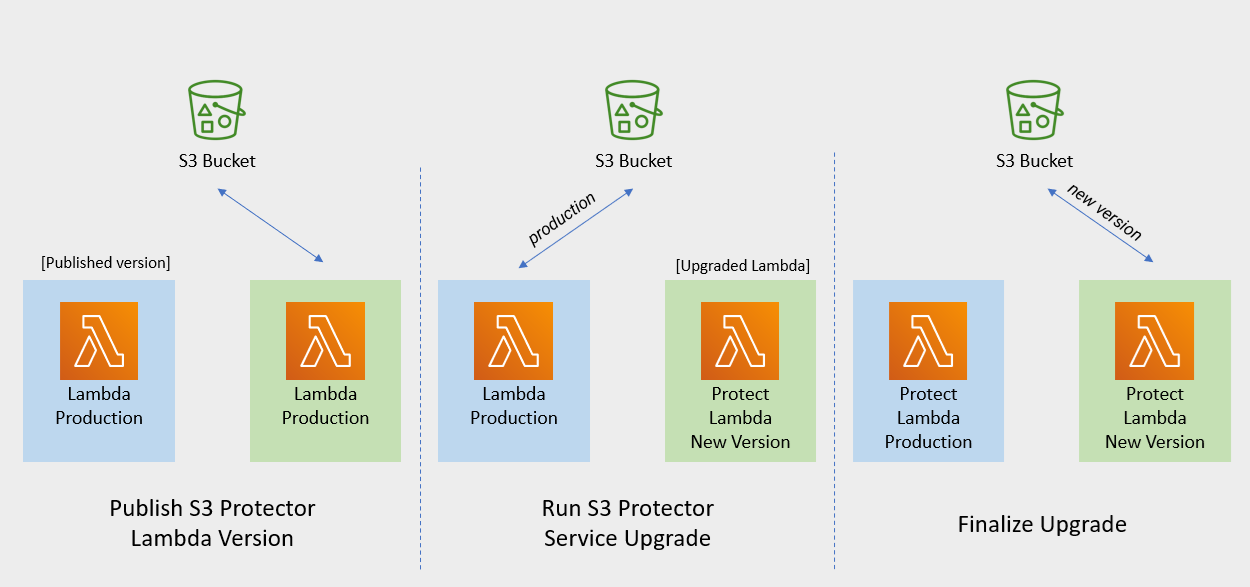
- 1.9: Upgrading To The Latest Version
- 1.10: Appendices
- 1.10.1: ADFS Federation using AWS Cognito User Pools
- 1.10.2: Installing the Policy Agent and Protector in Different AWS Accounts
- 1.10.3: Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
- 1.10.4: Invoke Lambda Directly
- 1.10.5: Policy Agent - Custom VPC Endpoint Hostname Configuration
- 1.10.6: Protection Methods
- 1.10.7: Configuring Regular Expression to Extract Policy Username
- 1.10.8: Associating ESA Data Store With Cloud Protect Agent
- 2: Athena
- 2.1: Overview
- 2.2: Architecture
- 2.3: Installation
- 2.3.1: Prerequisites
- 2.3.2: Pre-Configuration
- 2.3.3: Protect Service Installation
- 2.3.4: Policy Agent Installation
- 2.3.5: Audit Log Forwarder Installation
- 2.3.6:
- 2.3.7:
- 2.3.8:
- 2.3.9:
- 2.3.10:
- 2.3.11:
- 2.3.12:
- 2.4: Understanding Athena Objects
- 2.5: Performance
- 2.6: Audit Logging
- 2.7: No Access Behavior
- 2.8: Known Limitations
- 2.9: Upgrading To The Latest Version
- 2.10: Appendices
- 2.10.1: Sample Athena External Functions
- 2.10.2: Installing the Policy Agent and Protector in Different AWS Accounts
- 2.10.3: Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
- 2.10.4: Security Recommendations
- 2.10.5: Policy Agent - Custom VPC Endpoint Hostname Configuration
- 2.10.6: Protection Methods
- 2.10.7: Configuring Regular Expression to Extract Policy Username
- 2.10.8: Associating ESA Data Store With Cloud Protect Agent
- 3: Redshift
- 3.1: Overview
- 3.2: Architecture
- 3.3: Installation
- 3.3.1: Prerequisites
- 3.3.2: Pre-Configuration
- 3.3.3: Protect Service Installation
- 3.3.4: Policy Agent Installation
- 3.3.5: Audit Log Forwarder Installation
- 3.3.6:
- 3.3.7:
- 3.3.8:
- 3.4: Understanding Redshift Objects
- 3.5: Performance
- 3.6: Audit Logging
- 3.7: No Access Behavior
- 3.8: Known Limitations
- 3.9: Upgrading To The Latest Version
- 3.10: Appendices
- 3.10.1: Installing the Policy Agent and Protector in Different AWS Accounts
- 3.10.2: Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
- 3.10.3: Policy Agent - Custom VPC Endpoint Hostname Configuration
- 3.10.4: Redshift Cross-Account Configuration
- 3.10.5: Sample Redshift External Function
- 3.10.6: Configuring Regular Expression to Extract Policy Username
- 3.10.7: Associating ESA Data Store With Cloud Protect Agent
- 4: Snowflake
- 4.1: Overview
- 4.2: Installation
- 4.2.1: Pre-Configuration
- 4.2.2: Prerequisites
- 4.2.3: Protect Service Installation
- 4.2.4: Policy Agent Installation
- 4.2.5: Audit Log Forwarder Installation
- 4.2.6:
- 4.2.7:
- 4.2.8:
- 4.3: Understanding Snowflake Objects
- 4.3.1: External Functions
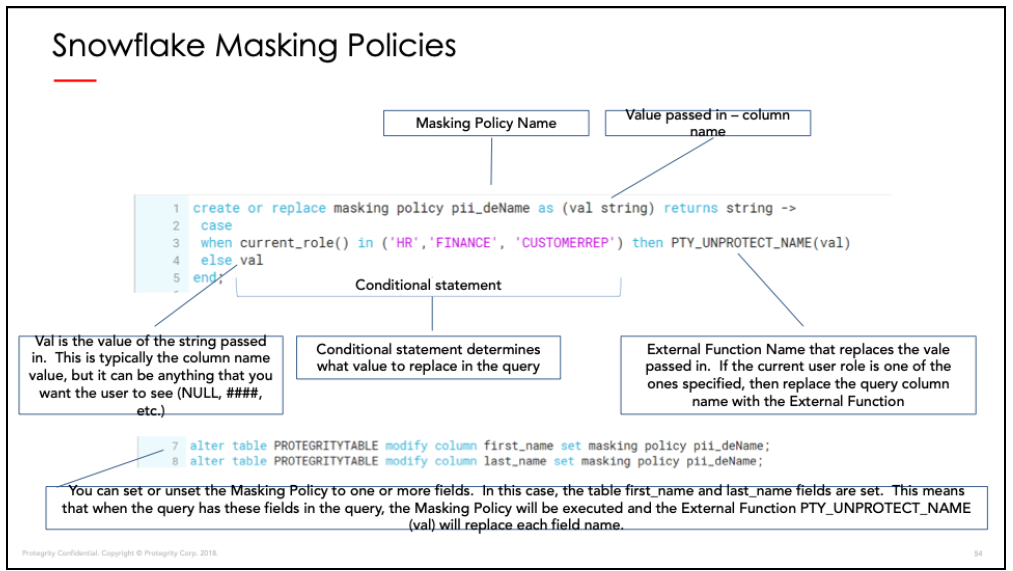
- 4.3.2: Snowflake Masking Policies
- 4.4: Performance
- 4.4.1: Performance Considerations
- 4.4.2: Sample Benchmarks
- 4.4.3: Concurrency
- 4.4.4: Concurrency Tuning
- 4.4.5: Log Forwarder Performance Tuning
- 4.4.6:
- 4.4.7:
- 4.4.8:
- 4.4.9:
- 4.5: Audit Logging
- 4.6: No Access Behavior
- 4.7: Upgrading To The Latest Version
- 4.8: Known Limitations
- 4.9: Appendices
- 4.9.1: Sample Snowflake External Function
- 4.9.2: Installing the Policy Agent and Protector in Different AWS Accounts
- 4.9.3: Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
- 4.9.4: Policy Agent - Custom VPC Endpoint Hostname Configuration
- 4.9.5: Protection Methods
- 4.9.6: Configuring Regular Expression to Extract Policy Username
- 4.9.7: Associating ESA Data Store With Cloud Protect Agent
- 5: Amazon S3
- 5.1: Overview
- 5.2: Architecture
- 5.3: Installation
- 5.3.1: Prerequisites
- 5.3.2: Pre-Configuration
- 5.3.3: S3 Protector Service Installation
- 5.3.4:
- 5.3.5:
- 5.3.6:
- 5.4: Mapping File Configuration
- 5.4.1: Mapping File
- 5.4.2: Column Mapping Rules
- 5.5: Performance
- 5.6: Known Limitations
- 5.7: Upgrading To The Latest Version
- 5.8: Appendices
- 6:
- 7:
- 8:
- 9:
- 10:
- 11:
- 12:
- 13:
- 14:
- 15:
1 - Cloud API
This section describes the high-level architecture of Protegrity Cloud API, installation procedures, and performance guidance. This section focuses on Protegrity specific aspects and should be consumed in conjunction with the corresponding AWS documentation.
This guide may also be used with the Protegrity Enterprise Security Administrator Guide, which explains the mechanism for managing the data security policy.
1.1 - Overview
Solution Overview
Cloud API Protector on AWS is a cloud-native, serverless product for fine-grained data protection. This enables the invocation of Protegrity data protection cryptographic methods in cloud-native serverless technology. The benefits of serverless include rapid auto-scaling, performance, low administrative overhead, and reduced infrastructure costs compared to a server-based solution.
This product provides a data protection API end-point for clients. The product is designed to scale elastically and yield reliable query performance under extremely high concurrent loads. During idle use, the serverless product will scale completely down, providing significant savings in Cloud compute fees.
Protegrity utilizes a data security policy maintained by an Enterprise Security Administrator (ESA), similar to other Protegrity products. Using a simple REST API interface, authorized users can perform both de-identification (protect) and re-identification (unprotect) operations on data. A user’s individual capabilities are subject to privileges and policies defined by the Enterprise Security Administrator.
Analytics on Protected Data
Protegrity’s format and length preserving tokenization scheme make it possible to perform analytics directly on protected data. Tokens are join-preserving so protected data can be joined across datasets. Often statistical analytics and machine learning training can be performed without the need to re-identify protected data. However, a user or service account with authorized security policy privileges may re-identify subsets of data using the Cloud API Protector on AWS service.
Features
Cloud API Protector on AWS incorporates Protegrity’s patent-pending vaultless tokenization capabilities into cloud-native serverless technology. Combined with an ESA security policy, the protector provides the following features:
- Role-based access control (RBAC) to protect and unprotect (re-identify) data depending on the user privileges.
- Policy enforcement features of other Protegrity application protectors.
For more information about the available protection options, such as, data types, Tokenization or Encryption types, or length preserving and non-preserving tokens, refer to Protection Methods Reference.
1.2 - Architecture
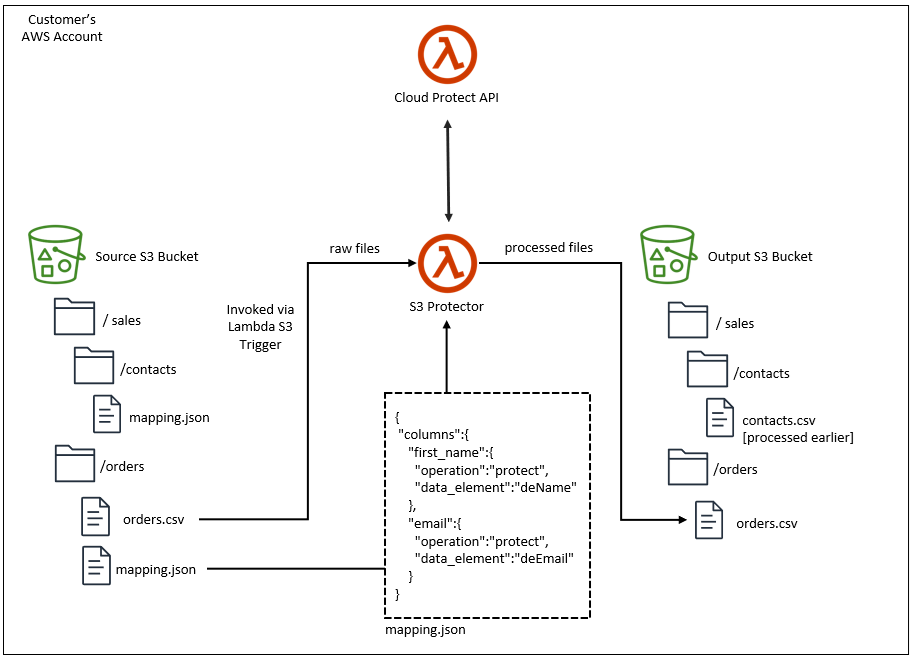
Protector Deployment Architecture
The product will be deployed in the Customer’s AWS account. The product incorporates Protegrity’s vaultless tokenization engine within an AWS Lambda Function. The encrypted data security policy from an ESA is deployed as a static resource through an Amazon Lambda Layer. The policy is decrypted in memory at runtime within the Lambda. This architecture allows Protegrity Serverless to be highly available and scale very quickly without direct dependency on any other Protegrity services.
The product exposes a remote data protection service. Each REST request includes a micro-batch of data to process and the data element type. The function applies the data security policy including user authorization and returns a corresponding response.
When used with an Enterprise Security Administrator (ESA) application, the security policy is synchronized through another serverless component called the Protegrity Policy Agent. The agent operates on a configurable schedule, fetches the policy from the ESA, performs additional envelope encryption using Amazon KMS, and deploys the policy into the Lambda Layer used by the serverless product. This solution can be configured to automatically provision the static policy or the final step can be performed on-demand by an administrator. The policy takes effect immediately for all new requests. There is no downtime for users during this process.
The following diagram shows the high-level architecture described above.
The following diagram shows a reference architecture for synchronizing the security policy from ESA.
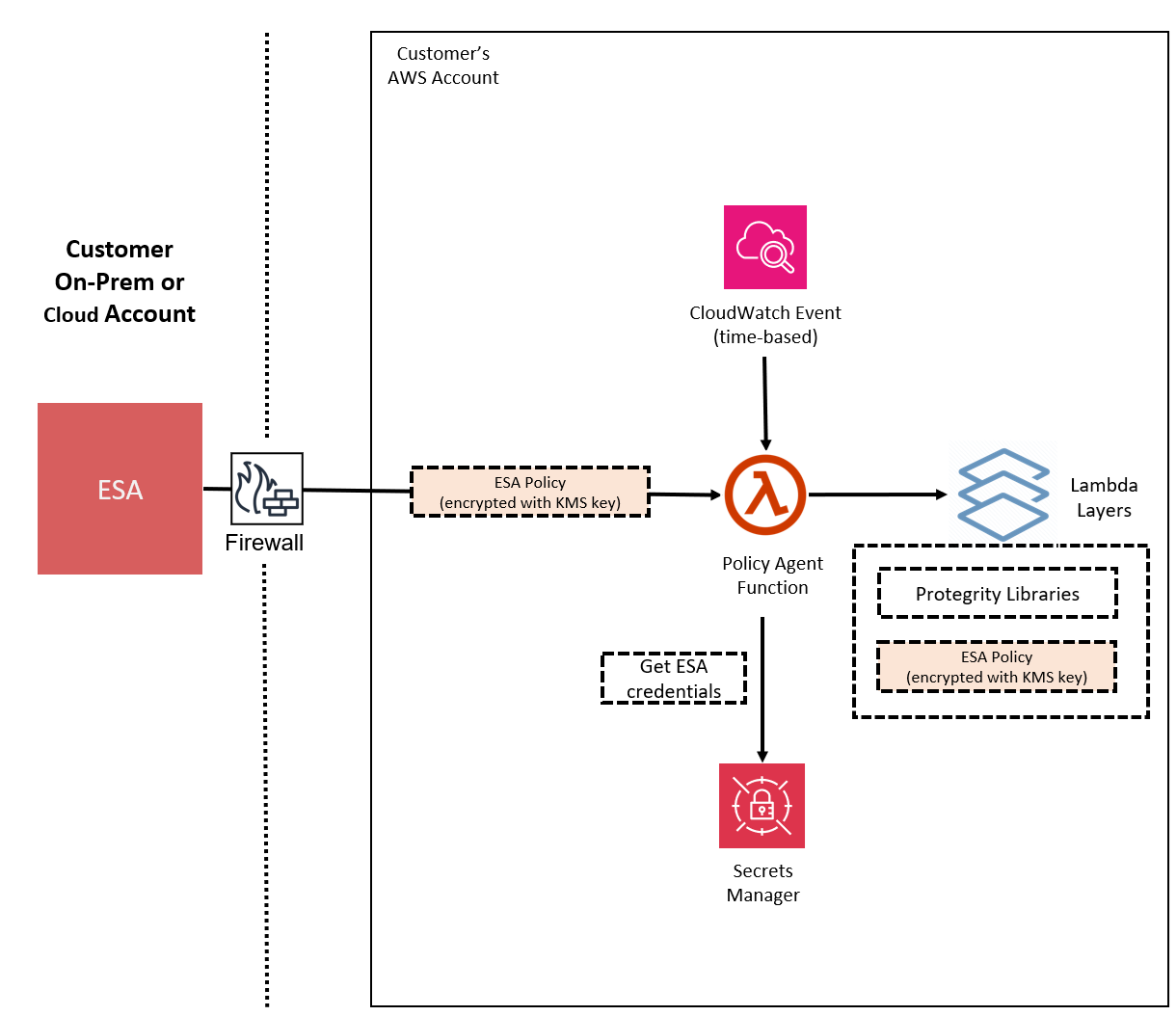
The Protegrity Policy Agent requires network access to an Enterprise Security Administrator (ESA). Most organizations install the ESA on-premise. Therefore, it is recommended that the Policy Agent is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
The ESA is a soft appliance that must be pre-installed on a separate server. It is used to create and manage security policies.
For more information about installing the ESA, and creating and managing policies, refer the Policy Management Guide.
Log Forwarding Architecture
Audit logs are by default sent to CloudWatch as long as the function’s execution role has the necessary permissions. The Protegrity Product can also be configured to send audit logs to ESA. Such configuration requires deploying Log Forwarder component which is available as part of Protegrity Product deployment bundle. The diagram below shows additional resources deployed with Log Forwarder component.
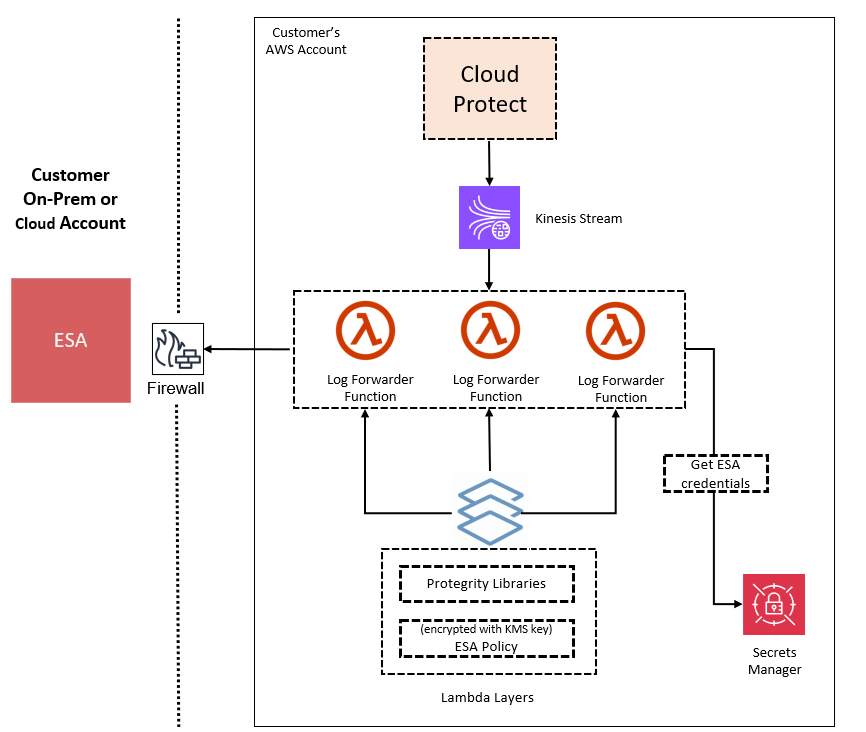
The log forwarder component includes Amazon Kinesis data stream and the forwarder Lambda function. Amazon Kinesis stream is used to batch audit records before sending them to forwarder function, where similar audit logs are aggregated before sending to ESA. Aggregation rules are described in the Protegrity Log Forwarding guide. When the protector function is configured to send audit logs to log forwarder, audit logs are aggregated on the protector function before sending to Amazon Kinesis. Due to specifics of the Lambda runtime lifecycle, audit logs may take up to 15 minutes before being sent to Amazon Kinesis. Protector function exposes configuration to minimize this time which is described in the protector function installation section.
The security of audit logs is ensured by using HTTPS connection on each link of the communication between protector function and ESA. Integrity and authenticity of audit logs is additionally checked on log forwarder which verifies individual logs signature. The signature verification is done upon arrival from Amazon Kinesis before applying aggregation. If signature cannot be verified, the log is forwarded as is to ESA where additional signature verification can be configured. Log forwarder function uses client certificate to authenticate calls to ESA.
To learn more about individual audit log entry structure and purpose of audit logs, refer to Audit Logging section in this document. Installation instructions can be found in Audit Log Forwarder installation.
The audit log forwarding requires network access from the cloud to the ESA. Most organizations install the ESA on-premise. Therefore, it is recommended that the Log Forwarder Function is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
Access Control
The following mechanisms are available for controlling and restricting access to the endpoint:
- IAM policy: The IAM resource policy controls which IAM users or services may invoke Protect operations. IAM policies can be applied to the API Gateway and/or the Lambda directly depending on allowable access patterns and the client.
- JWT tokens: The Lambda can be configured to use JSON Web Tokens (JWT) with optional verification. JSON Web Tokens (JWT) are an open, industry-standard RFC 7519 method for representing claims securely between two parties. JWT provides a mechanism for implementing custom authentication or integrating with AWS Cognito.
AWS Resources
Access and authorization between various AWS services involved in this architecture are achieved through IAM resource policies. For instance, the Amazon Lambda resource-based policy can restrict requests to the Amazon API Gateway or optionally allow direct invocation to the Lambda function itself. The installation steps provide a default recommended configuration. Alternative IAM role configurations are shown in the appendices in this document.
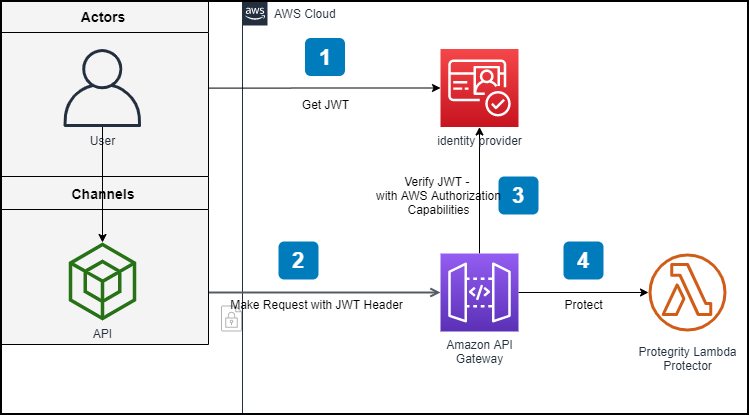
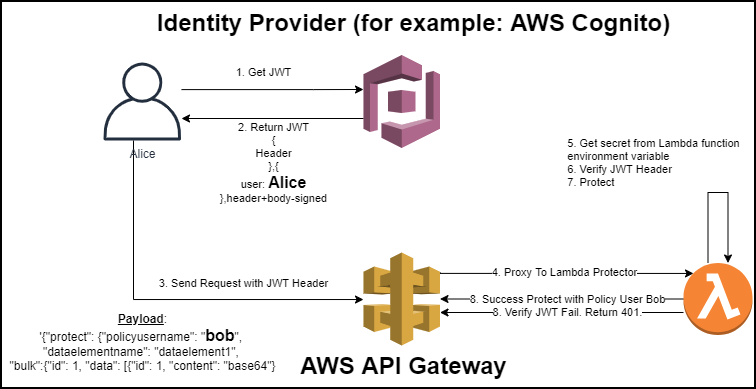
REST API Authentication
AWS API Gateway supports multiple mechanisms for controlling and managing access to the product.
In standard solutions, AWS API Gateway will authorize access tokens generated in the identity provider. When setting up an AWS API Gateway method to require an authorization, customers can leverage AWS Signature Version 4 or Lambda authorizers to support their organization’s bearer token auth strategy.
https://docs.aws.amazon.com/apigateway/latest/developerguide/apigateway-control-access-to-api.html
REST API Authorization
Once the request is authenticated and authorized in the API Gateway, Protegrity Lambda Protector validates the user received in the authorization header of JWT, and the data element and security operations (protect or unprotect) from the payload with Protegrity Security Policy.
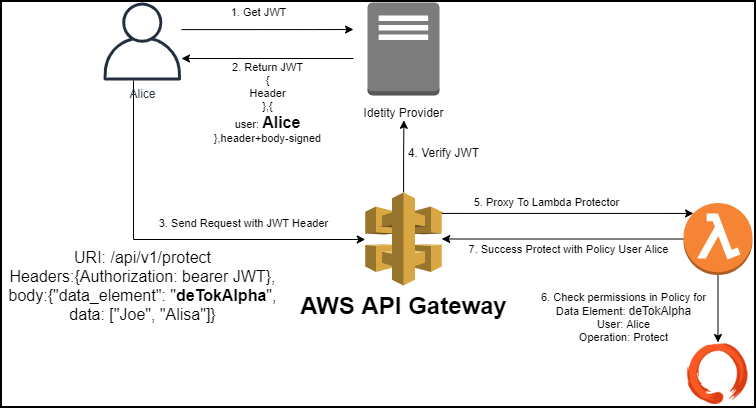
If the API Gateway is not used or configured to verify JWT tokens, the product can be configured to perform the JWT verification in the Lambda function itself.
1.3 - Installation
1.3.1 - Prerequisites
AWS Services
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
API Gateway | Provides the endpoint and access control. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials . |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
ESA Version Requirements
The Protector and Log Forwarder functions require a security policy from a compatible ESA version.
The table below shows compatibility between different Protector and ESA versions.
Note
For the latest up-to-date information refer to: Protegrity Compatibility Matrix| Protector Version | ESA Version | |||
|---|---|---|---|---|
| 8.x | 9.0 | 9.1 & 9.2 | 10.0 | |
| 2.x | No | Yes | * | No |
| 3.0.x & 3.1.x | No | No | Yes | No |
| 3.2.x | No | No | Yes | * |
| 4.0.x | No | No | No | Yes |
Legend | |
|---|---|
Yes | Protector was designed to work with this ESA version |
No | Protector will not work with this ESA version |
* | Backward compatible policy download supported:
|
Prerequisites
Requirement | Detail |
|---|---|
Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
Required Skills and Abilities
Role / Skillset | Description |
|---|---|
AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
Cheat Sheet Recommendation
Tip
During the installation you will need output of steps, such as resources names and ids. We recommend copying the following cheat sheet into a notepad and fill in the information as you progress with the installation.AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
S3 Bucket name (ArtifactS3Bucket): ___________________
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
ProtectLambdaPolicyName: __________________
Role ARN (LambdaExecutionRoleArn): ___________________
ApiGatewayId: ________________________________
ProtectFunctionName: __________________________
ProtectLayerName: _____________________________
ESA IP address: ___________________
VPC name: ___________________
Subnet name: ___________________
Policy Agent Security Group Id: ___________________
ESA Credentials Secret Name: ___________________
Policy Name: ___________________
Agent Lambda IAM Execution Role Name: ___________________
What’s Next
1.3.2 - Pre-Configuration
Provide AWS sub-account
Identify or create an AWS account where the Protegrity solution will be installed. It is recommended that a new AWS sub-account be created. This can provide greater security controls and help avoid conflicts with other applications that might impact regional account limits. An individual with the Cloud Administrator role will be required for some subsequent installation steps.
AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
Create S3 bucket for Installing Artifacts
This S3 bucket will be used for the artifacts required by the CloudFormation installation steps. This S3 bucket must be created in the region that is defined in Provide AWS sub-account
Sign in to the AWS Management Console and open the Amazon S3 console.
Change region to the one determined in Provide AWS sub-account
Click Create Bucket.
Enter a unique bucket name:
For example, protegrity-install.us-west-2.example.com
Upload the installation artifacts to this bucket. Protegrity will provide the following three artifacts:
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
Important
The deployment package you receive from Protegrity must be extracted to reveal the Protegrity artifacts. CloudFormation requires them in the provided .zip format. Do not extract the individual Protegrity artifacts. Upload these artifacts to the S3 bucket created.
S3 Bucket name (ArtifactS3Bucket): ___________________
Create KMS Key
The Amazon Key Management Service (KMS) provides the ability for the Protegrity Serverless solution to encrypt and decrypt the Protegrity Security Policy.
Note
It is recommended to host the KMS key in a separate AWS sub-account. This allows dual control, separating the responsibility between the key administrator and the Protegrity Serverless account administrator.To create KMS key:
In the AWS sub-account where the KMS key will reside, select the region.
Navigate to Key Management Service > Create Key.
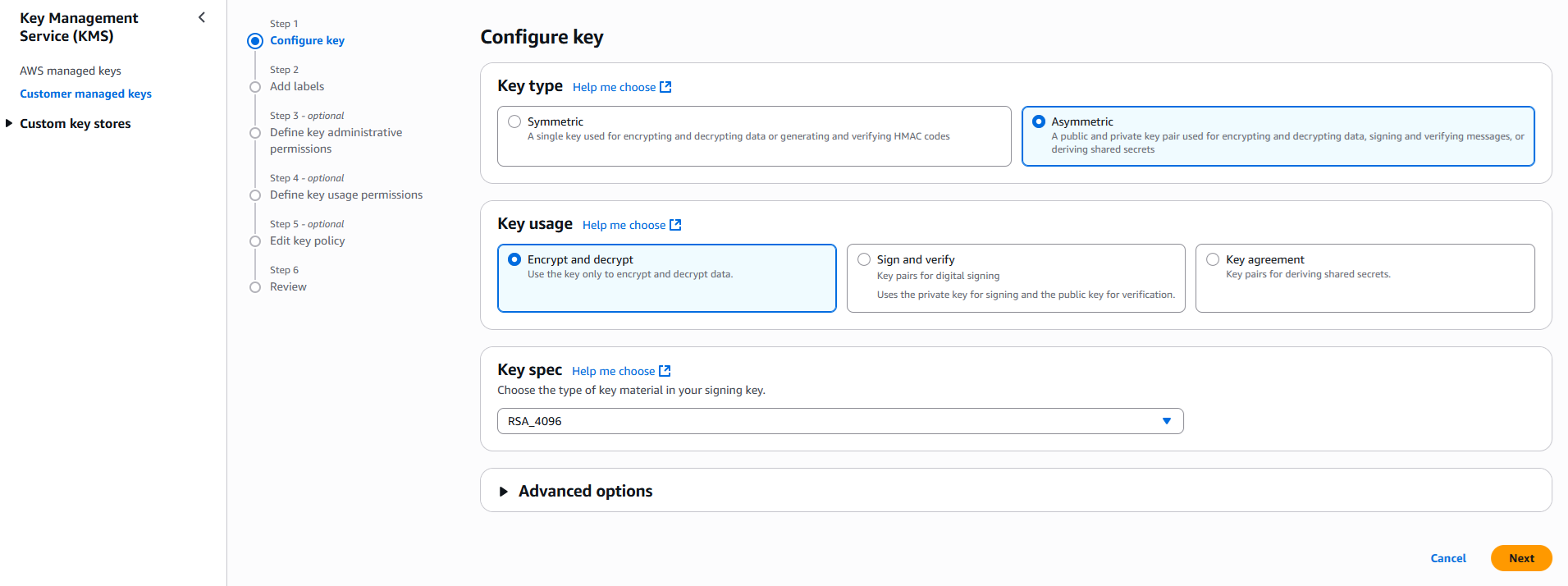
Configure the key settings:
- Key type: Asymmetric
- Key usage: Encrypt and decrypt
- Key spec: RSA_4096
- Click Next
Create alias and optional description, such as, Protegrity-Serverless and click Next.
Define key administrative permissions, the IAM user who will administrate the key.
Note
It is recommended the administrator be different than the administrator of the Protegrity Serverless accountClick Next.
Define the key usage permissions.
In Other AWS accounts, enter the AWS account id used for the Protegrity Serverless installation.
Continue on to create the key. If there is a concern this permission is overly broad, then you can return later to restrict access to the role of two Protegrity Serverless Lambda as principals. Click to open the key in the list and record the ARN.
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
Download the public key from the KMS key. Navigate to the key in KMS console, select the Public key tab, and click Download. Save the PEM file. This public key will be added to the ESA data store as an export key. Refer to Exporting Keys to Datastore for instructions on adding the public key to the data store.
Note
This step is not applicable for ESA versions lower than 10.2.KMS Public Key PEM file: ___________________
What’s Next
1.3.3 - Protect Service Installation
Protect Service Installation
The following sections install the Cloud Protect serverless Lambda function.
Preparation
Ensure that all the steps in Pre-Configuration are performed.
Login to the AWS sub-account console where Protegrity will be installed.
Ensure that the required CloudFormation templates provided by Protegrity are available on your local computer.
Create Protect Lambda IAM Execution Policy
This task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Next, type in a policy name, for example, ProtegrityProtectLambdaPolicy and Create Policy. Record the policy name:
ProtectLambdaPolicyName:__________________
Create Protect Lambda IAM Role
The following steps create the role to utilize the policy defined in Create Protect Lambda IAM Execution Policy.
To create protect lambda IAM execution role:
From the AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
In the list, search and select the policy created in Create Protect Lambda IAM Execution Policy.
Click Next
Type the role name, for example, ProtegrityProtectRole
Click Create role
Record the role ARN.
Role ARN (LambdaExecutionRoleArn): ___________________
Install through CloudFormation
The following steps describe the deployment of the Lambda function.
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_protect_api_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter
Description
Default Value
ArtifactS3Bucket
The name of S3 bucket created during the pre-configuration steps
LambdaExecutionRoleArn
The ARN of Lambda role created in the prior step
MinLogLevel
The minimum log level for the protect function.
Supported values: [off, severe, warning, info, config, all]
severe
AllowAssumeUser (Optional)
If 0 is set, the user in the request body will be ignored and the REST API authenticated user will be the acting user.
Supported values: [0, 1]
0
LambdaAuthorization (Optional)
If “jwt” is set, then Authorization header for JWT will be required in the AWS Protect Lambda request. Any other value is ignored and effective policy user is taken from request payload.
Supported values: [“jwt”, “”]
""
jwtUsernameClaim (Optional)
The JWT claim with username.
Common claims: name, preferred_username, cognito:username
Also accepts ordered list of claim names in JSON array format, e.g. [“username”, “email”]
cognito:username
jwtVerify (Optional)
If 1 is set, then jwtSecretBase64 is required. Only applicable when LambdaAuthorization is set to “jwt”. Supported JWT algorithms are: RS256, RS384, RS512. While algorithms HS256, HS384, HS512 are supported, they are not recommended for use.
0
jwtSecretBase64 (Optional)
Required when jwtVerify is set to 1 and Authorization is set to “jwt”. The secret must be provided in base64 encoding. It is recommended to only use public key (asymmetric algorithm).
""
The log forwarder parameters can be provided later after log forwarder is deployed. If you are not planning to deploy log forwarder you can skip this step.
Parameter Description KinesisLogStreamArn The ARN of the AWS Kinesis stream where audit logs will be sent for aggregation AuditLogFlushInterval Time interval in seconds used to accumulate audit logs before sending to Kinesis. Default value: 30. See Log Forwarder Performance section for more details. Click Next with defaults to complete CloudFormation.
After CloudFormation is completed, select the Outputstab in the stack.
Record the following values:
ApiGatewayId: ________________________________
ProtectFunctionName: __________________________
ProtectFunctionProductionAlias: __________________________
ProtectLayerName: _____________________________
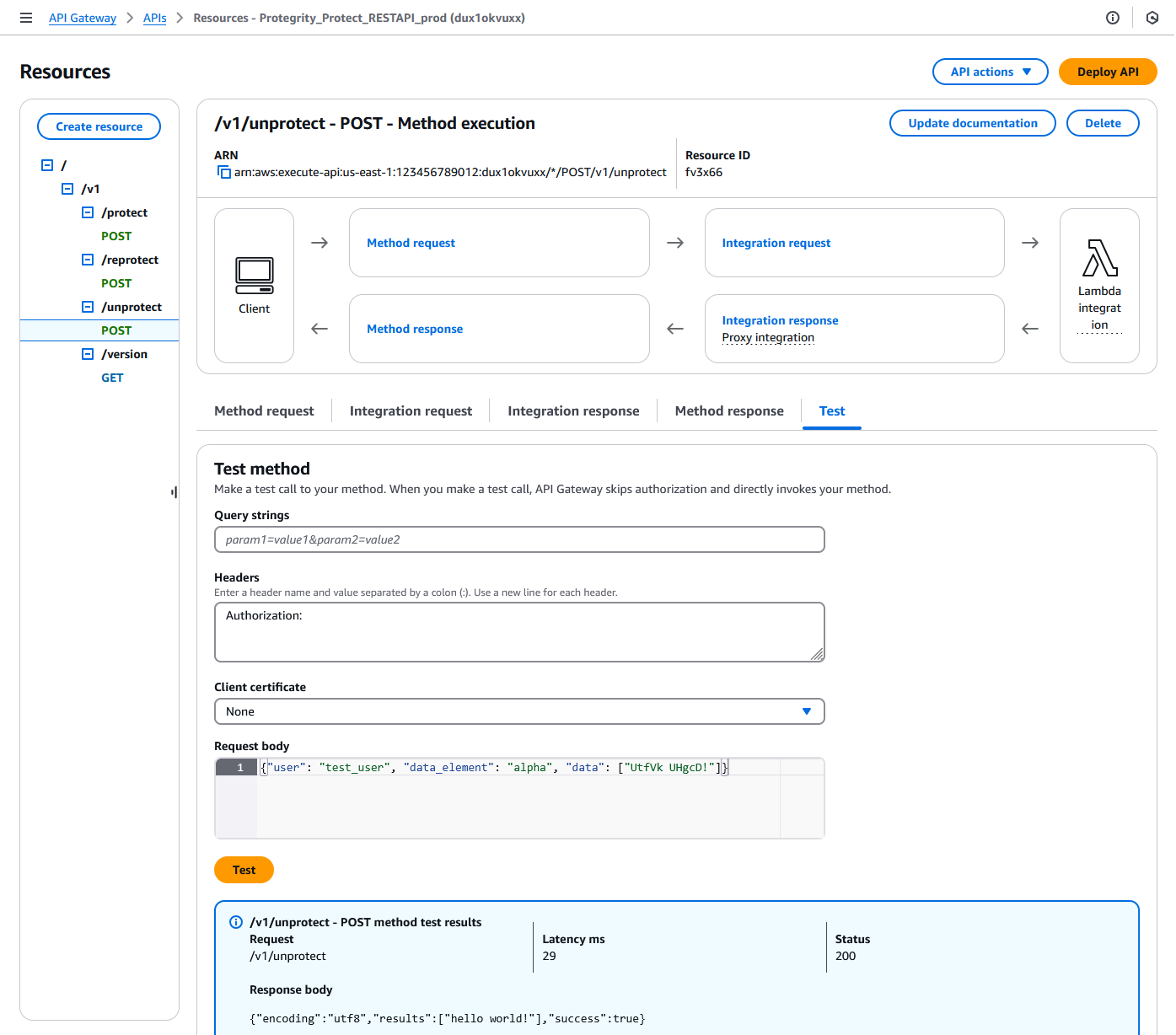
Test Connectivity
Perform the following steps to verify if the API Gateway is working correctly with the Protegrity product.
- In the AWS console Access API Gateway.
Search for API (CloudFormation output ApiGatewayId value).
Select Resources > /v1/unprotect POST.
Click on Test tab.
Provide the following input in Headers.
Authorization:Provide the following input in Request body.
{"user": "test_user", "data_element": "alpha", "data": ["UtfVk UHgcD!"]}Click Test.
Verify the response Status is 200 and the Response Body is as follows:
{"encoding": "utf8", "results": ["hello world!"], "success": true}For example:
Troubleshooting
Error | Action |
|---|---|
5xx error |
If this step fails, then check the console for the meaningful error. |
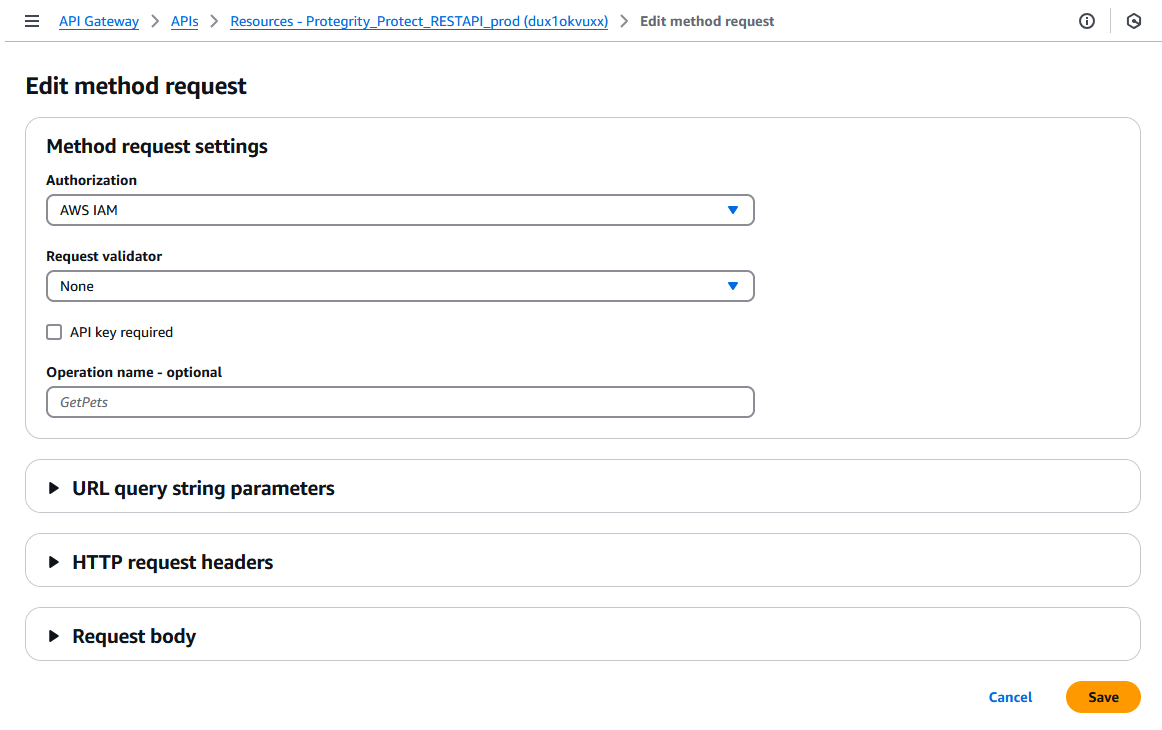
Setting up Authentication
This step describes how to setup an AWS API Gateway Authorization.
By default, the API Gateway is configured to use AWS_IAM Authorization.
- From AWS console access API Gateway.
- If you are using AWS API Gateway Authorizer, ensure that the Authorizer is configured in Authorizers.
- Go to Resources > /v1/protect POST > Method Request tab > Click Edit button
- Select from Authorization. dropdown.
- Click Save button.
- Click Deploy API button to deploy to pty stage.
Protect Lambda Configuration
After Cloud Formation stack is deployed, Protector Lambda can be reconfigured based on the authentication selected in previous stage. From your AWS console navigate to lambda and select following lambda: Protegrity_Protect_RESTAPI_<STACK_NAME>. Scroll down to Environment variables section, select Edit and replace the entries based on the following information.
Environment Variable | Description | Notes |
|---|---|---|
authorization | If “jwt” is set, Authorization header with JWT will be required in the AWS Protect Lambda request. Any other value is ignored and effective policy user is taken from request payload. Supported Values: [“jwt”, “”] | If “jwt” is set, any request without valid JWT in the Authorization header, will result in error from API Gateway: 502 Bad Gateway. Default Value: "" |
allow_assume_user | If 0 is set, API Gateway user will not be used, and the effective user is the JWT user. Supported Values: [0, 1] | Applicable when authorization is set to “jwt”. Default Value: 0 |
jwt_user_claim | The JWT claim with username. Common claims: name, preferred_username, cognito:username | Applicable when authorization is set to “jwt” Default Value: cognito:username |
jwt_verify | If 1 is set, jwt_secret_base64 is required. Only applicable when authorization is set to “jwt”. Supported JWT algorithm RS256, RS384, RS512. While algorithms HS256, HS384, HS512 are supported, they are not recommended for use. | Applicable when authorization is set to “jwt” |
jwt_secret_base64 | Required when jwt_verify is set to 1 and Authorization is set to “jwt”. The secret must be provided in base64 encoding. It is recommended to only use public key (asymmetric algorithm). | Applicable when authorization is set to “jwt” and jwt_verify is set to 1 |
service_user | If set, it will be used as effective policy user. | service_user should be used when the Cloud API should always run as single service user or account no matter what user is in the request. service_user will always take priority over users in the payload and in the JWT header. |
USERNAME_REGEX | If set, the effective policy user will be extracted from the user in the request using supplied regular expression. | See Configuring Regular Expression to Extract Policy Username to learn how to extract username from the request |
What’s Next
1.3.4 - Policy Agent Installation
The following sections will install the Policy Agent. The Policy Agent polls the ESA and deploys the policy to Protegrity Serverless as a static resource. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. Contact Protegrity Professional Services for further guidance on configuration alternatives in the Cloud.
Important
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), refer to the PPC Appendix: Policy Agent Certificate and Key Guidance for specific instructions on obtaining and using the CA certificate and datastore key fingerprint. The steps in this section are specific to ESA and may differ for PPC. Be sure to follow the PPC documentation for the most accurate and up-to-date setup guidance.ESA Server
Policy Agent Lambda requires ESA server running and accessible on TCP port 443.
Note down ESA IP address:
ESA IP Address (EsaIpAddress): ___________________
Certificates on ESA
Note
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), see PPC Appendix: Policy Agent Certificate Guidance for specific instructions on obtaining and using the CA certificate. The steps in this section are specific to ESA and may differ for PPC.Whether your ESA is configured with default self-signed certificate or your corporate CA certificate, Policy Agent can validate authenticity of ESA connection using CA certificate. The process for both scenarios is the same:
- Obtain CA certificate
- Convert CA certificate to a value accepted by Policy Agent
- Provide converted CA certificate value to Policy Agent
To obtain self-signed CA certificate from ESA:
Log in to ESA Web UI.
Select Settings > Network > Manage Certificates.
Hover over Server Certificate and click on download icon to download the CA certificate.
To convert downloaded CA certificate to a value accepted by Policy Agent, open the downloaded PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PTY_ESA_CA_SERVER_CERT or PTY_ESA_CA_SERVER_CERT_SECRET Lambda variable in section Policy Agent Lambda Configuration
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
Identify or Create a new VPC
Establish a VPC where the Policy Agent will be hosted. This VPC will need connectivity to the ESA. The VPC should be in the same account and region established in Pre-Configuration.
VPC name: ___________________
VPC Subnet Configuration
Identify or create a new subnet in the VPC where tha Lambda function will be connected to. It is recommended to use a private subnet.
Subnet name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoints Configuration
If an internal VPC was created, then add VPC Endpoints, which will be used by the Policy Agent to access AWS services. Policy Agent needs access to the following AWS services:
Type | Service name |
|---|---|
Interface | com.amazonaws.{REGION}.secretsmanager |
Interface | com.amazonaws.{REGION}.kms |
Gateway | com.amazonaws.{REGION}.s3 |
Interface | com.amazonaws.{REGION}.lambda |
Identify or Create Security Groups
Policy Agent and cloud-based ESA appliance use AWS security groups to control traffic that is allowed to leave and reach them. Policy Agent runs on schedule and is mostly concerned with allowing traffic out of itself to ESA and AWS services it depends on. ESA runs most of the time and it must allow Policy Agent to connect to it.
Policy Agent security group must allow outbound traffic using rules described in the table below. To edit security group navigate:
From VPC > Security Groups > Policy Agent Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG | ESA Communication |
| HTTPS | TCP | 443 | Any | AWS Services |
Record Policy Agent security group ID:
Policy Agent Security Group Id: ___________________
Policy Agent will reach out to ESA on port 443. Create following inbound security group rule for cloud-based ESA appliance to allow connections from Policy Agent:
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG |
Creating ESA Credentials
Policy Agent Lambda requires ESA credentials to be provided as one of the three options.
Note
The username and password of the ESA user requires role with Export Resilient Package and Can Create JWT Token permissions. Security Administrator is one of the predefined roles which contains the above permissions, however for separation of duties it is recommended to create custom role.Option 1: Secrets Manager
Creating secrets manager secret with ESA username and password.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the username and password key value pair.
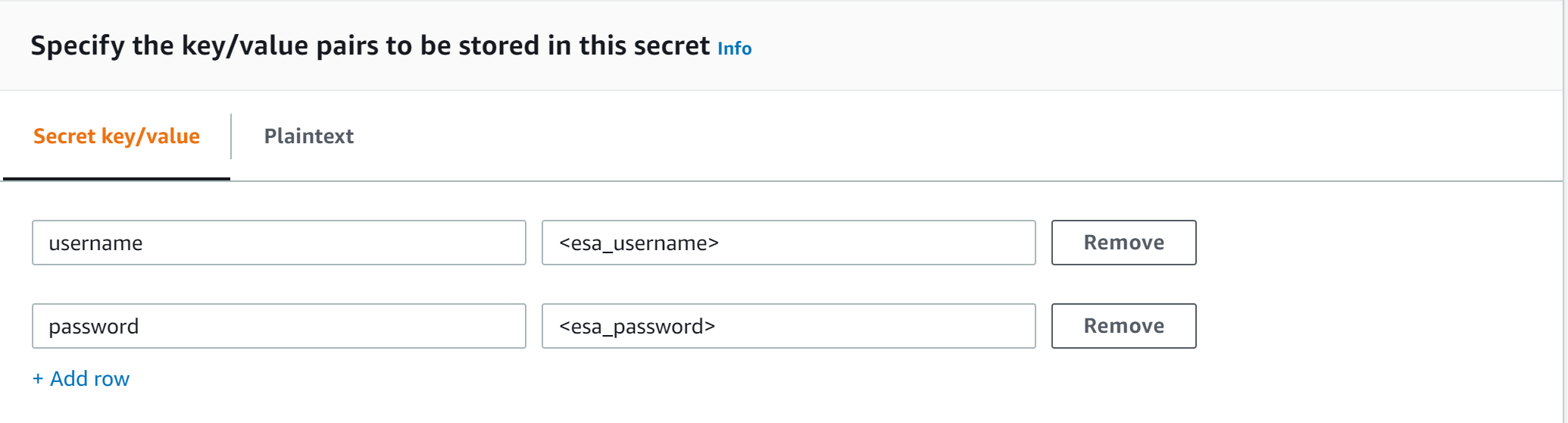
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it.
ESA Credentials Secret Name: __________________
Option 2: KMS Encrypted Password
ESA password is encrypted with AWS KMS symmetric key.
Create AWS KMS symmetric key which will be used to encrypt ESA password. See Create KMS Key for instructions on how to create KMS symmetric key using AWS console.
Record KMS Key ARN.
ESA PASSWORD KMS KEY ARN: __________________
Run AWS CLI command to encrypt ESA password. Below you can find sample Linux aws cli command. Replace <key_arn> with KMS symmetric key ARN.
aws kms encrypt --key-id <key_arn> --plaintext $(echo '<esa_password>' | base64 )Sample output.
{ "CiphertextBlob": "esa_encrypted_password", "KeyId": "arn:aws:kms:region:aws_account:key/key_id ", "EncryptionAlgorithm": "SYMMETRIC_DEFAULT" }Record ESA username and encrypted password.
ESA USERNAME: __________________
ESA ENCRYPTED PASSWORD: __________________
Option 3: Custom AWS Lambda function
With this option ESA username and password are returned by a custom AWS Lambda function. This method may be used to get the username and password from external vaults.
Create AWS Lambda in any AWS supported runtime.
There is no input needed.
The Lambda function must return the following response schema.
response: type: object properties: username: string password: stringFor example,
example output: {"username": "admin", "password": "Password1234"}Sample AWS Lambda function in Python:
import json def lambda_handler(event, context): return {"username": "admin", "password": "password1234"}Warning
Protegrity does not recommend hardcoding ESA username and password in the clear.
Record the Lambda name:
Custom AWS lambda for ESA credentials: _______________
Create Agent Lambda IAM Policy
Follow the steps below to create Lambda execution policies.
Create Agent Lambda IAM policy
From AWS IAM console, select Policies > Create Policy.
Select JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "KmsEncrypt", "Effect": "Allow", "Action": [ "kms:GetPublicKey" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace wildcard * with the region, account, and resource name information where required.
This step is required if KMS is used to encrypt ESA password.
Add policy entry below. Replace ESA PASSWORD KMS KEY ARN with the value recorded in Option 2: KMS Encrypted Password.
{ "Sid": "KmsDecryptEsaPassword", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "**ESA PASSWORD KMS KEY ARN**" ] }Select Next type in the policy name and Create Policy. Record policy name:
Policy Name: ___________________
Create Agent Lambda IAM Role
Perform the following steps to create Agent Lambda execution IAM role.
To create agent Lambda IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Agent Lambda IAM policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityAgentRole and click Confirm.
Select Create role.
Record the role ARN.
Agent Lambda IAM Execution Role Name: ___________________
Corporate Firewall Configuration
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access from the NAT Gateway IP to ESA via port 443 and 443.
CloudFormation Installation
Create the Policy Agent in the VPC using the CloudFormation script provided by Protegrity.
Access the CloudFormation service.
Select the target installation region.
Create a stack with new resources.
Upload the Policy Agent CloudFormation template (file name: pty_agent_cf.json).
Specify the following parameters for Cloud Formation:
Parameter Description Note VPC VPC where the Policy Agent will be hosted Identify or Create a new VPC Subnet Subnet where the Policy Agent will be hosted VPC Subnet Configuration PolicyAgentSecurityGroupId Security Group Id, which allows communication between the Policy Agent and the ESA Identify or Create Security Groups LambdaExecutionRoleArn Agent Lambda IAM execution role ARN allowing access to the S3 bucket, KMS encryption Key, Lambda and Lambda Layer Create Agent Lambda IAM Role ArtifactS3Bucket S3 bucket name with deployment package for the Policy Agent Use S3 Bucket name recorded in Create S3 bucket for Installing Artifacts CreateCRONJob Set to True to create a CloudWatch schedule for the agent to run. Default: False
Policy Agent Lambda Configuration
After the CloudFormation stack is deployed, the Policy Agent Lambda must be configured with parameters recorded in earlier steps. From your AWS Console, navigate to lambda and select the following Lambda.
Protegrity_Agent<STACK_NAME>_
Select Configuration tab and scroll down to the Environment variables section. Select Editand replace all entries with the actual values.
Parameter | Description | Notes |
|---|---|---|
PTY_ESA_IP | ESA IP address or hostname | |
PTY_ESA_CA_SERVER_CERT | ESA self-signed CA certificate or your corporate CA certificate used by policy Agent Lambda to ensure ESA is the trusted server. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT configuration will be ignored. |
PTY_ESA_CA_SERVER_CERT_SECRET | This configuration option fulfills the same function as PTY_ESA_CA_SERVER_CERT but supports larger configuration values, making it the recommended choice. The value should specify the name of the AWS Secrets Manager secret containing the ESA self-signed CA certificate. The secret value should be set to the json with “PTY_ESA_CA_SERVER_CERT” key and PEM formated CA certificate content value as shown below. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT_SECRET configuration will be ignored. When both PTY_ESA_CA_SERVER_CERT and PTY_ESA_CA_SERVER_CERT_SECRET are configured the PTY_ESA_CA_SERVER_CERT_SECRET takes precedence. |
PTY_ESA_CREDENTIALS_SECRET | ESA username and password (encrypted value by AWS Secrets Manager) | |
PTY_DATASTORE_KEY | ESA policy datastore public key fingerprint (64 char long) e.g. 123bff642f621123d845f006c6bfff27737b21299e8a2ef6380aa642e76e89e5. | NoteThis configuration is not applicable for ESA versions lower than 10.2.The export key is the public part of an asymmetric key pair created in a Create KMS Key. A user with Security Officer permissions adds the public key to the data store in ESA via Policy Management > Data Stores > Export Keys. The fingerprint can then be copied using the Copy Fingerprint icon next to the key. Refer to Exporting Keys to Datastore for details. NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate and Key Guidance for details on obtaining and using the datastore key fingerprint. |
AWS_KMS_KEY_ID | KMS key id or full ARN e.g. arn:aws:kms:us-west-2:112233445566:key/bfb6c4fb-509a-43ac-b0aa-82f1ca0b52d3 | |
AWS_POLICY_S3_BUCKET | S3 bucket where the encrypted policy will be written | S3 bucket of your choice |
AWS_POLICY_S3_FILENAME | Filename of the encrypted policy stored in S3 bucket | Default: protegrity-policy.zip |
AWS_PROTECT_FN_NAME | Comma separated list of Protect function names or ARNs | ProtectFunctionName(s), recorded in CloudFormation Installation |
DISABLE_DEPLOY | This flag can be either 1 or 0. If set to 1, then the agent will not update PTY_PROTECT lambda with the newest policy. Else, the policy will be saved in the S3 bucket and deployed to the Lambda Layer | Default: 0 |
AWS_POLICY_LAYER_NAME | Lambda layer used to store the Protegrity policy used by the PTY_PROTECT function |
|
POLICY_LAYER_RETAIN | Number of policy versions to retain as backup. (e.g. 2 will retain the latest 2 policies and remove older ones). -1 retains all. | Default: 2 |
POLICY_PULL_TIMEOUT | Time in seconds to wait for the ESA to send the full policy | Default: 20s |
ESA_CONNECTION_TIMEOUT | Time in seconds to wait for the ESA response | Default: 5s |
LOG_LEVEL | Application and audit logs verbiage level | Default: INFO Allowed values: DEBUG – the most verbose, INFO, WARNING, ERROR – the least verbose |
PTY_CORE_EMPTYSTRING | Override default behavior. Empty string response values are returned as null values. For instance: (un)protect(’’) -> null (un)protect(’’) -> '' | Default: empty Allowed values: null empty |
PTY_CORE_CASESENSITIVE | Specifies whether policy usernames should be case sensitive | Default: no Allowed values: yes no |
PTY_ADDIPADDRESSHEADER | When enabled, agent will send its source IP address in the request header. This configuration works in conjunction with ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP (default=false). See Associating ESA Data Store With Cloud Protect Agent for more information. | Default: yes Allowed values: yes no |
PTY_ESA_USERNAME | Plaintext ESA username which is used together with PTY_ESA_ENCRYPTED_PASSWORD as an optional ESA credentials | Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored |
PTY_ESA_ENCRYPTED_PASSWORD | ESA password encrypted with KMS symmetric key. Example AWS cli command to generate the value:
| Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored Value must be base64 encoded |
EMPTY_POLICY_S3 | This flag can be either 1 or 0. If set to 1, then the agent will remove the content of the policy file in S3 bucket, but will keep the checksum in the metadata. Else, the policy will be saved in the S3 bucket and not removed. | Default: 0 |
PTY_ESA_CREDENTIALS_LAMBDA | Lambda function to return ESA credentials | Recorded in step Option 3: Custom AWS Lambda function LAMBDA FOR ESA CREDENTIALS. Presence of PTY_ESA_USERNAME, or PTY_ESA_CREDENTIALS_SECRET will cause this value to be ignored. The Policy Agent Lambda must have network access and IAM permissions to invoke the custom ESA Credentials Lambda you have created in Option 3: Custom AWS Lambda function. |
Test Installation
Open the Lambda and configure Test to execute the lambda and specify the default test event. Wait for around 20 seconds for the Lambda to complete. If policy is downloaded successfully, then a success message appears.
Navigate to the AWS_POLICY_S3_BUCKET bucket and verify that the AWS_POLICY_S3_FILENAME file was created.
Troubleshooting
Lambda Error | Example Error | Action |
|---|---|---|
Task timed out after x seconds | |
|
ESA connection error. Failed to download certificates | ||
Policy Pull takes a long time | |
|
ESA connection error. Failed to download certificates. HTTP response code: 401 | | Ensure that the PTY_ESA_CREDENTIALS_SECRET has correct ESA username and password |
An error occurred (AccessDeniedException) when calling xyz operation | | Ensure that the Lambda execution role has permission to call the xyz operation |
Access Denied to Secret Manager. | |
|
Master Key xyz unable to generate data key | Ensure that the Lambda can access xyz CMK key | |
The S3 bucket server-side encryption is enabled, the encryption key type is SSE-KMS but the Policy Agent execution IAM role doesn’t have permissions to encrypt using the KMS key . | | Add the following permissions to the Policy Agent excution role. NoteWhen the KMS key and the Policy Agent Lambda are in separate accounts, update both the AWS KMS key and the Policy Agent execution role. |
The S3 bucket has bucket policy to only allow access from within the VPC. | | The Policy Agent publishes a new Lambda Layer version, and the Lambda Layer service uploads the policy file from the s3 bucket and the upload request is originated from the AWS service outside the Policy Agent Lambda VPC. Update the S3 bucket resource policy to allow access from AWS Service. Sample security policy to lock down access to the vpc: |
Additional Configuration
Strengthen the KMS IAM policy by granting access only to the required Lambda function(s).
Finalize the IAM policy for the Lambda Execution Role. Ensure to replace wildcard * with the region, account, and resource name information where required.
For example,
"arn:aws:lambda:*:*:function:*" -> "arn:aws:lambda:us-east-1:account:function:function_name"
Policy Agent Schedule
If specified in CloudFormation Installation, the agent installation created a CloudWatch event rule, which checks for policy update on an hourly schedule. This schedule can be altered to the required frequency.
Under CloudWatch > Events > Rules, find Protegrity_Agent_{stack_name}. Click Action > Edit Set the cron expression. A cron expression can easily be defined using CronMaker, a free online tool. Refer to http://www.cronmaker.com.
What’s Next
1.3.5 - Audit Log Forwarder Installation
The following sections show steps how to install Audit Log Forwarder component in the AWS Cloud. The Log Forwarder deployment allows for the audit logs generated by Protector to be delivered to ESA for auditing and governance purposes. Log Forwarder component is optional and is not required for the Protector Service to work properly. See Log Forwarding Architecture section in this document for more information. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. C ontact Protegrity for further guidance on configuration alternatives in the Cloud.
Note
The installation steps below assume that the Log Forwarder is going to be installed in the same AWS account as the corresponding Protect Lambda service. For instructions on how to install Log Forwarder in the AWS account separate than the Protect Lambda, please contact Protegrity.ESA Audit Store Configuration
ESA server is required as the recipient of audit logs. Verify the information below to ensure ESA is accessible and configured properly.
ESA server running and accessible on TCP port 9200 (Audit Store) or 24284 (td-agent).
Audit Store service is configured and running on ESA. Applies when audit logs are output to Audit Store directly or through td-agent. For information related to ESA Audit Store configuration, refer to Audit Store Guide.
(Optional) td-agent is configured for external input. For more information related to td-agent configuration, refer to ESA guide Sending logs to an external security information and event management (SIEM).
Certificates on ESA
Note
This section is optional. If CA certificate is not provided, the Log Forwarder will skip server certificate validation and will connect to ESA without verifying that it is a trusted server.
If you are deploying Log Forwarder with Protegrity Provisioned Cluster (PPC), certificate authorization and CA validation are not supported. Configuration steps related to certificates in this section do not apply to PPC. See Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster): Log Forwarder Setup with PPC for details.
By default, ESA is configured with self-signed certificates, which can optionally be validated using a self-signed CA certificate supplied in the Log Forwarder configuration. If no CA certificate is provided, the Log Forwarder will skip server certificate validation.
Note
Certificate Validation can be bypassed for testing purposes, see section: Install through CloudFormationIf ESA is configured with publicly signed certificates, this section can be skipped since the forwarder Lambda will use the public CA to validate ESA certificates.
To obtain the self-signed CA certificate from ESA:
Download ESA CA certificate from the /etc/ksa/certificates/plug directory of the ESA
After certificate is downloaded, open the PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PtyEsaCaServerCert cloudformation parameter in section Install through CloudFormation
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
AWS VPC Configuration
Log forwarder Lambda function requires network connectivity to ESA, similar to Policy Agent Lambda function. Therefore, it can be hosted in the same VPC as Policy Agent.
Separate VPC can be used, as long as it provides network connectivity to ESA.
Note
AWS Lambda service uses permissions in log forwarder function execution role to create and manage network interfaces. Lambda creates a Hyperplane ENI and reuses it for other VPC-enabled functions in your account that use the same subnet and security group combination. Each Hyperplane ENI can handle thousands of connections/ports as the Lambda function scales up. If more connections are needed AWS Lambda service creates additional Hyperplane ENIs. There’s no additional charge for using a VPC or a Hyperplane ENI. Refer to AWS official Lambda Hyperplane ENIs docs for more information.VPC Name: ___________________
VPC Subnet Configuration
Log Forwarder can be connected to the same subnet as Policy Agent or separate one as long as it provides connectivity to ESA.
Subnet Name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoint Configuration
Log Forwarder Lambda function requires connectivity to Secrets Manager AWS service. If the VPC identified in the steps before has no connectivity to public internet through the NAT Gateway, then the following service endpoint must be configured:
- com.amazonaws.{REGION}.cloudwatch
- com.amazonaws.{REGION}.secretsmanager
- com.amazonaws.{REGION}.kms
Security Group Configuration
Security groups restrict communication between Log Forwarder Lambda function and the ESA appliance. The following rules must be in place for ESA and Log Forwarder Lambda function.
From VPC > Security Groups > Log Forwarder Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG | ESA Communication |
Record the name of Log Forwarder security group name.
Log Forwarder Security Group Id: ___________________
The following port must be open for the ESA. If the ESA is running in the Cloud, then create the following security.
Note
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access the NAT Gateway IP access to ESA via port 9200.ESA Security Group configuration
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG |
Configure ESA Audit Store Credentials
Note
This section is optional. If client certificate authentication is not set up, the Log Forwarder will connect to ESA without authentication credentials.Audit Log Forwarder can optionally authenticate with ESA using certificate-based authentication with a client certificate and certificate key. If used, both the certificate and certificate key will be stored in AWS Secrets Manager.
Download the following certificates from the /etc/ksa/certificates/plug directory of the ESA:
- client.key
- client.pem
After certificates are downloaded, open each PEM file in text editor and replace all new lines with escaped new line: \n. To escape new lines from command line, use one of the commands below depending on your operating system.
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' client.key > private_key.txt
awk 'NF {printf "%s\\n",$0;}' client.pem > public_key.txt
Windows PowerShell:
(Get-Content '.\client.key') -join '\n' | Set-Content 'private_key.pem'
(Get-Content '.\client.pem') -join '\n' | Set-Content 'public_key.pem'
For more information on how to configure client certificate authentication for Audit Store on ESA refer to Audit Store Guide.
To create secret with ESA client certificate/key pair in AWS Secrets Manager.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the private_key and public_key value pair.
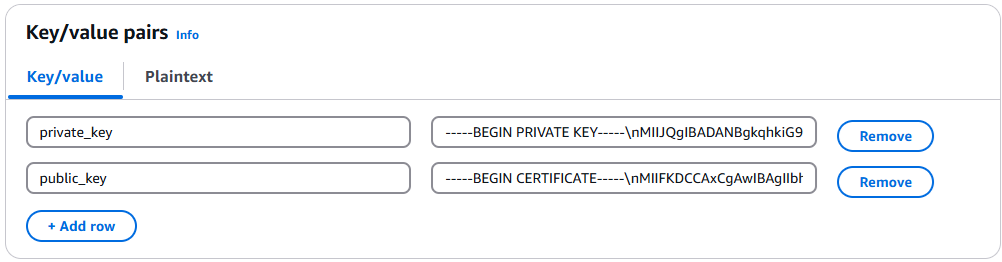
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it below.
ESA Client Certificate/Key Pair Secret Name: ___________________
This value will be used to set PtyEsaClientCertificatesSecretId cloudformation parameter in section Install through CloudFormation
Note
If you are deploying Log Forwarder with PPC, do not configure client certificate authentication. See PPC Appendix: Log Forwarder Certificate Guidance for details.Create Audit Log Forwarder IAM Execution Policy
This task defines a policy used by the Protegrity Log Forwarder Lambda function to write CloudWatch logs, access the KMS encryption key to decrypt the policy and access Secrets Manager for log forwarder user credentials.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "KinesisStreamRead", "Effect": "Allow", "Action": [ "kinesis:GetRecords", "kinesis:GetShardIterator", "kinesis:DescribeStream", "kinesis:DescribeStreamSummary", "kinesis:ListShards", "kinesis:ListStreams" ], "Resource": "*" }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Review policy, type in a policy name, for example, ProtegrityLogForwarderLambdaPolicy and Confirm. Record the policy name:
LogForwarderLambdaPolicyName:__________________
Create Log Forwarder IAM Role
Perform the following steps to create Log Forwarder execution IAM role.
To create Log Forwarder IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Audit Log Forwarder IAM Execution Policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityForwarderRole and click Confirm.
Record the role ARN.
Log Forwarder IAM Execution Role Name: ___________________
Installation Artifacts
Audit Log Forwarder installation artifacts are part of the same deployment package as the one used for protect and policy agent services. Follow the steps below to ensure the right artifacts are available for log forwarder installation.
Verify that the Protegrity deployment package is available on your local system, if not, you can download it from the Protegrity portal.
Note
If you maintain multiple Protegrity Cloud Protectors, make sure that the deployment package downloaded for Audit Log Forwarder is the same as the one used for Protect service installation.Extract the pty_log_forwarder_cf.json cloud formation file from the deployment package.
Check the S3 deployment bucket identified in section Create S3 bucket for Installing Artifacts. Make sure that all Protegrity deployment zip files are uploaded to the S3 bucket.
Install through CloudFormation
The following steps describe the deployment of the Audit Log Forwarder AWS cloud components.
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_log_forwarder_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter | Description | Default Value | Required |
|---|---|---|---|
LogForwarderSubnets | Subnets where the Log Forwarder will be hosted. |
|
|
LogForwarderSecurityGroups | Security Groups, which allow communication between the Log Forwarder and ESA. |
| X |
LambdaExecutionRoleArn | The ARN of Lambda role created in the prior step. |
| X |
ArtifactS3Bucket | Name of S3 bucket created in the pre-configuration step. |
| X |
LogDestinationEsaIp | IP or FQDN of the ESA instance or cluster. |
| X |
AuditLogOutput | Audit log processor to target on ESA. Allowed values: audit-store, td-agent | audit-store | X |
PtyEsaClientCertificatesSecretId | AWS Secrets Manager secret id containing client certificates used for authentication with ESA Audit Store. It is expected that the public key will be stored in a field public_key and the private key in a field named private_key. This parameter is optional. If not provided, Log Forwarder will connect to ESA without client certificate authentication. | ||
EsaTlsDisableCertVerify | Disable certificate verification when connecting to ESA if set to 1. This is only for dev purposes, do not disable in production environment. | 0 | X |
PtyEsaCaServerCert | ESA self-signed CA certificate used by log forwarder Lambda to ensure ESA is the trusted server. Recorded in step Certificates on ESA In case ESA is configured with publicly signed certificates, the PtyEsaCaServerCert configuration will be ignored. |
| |
EsaConnectTimeout | Time in seconds to wait for the ESA response. Minimum value: 1. | 5 | X |
EsaVirtualHost | ESA virtual hostname. This configuration is optional and it can be used when proxy server is present and supports TLS SNI extension. |
|
|
KinesisLogStreamRetentionPeriodHours | The number of hours for the log records to be stored in Kinesis Stream in case log destination server is not available. Minimum value: 24. See Log Forwarder Performance section for more details. | 24 | X |
KinesisLogStreamShardCount | The number of shards that the Kinesis log stream uses. For greater provisioned throughput, increase the number of shards. Minimum value: 1. See Log Forwarder Performance section for more details. | 10 | X |
MinLogLevel | Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all | severe | X |
Click Next with defaults to complete CloudFormation.
After CloudFormation is completed, select the Outputstab in the stack.
Record the following values
KinesisLogStreamArn: ________________________________
Add Kinesis Put Record permission to the Protect Function IAM Role
Login to the AWS account that hosts the Protect Lambda Function.
Search for Protect Lambda Function IAM Execution Role Name created in Create Protect Lambda IAM role.
Under Permissions policies, select Add Permissions > Create inline policy.
In Specify permissions view, switch to JSON.
Copy the policy json from below replacing the placeholder value indicated in the following snippet as <Audit Log Kinesis Stream ARN> with the value recorded in the previous step.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "KinesisPutRecords", "Effect": "Allow", "Action": "kinesis:PutRecords", "Resource": "<Audit Log Kinesis Stream ARN>" } ] }When you are finished, choose Next.
On the Review and create page, type a Name, then choose Create policy.
Test Log Forwarder Installation
Testing in this section validates the connectivity between Log Forwarder and ESA. The sample policy included with the initial installation and test event below are not based on your ESA policy. Any logs forwarded to ESA which are not signed with a policy generated by your ESA will not be added to the audit store.
Install Log Forwarder and configure according to previous sections. Log Forwarder configuration MinLogLevel must be at least info level.
Navigate to the log forwarder lambda function.
Select the Test tab.
Copy the json test event into the Event JSON pane.
{ "Records": [ { "kinesis": { "kinesisSchemaVersion": "1.0", "partitionKey": "041e96d78c778677ce43f50076a8ae3e", "sequenceNumber": "49620336010289430959432297775520367512250709822916263938", "data": "eyJpbmdlc3RfdGltZV91dGMiOiIyMDI2LTAzLTI3VDEzOjIzOjEyLjkwNFoiLCJhZGRpdGlvbmFsX2luZm8iOnsiZGVzY3JpcHRpb24iOiJEYXRhIHVucHJvdGVjdCBvcGVyYXRpb24gd2FzIHN1Y2Nlc3NmdWwuIn0sImNsaWVudCI6e30sImNudCI6NCwiY29ycmVsYXRpb25pZCI6InJzLXF1ZXJ5LWlkOjEyMzQiLCJsZXZlbCI6IlNVQ0NFU1MiLCJsb2d0eXBlIjoiUHJvdGVjdGlvbiIsIm9yaWdpbiI6eyJob3N0bmFtZSI6IlBSTy1VUy1QRjNSSEdGOSIsImlwIjoiMTAuMTAuMTAuMTAiLCJ0aW1lX3V0YyI6MTcxMTU1OTEwMH0sInByb2Nlc3MiOnsiaWQiOjJ9LCJwcm90ZWN0aW9uIjp7ImF1ZGl0X2NvZGUiOjgsImRhdGFlbGVtZW50IjoiYWxwaGEiLCJkYXRhc3RvcmUiOiJTQU1QTEVfUE9MSUNZIiwibWFza19zZXR0aW5nIjoiIiwib2xkX2RhdGFlbGVtZW50IjpudWxsLCJvcGVyYXRpb24iOiJVbnByb3RlY3QiLCJwb2xpY3lfdXNlciI6IlBUWURFViJ9LCJwcm90ZWN0b3IiOnsiY29yZV92ZXJzaW9uIjoiMS4yLjErNTUuZzU5MGZlLkhFQUQiLCJmYW1pbHkiOiJjcCIsInBjY192ZXJzaW9uIjoiMy40LjAuMTQiLCJ2ZW5kb3IiOiJyZWRzaGlmdCIsInZlcnNpb24iOiIwLjAuMS1kZXYifSwic2lnbmF0dXJlIjp7ImNoZWNrc3VtIjoiN0VCMkEzN0FDNzQ5MDM1NjQwMzBBNUUxNENCMTA5QzE0OEJGODYwRjE3NEVCMjMxMTAyMEI3RkE1QTY4MjdGQyIsImtleV9pZCI6ImM0MjQ0MzZhLTExMmYtNGMzZi1iMmRiLTEwYmFhOGI1NjJhNyJ9fQ==", "approximateArrivalTimestamp": 1626878559.213 }, "eventSource": "aws:kinesis", "eventVersion": "1.0", "eventID": "shardId-000000000000:49620336010289430959432297775520367512250709822916261234", "eventName": "aws:kinesis:record", "invokeIdentityArn": "arn:aws:iam::555555555555:role/service-role/TestRole", "awsRegion": "us-east-1", "eventSourceARN": "arn:aws:kinesis:us-east-1:555555555555:stream/CloudProtectEventStream" } ] }Note
The data payload is the base64 encoded audit log. See Audit Logging for detail on audit log contents.Select Test to execute the test event.
Test is successful if the Log Output of test results contains the following log:
[INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed recordsIf the log is not present, please consult the Troubleshooting section for common errors and solutions.
Update Protector With Kinesis Log Stream
In this section, Kinesis log stream ARN will be provided to the Protect Function installation.
Note
If the Protector has not been installed, you may provide the KinesisLogStreamArn during protector installation and skip the remainder of this section.Navigate to the Protector CloudFormation stack created in the protector installation section.
Select Update.
Choose Use existing template > Next.
Set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation.
Proceed with Next and Submit the changes.
Continue to the next section once stack status indicates UPDATE_COMPLETE.
Update Policy Agent With Log Forwarder Function Target
Log Forwarder Lambda function requires a policy layer which is in sync with the Protegrity Protector. This section will describe the steps to update the policy agent to include updating Log Forwarder Lambda function.
Note
If the policy agent has not been installed, follow the steps in Policy Agent Installation. Set AWS_PROTECT_FN_NAME to include both protector and log forwarder lambda functions.Navigate to the Policy Agent Function created in Policy Agent Installation
Select Configuration > Environment variables > Edit
Edit the value for environment variable AWS_PROTECT_FN_NAME to include the log forwarder function name/arn in the comma separated list of Lambda functions.
Save the changes and continue when update completes
Navigate to Test tab
Add an event {} and select Test to run the Policy Agent function
Verify Log forwarder function was updated to use the policy layer by inspecting the log output. Logs should include the following:
[INFO] 2024-07-09 18:58:04,793.793Z 622d374b-1f73-4123-9a38-abc61973adef iap_agent.policy_deployer:Updating lambda [Protegrity_LogForwarder_<stack ID>] to use layer version [arn:aws:lambda:<aws region>:<aws account number>:layer:Protegrity_Layer_<layer name>:<layer version>]
Test Full Log Forwarder Installation
Install and configure Protegrity Agent, Protector, and Log Forwarder components.
Send a protect operation to the protector using a data element or user which will result in audit log generation
Navigate to the CloudWatch log group for the Protect function
Select the log stream for the test operation and scroll to the latest logs
Expect to see a log similar to the below:
[2024-07-09T19:28:23.158] [INFO] [kinesis-external-sink.cpp:51] Sending 2 logs to Kinesis ... [2024-07-09T19:28:23.218] [INFO] [aws-utils.cpp:206] Kinesis send time: 0.060sNavigate to the CloudWatch log group for the Log Forwarder function
Expect to see a new log stream - it may take several minutes for the stream to start
Select the new stream and scroll to the most recent logs in the stream
Expect to see a log similar to the below:
[2024-07-09T19:32:31.648] [INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed records
Troubleshooting
Error | Action |
|---|---|
Log forwarder log contains severe level secrets permissions error: |
|
When testing log forwarder as described in Test Log Forwarder Installation, response contains policy decryption error: |
|
Cloudformation stack creation fails with error: |
|
Severe level kinesis permissions log message in protector function: |
|
TLS errors reported in log forwarder function logs: |
|
1.3.6 -
Cheat Sheet Recommendation
Tip
During the installation you will need output of steps, such as resources names and ids. We recommend copying the following cheat sheet into a notepad and fill in the information as you progress with the installation.AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
S3 Bucket name (ArtifactS3Bucket): ___________________
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
ProtectLambdaPolicyName: __________________
Role ARN (LambdaExecutionRoleArn): ___________________
ApiGatewayId: ________________________________
ProtectFunctionName: __________________________
ProtectLayerName: _____________________________
ESA IP address: ___________________
VPC name: ___________________
Subnet name: ___________________
Policy Agent Security Group Id: ___________________
ESA Credentials Secret Name: ___________________
Policy Name: ___________________
Agent Lambda IAM Execution Role Name: ___________________
1.3.7 -
Prerequisites
Requirement | Detail |
|---|---|
Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
1.3.8 -
AWS Services
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
API Gateway | Provides the endpoint and access control. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials . |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
1.3.9 -
Required Skills and Abilities
Role / Skillset | Description |
|---|---|
AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
1.4 - REST API
The following sections describe the key concepts in understanding the REST API.
Base URL:
https://{ApiGatewayId}.execute-api.{Region}.amazonaws.com/pty/v1
Once Protegrity Serverless REST API is installed, you can export the OpenAPI documentation file from API Gateway Export API, located in the AWS API Gateway Control Service.
https://docs.aws.amazon.com/apigateway/latest/developerguide/api-gateway-export-api.html
For testing the REST API, we recommend using tools, such as, Postman.
1.4.1 - Authorization
Policy Users
Protegrity Policy roles defines the unique data access privileges for every member. The Protegrity Lambda protects the data with the username sent in either the JWT-formatted authorization header or the request body.
The lambda behavior can be set in the Lambda environment variables as described in Protect Lambda Configuration
| Authorization/allow_assume_user | 0 | 1 |
|---|---|---|
| Empty | User from the request body. / (Throw an error). | User from the request body. |
| JWT | User from JWT payload | User from request body. If not found user from JWT payload. |
JWT Verification
To ensure the integrity of the user, the lambda protect can verify the JWT.
- From your AWS console, navigate to lambda and select the following Lambda: Protegrity_Protect_RESTAPI_<STACK_NAME>
- Scroll down to the Environment variables section, select Edit to replace the entries.
Parameter | Value | Notes |
|---|---|---|
authorization | JWT | |
jwt_verify | 1 |
|
jwt_secret_base64 | Secret in base64 encoding. For example, the value of the public key is as follows. This public key will be stored as follows. | The secret must be in base64. We recommend using RSA public certificates, it is not recommended to keep Hash (symmetric) secrets in the clear. |
1.4.2 - HTTP Status Codes
The following table explains the different HTTP Status Codes with their corresponding response.
Status Codes | Response | Description |
|---|---|---|
200 | | Success protected data is in results, and success attribute is true |
400 | | There was an issue in the request, success is false, check error_msg attribute. For more information check AWS Lambda’s CloudWatch logs. For example, the following error appears.
|
403 | |
|
500 | |
Authorization is to JWT and jwt _user_claim is not a valid json array. Example valid input: [“username”, “firstname”].
|
1.4.3 - Payload Encoding
Payload Encoding
The following encoding formats are supported in the REST API.
For every encoding, the resultant protected data is returned in the same encoding. For example, if request is hex-encoded, the response is also hex-encoded.
For more information about the encoding formats, refer to the Protection Methods Reference.
Encoding | Supported by data elements | Notes |
|---|---|---|
utf8 | All except binary data elements. | Default encoding if encoding is not specified. |
hex | All | Default encoding for binary data elements. |
base64 | All |
|
base64_mime | All |
|
base64_pem | All |
|
base64_url | All |
|
1.4.4 - TLS Mutual Authentication
By default, AWS API Gateway supports HTTPS endpoint and doesn’t allow HTTP protocol.
For an additional layer of security, you can configure AWS API Gateway TLS Mutual Authentication.
AWS API Gateway will ensure that the clients with a valid certificate only can call the REST API. Protegrity recommends to setup TLS Mutual Authentication in AWS API Gateway. For more information on how to set AWS API Gateway Mutual TLS go to the following link.
https://docs.aws.amazon.com/apigateway/latest/developerguide/rest-api-mutual-tls.html
1.4.5 - v1 Specification
AWS Lambda service limits maximum size of payload to 6 MB. Client applications of Protegrity Cloud API must ensure their payload size is within this limit. This applies to all types of requests described below.
Request
AWS Lambda service limits maximum size of payload to 6 MB. Client applications of Protegrity Cloud API must ensure their payload size is within this limit. This applies to all types of requests described below.
Performs a policy operation such as protect, unprotect, or reprotect.
URI
/v1/protector/v1/unprotector/v1/reprotectMethod
POST
Parameters
data: Input data to the policy operation.
data_element: Data element to use for the policy operation.
encoding: Optional, encoding of the data. One of: base64, base64_mime, base64_pem, base64_url, hex, or utf8. Defaults to hex for binary data elements, otherwise defaults to utf8.
external_iv: Optional, external initialization vector.
old_data_element: (reprotect) Data element for unprotecting the input.
old_external_iv: (reprotect) Optional, external initialization vector for the input.
query_id: Optional, identifier for the request.
user: User performing the operation.
Result
Returns the output of the policy operation.
Example 1 - without external IV
{
"encoding": "utf8",
"query_id": "1",
"user": "user1",
"data_element": "Alphanum",
"data":[<data1>,<data2>]
}
Example 2 - with external IV
{
"encoding": "utf8",
"query_id": "1",
"user": "user1",
"data_element": "Alphanum",
"external_iv": "abc123",
"data":[<data1>,<data2>]
}
Example 3 - reprotect
{
"encoding": "utf8",
"query_id": "1",
"user": "user1",
"data_element": "deName",
"old_data_element": "Alphanum",
"data":[<data1>,<data2>]
}
Performs policy operations using different data elements for each data set.
URI
/v1/protector/v1/unprotector/v1/reprotectMethod
POST
Parameters
encoding: Optional, encoding of the data. One of: base64, base64_mime, base64_pem, base64_url, hex, or utf8. Defaults to hex for binary data elements, otherwise defaults to utf8.
query_id: Optional, prefix for the request identifier.
user: User performing the operation.
arguments[].data: Input data to the policy operation.
arguments[].data_element: Data element to use for the policy operation.
arguments[].external_iv: Optional, external initialization vector.
arguments[].id: Optional, request identifier.
arguments[].old_data_element: (reprotect) Data element for unprotecting the input.
arguments[].old_external_iv: (reprotect) Optional, external initialization vector for the input.
Note
When multiple data elements are sent in the payload, the Cloud API generates an audit log per argument. The Cloud API appends the argument id, if it exists, to the query_id. For example: query_id.id:{id}. If an argument id is not provided then the index in the argument array is appended to the query_id. For example: query_id.index:{index}.Example 4 - multiple data elements support payload
{
"encoding": "utf8",
"query_id": "query1234",
"user": <policy_user>,
"arguments": [
{
"id": "1",
"external_iv": "<external iv>",
"data_element": "<data element name>",
"data":["<data1>","<data2>"]
},
{
"data_element": <data element name>,
"data":["<data1>","<data2>"]
}
]
}
External IV
The External IV feature provides an additional level of security by allowing different tokenized results across protectors for the same input data and token element, depending on the External IV set on each protector. External IVs must adhere to certain guardrails and not all data elements support External IV. To read more about the Tokenization model with External IV, refer to the External Initialization Vector (IV) chapter in the Protection Methods Reference.
Response
responsePayloadV1:
type: object
properties:
success:
type: bool
error_msg:
type: string
description: When success is false, error_msg is included
results:
type: array
items:
type: string
Example success:
{
"encoding": "utf8",
"results":["str1","str2"],
"success": true
}
If the request was successful, the success flag will always be true.
Example failure:
{
"error_msg": "token expired",
"success": false
}
If the request fails, the success flag will always be false.
Multi Data Elements Support Payload
responsePayloadV2:
type: object
properties:
success:
type: boolean
results:
type: array
items:
type: object
properties:
success:
type: bool
error_msg:
type: string
description: When success is false, error_msg is included
id:
type: string
description: When id is sent in the request payload, id is included in the response
results:
type: array
items:
type: string
Example success:
{
"encoding": "utf8",
"results":[
{
"encoding": "utf8",
"results":["str1","str2"],
"success": true
},
{
"encoding": "utf8",
"results":["str1","str2"],
"success": true
}
],
"success": true
}
If the all the subrequests were successful, the success flag will be true.
Example failure:
{
"results": [
{
"error_msg":
"Protect failed. Data element not found. Refer to audit log for details",
"success": false
},
{
"encoding": "utf8",
"results":["str1","str2"],
"success": true
}
],
"success": false
}
It is possible to have a mix of successful and unsuccessful results. In this case, the global success flag will be false.
1.4.6 - Legacy Specification
Protegrity has multiple products with REST API capabilities, such as Protection Server (out of support), DSG, and the latest product - IAP REST. Each one has its use case. To help you move to cloud-native implementation, Cloud Product REST API supports legacy payload.
Legacy documentation can be downloaded from AWS console, API, Models, prefix Legacy.
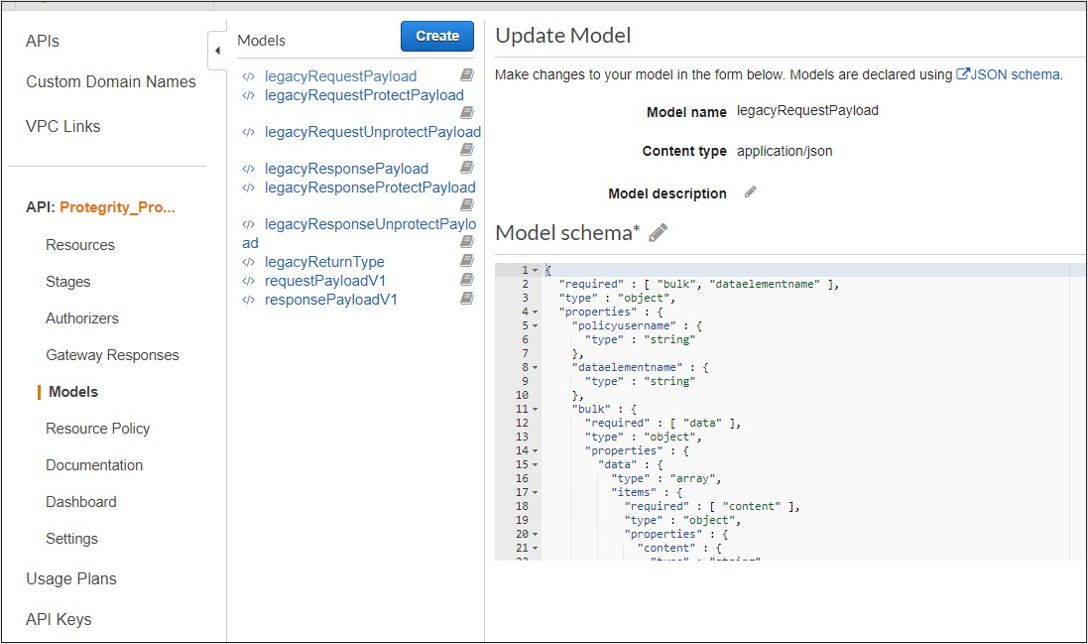
Request
Performs a policy operation such as protect, unprotect, or reprotect.
Method
POST
Parameters
dataelementname: (protect/unprotect) Data element to use for the policy operation.
externaliv: (protect/unprotect) Optional, external initialization vector.
newdataelementname: (reprotect) Data element to use for the output.
newexternaliv: (reprotect) Optional, external initialization vector for the output.
olddataelementname: (reprotect) Data element to use for the input.
oldexternaliv: (reprotect) Optional, external initialization vector for the input.
policyusername: User performing the operation.
bulk.id: Optional, identifier for the request.
bulk.data[].content: Input data to the policy operation.
Result
Returns the output of the policy operation.
Example 1 - protect without external IV
{
"protect": {
"policyusername": "user1",
"dataelementname": "Alphanum",
"bulk": {
"id": "1",
"data": [
{
"content": <Data encoded in base64>
}
]
}
}
}
Example 2 - protect with external IV
{
"protect": {
"policyusername": "user1",
"dataelementname": "Alphanum",
"externaliv": "abc123",
"bulk": {
"id": "1",
"data": [
{
"content": <Data encoded in base64>
}
]
}
}
}
Example 3 - unprotect
{
"unprotect": {
"policyusername": "user1",
"dataelementname": "Alphanum",
"bulk": {
"id": "1",
"data": [
{
"content": <Data encoded in base64>
}
]
}
}
}
Example 4 - reprotect
{
"reprotect": {
"policyusername": "user1",
"newdataelementname": "deName",
"olddataelementname": "Alphanum",
"bulk": {
"id": "1",
"data": [
{
"content": <Data encoded in base64>
}
]
}
}
}
Response
Example:
{"protect":{"bulk":{"returntype":"success","data":[{"returntype":"success","message":"Data
protection was successful.","content":"RGZBUFR4ODAzejFwNjQ5TWg0TEFpcFNqbA=="},{"returntype":"success",
"message":"Data protection was successful.","content":"aHNnVVB5QWFDYw=="}]}}}
1.5 - Performance
Performance Considerations
The following factors may cause variation in real performance versus benchmarks:
- Cold startup: The Lambda spends additional time on the initial invocation to decrypt and load the policy into memory. This time can vary between 400 ms and 1200 ms depending on the policy size. Once the Lambda is initialized, subsequent “warm executions” should process quickly.
- Noisy neighbors: There are many multi-tenant components in the Cloud. The same request may differ by 50% between runs regardless of Protegrity. A single execution may not be the best predictor of average performance.
- Size of policy: The size of the policy impacts cold start performance. Larger policies take more time to initialize.
- Lambda memory: AWS provides more virtual cores based on the memory configuration. The initial configuration of 1728MB provides a good tradeoff between performance and cost with the benchmarked policy. Memory can be increased to optimize for your individual case.
- Number of protect, unprotect and reprotect security operations.
- Lambda Concurrent and Burst quotas: AWS limits the number of concurrent executions and how quickly lambda can scale to meet demand. This is discussed in an upcoming section of the document.
- Size of data element. Operations on larger text may take more time.
- API Gateway Authentication. API Gateway support different authorizers and authentication method, which may differ.
Lambda Tuning
AWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region.

The concurrent executions quota cap is the maximum number of Lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket.
The Burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. After the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a 429 Too Many Requests response.
The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended to select an AWS region with the highest burst limits.
API Gateway Tuning
AWS maintains a Throttle quota for the API Gateway. By default, API Gateway limits concurrent requests to 10,000 requests per second and throttles subsequent traffic with a 429 Too Many Requests error response. This quota applies across all APIs in an account and region.
The API Gateway default quota may need to be increased based on the Concurrency table. Keep in mind that hitting quota limits effectively throttles any other API services in the region.
The API Gateway also limits burst. Burst is the maximum number of concurrent requests that API Gateway can fulfill at any instant without returning 429 Too Many Requests error responses. This limit can be increased by AWS, but is not adjustable.
Enable CloudWatch metrics within the API Gateway to monitor max concurrency and investigate throttling errors. See the Concurrency Troubleshooting section on interpreting CloudWatch metrics.
Quotas adjustments are applied for region and account. Throttling is also enabled by default in the API Gateway stage used by the Protegrity Lambda function. The stage configuration throttling must be adjusted if the quota is modified. Stage throttling is shown in the following image.
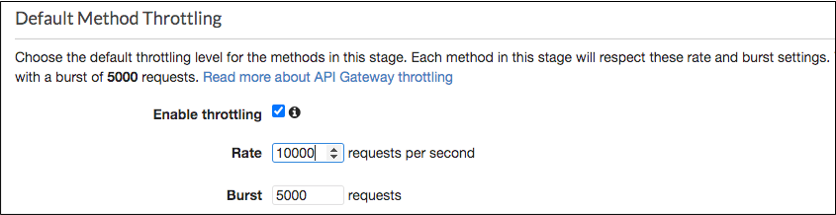
For example, the REST Client makes over 20,000 requests/sec to execute the given query. Using API Gateway’s default settings, the requests exceeding 10,000 requests/sec will be throttled. Therefore, this query may fail intermittently due to a high number of throttling errors.
Concurrency Troubleshooting
Hitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a client query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your API Gateway or Lambda services in the region.
CloudWatch Metrics can be manually enabled on the API Gateway to reveal if quotas are being reached. Metrics aggregate errors into two buckets that are 4xx and 5xx. CloudWatch logs can be used to access the actual error code. The following table describes how to interpret the CloudWatch metrics.
| Error Type | Possible issue | Remedy |
|---|---|---|
| 4xx errors | API Gateway burst or throttle quota exceeded | Request an increase to the API Gateway throttle quota. |
| 5xx errors | Lambda concurrent requests or burst quota exceeded. Verify 4xx errors in Lambda Metrics. | Request an increase the Lambda concurrent request quota |
Note
The API Gateway Lambda proxy maps 429 errors from the Lambda service to 500 errors.The following screenshot shows an example of searching CloudWatch Logs using Log Insights:
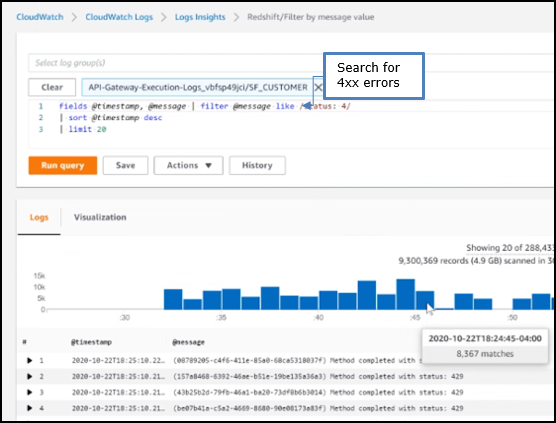
Cold-Start Performance
Cold-start vs warm execution refers to the state of the Lambda when a request is received. A cold-start undergoes additional initialization, such as, loading the security policy. Warm execution applies to all subsequent requests served by the Lambda.
The following table shows an example how these states impact latency and performance:
| Execution state | Avg. Execution Duration | Avg. Total (w/ network latency) |
|---|---|---|
| Cold execution | 438 ms | 522 ms |
| Warm execution | < 2ms | 84 ms |
Note
Cold execution time will vary based on the physical size of the security policy. A large security policy will result in longer cold startup times.Log Forwarder Performance
Log forwarder architecture is optimized to minimize the amount of connections and reduce the overall network bandwidth required to send audit logs to ESA. This is achieved with batching and aggregation taking place on two levels. The first level is in protect function instances, where audit logs from consecutive requests to an instance are batched and aggregated. The second level of batching takes place in Amazon Kinesis Stream where log records from different protect function instances are additionally batched and sent to log forwarder function where they are aggregated. This section shows how to configure the deployment to accommodate different patterns of anticipated audit log stream. It also shows how to monitor deployment resources to detect problems before audit records are lost.
Protector Cloud Formation Parameters
AuditLogFlushInterval: Determines the minimum amount of time required for the audit log to be sent to Amazon Kinesis. Changing flush interval may affect the level of aggregation, which in turn may result in different number of connections and different data rates to Amazon Kinesis. Default value is 30 seconds.
Increasing the flush interval may result in higher aggregation of audit logs, in fewer connections to Amazon Kinesis, in higher latency of audit logs arriving to ESA and in higher data throughput.
Lowering the flush interval may result in lower aggregation of audit logs, in more connections to Amazon Kinesis, in lower latency of audit logs arriving to ESA and in lower data throughput.
It is not recommended to reduce the flush interval from default value in production environment as it may overload the Amazon Kinesis service. However, it may be beneficial to reduce flush interval during testing to make audit records appear on ESA faster.
Log Forwarder Cloud Formation Parameters
Amazon KinesisLogStreamShardCount: The number of shards represents the level of parallel streams in the Amazon Kinesis and it is proportional to the throughput capacity of the stream. If the number of shards is too low and the volume of audit logs is too high, Amazon Kinesis service may be overloaded and some audit records sent from protect function may be lost.
Default value is 10, however you are advised to test with a production-like load to determine whether this is sufficient or not.
Amazon KinesisLogStreamRetentionPeriodHours: The time for the audit records to be retained in Amazon Kinesis log stream in cases where log forwarder function is unable to read records from the Kinesis stream or send records to ESA, for example due to a connectivity outage. Amazon Kinesis will retain failed audit records and retry periodically until connectivity with ESA is restored or retention period expires.
Default value is 24 hours, however you are advised to review this value to align it with your Recovery Time Objective and Recovery Point Objective SLAs.
Monitoring Log Forwarder Resources
Amazon Kinesis Stream Metrics: Any positive value in Amazon Kinesis PutRecords throttled records metric indicates that audit logs rate from protect function is too high. The recommended action is to increase the Amazon KinesisLogStreamShardCount or optionally increase the AuditLogFlushInterval.
Log Forwarder Function CloudWatch Logs: If log forwarder function is unable to send logs to ESA, it will log the following message:
[SEVERE] Dropped records: x.Note
When the error message above occurs, the dropped audit records will be preserved in the Amazon Kinesis data stream and retried again according to Amazon Kinesis retry schedule. Records will be retried until Amazon KinesisLogStreamRetentionPeriodHours expires.Protect Function CloudWatch Logs: If protect function is unable to send logs to Amazon Kinesis, it will log the following message:
[SEVERE] Amazon Kinesis error, retrying in x ms (retry: y/z) ..."Any dropped audit log records will be reported with the following log message:
[SEVERE] Failed to send x/y audit logs to Amazon Kinesis.
1.6 - Audit Logging
Audit Logging
Audit records and application logs stream to Amazon CloudWatch Logs or optionally be sent to ESA. Cloud Protect uses a JSON format for audit records that is described in the following sections.
You can analyze and alert on audit records using Protegrity ESA or Amazon CloudWatch. Third-party solutions may be used if they are supported by Amazon Cloudwatch or AWS Lambda logging extensions. For more information about forwarding your audit records to ESA, contact Protegrity. For more information about Amazon CloudWatch, refer to the Amazon CloudWatch User Guide.
For more information about audit records, refer to the Protegrity Analytics Guide.
Audit record fields
The audit record format has been altered in version 3.1 of the protector to provide more information.
| Field | Description |
|---|---|
| additional_info.deployment_id | The deployment_id contains the name of the Protect Function. It is automatically set based on the cloud-specific environment variables assigned to the Protect Function. This allows identifying the Cloud Protect deployment responsible for generating audit log. |
| additional_info.cluster | (Optional) Redshift cluster ARN |
| additional_info.description | A human-readable message describing the operation |
| additional_info.query_id | (Optional) Identifies the query that triggered the operation |
| additional_info.request_id | (Optional) AWS Lambda request identifier |
| cnt | Number of operations, may be aggregated |
| correlationid | (Deprecated) Use additional_info instead |
| level | Log severity, one of: SUCCESS, WARNING, ERROR, EXCEPTION |
| logtype | Always “Protection” |
| origin.ip | The private IP address of the compute resource that operates the Protect Function and is responsible for generating the log entry.NoteThe IP address is private, meaning it is used for internal network communication and is not accessible directly from the public internet.When Log Forwarding is enabled the IP address may be aggregated into minimal CIDR blocks. |
| origin.hostname | Hostname of the system that generated the log entry |
| origin.time_utc | UTC timestamp when the log entry was generated |
| protection.audit_code | Audit code of the protect operation; see the log return codes table in the Protegrity Troubleshooting Guide |
| protection.dataelement | Data element used for the policy operation |
| protection.datastore | Name of the data store corresponding to the deployed policy |
| protection.mask_setting | (Optional) Mask setting from policy management |
| protection.operation | Operation type, one of: Protect, Unprotect, Reprotect |
| protection.policy_user | User that performed the operation |
| protector.core_version | Internal core component version |
| protector.family | Always “cp” for Cloud Protect |
| protector.lambda_version | Protector Lambda application version. |
| protector.pcc_version | Internal pcc component version |
| protector.vendor | Identifies the cloud vendor and the database vendor |
| protector.version | Protector version number |
| signature.checksum | Hash value of the signature key ID used to sign the log message when the log is generated |
| signature.key_id | Key used to sign the log message when the log is generated |
Example Audit Records
The following are sample audit messages:
Protect Success:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "Data protect operation was successful.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "SUCESS",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 6,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "B324AF7C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
User permission denied:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The user does not have the appropriate permissions to perform the requested operation.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 3,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "A216797C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
Data element not found:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The data element could not be found in the policy.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 2,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "AF09217C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
1.7 - No Access Behavior
No Access Behavior
The security policy maintains a No Access Operation, configured in an ESA, which determines the response for unauthorized unprotect requests.
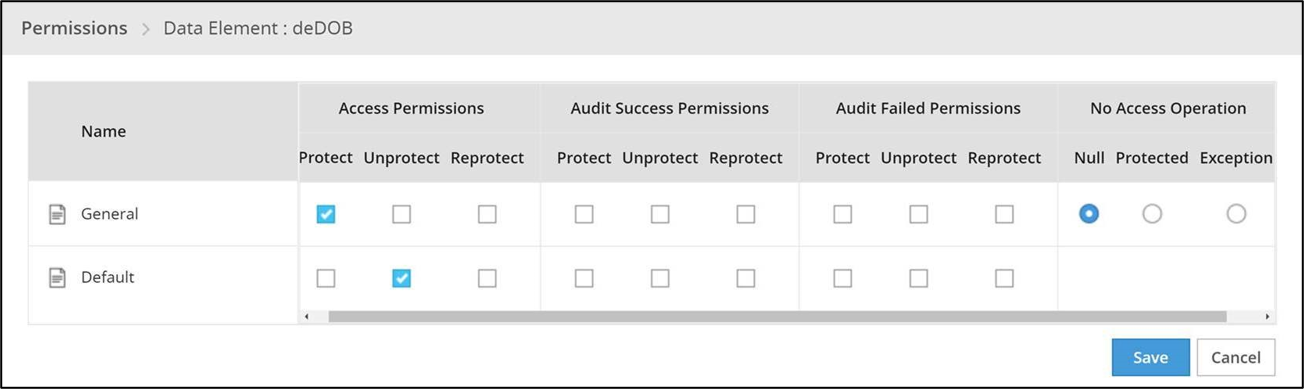
The following table describes the result returned in the response for the various no access unprotect permissions.
| No Access Operation | Data Returned |
|---|---|
| Null | null |
| Protected | (protected value) |
| Exception | Query will fail with an exception |
Note
An unauthorized protect will throw an exception.1.8 - Known Limitations
Known Limitations
Known product limitations:
- FPE is supported only for ASCII values.
1.9 - Upgrading To The Latest Version
Download the Latest Version
You can download the latest version of the deployment package from https://my.protegrity.com. Navigate to Data Protection > Cloud Protect to download the latest version.
After downloading the deployment package from the Protegrity Portal, unzip the package to extract the artifact files. In the AWS Console, navigate to the S3 bucket that was previously created to upload deployment artifacts (see: Create S3 bucket for Installing Artifacts).
Note
Only extract the deployment package and not the files in it.Upload the following artifacts to the S3 bucket:
- -- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-athena-protect-udfs-<version>.jar
- protegrity-external-extension-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-sample-policy-<version>.zip
If the release version matches your existing deployment, you don’t need to upload it again. Save the following artifacts on your local system so that you have them available during the next steps:
- -- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_api_cf.json
- pty_agent_cf.json
- pty_log_forwarder_cf.json
- pty_athena_protect_cf.json
- pty_agent_cf.json
Perform the following steps to upgrade the Agent Lambda and Protect Lambda separately.
Important
If new versions are available for both Agent and Protect Lambdas, Agent Lambda must be upgraded first.Disable Protegrity Agent Function CloudWatch Event Rule
Cloud Watch Event Rule is used to periodically run Protegrity Agent Function to synchronize policy from ESA. This functionality is optional when deploying Protegrity Serverless Solution. If the Event Rule is enabled, it must be disabled temporarily for the time of the upgrade process.
Follow the steps below to determine if your deployment uses Event Rule and disable it.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Resources tab from the top portion of the screen.
Check if there is a resource with ScheduledRule LogicalID. If there is no such resource you can skip to Upgrading Policy Agent Lambda section. If the scheduled rule is there, continue with the next steps in this section.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Disable from the top-right portion of the screen. This will disable the rule. You will re-enable it after the upgrade process is complete.
Upgrading Policy Agent Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Agent Lambda upgrade.Go to AWS Lambda console and select existing Protegrity Agent Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish. The version of Agent Lambda you just created will serve as restore point in the case you needed to rollback the upgrade.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonGo to AWS Cloud Formation and select existing Protegrity Agent deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_agent_cf.json file and select Next.
Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Navigate back to Agent Lambda Function.
Note
Make sure you are viewing the latest Lambda Function, not the published version.Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current agent installation version is lower than 3.0.12, make sure you set the following function configuration variables:
- PTY_ADDIPADDRESSHEADER
- PTY_ESA_CA_SERVER_CERT You can read more about these variables in section Policy Agent Lambda Configuration.
If you are upgrading from versions prior to v3.0, backup and remove existing policy from the bucket defined by AWS_POLICY_S3_BUCKET property, so that the policy can be re-downloaded and re-encrypted with new ‘key commitment’ feature.
If you are upgrading from version prior to 1.6.1 please follow the steps below, otherwise the upgrade process is completed.
From AWS Console, navigate to IAM > Policies
Search for the Agent Lambda IAM Policy created in Create Agent Lambda IAM policy
Click on the policy, then select Edit Policy. Select JSON tab.
Add the following statement to the list of policy statements.
{ "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }Click Review Policy, then Save Changes. Wait for the changes to save.
Upgrading Log Forwarder Lambda
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], skip this section and follow instruction to install new Log Forwarder Audit Log Forwarder Installation.Publish Log Forwarder Lambda Version
Publishing a version of the Log Forwarder Lambda allows to roll-back to pre-existing version if upgrade fails
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Log Forwarder Lambda version number for roll-backs: ___________________
Disable Kinesis Trigger
Disabling Kinesis trigger ensures there are no unprocessed or re-processed events while function is upgraded.
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Uncheck Activate trigger and click Save
- Wait for function to stop processing events by monitoring function in Monitor tab
Upgrade Forwarder Lambda Version
Upgrade Log Forwarder function with new code
- Go to AWS Cloud Formation and select existing Protegrity Log Forwarder deployment stack.
- Select Update Stack > Make a direct update.
- Select Replace existing template > Upload a template file.
- Upload pty_log_forwarder_cf file and select Next.
- Click Next until Review window and then select Update stack.
- Wait for the Cloud Formation to complete.
Enable Kinesis Trigger
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Check Activate trigger and click Save Log Forwarder function will now start processing events from where it left off when Kinesis trigger was disabled.
Monitor and roll-back
Monitor Log Forwarder function for errors in its CloudWatch logs and in Montior tab. To roll back function to the previous version if any errors occur follow these steps:
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Select Configuration tab > Triggers
Expand Details section of Kinesis trigger and record UUID value
Execute the following AWS CLI command to move Kinesis trigger to previous version of Log Forwarder Lambda that was created earlier and recorded as Log Forwarder Lambda version number for roll-backs. Substitute kinesis-mapping-uuid, log-forwarder-function-name, version-for-roll-backs with your values:
aws lambda update-event-source-mapping --uuid <kinesis-mapping-uuid> --function-name <log-forwarder-function-name>:<version-for-roll-backs>Find Kinesis trigger attached to previous version of Log Forwarder Lambda by navigating Versions tab > Version number link in the Versions column Kinesis trigger is now moved to previous version of Log Forwarder Lambda function.
Upgrading Protect Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Diagram below illustrates upgrade steps.
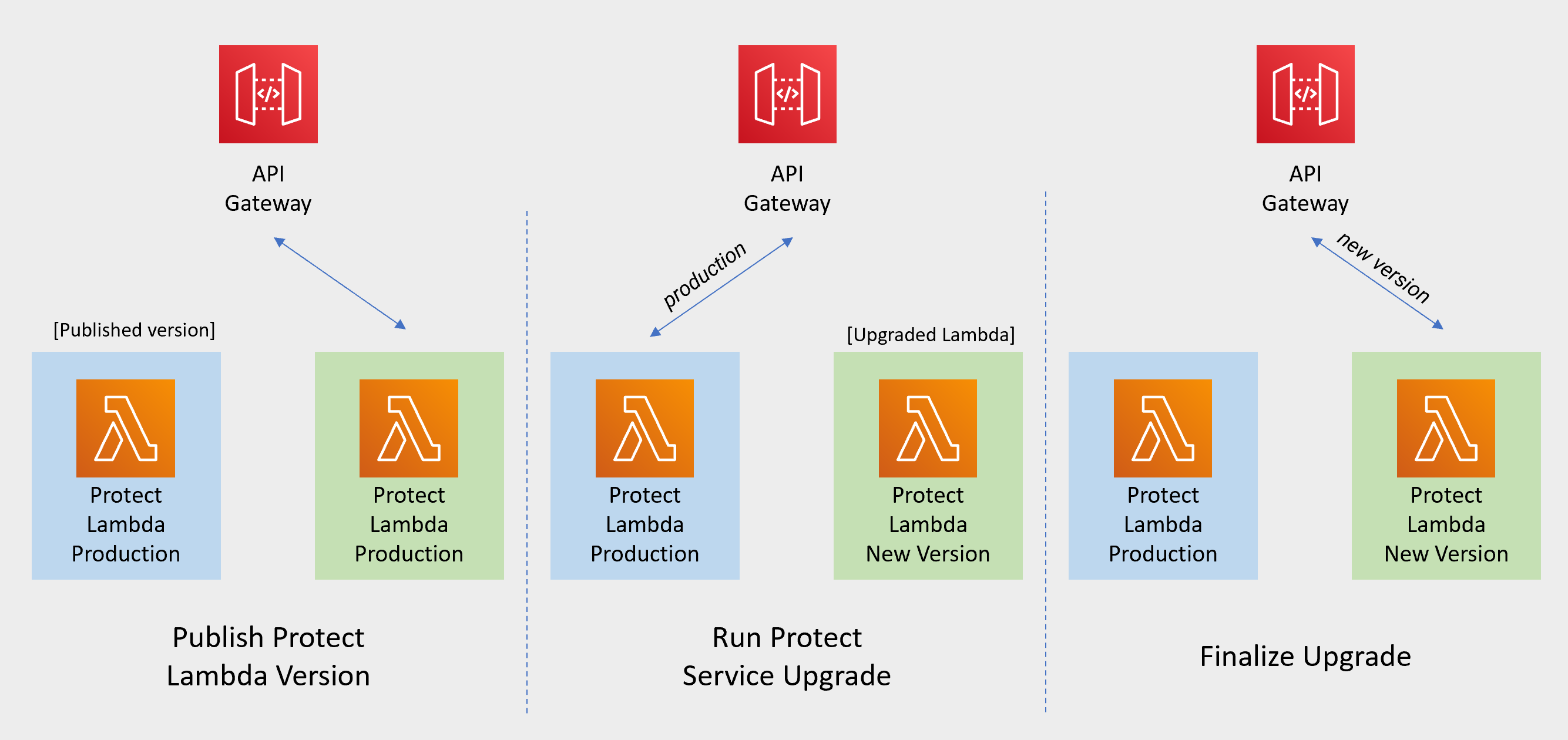
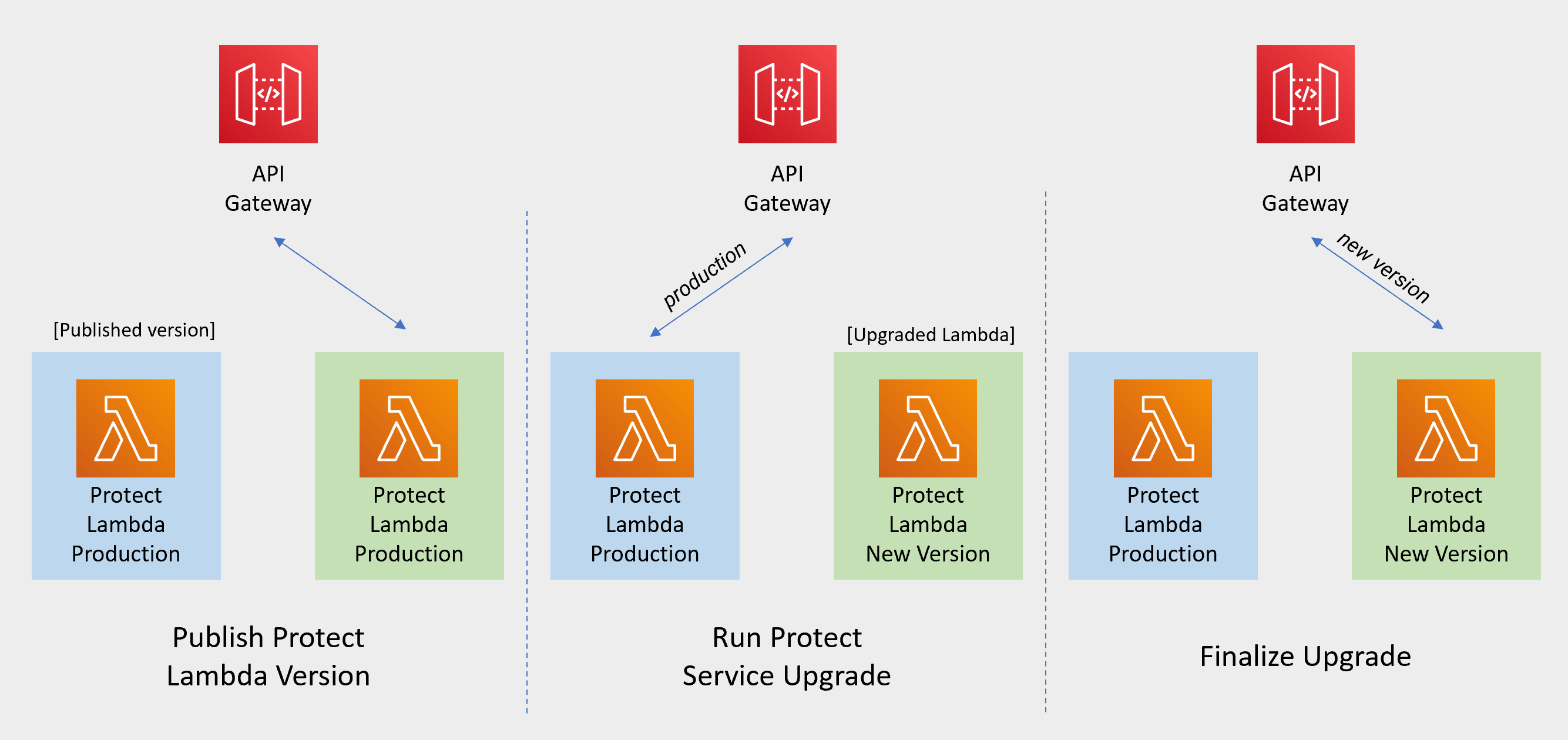
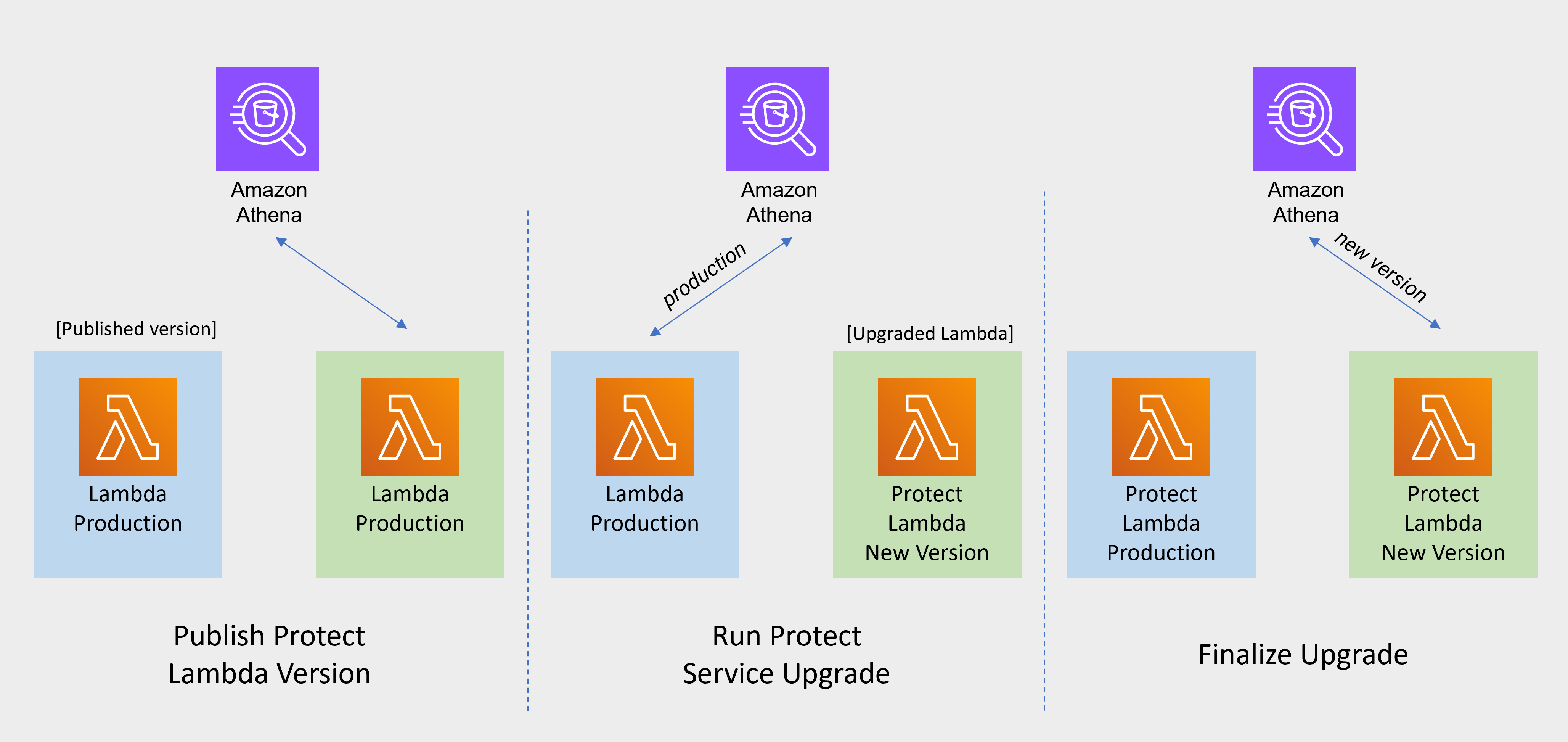
Publish Protect Lambda Version
Publishing a version of the Protect Lambda allows updating it without interruptions to the existing traffic.
Go to AWS Lambda console and select existing Protegrity Protect Lambda.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonClick Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Protect Lambda version number: ___________________
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:<protect_lambda_version_number>' iam_role 'arn:aws:iam::123456789212:role/example_role';
Run protect service upgrade
In this step, the Protect service including Lambda $LATEST version will be updated using Cloud Formation template. The Lambda version created in previous step will be used to serve existing traffic during the upgrade process.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_protect_cf.json file and select Next.
Update ProtectFunctionProductionVersion parameter with Protect Lambda version number recorded in step 3.
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation for the newly deployed log forwarder.Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Go back to Lambda console and select Protect Lambda.
Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current protect installation version is lower than 3.0.14, you can optionally set the following variable:
- LOG_REDSHIFT_CLUSTER_ARN You can read more about this configuration in section Protect Lambda Configuration.
Navigate to Aliases tab. Verify that Production alias points to the lambda version you specified in the cloud formation template.
The upgraded Protect Lambda is configured with a sample policy. Run Agent Lambda Function before continuing with next steps.
Finalize upgrade
In this step, the Protect Lambda will be configured to serve traffic using $LATEST version upgraded in the previous step.
Go back to Protegrity AWS Cloud Formation deployment stack.
Select Update. Check Use Current template.
Update ProtectFunctionProductionVersion parameter with the following value: $LATEST.
Click Next until Review window and then select Update stack.
Go back to Lambda console and select Protect Lambda.
From the Lambda console, verify that Latest alias points to $LATEST version.
Test your function to make sure it works as expected.
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:Production' iam_role 'arn:aws:iam::123456789212:role/example_role';If you need to rollback to older version of Protect Lambda, you can re-run the cloud formation with ProtectFunctionProductionVersion parameter set to the previous version of Protect Lambda.
Re-enable Protegrity Agent Function CloudWatch Event Rule
If the Event Rule was disabled at the beginning of the upgrade process, you must re-enabled it. Follow the steps below to re-enable Policy Agent Event rule.
Go to the Protegrity Agent Cloud Formation Stack.
Select Resources tab from the top portion of the screen.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Enable from the top-right portion of the screen. This will enable the rule. You will re-enable it after the upgrade process is complete.
1.10 - Appendices
1.10.1 - ADFS Federation using AWS Cognito User Pools
ADFS Federation using AWS Cognito User Pools
Common use case for Protegrity Policy Member source integrates with customer’s Active Directory. The AWS API Gateway can integrate with ADFS using AWS Cognito. The following article describes the procedure.
1.10.2 - Installing the Policy Agent and Protector in Different AWS Accounts
The Policy Agent Lambda function and Protect Lambda functions can be installed in separate AWS accounts. However, additional configuration is required to authorize the Policy Agent to provision the security policy to a remote Protect Lambda function.
Note
The Policy Agent will deploy an encrypted security policy file to an S3 bucket in the Protect function’s AWS Account.Create Agent Lambda IAM policy
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace the wildcards (*) with the region, account, and resource name information where required.
Select Review policy, type in the policy name, and confirm. Record policy name:
Agent Lambda Cross Account Policy Name: ___________________
Create Policy Agent cross-account IAM Role
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Roles > Create Role
Select AWS Service > Lambda . Proceed to Permissions.
Select Policy created in the step above. Proceed to Tags.
Specify Tag, proceed to the final screen. Type in policy name and confirm. Record the name.
Policy Agent Cross Account IAM Role Name: ___________________
Allow the Policy Agent Cross-Account Role to be Assumed by the Policy Agent IAM Role
Login to the AWS account that hosts the Protect Lambda function.
Navigate to the previously created IAM Role (Agent Lambda Cross-Account IAM Role Name).
Navigate to Trust Relationships > Edit Trust Relationships.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda IAM Execution Role ARN> with ARN of Agent Lambda IAM Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Click Update Trust Policy.
Add Assume Role to the Policy Agent Execution IAM Role
Login to the AWS account that hosts the Policy Agent.
Navigate to the Agent Lambda IAM Execution Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Add Inline Policy.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda Cross-Account IAM ARN> with the value recorded in Create Policy Agent cross-account IAM Role.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "sts:AssumeRole" ], "Resource": "<Agent Lambda Cross-Account IAM ARN>." } ] }When you are finished, choose Review Policy.
On the Review policy page, type a Name, then choose Create Policy.
Update the Policy Agent Lambda Configuration
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select Configuration tab | Environment variables.
Select Edit and add the following environment variables with the value from Agent Lambda Cross-Account IAM ARN:
Parameter Value AWS_ASSUME_ROLE Agent Lambda Cross-Account IAM ARN Ensure the values in the Parameters AWS_POLICY_S3_BUCKET, AWS_PROTECT_FN_NAME and AWS_POLICY_LAYER_NAME are all in the Protect Lambda Function AWS Account.
In case custom VPC hostname configuration is used, you will need to set the ENDPOINT_URL. Refer to Policy Agent - Custom VPC Endpoint Hostname Configuration.
AWS_VPC_ENDPOINT_URL
<AWS_VPC_ENDPOINT>
Click Save and Run the Lambda. The Lambda will now assume the Role in Protect Lambda Function AWS Account and update the policy cross accounts.
1.10.3 - Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
This guide describes how to configure the Protegrity Policy Agent and Log Forwarder to connect to a Protegrity Provisioned Cluster (PPC), highlighting the differences from connecting to ESA.
Key Differences: PPC vs ESA
| Feature | ESA 10.2 | PPC (this guide) |
|---|---|---|
| Datastore Key Fingerprint | Optional/Recommended | Required |
| CA Certificate on Agent | Optional/Recommended | Optional/Recommended |
| CA Certificate on Log Forwarder | Optional/Recommended | Not supported |
| Client Certificate Authentication from Log Forwarder | Optional/Recommended | Not supported |
| IP Address | ESA IP address | PPC address |
Prerequisites
- Access to PPC and required credentials.
- Tools:
curl,kubectlinstalled.
Policy Agent Setup with PPC
Important
When connecting to PPC, the Policy Agent requires thePTY_DATASTORE_KEY fingerprint. For ESA 10.2, the fingerprint is optional but recommended. See Policy Agent Installation for general setup steps.Follow these instructions as a guide for understanding specific inputs for Policy Agent integrating with PPC:
Obtain the Datastore Key Fingerprint
To retrieve the fingerprint for your Policy Agent:
curl -k -H "Authorization: Bearer ${TOKEN}" -X POST https://${HOST}/pty/v2/pim/datastores/1/export/keys -H "Content-Type: application/json" --data '{ "algorithm": "RSA-OAEP-256", "description": "example-key-from-kms", "pem": "-----BEGIN PUBLIC KEY-----\nABC123... ...890XYZ\n-----END PUBLIC KEY-----" }'Sample Output:
{"uid":"1","algorithm":"RSA-OAEP-256","fingerprint":"4c:46:d8:05:35:2e:eb:39:4d:39:8e:6f:28:c3:ab:d3:bc:9e:7a:cb:95:cb:b1:8e:b5:90:21:0f:d3:2c:0b:27","description":"example-key-from-kms"}Record the
fingerprintvalue and configure it as thePTY_DATASTORE_KEYfor the Policy Agent.Retrieve the PPC CA Certificate
To obtain the CA certificate from PPC:
kubectl -n api-gateway get secret ingress-certificate-secret -o jsonpath='{.data.ca\.crt}' | base64 -d > CA.pemUse the
CA.pemthat was returned as described in Policy Agent Installation.Configure the PPC Address
Use the PPC address in place of the ESA IP address wherever required in your configuration.
Log Forwarder Setup with PPC
Note
When using PPC, certificate authentication and CA validation are not supported for the Log Forwarder. Configuration steps related to certificates in Log Forwarder Installation do not apply to PPC. If you attempt to use certificates provided by PPC, the Log Forwarder will not function correctly.- The Log Forwarder will proceed without certificates and will print a warning if
PtyEsaCaServerCertandPtyEsaClientCertificatesSecretIdare not provided. - No additional certificate or CA configuration is needed for PPC.
Troubleshooting
Protector Lambda fails with “AWS KMS Decrypt failed”
Symptom:
After a successful Policy Agent run and layer update, the Protector Lambda returns:
{
"body": "{\"error_msg\":\"Failed to open decoder: rpdecode decrypt failure: dek callback failed: AWS KMS Decrypt failed: \",\"success\":false}",
"isBase64Encoded": false,
"statusCode": 400
}
The Protector Lambda logs show:
[SEVERE] [utils.cpp:185] AWS KMS Decrypt failed:
Cause:
The public key configured in the PPC/ESA datastore does not match the KMS key pair used by the Policy Agent. The policy package is encrypted with the public key stored in the datastore. If that key does not correspond to the KMS key pair whose private key is used for decryption, the Protector Lambda will fail to decrypt the policy.
Resolution:
- Identify the KMS key pair used by the Policy Agent (the key ARN configured during pre-configuration).
- Export the public key from that KMS key pair.
- In PPC/ESA, ensure the datastore’s export key is configured with the public key from that same KMS key pair. See Obtain the Datastore Key Fingerprint above.
- Re-run the Policy Agent to generate a new policy package encrypted with the correct key.
- Test the Protector Lambda again.
Important
Always verify that the public key registered in the PPC/ESA datastore belongs to the same KMS key pair referenced by the Policy Agent. A mismatch between these keys is a common cause of AWS KMS Decrypt failed errors.
The KMS key must be an asymmetric key with the Encrypt and decrypt key usage type. Symmetric keys or asymmetric keys configured for signing will not work.
Additional Notes
- For troubleshooting, consult the Protegrity Documentation.
1.10.4 - Invoke Lambda Directly
AWS Lambda can be invoked directly, such as from AWS SDK. This section contains information about request and response payloads with examples demonstrating direct invocation using AWS CLI and Python SDK (Boto3).
Request Payload
Lambda request payload for the direct invocation is defined as following
{
"body": "<rest-api-request-payload>",
"path": "/v1/<operation>",
"headers": {}
}
- body - JSON string. Request schemas defined in Rest API Request.
- path - can be either ‘/v1/protect’ or ‘/v1/unprotect’.
- headers - can be used to pass authorization headers. See example below.
Example request:
{
"body": "{\"query_id\": \"3\",\"user\": \"user1\",\"data_element\": \"deAlpha\",\"data\": [\"data1\", \"data2\"]}",
"path": "/v1/protect",
"headers": {}
}
Example Request with JWT authorization:
Note
Lambda Environment sample configuration:
authorization="jwt"
jwt_verify=1
allow_assume_user=1
jwt_user_claim="username"
jwt_secret_base64="Must be set to public certificate"
See REST API Authorization for JWT configuration details.
{
"body": "{\"query_id\": \"3\",\"user\": \"user1\",\"data_element\": \"deAlpha\",\"data\": [\"data1\", \"data2\"]}",
"path": "/v1/protect",
"headers": {
"authorization": "bearer eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJpYXQiOjE2MTM4NjIzNzEsImlkIjoiYS1iLWMtZC1lLWYtMS0yLTMiLCJ1c2VybmFtZSI6IlBhdWwgQXRyZWlkZXMifQ.R1NcJ43540HKdhEBOK9WaMMpjBOYSJetckQKrcPQdz0z6sx1EDwHXYngBP9DtHgUM-6Vf1VNjtFh_Nqfeepp1BavmigIXoe3ZbrxRI3DFKi2UuLmgn--EYrSGlWsQjnmjaz5qUkID9iY2MtsRunKSuolSvG9UsD1G32kv0KZYX0"
}
}
Response Payload
Lambda response payload has the following structure
{
"body": "<rest-api-response-payload>"
"isBase64Encoded": false,
"statusCode": <http-status-code>,
}
- body - JSON string. Response schemas defined in Rest API Response.
- isBase64Encoded - always set to false.
- statusCode - HTTP status code integer.
Success Response Payload Example:
{
"body": "{\"encoding\":\"utf8\",\"results\":[\"xcgd\", \"migs\"],\"success\":true}",
"isBase64Encoded": false,
"statusCode": 200
}
Error Response
Cloud API Lambda returns following error responses depending on the error type
Cloud API Protection Operation Error
Returned when invalid data element is used or user has insufficient permissions to execute security operation.
{
"body": "{\"error_msg\":\"Unprotect failed. Data element not found. Refer to audit log for details.\",\"success\":false}",
"isBase64Encoded": false,
"statusCode": 400
}
Cloud API Invalid Request Error
Missing fields in the incoming request or malformed request JSON.
{
"body": "Request format is not supported",
"isBase64Encoded": false,
"statusCode": 400
}
Cloud API Unexpected Lambda Exception Error
Caused by Lambda runtime exception, for instance due to too short timeout or not enough memory.
{
"errorMessage": "2023-01-18T16:42:19.593Z d0cf62d0-9eaf-427b-8ca5-1bdd8bd0b082 Task timed out after 10.25 seconds"
}
Examples
Prerequisites:
- AWS SDK or Command Line
- AWS Access Key ID and AWS Access Key
Note
IAM roles must follow the Principle of Least Privilege. Only users / services who must have access need to have invoke permissions on AWS Lambda.See Request Payload for request payload examples.
AWS CLI command to invoke Cloud API Lambda function:
aws lambda invoke --function-name Protegrity_Protect_RESTAPI_{stackname} --payload
fileb://request_payload.json --log-type Tail output
Sample Python code demonstrating Cloud API Direct Lambda Calls
import json
import logging
import boto3
lambda_client = boto3.client("lambda")
logging.basicConfig(format="%(message)s")
logger = logging.getLogger('pty_cloud_api_sample')
logger.setLevel(logging.DEBUG)
class ProtectClient(object):
"""
Sample client demonstrating how to invoke Protegrity Cloud API Lambda
protect_fn: str - Name of the Cloud API Lambda (for example, Protegrity_Protect_RESTAPI_my_deployment)
"""
def __init__(self, protect_fn):
self.protect_fn = protect_fn
def invoke_protect(self, values, data_element, operation, user, query_id,
column_info=""):
"""
Invokes Protegrity Cloud API Lambda to execute protect or unprotect operation
values: list[str] - List of values to be protected/unprotected
data_element: str - Name of the policy data element to use with protect/unprotect operation
operation: str - Either 'protect' or 'unprotect'
user: str - Policy user
query_id: str - Query id will be present in the audit log
column_info: - Used for troubleshooting, for instance, when protecting values/rows from multiple database columns
"""
# Set authorization header here if JWT authorization is
# enabled in Cloud API Function configuration
headers = {"Authorization": ""}
request_body = {
"user": user,
"data_element": data_element,
"data": values,
"query_id": query_id
}
payload = json.dumps({"body": json.dumps(request_body), "path": f"/v1/{operation}",
"headers": headers})
logger.debug(f"Request payload: {payload}")
response = lambda_client.invoke(FunctionName=self.protect_fn, Payload=payload)
lambda_response_payload = json.loads(response["Payload"].read().decode())
logger.debug(f"Response payload: {lambda_response_payload}")
response_status_code = lambda_response_payload.get("statusCode")
response_body_string = lambda_response_payload.get("body")
if response_status_code == None or response_body_string == None:
raise Exception(f"Unexpected Cloud API Lambda error: [{lambda_response_payload}]")
try:
body_json = json.loads(response_body_string)
if response_status_code == 200:
return body_json.get("results", [])
elif body_json.get("error_msg"):
raise Exception(f"Cloud API Lambda error: [{response_status_code} - {body_json.get('error_msg')}]")
raise Exception(f"Unexpected Cloud API Lambda error: [{lambda_response_payload}]")
except json.decoder.JSONDecodeError:
# Cloud API may return error in the response body
# For example, {"statusCode": 400, "body":"Error message"}
raise Exception(f"Cloud API Lambda error: [{response_status_code} - {response_body_string}]")
# Replace cloud-api-lambda-name with the name of the Cloud API Lambda
# For example, Protegrity_Protect_RESTAPI_my_deployment
protect_client = ProtectClient('cloud-api-lambda-name')
protected_data = ["UtfVk UHgcD!"]
logger.info(f"Protected data: {protected_data}")
unprotected_data = protect_client.invoke_protect(
values=protected_data,
data_element='alpha',
operation='unprrotect',
user='test-user',
query_id='1234')
logger.info(f"Unprotected data: {unprotected_data}")
1.10.5 - Policy Agent - Custom VPC Endpoint Hostname Configuration
The Policy Agent uses default endpoint hostnames to communicate with other AWS services (for example, secretsmanager.amazonaws.com). This configuration will only work in VPCs where Amazon-provided DNS is available (default VPC configuration with private DNS option enabled for the endpoint). If your VPC uses custom DNS, follow the instructions below to configure the Policy Agent Lambda to use custom endpoint hostnames.
Note
This configuration is only available with the Cloud Protect version 1.5.0 or higher. For more information about the upgrade instructions, refer to Upgrading to the Latest Version.Identify DNS Hostnames
To identify DNS hostnames:
From AWS console, select VPC > Endpoints.
Select Secrets Manager endpoint from the list of endpoints.
Under Details > DNS Names, note the private endpoint DNS names adding https:// at the beginning of the endpoint name.
For example, https://vpce-1234-4pzomrye.kms.us-west-1.vpce.amazonaws.com
Note down DNS names for the KMS and Lambda endpoints:
AWS_SECRETSMANAGER_ENDPOINT: https://_________________
AWS_KMS_ENDPOINT: https://_________________
AWS_LAMBDA_ENDPOINT: https://_________________
Update the Policy Agent Lambda configuration
To update policy agent lambda configuration:
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select the Configuration section and choose Environment variables.
Select Edit and add the following environment variables with the corresponding endpoint URLs recorded in steps 3-4:
Parameters Value AWS_SECRETSMANAGER_ENDPOINT_URL <AWS_SECRETS_ENDPOINT> AWS_KMS_ENDPOINT_URL <AWS KMS ENDPOINT> AWS_LAMBDA_ENDPOINT_URL <AWS LAMBDA ENDPOINT> Click Save and Run the Lambda. The Lambda will now use endpoints you have just configured.
1.10.6 - Protection Methods
Protection Methods
For more information about the protection methods supported by Protegrity, refer to the Protection Methods Reference.
Tokenization Type | Supported Input Data Types | Notes |
|---|---|---|
Numeric Credit Card Alpha Upper-case Alpha Alpha-Numeric Upper Alpha-Numeric Lower ASCII Printable Decimal Unicode Unicode Base64 Unicode Gen2 | STRING NULL | |
Integer | NUMBER NULL | |
Date Datetime | STRING NULL | For information about supported formats, refer to the Protection Methods Reference. |
Binary | STRING NULL | Must be |
Protection Method | Supported Input Data Types | Notes |
|---|---|---|
No Encryption | STRING NUMBER NULL |
Encryption Algorithm | Supported Input Data Types | Notes |
|---|---|---|
3DES AES-128 AES-256 CUSP 3DES CUSP AES-128 CUSP AES-256 | STRING | Must be |
1.10.7 - Configuring Regular Expression to Extract Policy Username
Configuring Regular Expression to Extract Policy Username
Cloud Protect Lambda Function exposes USERNAME_REGEX configuration to allow extraction of policy username from user in the request.
USERNAME_REGEX Lambda Environment configuration
The USERNAME_REGEX configuration can be used to extract policy username from user in the request. The following are allowed values for USERNAME_REGEX:
1 - Default build-in regular expression is used:
^arn:aws:(?:iam|sts)::[0-9]{12}:(?:role|user|group|assumed\-role|federated\-user)\/([\w\/+=,.\-]{1,1024}|[\w\/+=,.\-@]{1,1024})(?:@[a-zA-Z0-9\-]{1,320}(?:\.\w+)+)?$^User regex$ - Custom regex with one capturing group. This group is used to extract the username. Examples below show different regular expression values and the resulting policy user.
USERNAME_REGEX | User in the request | Effective Policy User |
|---|---|---|
Not Set | arn:aws:iam::123456789012:user/juliet.snow | arn:aws:iam::123456789012:user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | arn:aws:sts::123456789012:assumed-role/TestSaml | |
1 | arn:aws:iam::123456789012:user/juliet.snow | juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | TestSaml | |
| arn:aws:iam::123456789012:user/juliet.snow | user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | assumed-role/TestSaml |
1.10.8 - Associating ESA Data Store With Cloud Protect Agent
Associating ESA Data Store With Cloud Protect Agent
ESA controls which policy is deployed to protector using concept of data store. A data store may contain a list of IP addresses identifying servers allowed to pull the policy associated with that specific data store. Data store may also be defined as default data store, which allows any server to pull the policy, provided it does not belong to any other data stores. Node registration occurs when the policy server (in this case the policy agent) makes a policy request to ESA, where the agent’s IP address is identified by ESA.
Note
For more information about ESA data store refer to Policy Management Guide which is part of Protegrity ESA documentation.Policy agent lambda source IP address used for node registration on ESA depends on ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP and the PTY_ADDIPADDRESSHEADER configuration exposed by the agent lambda.
The Lambda service uses multiple network interfaces, internal network interface with ephemeral IP range of 169.254.x.x and external network interface with IP range of the VPC subnet the Lambda is associated with. By default, when agent lambda is contacting ESA to register node for policy download, ESA uses agent Lambda VPC IP address. This default behavior is caused by the default ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP=false and agent default configuration PTY_ADDIPADDRESSHEADER=yes.
In some cases, when there is a proxy server between the ESA and agent lambda, the desirable ESA configuration is ASSIGN_DATASTORE_USING_NODE_IP=true. and PTY_ADDIPADDRESSHEADER=no which will cause the ESA to use proxy server IP address.
The table below shows how the hubcontroller and agent settings will affect node IP registration on ESA.
| Agent source IP | Agent VPC subnet IP | Proxy IP | ESA config - ASSIGN_DATASTORE_USING_NODE_IP | Agent lambda config - PTY_ADDIPADDRESSHEADER | Agent node registration IP |
|---|---|---|---|---|---|
| 169.254.144.81 | 10.1.2.173 | No Proxy | true | yes | 169.254.144.81 |
| true | no | 10.1.2.173 | |||
| false | yes | ||||
| false | no | ||||
| 169.254.144.81 | 10.1.2.173 | 34.230.42.110 | true | yes | 169.254.144.81 |
| true | no | 34.230.42.110 | |||
| false | yes | ||||
| false | no |
2 - Athena
This section describes the high-level architecture of Athena, installation procedures, and performance guidance. This section focuses on Protegrity specific aspects and should be consumed in conjunction with the corresponding AWS documentation.
This guide may also be used with the Protegrity Enterprise Security Administrator Guide, which explains the mechanism for managing the data security policy.
2.1 - Overview
Solution Overview
Athena Protector on AWS is a cloud native, serverless product for fine-grained data protection with Amazon Athena. It enables invocation of Protegrity data protection operations from Amazon Athena SQL.
The product provides data protection services invoked by External User Defined Functions (UDFs) within Amazon Athena. The UDFs act as a client transmitting micro-batches of data to a remote Protegrity Athena Protector. The protector runs inside a serverless AWS Lambda function. User queries from Amazon Athena may generate hundreds or thousands of parallel requests to perform security operations. Protegrity’s serverless solution is designed to scale and yield reliable query performance under such load.
The Amazon Athena Protector utilizes a data security policy from an Enterprise Security Administrator (ESA), similar to other Protegrity products.
Analytics on Protected Data
Protegrity’s format and length preserving tokenization scheme make it possible to perform analytics directly on protected data. Tokens are join-preserving so protected data can be joined across datasets. Often statistical analytics and machine learning training can be performed without the need to re-identify protected data. However, a user or service account with authorized security policy privileges may re-identify subsets of data using the Athena Protector on AWS service.
Features
Athena Protector on AWS incorporates Protegrity’s patent-pending vaultless tokenization capabilities into cloud-native serverless technology. Combined with an ESA security policy, the protector provides the following features:
- Role-based access control (RBAC) to protect and unprotect (re-identify) data depending on the user privileges.
- Policy enforcement features of other Protegrity application protectors.
For more information about the available protection options, such as, data types, Tokenization or Encryption types, or length preserving and non-preserving tokens, refer to Protection Methods Reference.
2.2 - Architecture
Deployment Architecture
The Amazon Athena Protector should be deployed in the customer’s AWS account. The product incorporates Protegrity’s vaultless tokenizationengine within an AWS Lambda Function. The data security policy from an ESA is provisioned periodically as a static, encrypted resource through an AWS Lambda Layer. The policy is decrypted in memory at runtime within the Lambda. This architecture allows Protegrity to be highly available and scale very quickly without direct dependency on other Protegrity services.
The product exposes a remote data protection service invoked from external User Defined Functions (UDFs), a native feature of Amazon Athena.The UDFs is invoked by users through SQL queries. The Amazon Athena execution engine makes remote calls to the Protegrity product to perform protect and unprotect data operations. Each network request includes a micro-batch of data to process and a secure payload including the federated user (if available) and the data element type. The product applies the ESA security policy including user authorization and returns a corresponding response.
When used with an Enterprise Security Administrator (ESA) application, the security policy is synchronized through another serverless component called the Protegrity Policy Agent. The agent operates on a configurable schedule, fetches the policy from the ESA, performs additional envelope encryption using Amazon KMS, and deploys the policy into the Lambda Layer used by the serverless product. This solution can be configured to automatically provision the static policy or the final step can be performed on-demand by an administrator. The policy takes effect immediately for all new requests. There is no downtime for users during this process.
The following diagram shows the high-level architecture described above.
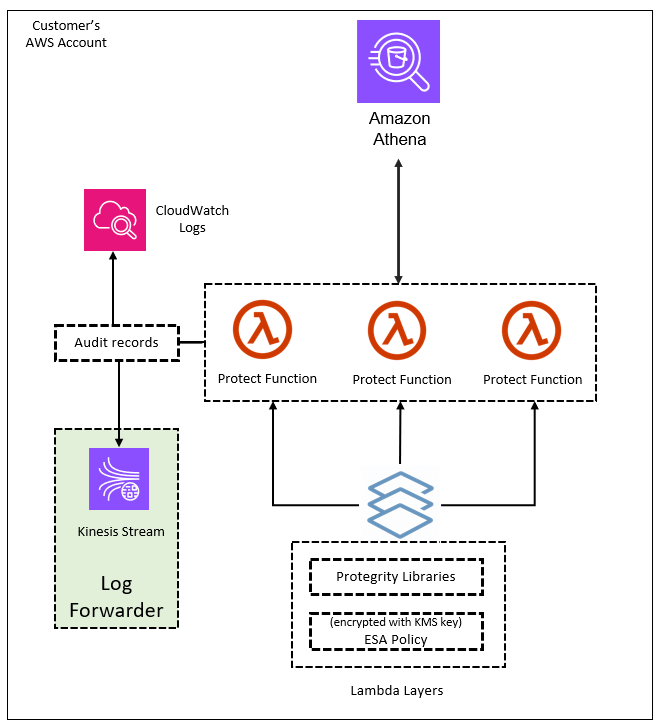
The following diagram shows a reference architecture for synchronizing the security policy from the ESA to the product.
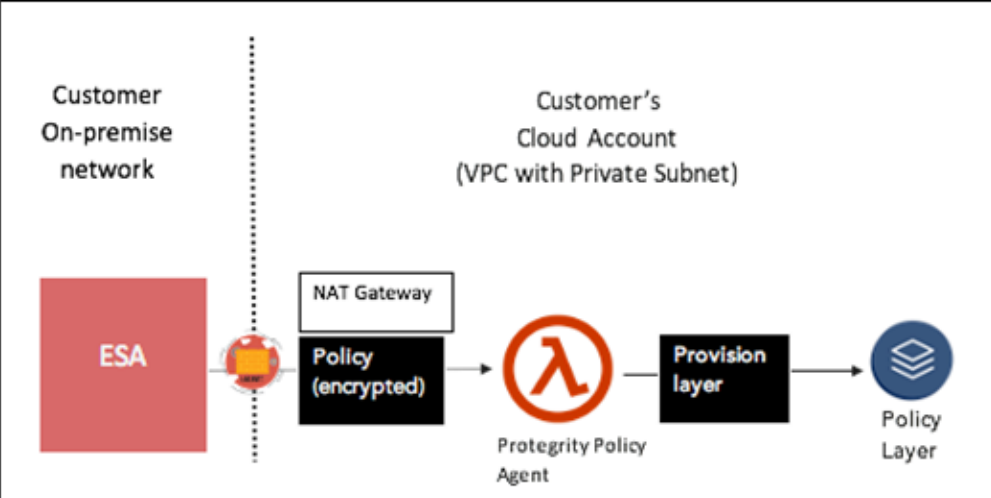
The Protegrity Policy Agent requires network access to an Enterprise Security Administrator (ESA). Most organizations install the ESA on-premise. Therefore, it is recommended that the Policy Agent is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
The ESA is a soft appliance that must be pre-installed on a separate server. It is used to create and manage security policies.
For more information about installing the ESA, and creating and managing policies, refer the Policy Management Guide.
Log Forwarding Architecture
Audit logs are by default sent to CloudWatch as long as the function’s execution role has the necessary permissions. The Protegrity Product can also be configured to send audit logs to ESA. Such configuration requires deploying Log Forwarder component which is available as part of Protegrity Product deployment bundle. The diagram below shows additional resources deployed with Log Forwarder component.
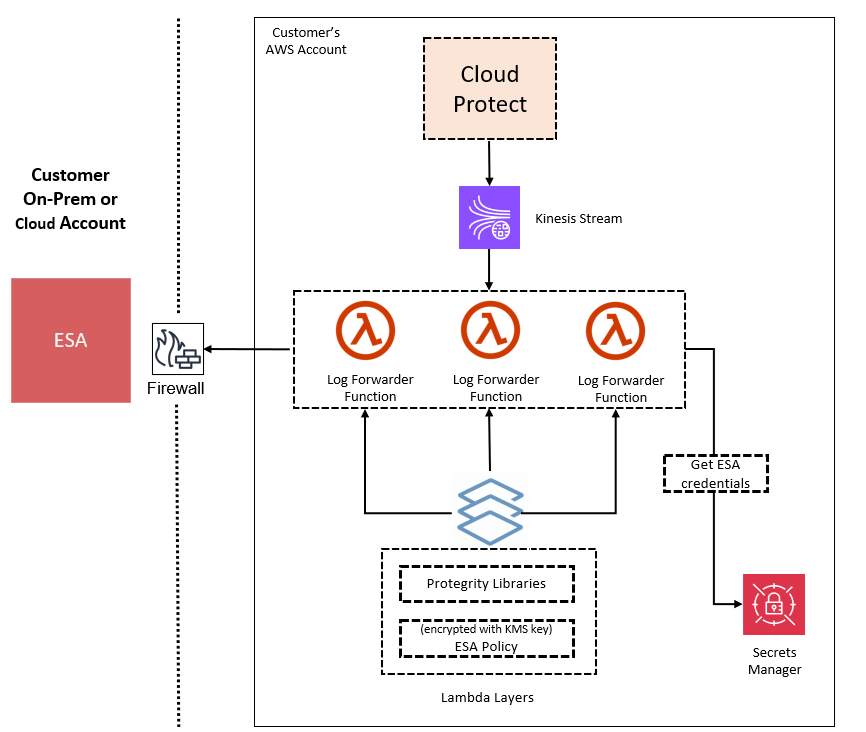
The log forwarder component includes Amazon Kinesis data stream and the forwarder Lambda function. Amazon Kinesis stream is used to batch audit records before sending them to forwarder function, where similar audit logs are aggregated before sending to ESA. Aggregation rules are described in the Protegrity Log Forwarding guide. When the protector function is configured to send audit logs to log forwarder, audit logs are aggregated on the protector function before sending to Amazon Kinesis. Due to specifics of the Lambda runtime lifecycle, audit logs may take up to 15 minutes before being sent to Amazon Kinesis. Protector function exposes configuration to minimize this time which is described in the protector function installation section.
The security of audit logs is ensured by using HTTPS connection on each link of the communication between protector function and ESA. Integrity and authenticity of audit logs is additionally checked on log forwarder which verifies individual logs signature. The signature verification is done upon arrival from Amazon Kinesis before applying aggregation. If signature cannot be verified, the log is forwarded as is to ESA where additional signature verification can be configured. Log forwarder function uses client certificate to authenticate calls to ESA.
To learn more about individual audit log entry structure and purpose of audit logs, refer to Audit Logging section in this document. Installation instructions can be found in Audit Log Forwarder installation.
The audit log forwarding requires network access from the cloud to the ESA. Most organizations install the ESA on-premise. Therefore, it is recommended that the Log Forwarder Function is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
Athena Connectivity
Amazon Athena is an interactive, serverless query service that makes it easy to analyze data in Amazo n S3 using standard SQL. Athena is serverless, so there is no infrastructure to manage, and you pay only for the queries that you run.
Athena’s external UDF makes remote invocations to the Protegrity protector, a serverless Lambda function incorporating Protegrity libraries and the Athena Query Federation SDK.
Access and authorization between various AWS services involved in this architecture is achieved throu gh Identity Access Management (IAM). For instance, the IAM principal running the query must be allowed to invoke the protect Lambda. Various IAM role configuration settings are shown in the appen dices of this document.
The following figure illustrates the Protegrity Athena Integration architecture.
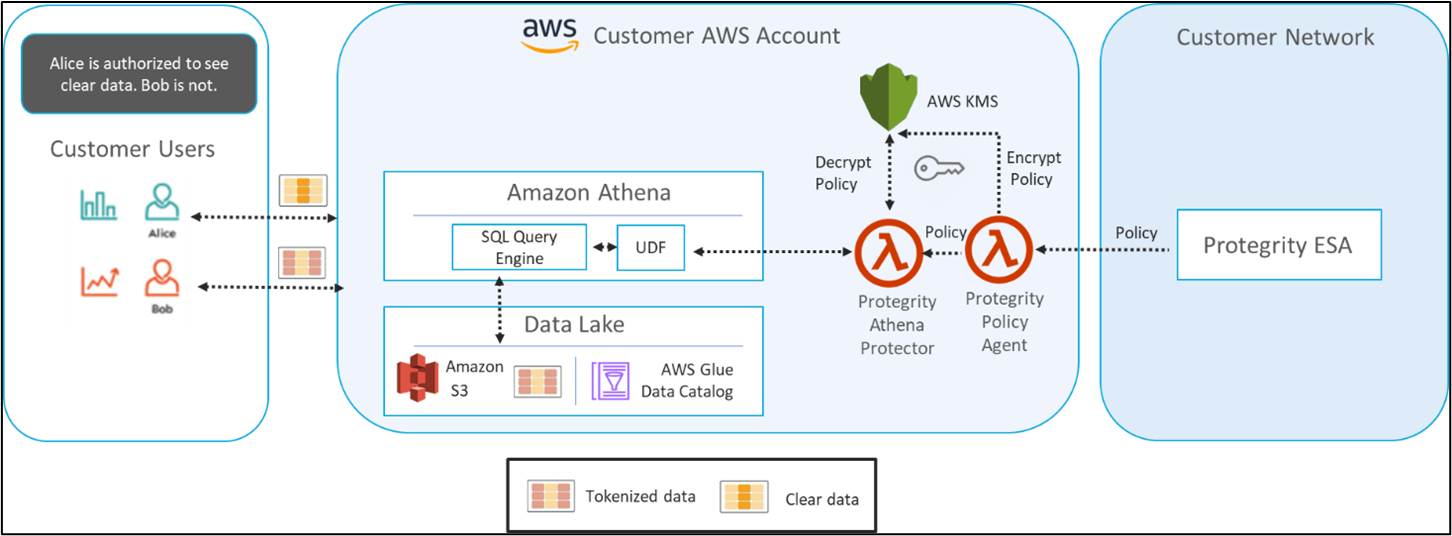
2.3 - Installation
2.3.1 - Prerequisites
AWS Service Dependencies
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials. |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
ESA Version Requirements
The Protector and Log Forwarder functions require a security policy from a compatible ESA version.
The table below shows compatibility between different Protector and ESA versions.
Note
For the latest up-to-date information refer to: Protegrity Compatibility Matrix| Protector Version | ESA Version | |||
|---|---|---|---|---|
| 8.x | 9.0 | 9.1 & 9.2 | 10.0 | |
| 2.x | No | Yes | * | No |
| 3.0.x & 3.1.x | No | No | Yes | No |
| 3.2.x | No | No | Yes | * |
| 4.0.x | No | No | No | Yes |
Legend | |
|---|---|
Yes | Protector was designed to work with this ESA version |
No | Protector will not work with this ESA version |
* | Backward compatible policy download supported:
|
Prerequisites
| Requirement | Detail |
|---|---|
| Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
| Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
| AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
| Athena Engine Version 3 | Only Athena engine version 3 is supported. The product may work in Athena engine version 2, but it is deprecated and all users are encouraged to upgrade. |
Required Skills and Abilities
Role / Skillset | Description |
|---|---|
AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
What’s Next
2.3.2 - Pre-Configuration
Provide AWS sub-account
Identify or create an AWS account where the Protegrity solution will be installed. It is recommended that a new AWS sub-account be created. This can provide greater security controls and help avoid conflicts with other applications that might impact regional account limits. An individual with the Cloud Administrator role will be required for some subsequent installation steps.
AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
Create S3 bucket for Installing Artifacts
This S3 bucket will be used for the artifacts required by the CloudFormation installation steps. This S3 bucket must be created in the region that is defined in Determine AWS Region.
To create S3 bucket for installing artifacts:
Access the AWS S3 Management Console.
Change region to the one determined in Determine AWS Region
Click Create Bucket.
Enter a unique bucket name:
For example, protegrity-install.us-west-2.example.com.
Click Create Bucket.
Upload the installation artifacts to this bucket. Protegrity will provide the following three artifacts.
- protegrity-athena-protect-udfs-<version>.jar
- protegrity-agent-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-external-extension-<version>.zip
Important
The deployment package you receive from Protegrity must be extracted to reveal the Protegrity artifacts. CloudFormation requires them in the provided .zip format. Do not extract the individual Protegrity artifacts. Upload these artifacts to the S3 bucket created.
S3 Bucket name (ArtifactS3Bucket): ___________________
Create KMS Key
The Amazon Key Management Service (KMS) provides the ability for the Protegrity Serverless solution to encrypt and decrypt the Protegrity Security Policy.
Note
It is recommended to host the KMS key in a separate AWS sub-account. This allows dual control, separating the responsibility between the key administrator and the Protegrity Serverless account administrator.To create KMS key:
In the AWS sub-account where the KMS key will reside, select the region.
Navigate to Key Management Service > Create Key.
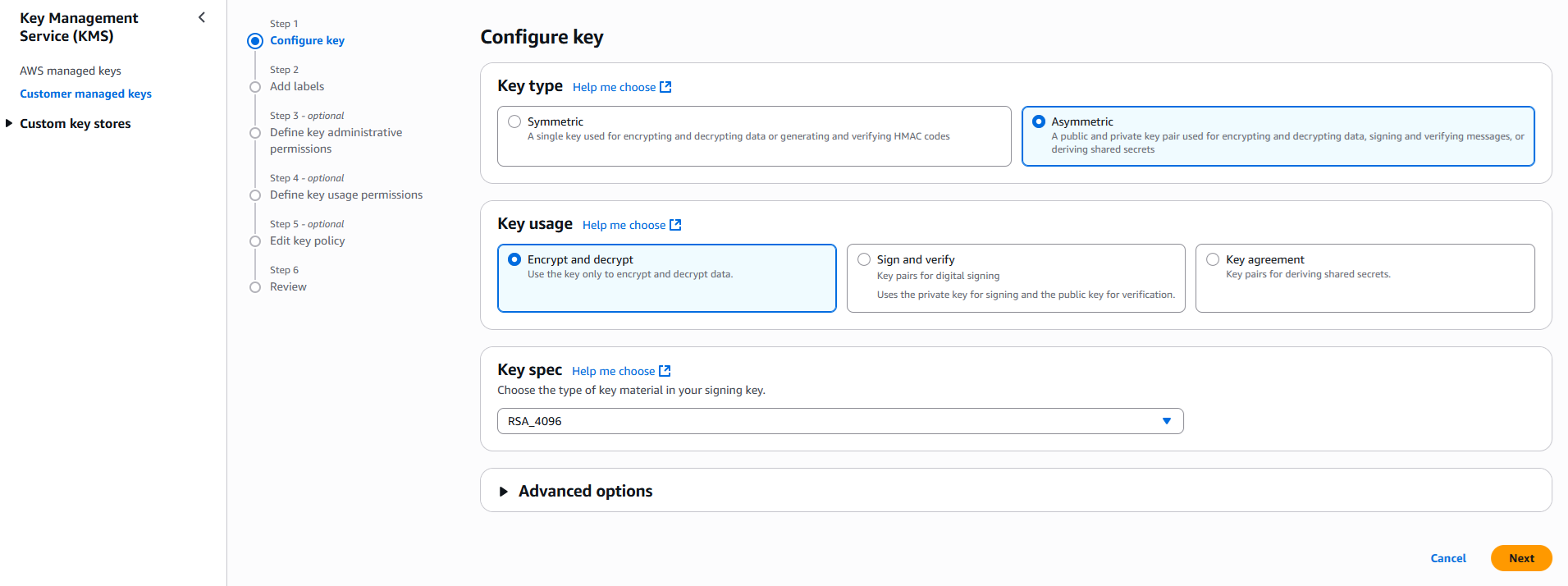
Configure the key settings:
- Key type: Asymmetric
- Key usage: Encrypt and decrypt
- Key spec: RSA_4096
- Click Next
Create alias and optional description, such as, Protegrity-Serverless and click Next.
Define key administrative permissions, the IAM user who will administrate the key.
Note
It is recommended the administrator be different than the administrator of the Protegrity Serverless accountClick Next.
Define the key usage permissions.
In Other AWS accounts, enter the AWS account id used for the Protegrity Serverless installation.
Continue on to create the key. If there is a concern this permission is overly broad, then you can return later to restrict access to the role of two Protegrity Serverless Lambda as principals. Click to open the key in the list and record the ARN.
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
Download the public key from the KMS key. Navigate to the key in KMS console, select the Public key tab, and click Download. Save the PEM file. This public key will be added to the ESA data store as an export key. Refer to Exporting Keys to Datastore for instructions on adding the public key to the data store.
Note
This step is not applicable for ESA versions lower than 10.2.KMS Public Key PEM file: ___________________
What’s Next
2.3.2.1 -
Determine AWS Region
Determine the AWS region where the Amazon Athena Workgroup is running. This is the region in where the Protegrity solution must be installed.
AWS Region (AccountRegion): ___________________
2.3.3 - Protect Service Installation
Protect Service Installation
The following sections install the Cloud Protect serverless Lambda function.
Preparation
Ensure that all the steps in Pre-Configuration are performed.
Login to the AWS account console where Protegrity Serverless will be installed.
Ensure that the required CloudFormation templates provided by Protegrity are available on your local computer.
Create Protect Lambda IAM Execution Policy
This task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Next, type in a policy name, for example, ProtegrityProtectLambdaPolicy and Create Policy. Record the policy name:
ProtectLambdaPolicyName:__________________
Create Protect Lambda IAM Role
The following steps create the role to utilize the policy defined in Create Protect Lambda IAM Execution Policy.
To create protect lambda IAM execution role:
From the AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
In the list, search and select the policy created in Create Protect Lambda IAM Execution Policy.
Click Next
Type the role name, for example, ProtegrityProtectRole
Click Create role
Record the role ARN.
Role ARN (LambdaExecutionRoleArn): ___________________
Install using CloudFormation
The following steps describe the deployment of the Lambda function.
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
In Specify template section select Upload a template file.
Click Choose file to upload the Protegrity-provided CloudFormation template called pty_athena_protect_cf.json and click Next.
Specify stack details. Enter stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter
Description
ArtifactS3Bucket
Name of S3 bucket created in the pre-configuration step
LambdaExecutionRoleArn
The ARN of Lambda role created in the prior step
PolicyUser
Name of the Policy User that will be passed as an environment variable to the lambda function. With protegrity-sample-policy-<version>.zip, you can set this value to policyuser.
PolicyUserConfig
The settings for POLICY_USER_CONFIG. Default Value: 0, Values: [0,1,2].
Note
See Policy User for information on POLICY_USER_CONFIG.UsernameRegex
The settings for USERNAME_REGEX. Default Value: Not Set, Values: “1” or regex expression.
Note
See Policy User and Configuring Regular Expression to Extract Policy Username for information on USERNAME_REGEX.MinLogLevel
Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all
The log forwarder parameters can be provided later after log forwarder is deployed. If you are not planning to deploy log forwarder you can skip this step.
Log Forwarder Parameters Description KinesisLogStreamArn The ARN of the AWS Kinesis stream where audit logs will be sent for aggregation AuditLogFlushInterval Time interval used to accumulate audit logs before sending to Kinesis Proceed to the last step of the Create Stack wizard with defaults and click Submit to create CloudFormation stack.
After CloudFormation is completed, select the Outputs tab in the stack. Record the following values:
ProtectFunctionName: __________________________
ProtectFunctionProductionAlias: __________________________
ProtectLayerName: _____________________________
Test Connectivity
Perform the following steps to verify Athena is working correctly with Protegrity.
Access the Athena console.
Copy and paste the following snippet into a worksheet.
USING EXTERNAL FUNCTION unprotect(val varchar, el varchar) RETURNS varchar LAMBDA '<replace_with_athena_protect_function_name>:Production' SELECT unprotect('UtfVk UHgcD!', 'alpha')Replace the placeholder value with the lambda function name
Run the above Query
Verify that the string hello world! is returned.
Note
See Granting access to use the Cloud Protect UDF for information on Athena query permissions.Troubleshooting Tips
Error | Action |
|---|---|
User: <USER_ARN> is not authorized to perform: glue:GetDatabases on resource: arn:aws:glue:<AWS_REGION>:<AWS_ACCOUNT>:catalog (Service: AmazonDataCatalog; Status Code: 400; Error Code: AccessDeniedException; Request ID: <REQUEST_ID>; Proxy: null) | Verify user has Glue permission GetDatabases |
User: <USER_ARN> is not authorized to perform: glue:GetTables on resource: arn:aws:glue: <AWS_REGION>:<AWS_ACCOUNT>:catalog (Service: AmazonDataCatalog; Status Code: 400; Error Code: AccessDeniedException; Request ID: <REQUEST_ID>; Proxy: null) | Verify user has Glue permission GetTables |
Insufficient permissions to execute the query | Verify user has InvokeFunction permission for the protect lambda function |
Access denied when writing output to url: s3://<BUCKET_NAME>/Unsaved/<YEAR>/<MONTH>/<DAY>/<QUERY_ID>.csv Please ensure you are allowed to access the S3 bucket. If you are encrypting query results with KMS key, please ensure you are allowed to access your KMS key | Verify user has S3 permission PutObject for the query result location bucket. If using KMS encryption, verify the required KMS permissions. |
You do not seem to have access to the S3 location of your query results. Please confirm your account has access to the S3 location where your query results are saved and try again. If you are using KMS to encrypt query results, please ensure you have permission to access your KMS key. | Verify user has S3 permission GetObject for the query result location bucket. If using KMS encryption, verify the required KMS decrypt permissions. |
User: <USER_ARN>is not authorized to perform: athena:<ACTION> on resource: arn:aws:athena:<AWS_REGION>:<ACCOUNT>:workgroup/<WORKGROUP> (Service: AmazonAthena; Status Code: 400; Error Code: AccessDeniedException; Request ID: <REQUEST_ID>; Proxy: null) | Verify user has the permissions: StartQueryExecution GetQueryResults GetWorkGroup StopQueryExecution GetQueryExecution |
java.lang.RuntimeException: Failed to initialize MemoryUtil. Was Java started with `–add-opens=java.base/java.nio=ALL-UNNAMED`? (See https://arrow.apache.org/docs/java/install.html) | Verify that the environment variable |
What’s Next
2.3.4 - Policy Agent Installation
The following sections will install the Policy Agent. The Policy Agent polls the ESA and deploys the policy to Protegrity Serverless as a static resource. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. Contact Protegrity Professional Services for further guidance on configuration alternatives in the Cloud.
Important
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), refer to the PPC Appendix: Policy Agent Certificate and Key Guidance for specific instructions on obtaining and using the CA certificate and datastore key fingerprint. The steps in this section are specific to ESA and may differ for PPC. Be sure to follow the PPC documentation for the most accurate and up-to-date setup guidance.ESA Server
Policy Agent Lambda requires ESA server running and accessible on TCP port 443.
Note down ESA IP address:
ESA IP Address (EsaIpAddress): ___________________
Certificates on ESA
Note
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), see PPC Appendix: Policy Agent Certificate Guidance for specific instructions on obtaining and using the CA certificate. The steps in this section are specific to ESA and may differ for PPC.Whether your ESA is configured with default self-signed certificate or your corporate CA certificate, Policy Agent can validate authenticity of ESA connection using CA certificate. The process for both scenarios is the same:
- Obtain CA certificate
- Convert CA certificate to a value accepted by Policy Agent
- Provide converted CA certificate value to Policy Agent
To obtain self-signed CA certificate from ESA:
Log in to ESA Web UI.
Select Settings > Network > Manage Certificates.
Hover over Server Certificate and click on download icon to download the CA certificate.
To convert downloaded CA certificate to a value accepted by Policy Agent, open the downloaded PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PTY_ESA_CA_SERVER_CERT or PTY_ESA_CA_SERVER_CERT_SECRET Lambda variable in section Policy Agent Lambda Configuration
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
Identify or Create a new VPC
Establish a VPC where the Policy Agent will be hosted. This VPC will need connectivity to the ESA. The VPC should be in the same account and region established in Pre-Configuration.
VPC name: ___________________
VPC Subnet Configuration
Identify or create a new subnet in the VPC where tha Lambda function will be connected to. It is recommended to use a private subnet.
Subnet name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoints Configuration
If an internal VPC was created, then add VPC Endpoints, which will be used by the Policy Agent to access AWS services. Policy Agent needs access to the following AWS services:
Type | Service name |
|---|---|
Interface | com.amazonaws.{REGION}.secretsmanager |
Interface | com.amazonaws.{REGION}.kms |
Gateway | com.amazonaws.{REGION}.s3 |
Interface | com.amazonaws.{REGION}.lambda |
Identify or Create Security Groups
Policy Agent and cloud-based ESA appliance use AWS security groups to control traffic that is allowed to leave and reach them. Policy Agent runs on schedule and is mostly concerned with allowing traffic out of itself to ESA and AWS services it depends on. ESA runs most of the time and it must allow Policy Agent to connect to it.
Policy Agent security group must allow outbound traffic using rules described in the table below. To edit security group navigate:
From VPC > Security Groups > Policy Agent Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG | ESA Communication |
| HTTPS | TCP | 443 | Any | AWS Services |
Record Policy Agent security group ID:
Policy Agent Security Group Id: ___________________
Policy Agent will reach out to ESA on port 443. Create following inbound security group rule for cloud-based ESA appliance to allow connections from Policy Agent:
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG |
Creating ESA Credentials
Policy Agent Lambda requires ESA credentials to be provided as one of the three options.
Note
The username and password of the ESA user requires role with Export Resilient Package and Can Create JWT Token permissions. Security Administrator is one of the predefined roles which contains the above permissions, however for separation of duties it is recommended to create custom role.Option 1: Secrets Manager
Creating secrets manager secret with ESA username and password.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the username and password key value pair.
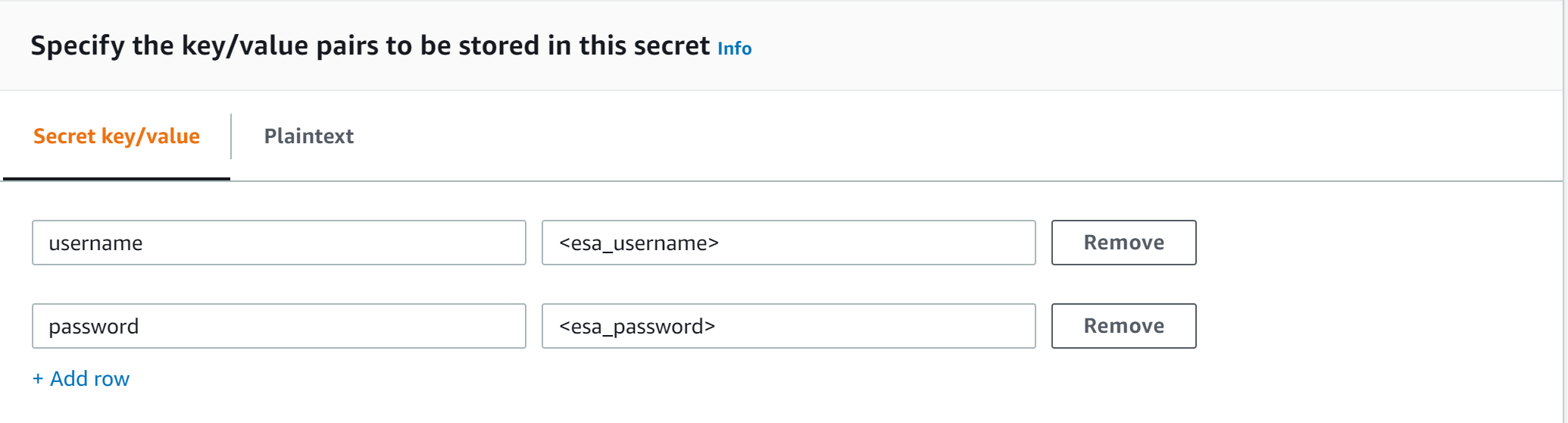
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it.
ESA Credentials Secret Name: __________________
Option 2: KMS Encrypted Password
ESA password is encrypted with AWS KMS symmetric key.
Create AWS KMS symmetric key which will be used to encrypt ESA password. See Create KMS Key for instructions on how to create KMS symmetric key using AWS console.
Record KMS Key ARN.
ESA PASSWORD KMS KEY ARN: __________________
Run AWS CLI command to encrypt ESA password. Below you can find sample Linux aws cli command. Replace <key_arn> with KMS symmetric key ARN.
aws kms encrypt --key-id <key_arn> --plaintext $(echo '<esa_password>' | base64 )Sample output.
{ "CiphertextBlob": "esa_encrypted_password", "KeyId": "arn:aws:kms:region:aws_account:key/key_id ", "EncryptionAlgorithm": "SYMMETRIC_DEFAULT" }Record ESA username and encrypted password.
ESA USERNAME: __________________
ESA ENCRYPTED PASSWORD: __________________
Option 3: Custom AWS Lambda function
With this option ESA username and password are returned by a custom AWS Lambda function. This method may be used to get the username and password from external vaults.
Create AWS Lambda in any AWS supported runtime.
There is no input needed.
The Lambda function must return the following response schema.
response: type: object properties: username: string password: stringFor example,
example output: {"username": "admin", "password": "Password1234"}Sample AWS Lambda function in Python:
import json def lambda_handler(event, context): return {"username": "admin", "password": "password1234"}Warning
Protegrity does not recommend hardcoding ESA username and password in the clear.
Record the Lambda name:
Custom AWS lambda for ESA credentials: _______________
Create Agent Lambda IAM Policy
Follow the steps below to create Lambda execution policies.
Create Agent Lambda IAM policy
From AWS IAM console, select Policies > Create Policy.
Select JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "KmsEncrypt", "Effect": "Allow", "Action": [ "kms:GetPublicKey" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace wildcard * with the region, account, and resource name information where required.
This step is required if KMS is used to encrypt ESA password.
Add policy entry below. Replace ESA PASSWORD KMS KEY ARN with the value recorded in Option 2: KMS Encrypted Password.
{ "Sid": "KmsDecryptEsaPassword", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "**ESA PASSWORD KMS KEY ARN**" ] }Select Next type in the policy name and Create Policy. Record policy name:
Policy Name: ___________________
Create Agent Lambda IAM Role
Perform the following steps to create Agent Lambda execution IAM role.
To create agent Lambda IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Agent Lambda IAM policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityAgentRole and click Confirm.
Select Create role.
Record the role ARN.
Agent Lambda IAM Execution Role Name: ___________________
Corporate Firewall Configuration
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access from the NAT Gateway IP to ESA via port 443 and 443.
CloudFormation Installation
Create the Policy Agent in the VPC using the CloudFormation script provided by Protegrity.
Access the CloudFormation service.
Select the target installation region.
Create a stack with new resources.
Upload the Policy Agent CloudFormation template (file name: pty_agent_cf.json).
Specify the following parameters for Cloud Formation:
Parameter Description Note VPC VPC where the Policy Agent will be hosted Identify or Create a new VPC Subnet Subnet where the Policy Agent will be hosted VPC Subnet Configuration PolicyAgentSecurityGroupId Security Group Id, which allows communication between the Policy Agent and the ESA Identify or Create Security Groups LambdaExecutionRoleArn Agent Lambda IAM execution role ARN allowing access to the S3 bucket, KMS encryption Key, Lambda and Lambda Layer Create Agent Lambda IAM Role ArtifactS3Bucket S3 bucket name with deployment package for the Policy Agent Use S3 Bucket name recorded in Create S3 bucket for Installing Artifacts CreateCRONJob Set to True to create a CloudWatch schedule for the agent to run. Default: False
Policy Agent Lambda Configuration
After the CloudFormation stack is deployed, the Policy Agent Lambda must be configured with parameters recorded in earlier steps. From your AWS Console, navigate to lambda and select the following Lambda.
Protegrity_Agent<STACK_NAME>_
Select Configuration tab and scroll down to the Environment variables section. Select Editand replace all entries with the actual values.
Parameter | Description | Notes |
|---|---|---|
PTY_ESA_IP | ESA IP address or hostname | |
PTY_ESA_CA_SERVER_CERT | ESA self-signed CA certificate or your corporate CA certificate used by policy Agent Lambda to ensure ESA is the trusted server. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT configuration will be ignored. |
PTY_ESA_CA_SERVER_CERT_SECRET | This configuration option fulfills the same function as PTY_ESA_CA_SERVER_CERT but supports larger configuration values, making it the recommended choice. The value should specify the name of the AWS Secrets Manager secret containing the ESA self-signed CA certificate. The secret value should be set to the json with “PTY_ESA_CA_SERVER_CERT” key and PEM formated CA certificate content value as shown below. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT_SECRET configuration will be ignored. When both PTY_ESA_CA_SERVER_CERT and PTY_ESA_CA_SERVER_CERT_SECRET are configured the PTY_ESA_CA_SERVER_CERT_SECRET takes precedence. |
PTY_ESA_CREDENTIALS_SECRET | ESA username and password (encrypted value by AWS Secrets Manager) | |
PTY_DATASTORE_KEY | ESA policy datastore public key fingerprint (64 char long) e.g. 123bff642f621123d845f006c6bfff27737b21299e8a2ef6380aa642e76e89e5. | NoteThis configuration is not applicable for ESA versions lower than 10.2.The export key is the public part of an asymmetric key pair created in a Create KMS Key. A user with Security Officer permissions adds the public key to the data store in ESA via Policy Management > Data Stores > Export Keys. The fingerprint can then be copied using the Copy Fingerprint icon next to the key. Refer to Exporting Keys to Datastore for details. NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate and Key Guidance for details on obtaining and using the datastore key fingerprint. |
AWS_KMS_KEY_ID | KMS key id or full ARN e.g. arn:aws:kms:us-west-2:112233445566:key/bfb6c4fb-509a-43ac-b0aa-82f1ca0b52d3 | |
AWS_POLICY_S3_BUCKET | S3 bucket where the encrypted policy will be written | S3 bucket of your choice |
AWS_POLICY_S3_FILENAME | Filename of the encrypted policy stored in S3 bucket | Default: protegrity-policy.zip |
AWS_PROTECT_FN_NAME | Comma separated list of Protect function names or ARNs | ProtectFunctionName(s), recorded in CloudFormation Installation |
DISABLE_DEPLOY | This flag can be either 1 or 0. If set to 1, then the agent will not update PTY_PROTECT lambda with the newest policy. Else, the policy will be saved in the S3 bucket and deployed to the Lambda Layer | Default: 0 |
AWS_POLICY_LAYER_NAME | Lambda layer used to store the Protegrity policy used by the PTY_PROTECT function |
|
POLICY_LAYER_RETAIN | Number of policy versions to retain as backup. (e.g. 2 will retain the latest 2 policies and remove older ones). -1 retains all. | Default: 2 |
POLICY_PULL_TIMEOUT | Time in seconds to wait for the ESA to send the full policy | Default: 20s |
ESA_CONNECTION_TIMEOUT | Time in seconds to wait for the ESA response | Default: 5s |
LOG_LEVEL | Application and audit logs verbiage level | Default: INFO Allowed values: DEBUG – the most verbose, INFO, WARNING, ERROR – the least verbose |
PTY_CORE_EMPTYSTRING | Override default behavior. Empty string response values are returned as null values. For instance: (un)protect(’’) -> null (un)protect(’’) -> '' | Default: empty Allowed values: null empty |
PTY_CORE_CASESENSITIVE | Specifies whether policy usernames should be case sensitive | Default: no Allowed values: yes no |
PTY_ADDIPADDRESSHEADER | When enabled, agent will send its source IP address in the request header. This configuration works in conjunction with ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP (default=false). See Associating ESA Data Store With Cloud Protect Agent for more information. | Default: yes Allowed values: yes no |
PTY_ESA_USERNAME | Plaintext ESA username which is used together with PTY_ESA_ENCRYPTED_PASSWORD as an optional ESA credentials | Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored |
PTY_ESA_ENCRYPTED_PASSWORD | ESA password encrypted with KMS symmetric key. Example AWS cli command to generate the value:
| Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored Value must be base64 encoded |
EMPTY_POLICY_S3 | This flag can be either 1 or 0. If set to 1, then the agent will remove the content of the policy file in S3 bucket, but will keep the checksum in the metadata. Else, the policy will be saved in the S3 bucket and not removed. | Default: 0 |
PTY_ESA_CREDENTIALS_LAMBDA | Lambda function to return ESA credentials | Recorded in step Option 3: Custom AWS Lambda function LAMBDA FOR ESA CREDENTIALS. Presence of PTY_ESA_USERNAME, or PTY_ESA_CREDENTIALS_SECRET will cause this value to be ignored. The Policy Agent Lambda must have network access and IAM permissions to invoke the custom ESA Credentials Lambda you have created in Option 3: Custom AWS Lambda function. |
Test Installation
Open the Lambda and configure Test to execute the lambda and specify the default test event. Wait for around 20 seconds for the Lambda to complete. If policy is downloaded successfully, then a success message appears.
Navigate to the AWS_POLICY_S3_BUCKET bucket and verify that the AWS_POLICY_S3_FILENAME file was created.
Troubleshooting
Lambda Error | Example Error | Action |
|---|---|---|
Task timed out after x seconds | |
|
ESA connection error. Failed to download certificates | ||
Policy Pull takes a long time | |
|
ESA connection error. Failed to download certificates. HTTP response code: 401 | | Ensure that the PTY_ESA_CREDENTIALS_SECRET has correct ESA username and password |
An error occurred (AccessDeniedException) when calling xyz operation | | Ensure that the Lambda execution role has permission to call the xyz operation |
Access Denied to Secret Manager. | |
|
Master Key xyz unable to generate data key | Ensure that the Lambda can access xyz CMK key | |
The S3 bucket server-side encryption is enabled, the encryption key type is SSE-KMS but the Policy Agent execution IAM role doesn’t have permissions to encrypt using the KMS key . | | Add the following permissions to the Policy Agent excution role. NoteWhen the KMS key and the Policy Agent Lambda are in separate accounts, update both the AWS KMS key and the Policy Agent execution role. |
The S3 bucket has bucket policy to only allow access from within the VPC. | | The Policy Agent publishes a new Lambda Layer version, and the Lambda Layer service uploads the policy file from the s3 bucket and the upload request is originated from the AWS service outside the Policy Agent Lambda VPC. Update the S3 bucket resource policy to allow access from AWS Service. Sample security policy to lock down access to the vpc: |
Additional Configuration
Strengthen the KMS IAM policy by granting access only to the required Lambda function(s).
Finalize the IAM policy for the Lambda Execution Role. Ensure to replace wildcard * with the region, account, and resource name information where required.
For example,
"arn:aws:lambda:*:*:function:*" -> "arn:aws:lambda:us-east-1:account:function:function_name"
Policy Agent Schedule
If specified in CloudFormation Installation, the agent installation created a CloudWatch event rule, which checks for policy update on an hourly schedule. This schedule can be altered to the required frequency.
Under CloudWatch > Events > Rules, find Protegrity_Agent_{stack_name}. Click Action > Edit Set the cron expression. A cron expression can easily be defined using CronMaker, a free online tool. Refer to http://www.cronmaker.com.
What’s Next
2.3.5 - Audit Log Forwarder Installation
The following sections show steps how to install Audit Log Forwarder component in the AWS Cloud. The Log Forwarder deployment allows for the audit logs generated by Protector to be delivered to ESA for auditing and governance purposes. Log Forwarder component is optional and is not required for the Protector Service to work properly. See Log Forwarding Architecture section in this document for more information. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. C ontact Protegrity for further guidance on configuration alternatives in the Cloud.
Note
The installation steps below assume that the Log Forwarder is going to be installed in the same AWS account as the corresponding Protect Lambda service. For instructions on how to install Log Forwarder in the AWS account separate than the Protect Lambda, please contact Protegrity.ESA Audit Store Configuration
ESA server is required as the recipient of audit logs. Verify the information below to ensure ESA is accessible and configured properly.
ESA server running and accessible on TCP port 9200 (Audit Store) or 24284 (td-agent).
Audit Store service is configured and running on ESA. Applies when audit logs are output to Audit Store directly or through td-agent. For information related to ESA Audit Store configuration, refer to Audit Store Guide.
(Optional) td-agent is configured for external input. For more information related to td-agent configuration, refer to ESA guide Sending logs to an external security information and event management (SIEM).
Certificates on ESA
Note
This section is optional. If CA certificate is not provided, the Log Forwarder will skip server certificate validation and will connect to ESA without verifying that it is a trusted server.
If you are deploying Log Forwarder with Protegrity Provisioned Cluster (PPC), certificate authorization and CA validation are not supported. Configuration steps related to certificates in this section do not apply to PPC. See Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster): Log Forwarder Setup with PPC for details.
By default, ESA is configured with self-signed certificates, which can optionally be validated using a self-signed CA certificate supplied in the Log Forwarder configuration. If no CA certificate is provided, the Log Forwarder will skip server certificate validation.
Note
Certificate Validation can be bypassed for testing purposes, see section: Install through CloudFormationIf ESA is configured with publicly signed certificates, this section can be skipped since the forwarder Lambda will use the public CA to validate ESA certificates.
To obtain the self-signed CA certificate from ESA:
Download ESA CA certificate from the /etc/ksa/certificates/plug directory of the ESA
After certificate is downloaded, open the PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PtyEsaCaServerCert cloudformation parameter in section Install through CloudFormation
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
AWS VPC Configuration
Log forwarder Lambda function requires network connectivity to ESA, similar to Policy Agent Lambda function. Therefore, it can be hosted in the same VPC as Policy Agent.
Separate VPC can be used, as long as it provides network connectivity to ESA.
Note
AWS Lambda service uses permissions in log forwarder function execution role to create and manage network interfaces. Lambda creates a Hyperplane ENI and reuses it for other VPC-enabled functions in your account that use the same subnet and security group combination. Each Hyperplane ENI can handle thousands of connections/ports as the Lambda function scales up. If more connections are needed AWS Lambda service creates additional Hyperplane ENIs. There’s no additional charge for using a VPC or a Hyperplane ENI. Refer to AWS official Lambda Hyperplane ENIs docs for more information.VPC Name: ___________________
VPC Subnet Configuration
Log Forwarder can be connected to the same subnet as Policy Agent or separate one as long as it provides connectivity to ESA.
Subnet Name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoint Configuration
Log Forwarder Lambda function requires connectivity to Secrets Manager AWS service. If the VPC identified in the steps before has no connectivity to public internet through the NAT Gateway, then the following service endpoint must be configured:
- com.amazonaws.{REGION}.cloudwatch
- com.amazonaws.{REGION}.secretsmanager
- com.amazonaws.{REGION}.kms
Security Group Configuration
Security groups restrict communication between Log Forwarder Lambda function and the ESA appliance. The following rules must be in place for ESA and Log Forwarder Lambda function.
From VPC > Security Groups > Log Forwarder Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG | ESA Communication |
Record the name of Log Forwarder security group name.
Log Forwarder Security Group Id: ___________________
The following port must be open for the ESA. If the ESA is running in the Cloud, then create the following security.
Note
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access the NAT Gateway IP access to ESA via port 9200.ESA Security Group configuration
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG |
Configure ESA Audit Store Credentials
Note
This section is optional. If client certificate authentication is not set up, the Log Forwarder will connect to ESA without authentication credentials.Audit Log Forwarder can optionally authenticate with ESA using certificate-based authentication with a client certificate and certificate key. If used, both the certificate and certificate key will be stored in AWS Secrets Manager.
Download the following certificates from the /etc/ksa/certificates/plug directory of the ESA:
- client.key
- client.pem
After certificates are downloaded, open each PEM file in text editor and replace all new lines with escaped new line: \n. To escape new lines from command line, use one of the commands below depending on your operating system.
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' client.key > private_key.txt
awk 'NF {printf "%s\\n",$0;}' client.pem > public_key.txt
Windows PowerShell:
(Get-Content '.\client.key') -join '\n' | Set-Content 'private_key.pem'
(Get-Content '.\client.pem') -join '\n' | Set-Content 'public_key.pem'
For more information on how to configure client certificate authentication for Audit Store on ESA refer to Audit Store Guide.
To create secret with ESA client certificate/key pair in AWS Secrets Manager.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the private_key and public_key value pair.
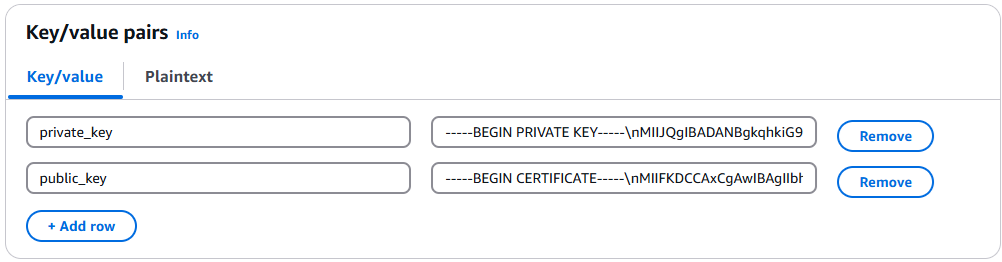
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it below.
ESA Client Certificate/Key Pair Secret Name: ___________________
This value will be used to set PtyEsaClientCertificatesSecretId cloudformation parameter in section Install through CloudFormation
Note
If you are deploying Log Forwarder with PPC, do not configure client certificate authentication. See PPC Appendix: Log Forwarder Certificate Guidance for details.Create Audit Log Forwarder IAM Execution Policy
This task defines a policy used by the Protegrity Log Forwarder Lambda function to write CloudWatch logs, access the KMS encryption key to decrypt the policy and access Secrets Manager for log forwarder user credentials.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "KinesisStreamRead", "Effect": "Allow", "Action": [ "kinesis:GetRecords", "kinesis:GetShardIterator", "kinesis:DescribeStream", "kinesis:DescribeStreamSummary", "kinesis:ListShards", "kinesis:ListStreams" ], "Resource": "*" }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Review policy, type in a policy name, for example, ProtegrityLogForwarderLambdaPolicy and Confirm. Record the policy name:
LogForwarderLambdaPolicyName:__________________
Create Log Forwarder IAM Role
Perform the following steps to create Log Forwarder execution IAM role.
To create Log Forwarder IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Audit Log Forwarder IAM Execution Policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityForwarderRole and click Confirm.
Record the role ARN.
Log Forwarder IAM Execution Role Name: ___________________
Installation Artifacts
Audit Log Forwarder installation artifacts are part of the same deployment package as the one used for protect and policy agent services. Follow the steps below to ensure the right artifacts are available for log forwarder installation.
Verify that the Protegrity deployment package is available on your local system, if not, you can download it from the Protegrity portal.
Note
If you maintain multiple Protegrity Cloud Protectors, make sure that the deployment package downloaded for Audit Log Forwarder is the same as the one used for Protect service installation.Extract the pty_log_forwarder_cf.json cloud formation file from the deployment package.
Check the S3 deployment bucket identified in section Create S3 bucket for Installing Artifacts. Make sure that all Protegrity deployment zip files are uploaded to the S3 bucket.
Install through CloudFormation
The following steps describe the deployment of the Audit Log Forwarder AWS cloud components.
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_log_forwarder_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter | Description | Default Value | Required |
|---|---|---|---|
LogForwarderSubnets | Subnets where the Log Forwarder will be hosted. |
|
|
LogForwarderSecurityGroups | Security Groups, which allow communication between the Log Forwarder and ESA. |
| X |
LambdaExecutionRoleArn | The ARN of Lambda role created in the prior step. |
| X |
ArtifactS3Bucket | Name of S3 bucket created in the pre-configuration step. |
| X |
LogDestinationEsaIp | IP or FQDN of the ESA instance or cluster. |
| X |
AuditLogOutput | Audit log processor to target on ESA. Allowed values: audit-store, td-agent | audit-store | X |
PtyEsaClientCertificatesSecretId | AWS Secrets Manager secret id containing client certificates used for authentication with ESA Audit Store. It is expected that the public key will be stored in a field public_key and the private key in a field named private_key. This parameter is optional. If not provided, Log Forwarder will connect to ESA without client certificate authentication. | ||
EsaTlsDisableCertVerify | Disable certificate verification when connecting to ESA if set to 1. This is only for dev purposes, do not disable in production environment. | 0 | X |
PtyEsaCaServerCert | ESA self-signed CA certificate used by log forwarder Lambda to ensure ESA is the trusted server. Recorded in step Certificates on ESA In case ESA is configured with publicly signed certificates, the PtyEsaCaServerCert configuration will be ignored. |
| |
EsaConnectTimeout | Time in seconds to wait for the ESA response. Minimum value: 1. | 5 | X |
EsaVirtualHost | ESA virtual hostname. This configuration is optional and it can be used when proxy server is present and supports TLS SNI extension. |
|
|
KinesisLogStreamRetentionPeriodHours | The number of hours for the log records to be stored in Kinesis Stream in case log destination server is not available. Minimum value: 24. See Log Forwarder Performance section for more details. | 24 | X |
KinesisLogStreamShardCount | The number of shards that the Kinesis log stream uses. For greater provisioned throughput, increase the number of shards. Minimum value: 1. See Log Forwarder Performance section for more details. | 10 | X |
MinLogLevel | Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all | severe | X |
Click Next with defaults to complete CloudFormation.
After CloudFormation is completed, select the Outputstab in the stack.
Record the following values
KinesisLogStreamArn: ________________________________
Add Kinesis Put Record permission to the Protect Function IAM Role
Login to the AWS account that hosts the Protect Lambda Function.
Search for Protect Lambda Function IAM Execution Role Name created in Create Protect Lambda IAM role.
Under Permissions policies, select Add Permissions > Create inline policy.
In Specify permissions view, switch to JSON.
Copy the policy json from below replacing the placeholder value indicated in the following snippet as <Audit Log Kinesis Stream ARN> with the value recorded in the previous step.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "KinesisPutRecords", "Effect": "Allow", "Action": "kinesis:PutRecords", "Resource": "<Audit Log Kinesis Stream ARN>" } ] }When you are finished, choose Next.
On the Review and create page, type a Name, then choose Create policy.
Test Log Forwarder Installation
Testing in this section validates the connectivity between Log Forwarder and ESA. The sample policy included with the initial installation and test event below are not based on your ESA policy. Any logs forwarded to ESA which are not signed with a policy generated by your ESA will not be added to the audit store.
Install Log Forwarder and configure according to previous sections. Log Forwarder configuration MinLogLevel must be at least info level.
Navigate to the log forwarder lambda function.
Select the Test tab.
Copy the json test event into the Event JSON pane.
{ "Records": [ { "kinesis": { "kinesisSchemaVersion": "1.0", "partitionKey": "041e96d78c778677ce43f50076a8ae3e", "sequenceNumber": "49620336010289430959432297775520367512250709822916263938", "data": "eyJpbmdlc3RfdGltZV91dGMiOiIyMDI2LTAzLTI3VDEzOjIzOjEyLjkwNFoiLCJhZGRpdGlvbmFsX2luZm8iOnsiZGVzY3JpcHRpb24iOiJEYXRhIHVucHJvdGVjdCBvcGVyYXRpb24gd2FzIHN1Y2Nlc3NmdWwuIn0sImNsaWVudCI6e30sImNudCI6NCwiY29ycmVsYXRpb25pZCI6InJzLXF1ZXJ5LWlkOjEyMzQiLCJsZXZlbCI6IlNVQ0NFU1MiLCJsb2d0eXBlIjoiUHJvdGVjdGlvbiIsIm9yaWdpbiI6eyJob3N0bmFtZSI6IlBSTy1VUy1QRjNSSEdGOSIsImlwIjoiMTAuMTAuMTAuMTAiLCJ0aW1lX3V0YyI6MTcxMTU1OTEwMH0sInByb2Nlc3MiOnsiaWQiOjJ9LCJwcm90ZWN0aW9uIjp7ImF1ZGl0X2NvZGUiOjgsImRhdGFlbGVtZW50IjoiYWxwaGEiLCJkYXRhc3RvcmUiOiJTQU1QTEVfUE9MSUNZIiwibWFza19zZXR0aW5nIjoiIiwib2xkX2RhdGFlbGVtZW50IjpudWxsLCJvcGVyYXRpb24iOiJVbnByb3RlY3QiLCJwb2xpY3lfdXNlciI6IlBUWURFViJ9LCJwcm90ZWN0b3IiOnsiY29yZV92ZXJzaW9uIjoiMS4yLjErNTUuZzU5MGZlLkhFQUQiLCJmYW1pbHkiOiJjcCIsInBjY192ZXJzaW9uIjoiMy40LjAuMTQiLCJ2ZW5kb3IiOiJyZWRzaGlmdCIsInZlcnNpb24iOiIwLjAuMS1kZXYifSwic2lnbmF0dXJlIjp7ImNoZWNrc3VtIjoiN0VCMkEzN0FDNzQ5MDM1NjQwMzBBNUUxNENCMTA5QzE0OEJGODYwRjE3NEVCMjMxMTAyMEI3RkE1QTY4MjdGQyIsImtleV9pZCI6ImM0MjQ0MzZhLTExMmYtNGMzZi1iMmRiLTEwYmFhOGI1NjJhNyJ9fQ==", "approximateArrivalTimestamp": 1626878559.213 }, "eventSource": "aws:kinesis", "eventVersion": "1.0", "eventID": "shardId-000000000000:49620336010289430959432297775520367512250709822916261234", "eventName": "aws:kinesis:record", "invokeIdentityArn": "arn:aws:iam::555555555555:role/service-role/TestRole", "awsRegion": "us-east-1", "eventSourceARN": "arn:aws:kinesis:us-east-1:555555555555:stream/CloudProtectEventStream" } ] }Note
The data payload is the base64 encoded audit log. See Audit Logging for detail on audit log contents.Select Test to execute the test event.
Test is successful if the Log Output of test results contains the following log:
[INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed recordsIf the log is not present, please consult the Troubleshooting section for common errors and solutions.
Update Protector With Kinesis Log Stream
In this section, Kinesis log stream ARN will be provided to the Protect Function installation.
Note
If the Protector has not been installed, you may provide the KinesisLogStreamArn during protector installation and skip the remainder of this section.Navigate to the Protector CloudFormation stack created in the protector installation section.
Select Update.
Choose Use existing template > Next.
Set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation.
Proceed with Next and Submit the changes.
Continue to the next section once stack status indicates UPDATE_COMPLETE.
Update Policy Agent With Log Forwarder Function Target
Log Forwarder Lambda function requires a policy layer which is in sync with the Protegrity Protector. This section will describe the steps to update the policy agent to include updating Log Forwarder Lambda function.
Note
If the policy agent has not been installed, follow the steps in Policy Agent Installation. Set AWS_PROTECT_FN_NAME to include both protector and log forwarder lambda functions.Navigate to the Policy Agent Function created in Policy Agent Installation
Select Configuration > Environment variables > Edit
Edit the value for environment variable AWS_PROTECT_FN_NAME to include the log forwarder function name/arn in the comma separated list of Lambda functions.
Save the changes and continue when update completes
Navigate to Test tab
Add an event {} and select Test to run the Policy Agent function
Verify Log forwarder function was updated to use the policy layer by inspecting the log output. Logs should include the following:
[INFO] 2024-07-09 18:58:04,793.793Z 622d374b-1f73-4123-9a38-abc61973adef iap_agent.policy_deployer:Updating lambda [Protegrity_LogForwarder_<stack ID>] to use layer version [arn:aws:lambda:<aws region>:<aws account number>:layer:Protegrity_Layer_<layer name>:<layer version>]
Test Full Log Forwarder Installation
Install and configure Protegrity Agent, Protector, and Log Forwarder components.
Send a protect operation to the protector using a data element or user which will result in audit log generation
Navigate to the CloudWatch log group for the Protect function
Select the log stream for the test operation and scroll to the latest logs
Expect to see a log similar to the below:
[2024-07-09T19:28:23.158] [INFO] [kinesis-external-sink.cpp:51] Sending 2 logs to Kinesis ... [2024-07-09T19:28:23.218] [INFO] [aws-utils.cpp:206] Kinesis send time: 0.060sNavigate to the CloudWatch log group for the Log Forwarder function
Expect to see a new log stream - it may take several minutes for the stream to start
Select the new stream and scroll to the most recent logs in the stream
Expect to see a log similar to the below:
[2024-07-09T19:32:31.648] [INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed records
Troubleshooting
Error | Action |
|---|---|
Log forwarder log contains severe level secrets permissions error: |
|
When testing log forwarder as described in Test Log Forwarder Installation, response contains policy decryption error: |
|
Cloudformation stack creation fails with error: |
|
Severe level kinesis permissions log message in protector function: |
|
TLS errors reported in log forwarder function logs: |
|
2.3.6 -
Configuring Regular Expression to Extract Policy Username
Cloud Protect Lambda Function exposes USERNAME_REGEX configuration to allow extraction of policy username from user in the request.
USERNAME_REGEX Lambda Environment configuration
The USERNAME_REGEX configuration can be used to extract policy username from user in the request. The following are allowed values for USERNAME_REGEX:
1 - Default build-in regular expression is used:
^arn:aws:(?:iam|sts)::[0-9]{12}:(?:role|user|group|assumed\-role|federated\-user)\/([\w\/+=,.\-]{1,1024}|[\w\/+=,.\-@]{1,1024})(?:@[a-zA-Z0-9\-]{1,320}(?:\.\w+)+)?$^User regex$ - Custom regex with one capturing group. This group is used to extract the username. Examples below show different regular expression values and the resulting policy user.
USERNAME_REGEX | User in the request | Effective Policy User |
|---|---|---|
Not Set | arn:aws:iam::123456789012:user/juliet.snow | arn:aws:iam::123456789012:user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | arn:aws:sts::123456789012:assumed-role/TestSaml | |
1 | arn:aws:iam::123456789012:user/juliet.snow | juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | TestSaml | |
| arn:aws:iam::123456789012:user/juliet.snow | user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | assumed-role/TestSaml |
2.3.7 -
Create Protect Lambda IAM Execution Policy
This task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy.
Perform the following steps to create the Lambda execution role and required policies.
To create protect lambda IAM execution policy:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Next, type in a policy name, for example, ProtegrityProtectLambdaPolicy and Create Policy. Record the policy name:
ProtectLambdaPolicyName:__________________
2.3.8 -
Granting access to use the Cloud Protect UDF
The ability to use the Cloud Protect UDF from Athena is controlled through IAM permissions. The Athena user/role must have the InvokeFunction permission to the Cloud Protect Lambda function as shown in the following example:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "ProtectLambdaFunction",
"Effect": "Allow",
"Action": "lambda:InvokeFunction",
"Resource": "<PROTECT_FUNCTION_ARN>"
}
]
}
The policy above would be used in addition to any other IAM policies required to use Amazon Athena. Refer to the AWS Athena example policy for a typical IAM policy.
2.3.9 -
Policy User
Policy user for protect and unprotect operations can be provided from either Lambda environment variable or federated identity.
POLICY_USER Environment Variable in the Athena Protect Lambda
The Lambda environment variable POLICY_USER, may be set with a default user in the security policy or as a service user.
Federated Identity
When the request contains the federated identity, the policy user maybe the IAM ARN of the user running the SQL query. For example:
User | arn:aws:iam::123456789012:user/juliet.snow |
Role | arn:aws:sts::123456789012:assumed-role/TestSaml |
Note
The Federated Identity is not always provided to the Protect Lambda. AWS is working on adding the Federated Identity to more cases. As a result, the expect user may change after Athena workgroup updates.Note
See Configuring Regular Expression to Extract Policy Username to learn how to extract username from IAM ARNTo control which Policy User is used, Athena Protect Lambda has the Environment Variable: POLICY_USER_CONFIG.
Value | description |
|---|---|
0 | (Default) The Federated Identity is used when provided by Amazon Athena, if the Federated Identity is not provided, the user defaults to the POLICY_USER. |
1 | The Federated Identity will only be used. If The Federated Identity is not provided the Athena Protect Lambda will fail the query. |
2 | The POLICY_USER will always be used, regardless if the Federated Identity is provided or not. POLICY_USER is required. If it is empty or missing the Protect Lambda will fail the query. NoteThe USERNAME_REGEX Lambda configuration described in Configuring Regular Expression to Extract Policy Username will not have effect when the POLICY_USER=2. |
2.3.10 -
Prerequisites
| Requirement | Detail |
|---|---|
| Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
| Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
| AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
| Athena Engine Version 3 | Only Athena engine version 3 is supported. The product may work in Athena engine version 2, but it is deprecated and all users are encouraged to upgrade. |
2.3.11 -
AWS Service Dependencies
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials. |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
2.3.12 -
Required Skills and Abilities
Role / Skillset | Description |
|---|---|
AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
2.4 - Understanding Athena Objects
Understanding Athena Objects
The following sections describe key concepts in understanding Protegrity Serverless with Athena.
2.4.1 -
User Defined Functions
User Defined Functions (UDF) in Amazon Athena allow users to invoke protect and unprotect operations on data using Athena SQL.
To use a UDF in Athena, you must declare the USING EXTERNAL FUNCTION clause before the SELECT statement in a SQL query. For example, the following query would perform an unprotect on first_name and last_name fields using the deName element policy:
USING EXTERNAL FUNCTION unprotect(val varchar, el varchar) RETURNS varchar LAMBDA '<replace_with_athena_protect_function_name>:Production'
SELECT unprotect(first_name, 'deName'), unprotect(last_name, 'deName')
FROM customers;
Parent topic:Understanding Athena Objects
2.5 - Performance
Performance
Performance Considerations
The following factors may cause variation in real performance versus benchmarks:
- Cold startup: The Lambda spends additional time on the initial invocation to decrypt and load the policy into memory. This time can vary between 400 ms and 1200 ms depending on the policy size. Once the Lambda is initialized, subsequent “warm executions” should process quickly.
- Size of policy: The size of the policy impacts cold start performance. Larger policies take more time to initialize.
- Lambda memory: AWS provides more virtual cores based on the memory configuration. The initial configuration of 1728 MB provides a good tradeoff between performance and cost with the benchmarked policy. Memory can be increased to optimize for your individual cases.
- Number of security operations (protect or unprotect).
- Lambda concurrency and burst quotas: AWS limits the number of concurrent executions and how quickly lambda can scale to meet demand. This is discussed in an upcoming section of the document.
- Size of data element: Operations on larger text consume time.
Sample Benchmarks
The following benchmarks were performed against CSV files from an S3 bucket.
Benchmark (rows x columns):
| Operations | 1M * 6 cols | 10M * 6 cols | 100M * 6 cols |
|---|---|---|---|
| Athena Protector (Athena v3 Engine) | 8.5s | 17.9s | 2m 12s |
Note
- Peak throughput about 4M ops/sec
Note
** Time excludes baseline time for Athena query startupEstimated AWS costs:
| Type/#Ops | 5B ops/mo. | 50B ops/mo. | 500B ops/mo. | 1T ops/mo. |
|---|---|---|---|---|
| Athena Protector | $8 | $80 | $800 | $1,600 |
Performance Tuning
- Lambda Tuning
AWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region. - Concurrency Troubleshooting
Hitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a client query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your API Gateway or Lambda services in the region. - Cold-Start Performance
Cold-start vs warm execution refers to the state of the Lambda when a request is received. A cold-start undergoes additional initialization, such as, loading the security policy. Warm execution applies to all subsequent requests served by the Lambda.
Lambda Tuning
AWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region.

The concurrent executionsquota cap is the maximum number of lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket.
The burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. Once the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a 429 Too Many Requests response. Athena will generally retry until all requests succeed but may abort if a high percentage of failed responses occur.
The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended selecting a Athena AWS region with the highest burst limits.
Concurrency Troubleshooting
Exceeding your quota limits may indicate quota adjustments are required. Exceeding quota limits may cause a query to fail or reduce performance. Worst case, significant throttling can impact the performance of all your Lambda functions in the region.
Athena is tolerant of a certain ratio of failed requests and automatically retries. If a high percentage of requests fail, the query may abort.
CloudWatch Metrics can be observed on Lambda to reveal if quotas are being reached. CloudWatch logs can be used to access the actual error code.
Cold-Start Performance
Cold-start vs warm execution refers to the state of the Lambda function when a request is received. A cold-start undergoes additional initialization such as loading the security policy. Warm execution applies to all subsequent requests served by the Lambda. The following table shows an example how these states impact latency and performance:
| Execution state | Avg. Execution Duration |
|---|---|
| Cold execution | 438 ms |
| Warm execution | < 2ms |
Note
- Cold execution time will vary based on the physical size of the security policy. A large security policy will result in longer cold startup times.
Log Forwarder Performance
Log forwarder architecture is optimized to minimize the amount of connections and reduce the overall network bandwidth required to send audit logs to ESA. This is achieved with batching and aggregation taking place on two levels. The first level is in protect function instances, where audit logs from consecutive requests to an instance are batched and aggregated. The second level of batching takes place in Amazon Kinesis Stream where log records from different protect function instances are additionally batched and sent to log forwarder function where they are aggregated. This section shows how to configure the deployment to accommodate different patterns of anticipated audit log stream. It also shows how to monitor deployment resources to detect problems before audit records are lost.
Protector Cloud Formation Parameters
AuditLogFlushInterval: Determines the minimum amount of time required for the audit log to be sent to Amazon Kinesis. Changing flush interval may affect the level of aggregation, which in turn may result in different number of connections and different data rates to Amazon Kinesis. Default value is 30 seconds.
Increasing the flush interval may result in higher aggregation of audit logs, in fewer connections to Amazon Kinesis, in higher latency of audit logs arriving to ESA and in higher data throughput.
Lowering the flush interval may result in lower aggregation of audit logs, in more connections to Amazon Kinesis, in lower latency of audit logs arriving to ESA and in lower data throughput.
It is not recommended to reduce the flush interval from default value in production environment as it may overload the Amazon Kinesis service. However, it may be beneficial to reduce flush interval during testing to make audit records appear on ESA faster.
Log Forwarder Cloud Formation Parameters
Amazon KinesisLogStreamShardCount: The number of shards represents the level of parallel streams in the Amazon Kinesis and it is proportional to the throughput capacity of the stream. If the number of shards is too low and the volume of audit logs is too high, Amazon Kinesis service may be overloaded and some audit records sent from protect function may be lost.
Default value is 10, however you are advised to test with a production-like load to determine whether this is sufficient or not.
Amazon KinesisLogStreamRetentionPeriodHours: The time for the audit records to be retained in Amazon Kinesis log stream in cases where log forwarder function is unable to read records from the Kinesis stream or send records to ESA, for example due to a connectivity outage. Amazon Kinesis will retain failed audit records and retry periodically until connectivity with ESA is restored or retention period expires.
Default value is 24 hours, however you are advised to review this value to align it with your Recovery Time Objective and Recovery Point Objective SLAs.
Monitoring Log Forwarder Resources
Amazon Kinesis Stream Metrics: Any positive value in Amazon Kinesis PutRecords throttled records metric indicates that audit logs rate from protect function is too high. The recommended action is to increase the Amazon KinesisLogStreamShardCount or optionally increase the AuditLogFlushInterval.
Log Forwarder Function CloudWatch Logs: If log forwarder function is unable to send logs to ESA, it will log the following message:
[SEVERE] Dropped records: x.Note
When the error message above occurs, the dropped audit records will be preserved in the Amazon Kinesis data stream and retried again according to Amazon Kinesis retry schedule. Records will be retried until Amazon KinesisLogStreamRetentionPeriodHours expires.Protect Function CloudWatch Logs: If protect function is unable to send logs to Amazon Kinesis, it will log the following message:
[SEVERE] Amazon Kinesis error, retrying in x ms (retry: y/z) ..."Any dropped audit log records will be reported with the following log message:
[SEVERE] Failed to send x/y audit logs to Amazon Kinesis.
2.6 - Audit Logging
Audit Logging
Audit records and application logs stream to Amazon CloudWatch Logs or optionally be sent to ESA. Cloud Protect uses a JSON format for audit records that is described in the following sections.
You can analyze and alert on audit records using Protegrity ESA or Amazon CloudWatch. Third-party solutions may be used if they are supported by Amazon Cloudwatch or AWS Lambda logging extensions. For more information about forwarding your audit records to ESA, contact Protegrity. For more information about Amazon CloudWatch, refer to the Amazon CloudWatch User Guide.
For more information about audit records, refer to the Protegrity Analytics Guide.
Audit record fields
The audit record format has been altered in version 3.1 of the protector to provide more information.
| Field | Description |
|---|---|
| additional_info.deployment_id | The deployment_id contains the name of the Protect Function. It is automatically set based on the cloud-specific environment variables assigned to the Protect Function. This allows identifying the Cloud Protect deployment responsible for generating audit log. |
| additional_info.cluster | (Optional) Redshift cluster ARN |
| additional_info.description | A human-readable message describing the operation |
| additional_info.query_id | (Optional) Identifies the query that triggered the operation |
| additional_info.request_id | (Optional) AWS Lambda request identifier |
| cnt | Number of operations, may be aggregated |
| correlationid | (Deprecated) Use additional_info instead |
| level | Log severity, one of: SUCCESS, WARNING, ERROR, EXCEPTION |
| logtype | Always “Protection” |
| origin.ip | The private IP address of the compute resource that operates the Protect Function and is responsible for generating the log entry.NoteThe IP address is private, meaning it is used for internal network communication and is not accessible directly from the public internet.When Log Forwarding is enabled the IP address may be aggregated into minimal CIDR blocks. |
| origin.hostname | Hostname of the system that generated the log entry |
| origin.time_utc | UTC timestamp when the log entry was generated |
| protection.audit_code | Audit code of the protect operation; see the log return codes table in the Protegrity Troubleshooting Guide |
| protection.dataelement | Data element used for the policy operation |
| protection.datastore | Name of the data store corresponding to the deployed policy |
| protection.mask_setting | (Optional) Mask setting from policy management |
| protection.operation | Operation type, one of: Protect, Unprotect, Reprotect |
| protection.policy_user | User that performed the operation |
| protector.core_version | Internal core component version |
| protector.family | Always “cp” for Cloud Protect |
| protector.lambda_version | Protector Lambda application version. |
| protector.pcc_version | Internal pcc component version |
| protector.vendor | Identifies the cloud vendor and the database vendor |
| protector.version | Protector version number |
| signature.checksum | Hash value of the signature key ID used to sign the log message when the log is generated |
| signature.key_id | Key used to sign the log message when the log is generated |
Example Audit Records
The following are sample audit messages:
Protect Success:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "Data protect operation was successful.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "SUCESS",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 6,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "B324AF7C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
User permission denied:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The user does not have the appropriate permissions to perform the requested operation.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 3,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "A216797C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
Data element not found:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The data element could not be found in the policy.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 2,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "AF09217C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
2.7 - No Access Behavior
No Access Behavior
The security policy maintains a No Access Operation, configured in an ESA, which determines the response for unauthorized unprotect requests.
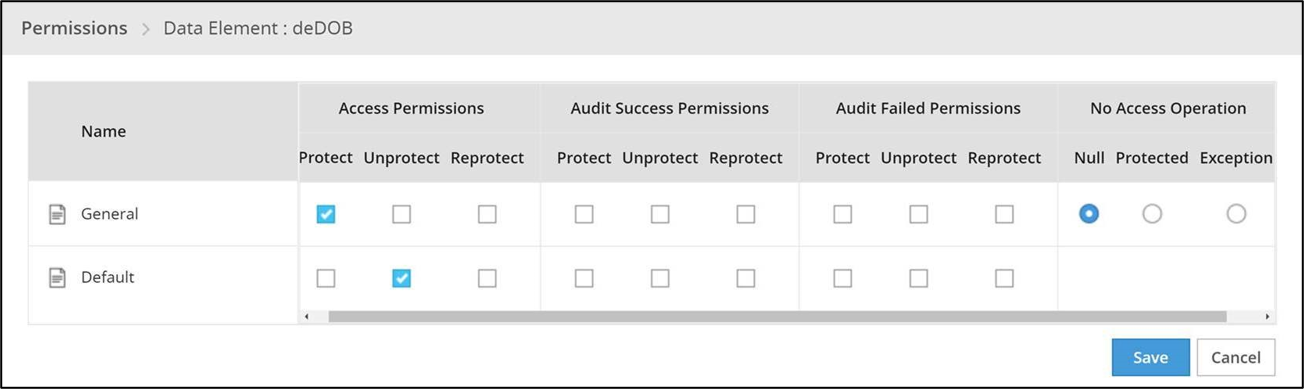
The following table describes the result returned in the response for the various no access unprotect permissions.
| No Access Operation | Data Returned |
|---|---|
| Null | null |
| Protected | (protected value) |
| Exception | Query will fail with an exception |
Note
An unauthorized protect will throw an exception.2.8 - Known Limitations
- FPE is supported only for ASCII values.
- Only the protect and unprotect operations are supported. The reprotect operation is not currently supported.
- Binary data types not supported.
2.9 - Upgrading To The Latest Version
Download the Latest Version
You can download the latest version of the deployment package from https://my.protegrity.com. Navigate to Data Protection > Cloud Protect to download the latest version.
After downloading the deployment package from the Protegrity Portal, unzip the package to extract the artifact files. In the AWS Console, navigate to the S3 bucket that was previously created to upload deployment artifacts (see: Create S3 bucket for Installing Artifacts).
Note
Only extract the deployment package and not the files in it.Upload the following artifacts to the S3 bucket:
- -- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-athena-protect-udfs-<version>.jar
- protegrity-external-extension-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-sample-policy-<version>.zip
If the release version matches your existing deployment, you don’t need to upload it again. Save the following artifacts on your local system so that you have them available during the next steps:
- -- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_api_cf.json
- pty_agent_cf.json
- pty_log_forwarder_cf.json
- pty_athena_protect_cf.json
- pty_agent_cf.json
Perform the following steps to upgrade the Agent Lambda and Protect Lambda separately.
Important
If new versions are available for both Agent and Protect Lambdas, Agent Lambda must be upgraded first.Disable Protegrity Agent Function CloudWatch Event Rule
Cloud Watch Event Rule is used to periodically run Protegrity Agent Function to synchronize policy from ESA. This functionality is optional when deploying Protegrity Serverless Solution. If the Event Rule is enabled, it must be disabled temporarily for the time of the upgrade process.
Follow the steps below to determine if your deployment uses Event Rule and disable it.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Resources tab from the top portion of the screen.
Check if there is a resource with ScheduledRule LogicalID. If there is no such resource you can skip to Upgrading Policy Agent Lambda section. If the scheduled rule is there, continue with the next steps in this section.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Disable from the top-right portion of the screen. This will disable the rule. You will re-enable it after the upgrade process is complete.
Upgrading Policy Agent Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Agent Lambda upgrade.Go to AWS Lambda console and select existing Protegrity Agent Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish. The version of Agent Lambda you just created will serve as restore point in the case you needed to rollback the upgrade.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonGo to AWS Cloud Formation and select existing Protegrity Agent deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_agent_cf.json file and select Next.
Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Navigate back to Agent Lambda Function.
Note
Make sure you are viewing the latest Lambda Function, not the published version.Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current agent installation version is lower than 3.0.12, make sure you set the following function configuration variables:
- PTY_ADDIPADDRESSHEADER
- PTY_ESA_CA_SERVER_CERT You can read more about these variables in section Policy Agent Lambda Configuration.
If you are upgrading from versions prior to v3.0, backup and remove existing policy from the bucket defined by AWS_POLICY_S3_BUCKET property, so that the policy can be re-downloaded and re-encrypted with new ‘key commitment’ feature.
If you are upgrading from version prior to 1.6.1 please follow the steps below, otherwise the upgrade process is completed.
From AWS Console, navigate to IAM > Policies
Search for the Agent Lambda IAM Policy created in Create Agent Lambda IAM policy
Click on the policy, then select Edit Policy. Select JSON tab.
Add the following statement to the list of policy statements.
{ "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }Click Review Policy, then Save Changes. Wait for the changes to save.
Upgrading Log Forwarder Lambda
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], skip this section and follow instruction to install new Log Forwarder Audit Log Forwarder Installation.Publish Log Forwarder Lambda Version
Publishing a version of the Log Forwarder Lambda allows to roll-back to pre-existing version if upgrade fails
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Log Forwarder Lambda version number for roll-backs: ___________________
Disable Kinesis Trigger
Disabling Kinesis trigger ensures there are no unprocessed or re-processed events while function is upgraded.
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Uncheck Activate trigger and click Save
- Wait for function to stop processing events by monitoring function in Monitor tab
Upgrade Forwarder Lambda Version
Upgrade Log Forwarder function with new code
- Go to AWS Cloud Formation and select existing Protegrity Log Forwarder deployment stack.
- Select Update Stack > Make a direct update.
- Select Replace existing template > Upload a template file.
- Upload pty_log_forwarder_cf file and select Next.
- Click Next until Review window and then select Update stack.
- Wait for the Cloud Formation to complete.
Enable Kinesis Trigger
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Check Activate trigger and click Save Log Forwarder function will now start processing events from where it left off when Kinesis trigger was disabled.
Monitor and roll-back
Monitor Log Forwarder function for errors in its CloudWatch logs and in Montior tab. To roll back function to the previous version if any errors occur follow these steps:
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Select Configuration tab > Triggers
Expand Details section of Kinesis trigger and record UUID value
Execute the following AWS CLI command to move Kinesis trigger to previous version of Log Forwarder Lambda that was created earlier and recorded as Log Forwarder Lambda version number for roll-backs. Substitute kinesis-mapping-uuid, log-forwarder-function-name, version-for-roll-backs with your values:
aws lambda update-event-source-mapping --uuid <kinesis-mapping-uuid> --function-name <log-forwarder-function-name>:<version-for-roll-backs>Find Kinesis trigger attached to previous version of Log Forwarder Lambda by navigating Versions tab > Version number link in the Versions column Kinesis trigger is now moved to previous version of Log Forwarder Lambda function.
Upgrading Protect Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Diagram below illustrates upgrade steps.
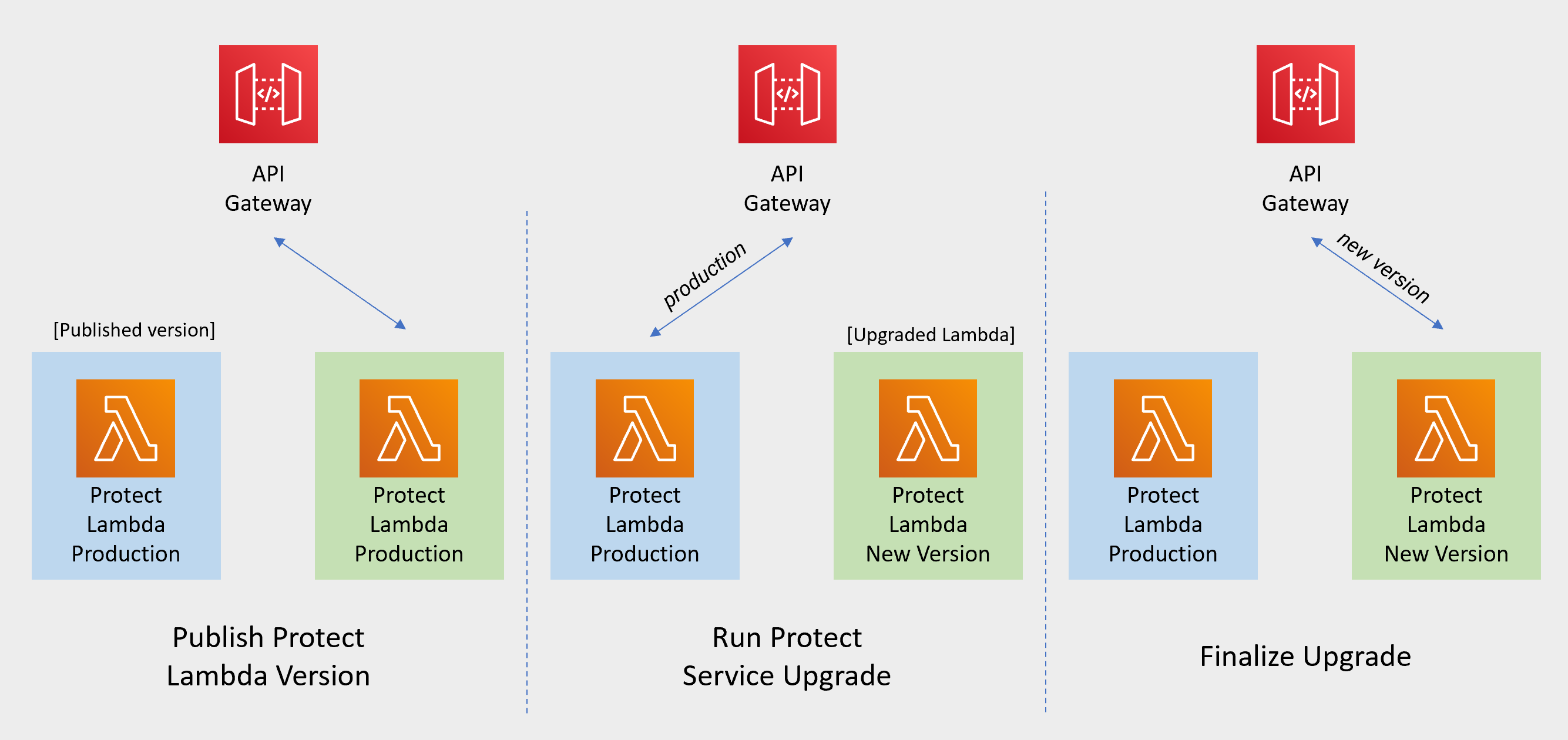
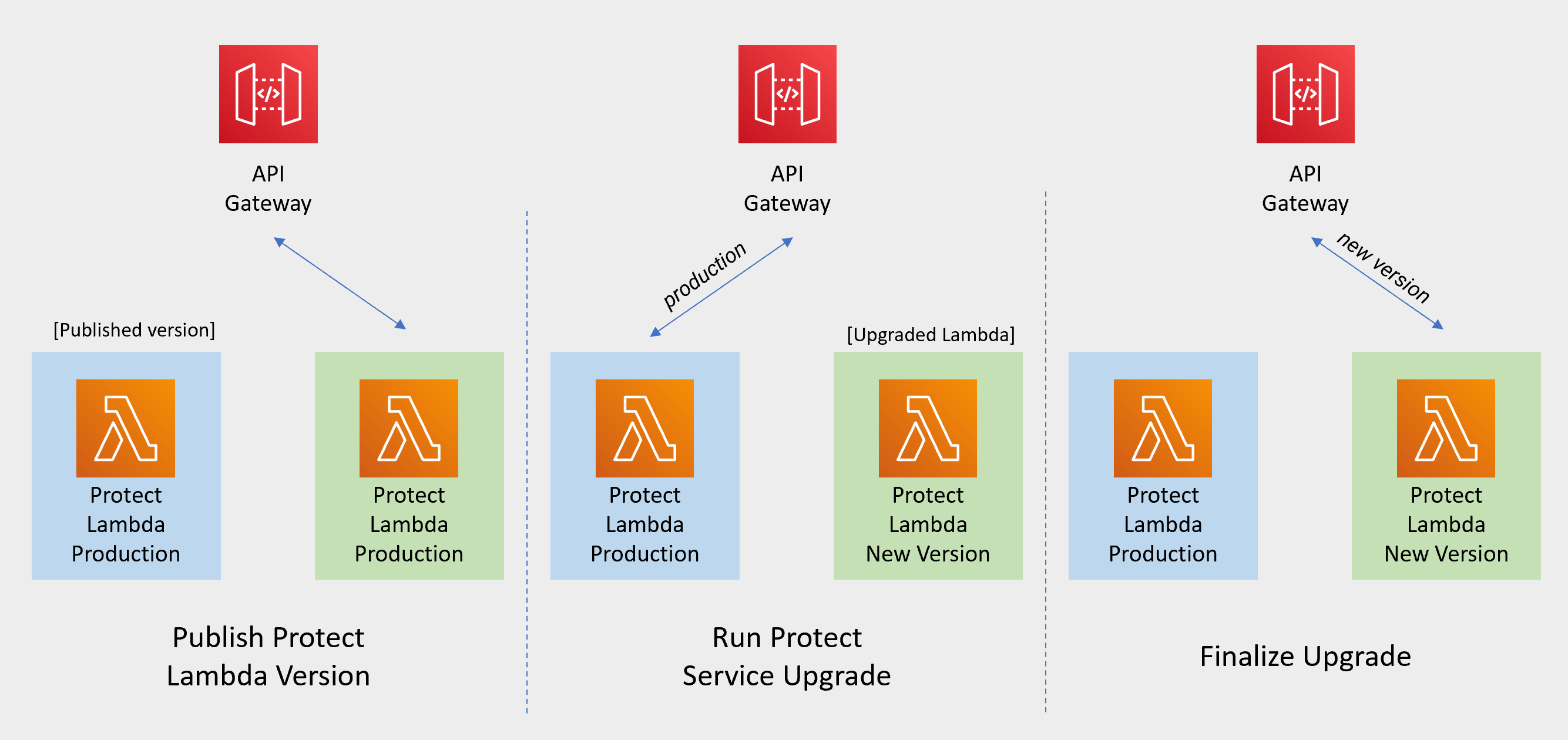
Publish Protect Lambda Version
Publishing a version of the Protect Lambda allows updating it without interruptions to the existing traffic.
Go to AWS Lambda console and select existing Protegrity Protect Lambda.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonClick Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Protect Lambda version number: ___________________
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:<protect_lambda_version_number>' iam_role 'arn:aws:iam::123456789212:role/example_role';
Run protect service upgrade
In this step, the Protect service including Lambda $LATEST version will be updated using Cloud Formation template. The Lambda version created in previous step will be used to serve existing traffic during the upgrade process.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_protect_cf.json file and select Next.
Update ProtectFunctionProductionVersion parameter with Protect Lambda version number recorded in step 3.
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation for the newly deployed log forwarder.Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Go back to Lambda console and select Protect Lambda.
Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current protect installation version is lower than 3.0.14, you can optionally set the following variable:
- LOG_REDSHIFT_CLUSTER_ARN You can read more about this configuration in section Protect Lambda Configuration.
Navigate to Aliases tab. Verify that Production alias points to the lambda version you specified in the cloud formation template.
The upgraded Protect Lambda is configured with a sample policy. Run Agent Lambda Function before continuing with next steps.
Finalize upgrade
In this step, the Protect Lambda will be configured to serve traffic using $LATEST version upgraded in the previous step.
Go back to Protegrity AWS Cloud Formation deployment stack.
Select Update. Check Use Current template.
Update ProtectFunctionProductionVersion parameter with the following value: $LATEST.
Click Next until Review window and then select Update stack.
Go back to Lambda console and select Protect Lambda.
From the Lambda console, verify that Latest alias points to $LATEST version.
Test your function to make sure it works as expected.
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:Production' iam_role 'arn:aws:iam::123456789212:role/example_role';If you need to rollback to older version of Protect Lambda, you can re-run the cloud formation with ProtectFunctionProductionVersion parameter set to the previous version of Protect Lambda.
Re-enable Protegrity Agent Function CloudWatch Event Rule
If the Event Rule was disabled at the beginning of the upgrade process, you must re-enabled it. Follow the steps below to re-enable Policy Agent Event rule.
Go to the Protegrity Agent Cloud Formation Stack.
Select Resources tab from the top portion of the screen.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Enable from the top-right portion of the screen. This will enable the rule. You will re-enable it after the upgrade process is complete.
2.10 - Appendices
2.10.1 - Sample Athena External Functions
Sample Athena External Functions
Method: Tokenization | ||
Type: ALPHA | ||
| ||
Athena Data Types | Athena Max Size | Protegrity Max Size |
VARCHAR | 65K (65,535 bytes) | 4K (4,096 bytes) |
| ||
| ||
| ||
External Function Sample Definitions: | ||
| ||
| ||
| ||
Method: Tokenization | ||
Type: NUMERIC | ||
| ||
Athena Data Types | Athena Max Size | Protegrity Max Size |
DECIMAL | 4K (4,096 bytes) | 4K (4,096 bytes) |
INTEGER | ||
BIGINT | ||
DOUBLE | ||
| ||
External Function Sample Definitions: | ||
| ||
| ||
Method: Tokenization | ||
Type: Date YYYY-MM-DD | ||
| ||
Athena Data Types | Athena Max Size | Protegrity Max Size |
DATE (any supported format) | 10 bytes | 10 bytes |
| ||
External Function Sample Definitions: | ||
| ||
| ||
| ||
Method: Tokenization | ||
Type: DATETIME YYYY-MM-DD HH:mm:ss | ||
| ||
Athena Data Types | Athena Max Size | Protegrity Max Size |
TIMESTAMP | 29 bytes | 29 bytes |
External Function Sample Definitions: | ||
| ||
| ||
Method: Encryption | ||
Type: AES | ||
| ||
Athena Data Types | Athena Max Size | Protegrity Max Size |
VARBINARY |
|
|
| ||
External Function Sample Definitions: | ||
| ||
| ||
2.10.2 - Installing the Policy Agent and Protector in Different AWS Accounts
The Policy Agent Lambda function and Protect Lambda functions can be installed in separate AWS accounts. However, additional configuration is required to authorize the Policy Agent to provision the security policy to a remote Protect Lambda function.
Note
The Policy Agent will deploy an encrypted security policy file to an S3 bucket in the Protect function’s AWS Account.Create Agent Lambda IAM policy
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace the wildcards (*) with the region, account, and resource name information where required.
Select Review policy, type in the policy name, and confirm. Record policy name:
Agent Lambda Cross Account Policy Name: ___________________
Create Policy Agent cross-account IAM Role
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Roles > Create Role
Select AWS Service > Lambda . Proceed to Permissions.
Select Policy created in the step above. Proceed to Tags.
Specify Tag, proceed to the final screen. Type in policy name and confirm. Record the name.
Policy Agent Cross Account IAM Role Name: ___________________
Allow the Policy Agent Cross-Account Role to be Assumed by the Policy Agent IAM Role
Login to the AWS account that hosts the Protect Lambda function.
Navigate to the previously created IAM Role (Agent Lambda Cross-Account IAM Role Name).
Navigate to Trust Relationships > Edit Trust Relationships.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda IAM Execution Role ARN> with ARN of Agent Lambda IAM Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Click Update Trust Policy.
Add Assume Role to the Policy Agent Execution IAM Role
Login to the AWS account that hosts the Policy Agent.
Navigate to the Agent Lambda IAM Execution Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Add Inline Policy.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda Cross-Account IAM ARN> with the value recorded in Create Policy Agent cross-account IAM Role.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "sts:AssumeRole" ], "Resource": "<Agent Lambda Cross-Account IAM ARN>." } ] }When you are finished, choose Review Policy.
On the Review policy page, type a Name, then choose Create Policy.
Update the Policy Agent Lambda Configuration
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select Configuration tab | Environment variables.
Select Edit and add the following environment variables with the value from Agent Lambda Cross-Account IAM ARN:
Parameter Value AWS_ASSUME_ROLE Agent Lambda Cross-Account IAM ARN Ensure the values in the Parameters AWS_POLICY_S3_BUCKET, AWS_PROTECT_FN_NAME and AWS_POLICY_LAYER_NAME are all in the Protect Lambda Function AWS Account.
In case custom VPC hostname configuration is used, you will need to set the ENDPOINT_URL. Refer to Policy Agent - Custom VPC Endpoint Hostname Configuration.
AWS_VPC_ENDPOINT_URL
<AWS_VPC_ENDPOINT>
Click Save and Run the Lambda. The Lambda will now assume the Role in Protect Lambda Function AWS Account and update the policy cross accounts.
2.10.3 - Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
This guide describes how to configure the Protegrity Policy Agent and Log Forwarder to connect to a Protegrity Provisioned Cluster (PPC), highlighting the differences from connecting to ESA.
Key Differences: PPC vs ESA
| Feature | ESA 10.2 | PPC (this guide) |
|---|---|---|
| Datastore Key Fingerprint | Optional/Recommended | Required |
| CA Certificate on Agent | Optional/Recommended | Optional/Recommended |
| CA Certificate on Log Forwarder | Optional/Recommended | Not supported |
| Client Certificate Authentication from Log Forwarder | Optional/Recommended | Not supported |
| IP Address | ESA IP address | PPC address |
Prerequisites
- Access to PPC and required credentials.
- Tools:
curl,kubectlinstalled.
Policy Agent Setup with PPC
Important
When connecting to PPC, the Policy Agent requires thePTY_DATASTORE_KEY fingerprint. For ESA 10.2, the fingerprint is optional but recommended. See Policy Agent Installation for general setup steps.Follow these instructions as a guide for understanding specific inputs for Policy Agent integrating with PPC:
Obtain the Datastore Key Fingerprint
To retrieve the fingerprint for your Policy Agent:
curl -k -H "Authorization: Bearer ${TOKEN}" -X POST https://${HOST}/pty/v2/pim/datastores/1/export/keys -H "Content-Type: application/json" --data '{ "algorithm": "RSA-OAEP-256", "description": "example-key-from-kms", "pem": "-----BEGIN PUBLIC KEY-----\nABC123... ...890XYZ\n-----END PUBLIC KEY-----" }'Sample Output:
{"uid":"1","algorithm":"RSA-OAEP-256","fingerprint":"4c:46:d8:05:35:2e:eb:39:4d:39:8e:6f:28:c3:ab:d3:bc:9e:7a:cb:95:cb:b1:8e:b5:90:21:0f:d3:2c:0b:27","description":"example-key-from-kms"}Record the
fingerprintvalue and configure it as thePTY_DATASTORE_KEYfor the Policy Agent.Retrieve the PPC CA Certificate
To obtain the CA certificate from PPC:
kubectl -n api-gateway get secret ingress-certificate-secret -o jsonpath='{.data.ca\.crt}' | base64 -d > CA.pemUse the
CA.pemthat was returned as described in Policy Agent Installation.Configure the PPC Address
Use the PPC address in place of the ESA IP address wherever required in your configuration.
Log Forwarder Setup with PPC
Note
When using PPC, certificate authentication and CA validation are not supported for the Log Forwarder. Configuration steps related to certificates in Log Forwarder Installation do not apply to PPC. If you attempt to use certificates provided by PPC, the Log Forwarder will not function correctly.- The Log Forwarder will proceed without certificates and will print a warning if
PtyEsaCaServerCertandPtyEsaClientCertificatesSecretIdare not provided. - No additional certificate or CA configuration is needed for PPC.
Troubleshooting
Protector Lambda fails with “AWS KMS Decrypt failed”
Symptom:
After a successful Policy Agent run and layer update, the Protector Lambda returns:
{
"body": "{\"error_msg\":\"Failed to open decoder: rpdecode decrypt failure: dek callback failed: AWS KMS Decrypt failed: \",\"success\":false}",
"isBase64Encoded": false,
"statusCode": 400
}
The Protector Lambda logs show:
[SEVERE] [utils.cpp:185] AWS KMS Decrypt failed:
Cause:
The public key configured in the PPC/ESA datastore does not match the KMS key pair used by the Policy Agent. The policy package is encrypted with the public key stored in the datastore. If that key does not correspond to the KMS key pair whose private key is used for decryption, the Protector Lambda will fail to decrypt the policy.
Resolution:
- Identify the KMS key pair used by the Policy Agent (the key ARN configured during pre-configuration).
- Export the public key from that KMS key pair.
- In PPC/ESA, ensure the datastore’s export key is configured with the public key from that same KMS key pair. See Obtain the Datastore Key Fingerprint above.
- Re-run the Policy Agent to generate a new policy package encrypted with the correct key.
- Test the Protector Lambda again.
Important
Always verify that the public key registered in the PPC/ESA datastore belongs to the same KMS key pair referenced by the Policy Agent. A mismatch between these keys is a common cause of AWS KMS Decrypt failed errors.
The KMS key must be an asymmetric key with the Encrypt and decrypt key usage type. Symmetric keys or asymmetric keys configured for signing will not work.
Additional Notes
- For troubleshooting, consult the Protegrity Documentation.
2.10.4 - Security Recommendations
The following section provides recommendations on configuring Amazon Athena for querying PII Data protected by Protegrity Athena Protector.
Security is a shared responsibility between AWS and you. When using PII Data in Amazon Athena, it is essential to understand the best practices and keep your Data always protected. In this section, we summarize the configuration needed when using Amazon Athena.
Note
The recommendations are noninclusive, and there are additional references within this article to more detailed information and guidelines.To read more on Amazon Shared responsibility on Amazon Athena, visit Amazon Athena Security - Amazon Athena
Logging and Monitoring
Enable AWS CloudTrail to audit all calls made to Athena API.
For more information, visit Logging Amazon Athena API Calls with AWS CloudTrail - Amazon Athena .
Encryption at rest
AWS S3 buckets
Amazon Athena lets you run queries on encrypted data stored in Amazon S3 repositories in the same region. Make sure you enable Amazon S3 encryption options supported by Amazon Athena.
For more information, visit Creating Tables Based on Encrypted Datasets in Amazon S3 - Amazon Athena .
Query Results and Query History
Amazon Athena saves the query history in an S3 bucket. If you unprotect data using Amazon Athena Protector, Amazon Athena saves the results (the unprotected data) in an S3 bucket. The query history is viewable by anyone with IAM permissions on the bucket. To remediate, we suggest the following configurations.
Setting Amazon Athena Workgroup
You should set up the Amazon Athena Workgroup S3 staging directory and overwrite Client-side settings. It ensures all users comply with the S3 staging directory and encryption setting for the results. Restrict the IAM access to the bucket to the minimum required for Amazon Athena to work.
Amazon S3 lifecycle policy
Amazon Athena’s defaults configuration is to store the results for 45 days, and we suggest reducing it to the minimum (1 day) using the Amazon S3 lifecycle policy.
For more infromation, visit Working with Query Results, Output Files, and Query History - Amazon Athena
Encrypt Glue Catalog
Amazon Athena has integration with AWS Glue Data Catalog. If you use it, you can enable encryption in the AWS Glue Data Catalog. It doesn’t encrypt the data, only the Athena table definition. It provides another layer of security on where your data exists and what it includes.
For more information, visit Encrypting Your Data Catalog. Access from Athena to Encrypted Metadata in the AWS Glue Data Catalog - Amazon Athena.
Encryption in transit
To allow only encrypted connections with HTTPS (TLS), you can apply the aws:SecureTransport condition on S3 buckets IAM policies.
Access Control
Resources
Make sure you provide the least privilege access control to Amazon Athena workgroup, S3 buckets, Protegrity Protect Lambda function, AWS KMS (If used for data encryption at rest).
For more information, visit Identity and Access Management in Athena - Amazon Athena .
Granting access to use the Cloud Protect UDF
The ability to use the Cloud Protect UDF from Athena is controlled through IAM permissions. The Athena user/role must have the InvokeFunction permission to the Cloud Protect Lambda function as shown in the following example:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "ProtectLambdaFunction",
"Effect": "Allow",
"Action": "lambda:InvokeFunction",
"Resource": "<PROTECT_FUNCTION_ARN>"
}
]
}
The policy above would be used in addition to any other IAM policies required to use Amazon Athena. Refer to the AWS Athena example policy for a typical IAM policy.
Separate Workgroups
Create separate Workgroups based on the privacy controls. It provides more control on who can see the Query History and access unprotected data stored there.
For more information, visit Using Workgroups to Control Query Access and Costs - Amazon Athena .
AWS Lake Formation
Amazon Athena can benefit from AWS Lake Formation table and column access policies. It is another layer of security before Protegrity Protect Function and reduces unauthorized requests.
For more information, visit Using Athena to Query Data Registered With AWS Lake Formation - Amazon Athena .
2.10.5 - Policy Agent - Custom VPC Endpoint Hostname Configuration
The Policy Agent uses default endpoint hostnames to communicate with other AWS services (for example, secretsmanager.amazonaws.com). This configuration will only work in VPCs where Amazon-provided DNS is available (default VPC configuration with private DNS option enabled for the endpoint). If your VPC uses custom DNS, follow the instructions below to configure the Policy Agent Lambda to use custom endpoint hostnames.
Note
This configuration is only available with the Cloud Protect version 1.5.0 or higher. For more information about the upgrade instructions, refer to Upgrading to the Latest Version.Identify DNS Hostnames
To identify DNS hostnames:
From AWS console, select VPC > Endpoints.
Select Secrets Manager endpoint from the list of endpoints.
Under Details > DNS Names, note the private endpoint DNS names adding https:// at the beginning of the endpoint name.
For example, https://vpce-1234-4pzomrye.kms.us-west-1.vpce.amazonaws.com
Note down DNS names for the KMS and Lambda endpoints:
AWS_SECRETSMANAGER_ENDPOINT: https://_________________
AWS_KMS_ENDPOINT: https://_________________
AWS_LAMBDA_ENDPOINT: https://_________________
Update the Policy Agent Lambda configuration
To update policy agent lambda configuration:
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select the Configuration section and choose Environment variables.
Select Edit and add the following environment variables with the corresponding endpoint URLs recorded in steps 3-4:
Parameters Value AWS_SECRETSMANAGER_ENDPOINT_URL <AWS_SECRETS_ENDPOINT> AWS_KMS_ENDPOINT_URL <AWS KMS ENDPOINT> AWS_LAMBDA_ENDPOINT_URL <AWS LAMBDA ENDPOINT> Click Save and Run the Lambda. The Lambda will now use endpoints you have just configured.
2.10.6 - Protection Methods
Protection Methods
For more information about the protection methods supported by Protegrity, refer to the Protection Methods Reference.
Tokenization Type | Supported Input Data Types | Notes |
|---|---|---|
Numeric Credit Card Alpha Upper-case Alpha Alpha-Numeric Upper Alpha-Numeric Lower ASCII Printable Decimal Unicode Unicode Base64 Unicode Gen2 | STRING NULL | |
Integer | NUMBER NULL | |
Date Datetime | STRING NULL | For information about supported formats, refer to the Protection Methods Reference. |
Binary | STRING NULL | Must be |
Protection Method | Supported Input Data Types | Notes |
|---|---|---|
No Encryption | STRING NUMBER NULL |
Encryption Algorithm | Supported Input Data Types | Notes |
|---|---|---|
3DES AES-128 AES-256 CUSP 3DES CUSP AES-128 CUSP AES-256 | STRING | Must be |
2.10.7 - Configuring Regular Expression to Extract Policy Username
Configuring Regular Expression to Extract Policy Username
Cloud Protect Lambda Function exposes USERNAME_REGEX configuration to allow extraction of policy username from user in the request.
USERNAME_REGEX Lambda Environment configuration
The USERNAME_REGEX configuration can be used to extract policy username from user in the request. The following are allowed values for USERNAME_REGEX:
1 - Default build-in regular expression is used:
^arn:aws:(?:iam|sts)::[0-9]{12}:(?:role|user|group|assumed\-role|federated\-user)\/([\w\/+=,.\-]{1,1024}|[\w\/+=,.\-@]{1,1024})(?:@[a-zA-Z0-9\-]{1,320}(?:\.\w+)+)?$^User regex$ - Custom regex with one capturing group. This group is used to extract the username. Examples below show different regular expression values and the resulting policy user.
USERNAME_REGEX | User in the request | Effective Policy User |
|---|---|---|
Not Set | arn:aws:iam::123456789012:user/juliet.snow | arn:aws:iam::123456789012:user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | arn:aws:sts::123456789012:assumed-role/TestSaml | |
1 | arn:aws:iam::123456789012:user/juliet.snow | juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | TestSaml | |
| arn:aws:iam::123456789012:user/juliet.snow | user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | assumed-role/TestSaml |
2.10.8 - Associating ESA Data Store With Cloud Protect Agent
Associating ESA Data Store With Cloud Protect Agent
ESA controls which policy is deployed to protector using concept of data store. A data store may contain a list of IP addresses identifying servers allowed to pull the policy associated with that specific data store. Data store may also be defined as default data store, which allows any server to pull the policy, provided it does not belong to any other data stores. Node registration occurs when the policy server (in this case the policy agent) makes a policy request to ESA, where the agent’s IP address is identified by ESA.
Note
For more information about ESA data store refer to Policy Management Guide which is part of Protegrity ESA documentation.Policy agent lambda source IP address used for node registration on ESA depends on ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP and the PTY_ADDIPADDRESSHEADER configuration exposed by the agent lambda.
The Lambda service uses multiple network interfaces, internal network interface with ephemeral IP range of 169.254.x.x and external network interface with IP range of the VPC subnet the Lambda is associated with. By default, when agent lambda is contacting ESA to register node for policy download, ESA uses agent Lambda VPC IP address. This default behavior is caused by the default ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP=false and agent default configuration PTY_ADDIPADDRESSHEADER=yes.
In some cases, when there is a proxy server between the ESA and agent lambda, the desirable ESA configuration is ASSIGN_DATASTORE_USING_NODE_IP=true. and PTY_ADDIPADDRESSHEADER=no which will cause the ESA to use proxy server IP address.
The table below shows how the hubcontroller and agent settings will affect node IP registration on ESA.
| Agent source IP | Agent VPC subnet IP | Proxy IP | ESA config - ASSIGN_DATASTORE_USING_NODE_IP | Agent lambda config - PTY_ADDIPADDRESSHEADER | Agent node registration IP |
|---|---|---|---|---|---|
| 169.254.144.81 | 10.1.2.173 | No Proxy | true | yes | 169.254.144.81 |
| true | no | 10.1.2.173 | |||
| false | yes | ||||
| false | no | ||||
| 169.254.144.81 | 10.1.2.173 | 34.230.42.110 | true | yes | 169.254.144.81 |
| true | no | 34.230.42.110 | |||
| false | yes | ||||
| false | no |
3 - Redshift
This section describes the high-level architecture of the product on AWS for integration with Amazon Redshift, the installation procedures, and provides guidance on performance. This section focuses on Protegrity-specific aspects and should be consumed with corresponding Redshift documentation.
This guide may also be used with the Protegrity Enterprise Security Administrator Guide, which explains the mechanism for managing the data security policy.
3.1 - Overview
Solution Overview
Amazon Redshift Protector is a cloud native, serverless product for fine-grained data protection with Redshift™, a managed Cloud data warehouse. This enables invocation of the Protegrity data protection cryptographic methods from the Redshift SQL execution context. The benefits of serverless include rapid auto-scaling, performance, low administrative overhead, and reduced infrastructure costs compared to a server-based solution.
This product provides data protection services invoked by External User Defined Functions (UDFs) within Amazon Redshift. The UDFs act as a client transmitting micro-batches of data to the serverless Protegrity Lambda function. User queries may generate hundreds or thousands of parallel requests to perform security operations. Protegrity’s serverless function is designed to scale and yield reliable query performance under such load.
Amazon Redshift Protector utilizes a data security policy maintained by an Enterprise Security Administrator (ESA), similar to other Protegrity products. Using regular SQL database queries or tools, such as, Tableau™, authorized users can perform de-identification (protect) and re-identification (unprotect) operations on data within the managed Cloud data warehouse. A user’s individual capabilities are subject to privileges and policies defined by the Enterprise Security Administrator.
The following data ingestion patterns are available with your managed Cloud data warehouse:
- Data protection at source applications: In this case, sensitive data is already de-identified (protected) across the enterprise wherever it resides, including the managed data warehouse. Protected data can be ingested directly into your managed Cloud data warehouse. Depending on usage patterns, this ensures that your managed data warehouse is not brought into scope for PCI, PII, GDPR, HIPPA, and other compliance policies.
- Data protection using the Extract-Transform-Load (ETL) pattern: In this case, sensitive data may be transformed with a Protegrity protector either on-premise or in the Cloud before it is ingested into Redshift.
- Data protection using the Extract-Load-Transform (ELT) pattern: In this case, sensitive data is protected after it lands into the target system typically through a temporary landing table. It uses the native data warehouse’s compute engine with Protegrity to protect incoming data at very high throughput rates. After the data is protected, the intermediate loading tables are dropped as part of the ingestion workflow.
Analytics on Protected Data
Protegrity’s format and length preserving tokenization scheme make it possible to perform analytics directly on protected data. Tokens are join-preserving so protected data can be joined across datasets. Often statistical analytics and machine learning training can be performed without the need to re-identify protected data. However, a user or service account with authorized security policy privileges may re-identify subsets of data using the Redshift Protector on AWS service.
Features
Amazon Redshift Protector incorporates Protegrity’s patent-pending vaultless tokenization capabilities into cloud-native serverless technology. Combined with an ESA security policy, Protegrity provides the following features:
- Fine grained field-level protection in the managed Cloud data warehouse
- Role-based access control (RBAC) to protect and unprotect (re-identify) data depending on the user privileges
- Policy enforcement features of other Protegrity application protectors.
For more information about the available protection options, such as, data types, Tokenization or Encryption types, or length preserving and non-preserving tokens, refer to Protection Methods Reference.
3.2 - Architecture
Protector Deployment Architecture
The Protegrity product should be deployed in the customer’s Cloud account within the same AWS region as the Redshift cluster. The product incorporates Protegrity’s vaultless tokenization engine within an AWS Lambda Function. The encrypted data security policy from an ESA is deployed periodically as a static resource through an AWS Lambda Layer. The policy is decrypted in memory at runtime within the Lambda. This architecture allows Protegrity to be highly available and scale very quickly without direct dependency on any other Protegrity services.
The product exposes a remote data protection service invoked from external User Defined Functions (UDFs), a native feature of specific Cloud databases. The UDFs can be invoked through direct SQL queries or database views. The external UDF makes parallel calls to the serverless Protegrity Lambda function to perform protect and unprotect data operations. Each network REST request includes a micro-batch of data to process and a secure context header generated by the database with the username and a Protegrity context header with the data element type, and operation to perform. The product applies the ESA security policy including user authorization and returns a corresponding response.
The security policy is synchronized through another serverless component called the Protegrity Policy Agent. The agent operates on a configurable schedule, fetches the policy from the ESA, performs additional envelope encryption using Amazon KMS, and deploys the policy into the Lambda Layer used by the serverless product. This solution can be configured to automatically provision the static policy or the final step can be performed on-demand by an administrator. The policy takes effect immediately for all new requests. There is no downtime for users during this process.
The following diagram shows the high-level architecture described above.
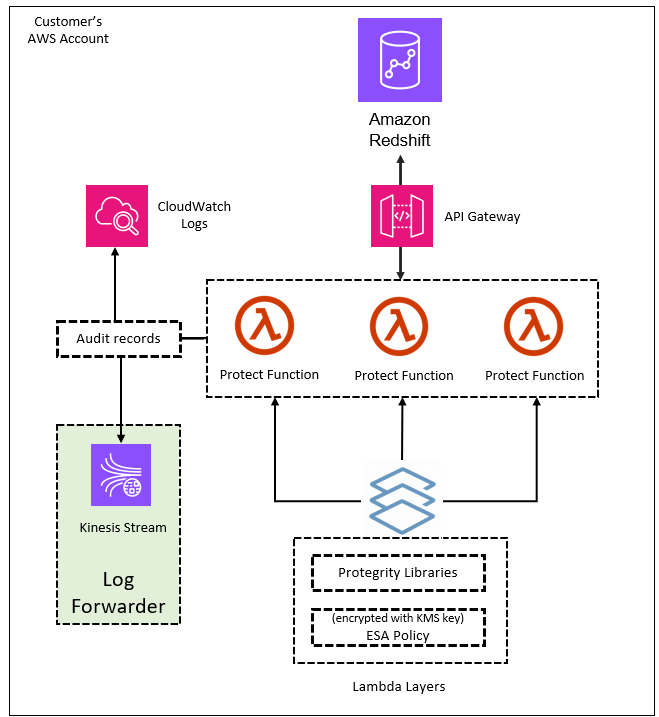
The following diagram shows a reference architecture for synchronizing the security policy from ESA.
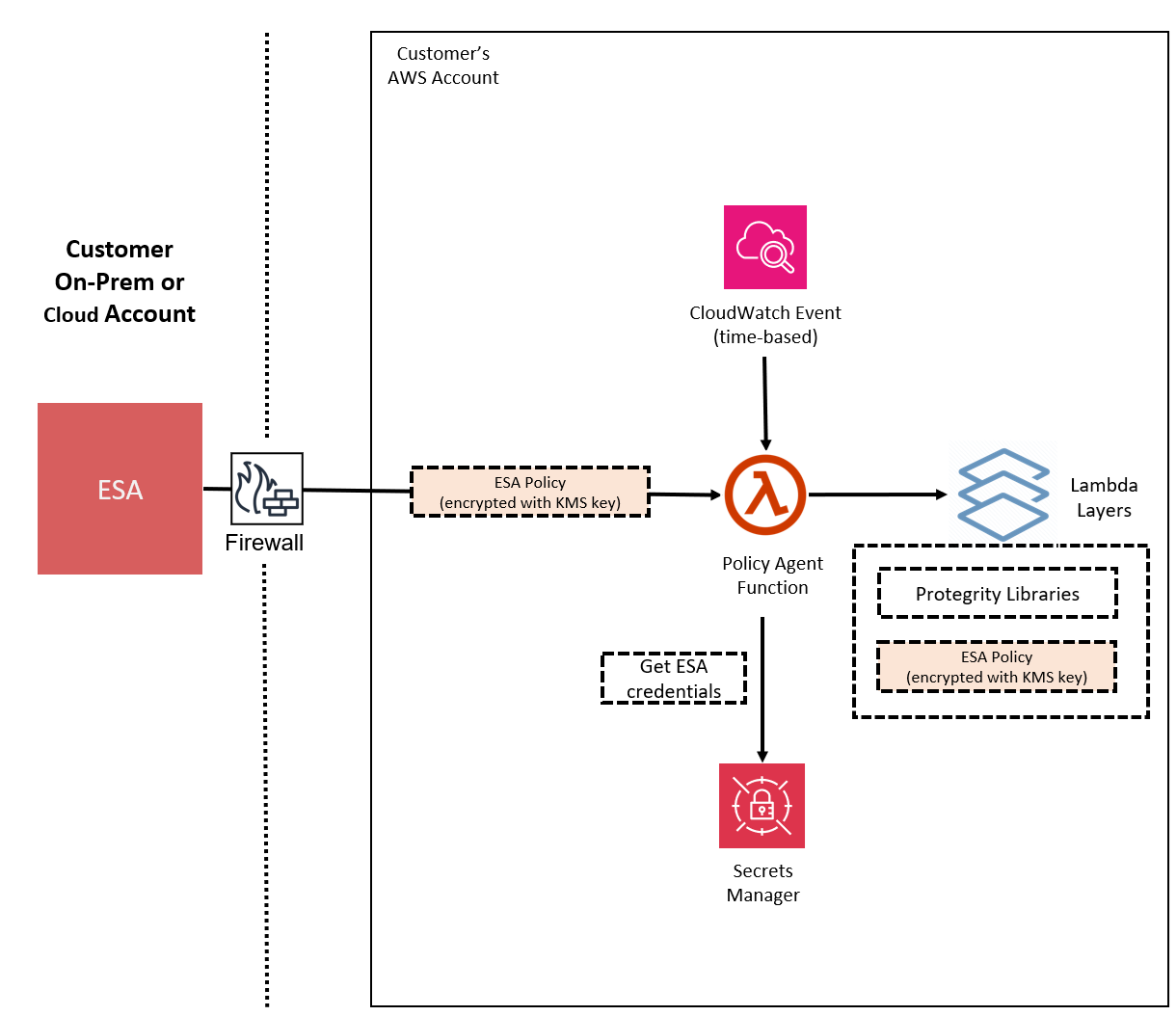
The Protegrity Policy Agent requires network access to an Enterprise Security Administrator (ESA). Most organizations install the ESA on-premise. Therefore, it is recommended that the Policy Agent is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
The ESA is a soft appliance that must be pre-installed on a separate server. It is used to create and manage security policies.
For more information about installing the ESA, and creating and managing policies, refer the Policy Management Guide.
Log Forwarding Architecture
Audit logs are by default sent to CloudWatch as long as the function’s execution role has the necessary permissions. The Protegrity Product can also be configured to send audit logs to ESA. Such configuration requires deploying Log Forwarder component which is available as part of Protegrity Product deployment bundle. The diagram below shows additional resources deployed with Log Forwarder component.
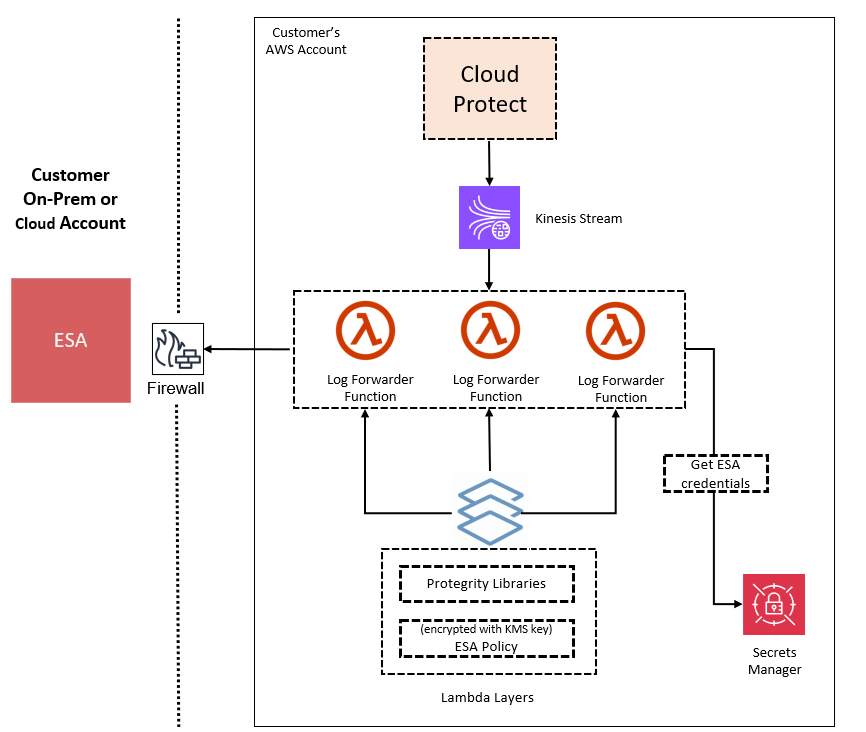
The log forwarder component includes Amazon Kinesis data stream and the forwarder Lambda function. Amazon Kinesis stream is used to batch audit records before sending them to forwarder function, where similar audit logs are aggregated before sending to ESA. Aggregation rules are described in the Protegrity Log Forwarding guide. When the protector function is configured to send audit logs to log forwarder, audit logs are aggregated on the protector function before sending to Amazon Kinesis. Due to specifics of the Lambda runtime lifecycle, audit logs may take up to 15 minutes before being sent to Amazon Kinesis. Protector function exposes configuration to minimize this time which is described in the protector function installation section.
The security of audit logs is ensured by using HTTPS connection on each link of the communication between protector function and ESA. Integrity and authenticity of audit logs is additionally checked on log forwarder which verifies individual logs signature. The signature verification is done upon arrival from Amazon Kinesis before applying aggregation. If signature cannot be verified, the log is forwarded as is to ESA where additional signature verification can be configured. Log forwarder function uses client certificate to authenticate calls to ESA.
To learn more about individual audit log entry structure and purpose of audit logs, refer to Audit Logging section in this document. Installation instructions can be found in Audit Log Forwarder installation.
The audit log forwarding requires network access from the cloud to the ESA. Most organizations install the ESA on-premise. Therefore, it is recommended that the Log Forwarder Function is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
Redshift Connectivity
The AWS Redshift system is a cloud data warehouse Platform-as-a-Service (PaaS) from AWS. Unlike traditional (on-prem or customer-managed) data warehouses and RDBMS systems, Redshift is a fully managed, multi-tenant PaaS service, where the customers do not have the ability to install 3rd party software within the Redshift infrastructure.
Currently, the Redshift architecture does not allow installing Protegrity data protection UDFs and policy enforcement point (PEP) agents inside the Redshift infrastructure. Therefore, a remote-coupling integration mechanism where Redshift invokes RESTful APIs exposed by the Protegrity product is used.
Redshift supports remote invocations to the Protegrity infrastructure through External Functions, which in turn calls AWS Lambda.
Access and authorization between various AWS services involved in this architecture is achieved through Identity Access Management (IAM). For instance, Redshift is given an IAM role to call Lambda, Lambda is given an IAM role to call Secrets Manager, etc. Various IAM role configuration settings are shown in the appendices of this document.
The following figure illustrates the Protegrity Redshift Integration architecture.
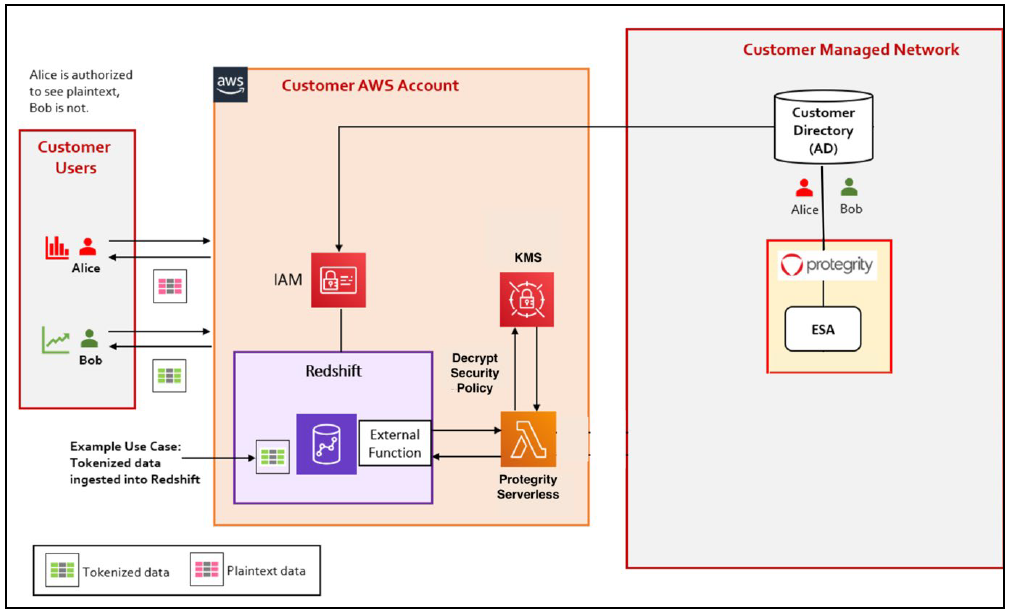
3.2.1 -
Redshift Connectivity
The AWS Redshift system is a cloud data warehouse Platform-as-a-Service (PaaS) from AWS. Unlike traditional (on-prem or customer-managed) data warehouses and RDBMS systems, Redshift is a fully managed, multi-tenant PaaS service, where the customers do not have the ability to install 3rd party software within the Redshift infrastructure.
Currently, the Redshift architecture does not allow installing Protegrity data protection UDFs and policy enforcement point (PEP) agents inside the Redshift infrastructure. Therefore, a remote-coupling integration mechanism where Redshift invokes RESTful APIs exposed by the Protegrity product is used.
Redshift supports remote invocations to the Protegrity infrastructure through External Functions, which in turn calls AWS Lambda.
Access and authorization between various AWS services involved in this architecture is achieved through Identity Access Management (IAM). For instance, Redshift is given an IAM role to call Lambda, Lambda is given an IAM role to call Secrets Manager, etc. Various IAM role configuration settings are shown in the appendices of this document.
The following figure illustrates the Protegrity Redshift Integration architecture.
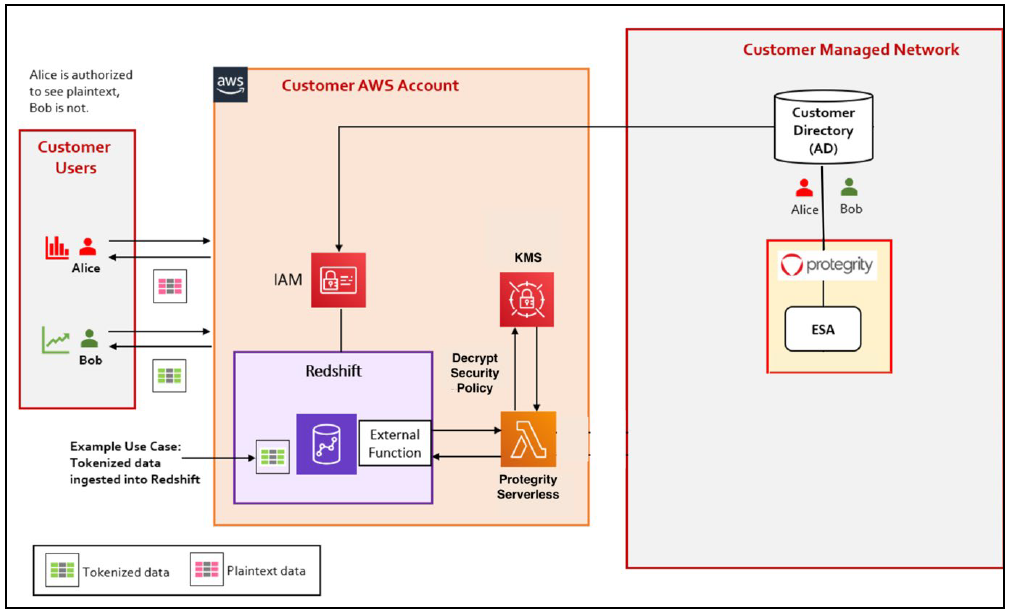
3.3 - Installation
3.3.1 - Prerequisites
AWS Services
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials. |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
ESA Version Requirements
The Protector and Log Forwarder functions require a security policy from a compatible ESA version.
The table below shows compatibility between different Protector and ESA versions.
Note
For the latest up-to-date information refer to: Protegrity Compatibility Matrix| Protector Version | ESA Version | |||
|---|---|---|---|---|
| 8.x | 9.0 | 9.1 & 9.2 | 10.0 | |
| 2.x | No | Yes | * | No |
| 3.0.x & 3.1.x | No | No | Yes | No |
| 3.2.x | No | No | Yes | * |
| 4.0.x | No | No | No | Yes |
Legend | |
|---|---|
Yes | Protector was designed to work with this ESA version |
No | Protector will not work with this ESA version |
* | Backward compatible policy download supported:
|
Prerequisites
| Requirements | Description |
|---|---|
| Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
| Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
| AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
| Redshift cluster (Enterprise Edition) | Must be in the same region as Protegrity Protect Lambda |
Required Skills and Abilities
| Requirements | Description |
|---|---|
| AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
| Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
| Redshift Administrator | Account Admin access required to setup access |
| Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
What’s Next
3.3.2 - Pre-Configuration
Provide AWS sub-account
Identify or create an AWS account where the Protegrity solution will be installed. It is recommended that a new AWS sub-account be created. This can provide greater security controls and help avoid conflicts with other applications that might impact regional account limits. An individual with the Cloud Administrator role will be required for some subsequent installation steps.
AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
Determine AWS Region
Determine the AWS region where the Amazon Redshift cluster is running. This is the region in where the Protegrity solution must be installed.
AWS Region (AccountRegion): ___________________
Create S3 bucket for Installing Artifacts
This S3 bucket will be used for the artifacts required by the CloudFormation installation steps. This S3 bucket must be created in the region that is defined in Provide AWS sub-account
Sign in to the AWS Management Console and open the Amazon S3 console.
Change region to the one determined in Provide AWS sub-account
Click Create Bucket.
Enter a unique bucket name:
For example, protegrity-install.us-west-2.example.com
Upload the installation artifacts to this bucket. Protegrity will provide the following three artifacts:
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
Important
The deployment package you receive from Protegrity must be extracted to reveal the Protegrity artifacts. CloudFormation requires them in the provided .zip format. Do not extract the individual Protegrity artifacts. Upload these artifacts to the S3 bucket created.
S3 Bucket name (ArtifactS3Bucket): ___________________
Create KMS Key
The Amazon Key Management Service (KMS) provides the ability for the Protegrity Serverless solution to encrypt and decrypt the Protegrity Security Policy.
Note
It is recommended to host the KMS key in a separate AWS sub-account. This allows dual control, separating the responsibility between the key administrator and the Protegrity Serverless account administrator.To create KMS key:
In the AWS sub-account where the KMS key will reside, select the region.
Navigate to Key Management Service > Create Key.
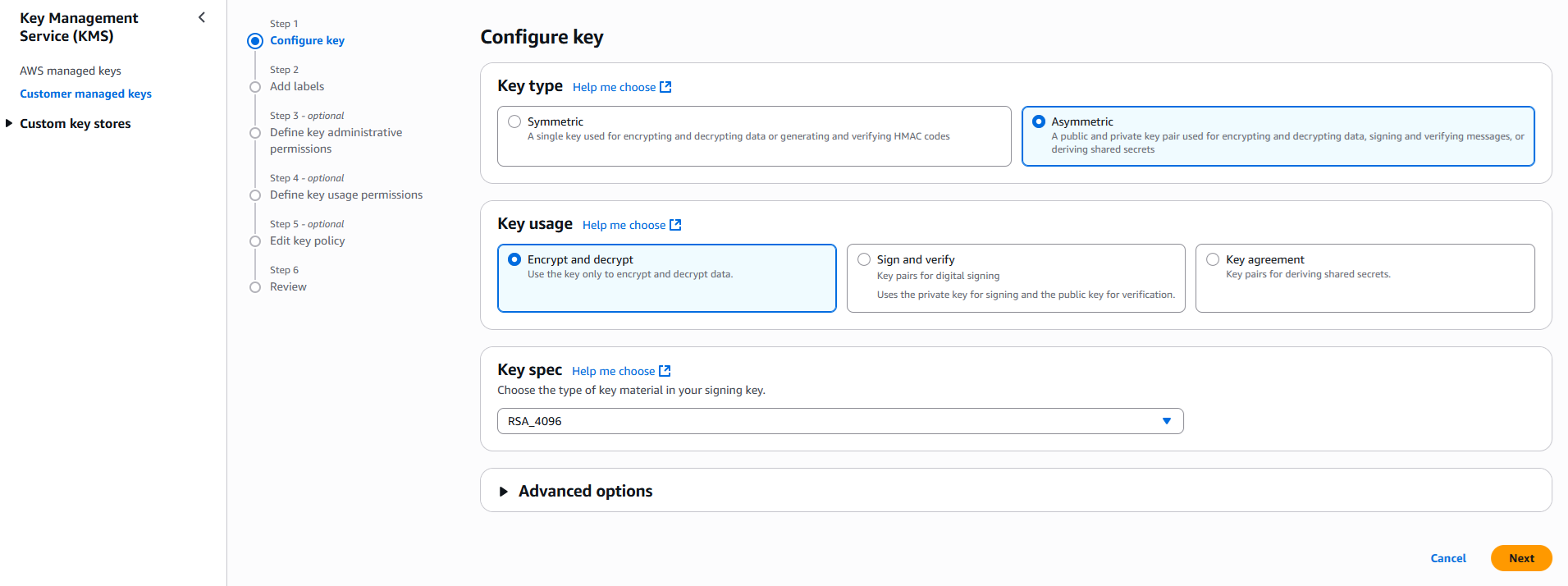
Configure the key settings:
- Key type: Asymmetric
- Key usage: Encrypt and decrypt
- Key spec: RSA_4096
- Click Next
Create alias and optional description, such as, Protegrity-Serverless and click Next.
Define key administrative permissions, the IAM user who will administrate the key.
Note
It is recommended the administrator be different than the administrator of the Protegrity Serverless accountClick Next.
Define the key usage permissions.
In Other AWS accounts, enter the AWS account id used for the Protegrity Serverless installation.
Continue on to create the key. If there is a concern this permission is overly broad, then you can return later to restrict access to the role of two Protegrity Serverless Lambda as principals. Click to open the key in the list and record the ARN.
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
Download the public key from the KMS key. Navigate to the key in KMS console, select the Public key tab, and click Download. Save the PEM file. This public key will be added to the ESA data store as an export key. Refer to Exporting Keys to Datastore for instructions on adding the public key to the data store.
Note
This step is not applicable for ESA versions lower than 10.2.KMS Public Key PEM file: ___________________
Create IAM Account Role
An IAM role is used to authorize Redshift to access the future Protect Lambda resource.
To create IAM account role:
From the AWS console, access IAM, select Roles and then Create Role.
In Trusted entity type section, select AWS service
In Use case section, for Service or use case, select Redshift.
For Use case, select Redshift – Customizable.
Click Next to advance to Add Permissions step.
Click Next to skip Add Permissions step.
Enter a Role name, for example, RedshiftProtegrity.
Click Create role.
After the role is created, click on the role. Record the following information:
- Role Name (DBRoleName): ____________________
- Role ARN (DBRoleARN): ____________________
What’s Next
3.3.3 - Protect Service Installation
Preparation
Ensure that all the steps in Pre-Configuration are performed.
Login to the AWS account console where Amazon Redshift Protector will be installed.
Ensure that the required CloudFormation templates provided by Protegrity are available on your local computer.
Create Protect Lambda IAM Execution Policy
This task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Next, type in a policy name, for example, ProtegrityProtectLambdaPolicy and Create Policy. Record the policy name:
ProtectLambdaPolicyName:__________________
Create Protect Lambda IAM Role
The following steps create the role to utilize the policy defined in Create Protect Lambda IAM Execution Policy.
To create protect lambda IAM execution role:
From the AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
In the list, search and select the policy created in Create Protect Lambda IAM Execution Policy.
Click Next
Type the role name, for example, ProtegrityProtectRole
Click Create role
Record the role ARN.
Role ARN (LambdaExecutionRoleArn): ___________________
Install through CloudFormation
The following steps describe the deployment of the Lambda function.
To install through CloudFormation:
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_protect_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter
Description
DBRoleName
Name of the account role created in the pre-configuration step
ArtifactS3Bucket
Name of S3 bucket created in the pre-configuration step
LambdaExecutionRoleArn
The ARN of Lambda role created in the prior step
MinLogLevel
Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all
UsernameRegex
If set, the effective policy user will be extracted from the user in the request.
Note
See Configuring Regular Expression to Extract Policy Username to learn how to extract username from the requestIf you are not planning to deploy log forwarder you can skip this step. The log forwarder parameters can be provided later after log forwarder is deployed.
Log Forwarder Parameters Description KinesisLogStreamArn The ARN of the AWS Kinesis stream where audit logs will be sent for aggregation AuditLogFlushInterval Time interval in seconds used to accumulate audit logs before sending to Kinesis. Default value: 30. See Log Forwarder Performance section for more details. Proceed to the last step of the Create Stack wizard with defaults and click Submit to create CloudFormation stack.
Select Outputs tab of the stack after stack is created.
Record the following values:
ProtectFunctionName: __________________________
ProtectFunctionProductionAlias: __________________________
ProtectLayerName: _____________________________
Protect Lambda Configuration
After CloudFormation stack is deployed, the Protect Lambda default configuration can be changed using Lambda environment configuration. See below for list of available configuration and instructions how to update it.
List of Protect Lambda Environment Variables
Variable Name
Description
Notes
LOG_REDSHIFT_CLUSTER_ARN
When enabled, Redshift cluster ARN is recorded in CloudWatch audit log.
Set LOG_REDSHIFT_CLUSTER_ARN = 1 to enable.
See Audit Logging for audit log examples.
Updating Lambda Configuration
From your AWS console, navigate to Lambda and select the following Lambda:
Protegrity_Protect_<STACK_NAME>
Select Configuration tab and scroll down to the Environment variables section. Select Edit then Add environment variable. For the list of allowed variables and corresponding values refer to the table above.
Delete API Gateway (Optional)
CloudFormation created an API Gateway that makes this product compatible with Snowflake. However, this service is not required for Amazon Redshift so it may be optionally removed.
To delete API Gateway:
From Services, access API Gateway.
Select the API Gateway service that is created.
Note
Sort by Created date. The name will have the same extension as the stack name created aboveClick Actions > Delete.
Add Lambda Protect IAM Permissions to Role
To add inline Lambda Protect IAM permissions to role:
Select the role created in section Create IAM Account Role (DBRoleName).
Tip
Sort descending by created date.In the Permissions tab, click Add inline policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "ProtegrityProtectInvokePermission", "Effect": "Allow", "Action": "lambda:InvokeFunction", "Resource": "arn:aws:lambda:*:*:function:*" } ] }Edit the Resource value in the snippet with the ARN of the Protect Lambda function to further restrict privileges.
Attach IAM Account Role to Redshift
Perform the following steps to allow Redshift to invoke the Protect Lambda function.
Note
This step is not required when the Protegrity Solution is not installed on the same AWS account as Amazon Redshift Cluster. For more information about Cross-Account Installation, refer to Cross-Account Configuration.Attach the IAM role (DBRoleName) created in Create IAM Account Role to the Redshift cluster.
To attach IAM account role to Redshift:
From the AWS console, access Amazon Redshift and click on the cluster.
Select Actions > Manage IAM Roles.
Under Available IAM roles, select Enter ARN.
Enter the Role ARN recorded in Create Protect Lambda IAM Role.
Click Add IAM role.
Note
After attaching the role, wait for the cluster to complete modification status (in the cluster status) before proceeding to test connectivity.
Test Connectivity
Perform the following steps to verify if Redshift is working correctly with the Protegrity product.
To test the connectivity:
Access the Redshift SQL console.
Copy and paste the following snippet into a worksheet.
CREATE OR REPLACE EXTERNAL FUNCTION pty_unprotect_alpha(varchar) RETURNS varchar VOLATILE lambda '<replace_with_protect_function_name>:Production' iam_role 'arn:aws:iam::<you-awsaccount- number>:role/<role-name>Replace the placeholder values with the lambda function name and role created in earlier steps.
Run the following command in the console:
select pty_unprotect_alpha('UtfVk UHgcD!')Verify that the string hello world! is returned.
Troubleshooting Tips
Error | Action |
|---|---|
Empty result or Invalid operation error |
|
What’s Next
3.3.4 - Policy Agent Installation
The following sections will install the Policy Agent. The Policy Agent polls the ESA and deploys the policy to Protegrity Serverless as a static resource. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. Contact Protegrity Professional Services for further guidance on configuration alternatives in the Cloud.
Important
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), refer to the PPC Appendix: Policy Agent Certificate and Key Guidance for specific instructions on obtaining and using the CA certificate and datastore key fingerprint. The steps in this section are specific to ESA and may differ for PPC. Be sure to follow the PPC documentation for the most accurate and up-to-date setup guidance.ESA Server
Policy Agent Lambda requires ESA server running and accessible on TCP port 443.
Note down ESA IP address:
ESA IP Address (EsaIpAddress): ___________________
Certificates on ESA
Note
If you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), see PPC Appendix: Policy Agent Certificate Guidance for specific instructions on obtaining and using the CA certificate. The steps in this section are specific to ESA and may differ for PPC.Whether your ESA is configured with default self-signed certificate or your corporate CA certificate, Policy Agent can validate authenticity of ESA connection using CA certificate. The process for both scenarios is the same:
- Obtain CA certificate
- Convert CA certificate to a value accepted by Policy Agent
- Provide converted CA certificate value to Policy Agent
To obtain self-signed CA certificate from ESA:
Log in to ESA Web UI.
Select Settings > Network > Manage Certificates.
Hover over Server Certificate and click on download icon to download the CA certificate.
To convert downloaded CA certificate to a value accepted by Policy Agent, open the downloaded PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PTY_ESA_CA_SERVER_CERT or PTY_ESA_CA_SERVER_CERT_SECRET Lambda variable in section Policy Agent Lambda Configuration
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
Identify or Create a new VPC
Establish a VPC where the Policy Agent will be hosted. This VPC will need connectivity to the ESA. The VPC should be in the same account and region established in Pre-Configuration.
VPC name: ___________________
VPC Subnet Configuration
Identify or create a new subnet in the VPC where tha Lambda function will be connected to. It is recommended to use a private subnet.
Subnet name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoints Configuration
If an internal VPC was created, then add VPC Endpoints, which will be used by the Policy Agent to access AWS services. Policy Agent needs access to the following AWS services:
Type | Service name |
|---|---|
Interface | com.amazonaws.{REGION}.secretsmanager |
Interface | com.amazonaws.{REGION}.kms |
Gateway | com.amazonaws.{REGION}.s3 |
Interface | com.amazonaws.{REGION}.lambda |
Identify or Create Security Groups
Policy Agent and cloud-based ESA appliance use AWS security groups to control traffic that is allowed to leave and reach them. Policy Agent runs on schedule and is mostly concerned with allowing traffic out of itself to ESA and AWS services it depends on. ESA runs most of the time and it must allow Policy Agent to connect to it.
Policy Agent security group must allow outbound traffic using rules described in the table below. To edit security group navigate:
From VPC > Security Groups > Policy Agent Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG | ESA Communication |
| HTTPS | TCP | 443 | Any | AWS Services |
Record Policy Agent security group ID:
Policy Agent Security Group Id: ___________________
Policy Agent will reach out to ESA on port 443. Create following inbound security group rule for cloud-based ESA appliance to allow connections from Policy Agent:
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 443 | Policy Agent Lambda SG |
Creating ESA Credentials
Policy Agent Lambda requires ESA credentials to be provided as one of the three options.
Note
The username and password of the ESA user requires role with Export Resilient Package and Can Create JWT Token permissions. Security Administrator is one of the predefined roles which contains the above permissions, however for separation of duties it is recommended to create custom role.Option 1: Secrets Manager
Creating secrets manager secret with ESA username and password.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the username and password key value pair.
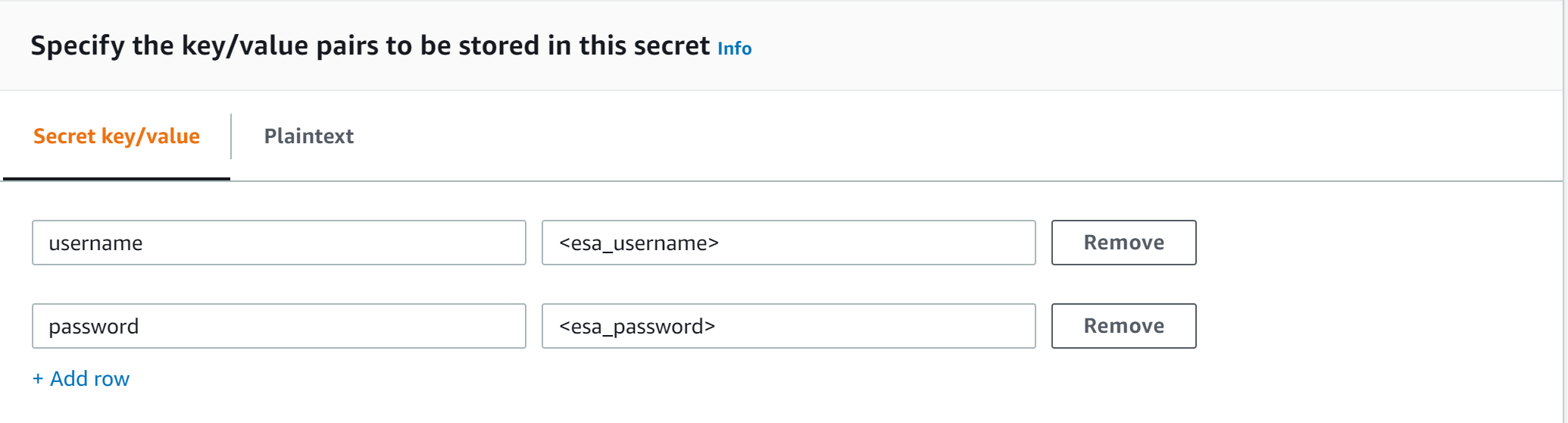
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it.
ESA Credentials Secret Name: __________________
Option 2: KMS Encrypted Password
ESA password is encrypted with AWS KMS symmetric key.
Create AWS KMS symmetric key which will be used to encrypt ESA password. See Create KMS Key for instructions on how to create KMS symmetric key using AWS console.
Record KMS Key ARN.
ESA PASSWORD KMS KEY ARN: __________________
Run AWS CLI command to encrypt ESA password. Below you can find sample Linux aws cli command. Replace <key_arn> with KMS symmetric key ARN.
aws kms encrypt --key-id <key_arn> --plaintext $(echo '<esa_password>' | base64 )Sample output.
{ "CiphertextBlob": "esa_encrypted_password", "KeyId": "arn:aws:kms:region:aws_account:key/key_id ", "EncryptionAlgorithm": "SYMMETRIC_DEFAULT" }Record ESA username and encrypted password.
ESA USERNAME: __________________
ESA ENCRYPTED PASSWORD: __________________
Option 3: Custom AWS Lambda function
With this option ESA username and password are returned by a custom AWS Lambda function. This method may be used to get the username and password from external vaults.
Create AWS Lambda in any AWS supported runtime.
There is no input needed.
The Lambda function must return the following response schema.
response: type: object properties: username: string password: stringFor example,
example output: {"username": "admin", "password": "Password1234"}Sample AWS Lambda function in Python:
import json def lambda_handler(event, context): return {"username": "admin", "password": "password1234"}Warning
Protegrity does not recommend hardcoding ESA username and password in the clear.
Record the Lambda name:
Custom AWS lambda for ESA credentials: _______________
Create Agent Lambda IAM Policy
Follow the steps below to create Lambda execution policies.
Create Agent Lambda IAM policy
From AWS IAM console, select Policies > Create Policy.
Select JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "KmsEncrypt", "Effect": "Allow", "Action": [ "kms:GetPublicKey" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace wildcard * with the region, account, and resource name information where required.
This step is required if KMS is used to encrypt ESA password.
Add policy entry below. Replace ESA PASSWORD KMS KEY ARN with the value recorded in Option 2: KMS Encrypted Password.
{ "Sid": "KmsDecryptEsaPassword", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "**ESA PASSWORD KMS KEY ARN**" ] }Select Next type in the policy name and Create Policy. Record policy name:
Policy Name: ___________________
Create Agent Lambda IAM Role
Perform the following steps to create Agent Lambda execution IAM role.
To create agent Lambda IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Agent Lambda IAM policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityAgentRole and click Confirm.
Select Create role.
Record the role ARN.
Agent Lambda IAM Execution Role Name: ___________________
Corporate Firewall Configuration
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access from the NAT Gateway IP to ESA via port 443 and 443.
CloudFormation Installation
Create the Policy Agent in the VPC using the CloudFormation script provided by Protegrity.
Access the CloudFormation service.
Select the target installation region.
Create a stack with new resources.
Upload the Policy Agent CloudFormation template (file name: pty_agent_cf.json).
Specify the following parameters for Cloud Formation:
Parameter Description Note VPC VPC where the Policy Agent will be hosted Identify or Create a new VPC Subnet Subnet where the Policy Agent will be hosted VPC Subnet Configuration PolicyAgentSecurityGroupId Security Group Id, which allows communication between the Policy Agent and the ESA Identify or Create Security Groups LambdaExecutionRoleArn Agent Lambda IAM execution role ARN allowing access to the S3 bucket, KMS encryption Key, Lambda and Lambda Layer Create Agent Lambda IAM Role ArtifactS3Bucket S3 bucket name with deployment package for the Policy Agent Use S3 Bucket name recorded in Create S3 bucket for Installing Artifacts CreateCRONJob Set to True to create a CloudWatch schedule for the agent to run. Default: False
Policy Agent Lambda Configuration
After the CloudFormation stack is deployed, the Policy Agent Lambda must be configured with parameters recorded in earlier steps. From your AWS Console, navigate to lambda and select the following Lambda.
Protegrity_Agent<STACK_NAME>_
Select Configuration tab and scroll down to the Environment variables section. Select Editand replace all entries with the actual values.
Parameter | Description | Notes |
|---|---|---|
PTY_ESA_IP | ESA IP address or hostname | |
PTY_ESA_CA_SERVER_CERT | ESA self-signed CA certificate or your corporate CA certificate used by policy Agent Lambda to ensure ESA is the trusted server. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT configuration will be ignored. |
PTY_ESA_CA_SERVER_CERT_SECRET | This configuration option fulfills the same function as PTY_ESA_CA_SERVER_CERT but supports larger configuration values, making it the recommended choice. The value should specify the name of the AWS Secrets Manager secret containing the ESA self-signed CA certificate. The secret value should be set to the json with “PTY_ESA_CA_SERVER_CERT” key and PEM formated CA certificate content value as shown below. | Recorded in step Certificates on ESA NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate Guidance for details on obtaining and using the CA certificate.In case ESA is configured with publicly signed certificates, the PTY_ESA_CA_SERVER_CERT_SECRET configuration will be ignored. When both PTY_ESA_CA_SERVER_CERT and PTY_ESA_CA_SERVER_CERT_SECRET are configured the PTY_ESA_CA_SERVER_CERT_SECRET takes precedence. |
PTY_ESA_CREDENTIALS_SECRET | ESA username and password (encrypted value by AWS Secrets Manager) | |
PTY_DATASTORE_KEY | ESA policy datastore public key fingerprint (64 char long) e.g. 123bff642f621123d845f006c6bfff27737b21299e8a2ef6380aa642e76e89e5. | NoteThis configuration is not applicable for ESA versions lower than 10.2.The export key is the public part of an asymmetric key pair created in a Create KMS Key. A user with Security Officer permissions adds the public key to the data store in ESA via Policy Management > Data Stores > Export Keys. The fingerprint can then be copied using the Copy Fingerprint icon next to the key. Refer to Exporting Keys to Datastore for details. NoteFor PPC deployments, see PPC Appendix: Policy Agent Certificate and Key Guidance for details on obtaining and using the datastore key fingerprint. |
AWS_KMS_KEY_ID | KMS key id or full ARN e.g. arn:aws:kms:us-west-2:112233445566:key/bfb6c4fb-509a-43ac-b0aa-82f1ca0b52d3 | |
AWS_POLICY_S3_BUCKET | S3 bucket where the encrypted policy will be written | S3 bucket of your choice |
AWS_POLICY_S3_FILENAME | Filename of the encrypted policy stored in S3 bucket | Default: protegrity-policy.zip |
AWS_PROTECT_FN_NAME | Comma separated list of Protect function names or ARNs | ProtectFunctionName(s), recorded in CloudFormation Installation |
DISABLE_DEPLOY | This flag can be either 1 or 0. If set to 1, then the agent will not update PTY_PROTECT lambda with the newest policy. Else, the policy will be saved in the S3 bucket and deployed to the Lambda Layer | Default: 0 |
AWS_POLICY_LAYER_NAME | Lambda layer used to store the Protegrity policy used by the PTY_PROTECT function |
|
POLICY_LAYER_RETAIN | Number of policy versions to retain as backup. (e.g. 2 will retain the latest 2 policies and remove older ones). -1 retains all. | Default: 2 |
POLICY_PULL_TIMEOUT | Time in seconds to wait for the ESA to send the full policy | Default: 20s |
ESA_CONNECTION_TIMEOUT | Time in seconds to wait for the ESA response | Default: 5s |
LOG_LEVEL | Application and audit logs verbiage level | Default: INFO Allowed values: DEBUG – the most verbose, INFO, WARNING, ERROR – the least verbose |
PTY_CORE_EMPTYSTRING | Override default behavior. Empty string response values are returned as null values. For instance: (un)protect(’’) -> null (un)protect(’’) -> '' | Default: empty Allowed values: null empty |
PTY_CORE_CASESENSITIVE | Specifies whether policy usernames should be case sensitive | Default: no Allowed values: yes no |
PTY_ADDIPADDRESSHEADER | When enabled, agent will send its source IP address in the request header. This configuration works in conjunction with ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP (default=false). See Associating ESA Data Store With Cloud Protect Agent for more information. | Default: yes Allowed values: yes no |
PTY_ESA_USERNAME | Plaintext ESA username which is used together with PTY_ESA_ENCRYPTED_PASSWORD as an optional ESA credentials | Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored |
PTY_ESA_ENCRYPTED_PASSWORD | ESA password encrypted with KMS symmetric key. Example AWS cli command to generate the value:
| Option 2: KMS Encrypted Password Presence of this parameter will cause PTY_ESA_CREDENTIALS_SECRET to be ignored Value must be base64 encoded |
EMPTY_POLICY_S3 | This flag can be either 1 or 0. If set to 1, then the agent will remove the content of the policy file in S3 bucket, but will keep the checksum in the metadata. Else, the policy will be saved in the S3 bucket and not removed. | Default: 0 |
PTY_ESA_CREDENTIALS_LAMBDA | Lambda function to return ESA credentials | Recorded in step Option 3: Custom AWS Lambda function LAMBDA FOR ESA CREDENTIALS. Presence of PTY_ESA_USERNAME, or PTY_ESA_CREDENTIALS_SECRET will cause this value to be ignored. The Policy Agent Lambda must have network access and IAM permissions to invoke the custom ESA Credentials Lambda you have created in Option 3: Custom AWS Lambda function. |
Test Installation
Open the Lambda and configure Test to execute the lambda and specify the default test event. Wait for around 20 seconds for the Lambda to complete. If policy is downloaded successfully, then a success message appears.
Navigate to the AWS_POLICY_S3_BUCKET bucket and verify that the AWS_POLICY_S3_FILENAME file was created.
Troubleshooting
Lambda Error | Example Error | Action |
|---|---|---|
Task timed out after x seconds | |
|
ESA connection error. Failed to download certificates | ||
Policy Pull takes a long time | |
|
ESA connection error. Failed to download certificates. HTTP response code: 401 | | Ensure that the PTY_ESA_CREDENTIALS_SECRET has correct ESA username and password |
An error occurred (AccessDeniedException) when calling xyz operation | | Ensure that the Lambda execution role has permission to call the xyz operation |
Access Denied to Secret Manager. | |
|
Master Key xyz unable to generate data key | Ensure that the Lambda can access xyz CMK key | |
The S3 bucket server-side encryption is enabled, the encryption key type is SSE-KMS but the Policy Agent execution IAM role doesn’t have permissions to encrypt using the KMS key . | | Add the following permissions to the Policy Agent excution role. NoteWhen the KMS key and the Policy Agent Lambda are in separate accounts, update both the AWS KMS key and the Policy Agent execution role. |
The S3 bucket has bucket policy to only allow access from within the VPC. | | The Policy Agent publishes a new Lambda Layer version, and the Lambda Layer service uploads the policy file from the s3 bucket and the upload request is originated from the AWS service outside the Policy Agent Lambda VPC. Update the S3 bucket resource policy to allow access from AWS Service. Sample security policy to lock down access to the vpc: |
Additional Configuration
Strengthen the KMS IAM policy by granting access only to the required Lambda function(s).
Finalize the IAM policy for the Lambda Execution Role. Ensure to replace wildcard * with the region, account, and resource name information where required.
For example,
"arn:aws:lambda:*:*:function:*" -> "arn:aws:lambda:us-east-1:account:function:function_name"
Policy Agent Schedule
If specified in CloudFormation Installation, the agent installation created a CloudWatch event rule, which checks for policy update on an hourly schedule. This schedule can be altered to the required frequency.
Under CloudWatch > Events > Rules, find Protegrity_Agent_{stack_name}. Click Action > Edit Set the cron expression. A cron expression can easily be defined using CronMaker, a free online tool. Refer to http://www.cronmaker.com.
What’s Next
3.3.5 - Audit Log Forwarder Installation
The following sections show steps how to install Audit Log Forwarder component in the AWS Cloud. The Log Forwarder deployment allows for the audit logs generated by Protector to be delivered to ESA for auditing and governance purposes. Log Forwarder component is optional and is not required for the Protector Service to work properly. See Log Forwarding Architecture section in this document for more information. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. C ontact Protegrity for further guidance on configuration alternatives in the Cloud.
Note
The installation steps below assume that the Log Forwarder is going to be installed in the same AWS account as the corresponding Protect Lambda service. For instructions on how to install Log Forwarder in the AWS account separate than the Protect Lambda, please contact Protegrity.ESA Audit Store Configuration
ESA server is required as the recipient of audit logs. Verify the information below to ensure ESA is accessible and configured properly.
ESA server running and accessible on TCP port 9200 (Audit Store) or 24284 (td-agent).
Audit Store service is configured and running on ESA. Applies when audit logs are output to Audit Store directly or through td-agent. For information related to ESA Audit Store configuration, refer to Audit Store Guide.
(Optional) td-agent is configured for external input. For more information related to td-agent configuration, refer to ESA guide Sending logs to an external security information and event management (SIEM).
Certificates on ESA
Note
This section is optional. If CA certificate is not provided, the Log Forwarder will skip server certificate validation and will connect to ESA without verifying that it is a trusted server.
If you are deploying Log Forwarder with Protegrity Provisioned Cluster (PPC), certificate authorization and CA validation are not supported. Configuration steps related to certificates in this section do not apply to PPC. See Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster): Log Forwarder Setup with PPC for details.
By default, ESA is configured with self-signed certificates, which can optionally be validated using a self-signed CA certificate supplied in the Log Forwarder configuration. If no CA certificate is provided, the Log Forwarder will skip server certificate validation.
Note
Certificate Validation can be bypassed for testing purposes, see section: Install through CloudFormationIf ESA is configured with publicly signed certificates, this section can be skipped since the forwarder Lambda will use the public CA to validate ESA certificates.
To obtain the self-signed CA certificate from ESA:
Download ESA CA certificate from the /etc/ksa/certificates/plug directory of the ESA
After certificate is downloaded, open the PEM file in text editor and replace all new lines with escaped new line: \n.
To escape new lines from command line, use one of the following commands depending on your operating system:
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' ProtegrityCA.pem > output.txtWindows PowerShell:
(Get-Content '.\ProtegrityCA.pem') -join '\n' | Set-Content 'output.txt'Record the certificate content with new lines escaped.
ESA CA Server Certificate (EsaCaCert): ___________________
This value will be used to set PtyEsaCaServerCert cloudformation parameter in section Install through CloudFormation
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation.
AWS VPC Configuration
Log forwarder Lambda function requires network connectivity to ESA, similar to Policy Agent Lambda function. Therefore, it can be hosted in the same VPC as Policy Agent.
Separate VPC can be used, as long as it provides network connectivity to ESA.
Note
AWS Lambda service uses permissions in log forwarder function execution role to create and manage network interfaces. Lambda creates a Hyperplane ENI and reuses it for other VPC-enabled functions in your account that use the same subnet and security group combination. Each Hyperplane ENI can handle thousands of connections/ports as the Lambda function scales up. If more connections are needed AWS Lambda service creates additional Hyperplane ENIs. There’s no additional charge for using a VPC or a Hyperplane ENI. Refer to AWS official Lambda Hyperplane ENIs docs for more information.VPC Name: ___________________
VPC Subnet Configuration
Log Forwarder can be connected to the same subnet as Policy Agent or separate one as long as it provides connectivity to ESA.
Subnet Name: ___________________
NAT Gateway For ESA Hosted Outside AWS Network
If ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well.
VPC Endpoint Configuration
Log Forwarder Lambda function requires connectivity to Secrets Manager AWS service. If the VPC identified in the steps before has no connectivity to public internet through the NAT Gateway, then the following service endpoint must be configured:
- com.amazonaws.{REGION}.cloudwatch
- com.amazonaws.{REGION}.secretsmanager
- com.amazonaws.{REGION}.kms
Security Group Configuration
Security groups restrict communication between Log Forwarder Lambda function and the ESA appliance. The following rules must be in place for ESA and Log Forwarder Lambda function.
From VPC > Security Groups > Log Forwarder Security Group configuration.
| Type | Protocol | Port Range | Destination | Reason |
|---|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG | ESA Communication |
Record the name of Log Forwarder security group name.
Log Forwarder Security Group Id: ___________________
The following port must be open for the ESA. If the ESA is running in the Cloud, then create the following security.
Note
If an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access the NAT Gateway IP access to ESA via port 9200.ESA Security Group configuration
| Type | Protocol | Port Range | Source |
|---|---|---|---|
| Custom TCP | TCP | 9200 | Log Forwarder Lambda SG |
Configure ESA Audit Store Credentials
Note
This section is optional. If client certificate authentication is not set up, the Log Forwarder will connect to ESA without authentication credentials.Audit Log Forwarder can optionally authenticate with ESA using certificate-based authentication with a client certificate and certificate key. If used, both the certificate and certificate key will be stored in AWS Secrets Manager.
Download the following certificates from the /etc/ksa/certificates/plug directory of the ESA:
- client.key
- client.pem
After certificates are downloaded, open each PEM file in text editor and replace all new lines with escaped new line: \n. To escape new lines from command line, use one of the commands below depending on your operating system.
Linux Bash:
awk 'NF {printf "%s\\n",$0;}' client.key > private_key.txt
awk 'NF {printf "%s\\n",$0;}' client.pem > public_key.txt
Windows PowerShell:
(Get-Content '.\client.key') -join '\n' | Set-Content 'private_key.pem'
(Get-Content '.\client.pem') -join '\n' | Set-Content 'public_key.pem'
For more information on how to configure client certificate authentication for Audit Store on ESA refer to Audit Store Guide.
To create secret with ESA client certificate/key pair in AWS Secrets Manager.
From the AWS Secrets Manager Console, select Store New Secret.
Select Other Type of Secrets.
Specify the private_key and public_key value pair.
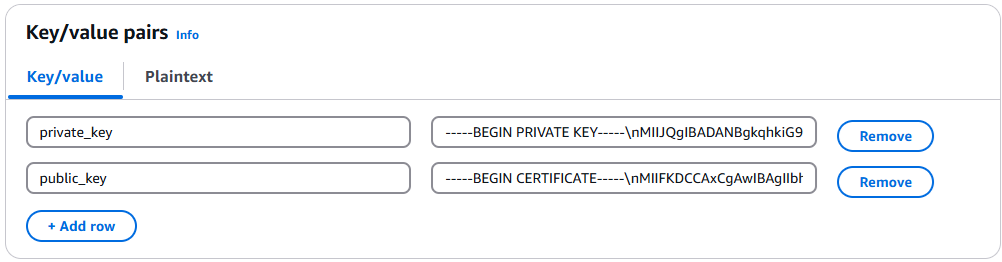
Select the encryption key or leave default AWS managed key.
Specify the Secret Name and record it below.
ESA Client Certificate/Key Pair Secret Name: ___________________
This value will be used to set PtyEsaClientCertificatesSecretId cloudformation parameter in section Install through CloudFormation
Note
If you are deploying Log Forwarder with PPC, do not configure client certificate authentication. See PPC Appendix: Log Forwarder Certificate Guidance for details.Create Audit Log Forwarder IAM Execution Policy
This task defines a policy used by the Protegrity Log Forwarder Lambda function to write CloudWatch logs, access the KMS encryption key to decrypt the policy and access Secrets Manager for log forwarder user credentials.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "EC2ModifyNetworkInterfaces", "Effect": "Allow", "Action": [ "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DeleteNetworkInterface" ], "Resource": "*" }, { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] }, { "Sid": "KinesisStreamRead", "Effect": "Allow", "Action": [ "kinesis:GetRecords", "kinesis:GetShardIterator", "kinesis:DescribeStream", "kinesis:DescribeStreamSummary", "kinesis:ListShards", "kinesis:ListStreams" ], "Resource": "*" }, { "Sid": "SecretsManagerGetSecret", "Effect": "Allow", "Action": [ "secretsmanager:GetSecretValue" ], "Resource": [ "arn:aws:secretsmanager:*:*:secret:*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Review policy, type in a policy name, for example, ProtegrityLogForwarderLambdaPolicy and Confirm. Record the policy name:
LogForwarderLambdaPolicyName:__________________
Create Log Forwarder IAM Role
Perform the following steps to create Log Forwarder execution IAM role.
To create Log Forwarder IAM role:
From AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
Select the policy created in Create Audit Log Forwarder IAM Execution Policy.
Proceed to Name, Review and Create.
Type the role name, for example, ProtegrityForwarderRole and click Confirm.
Record the role ARN.
Log Forwarder IAM Execution Role Name: ___________________
Installation Artifacts
Audit Log Forwarder installation artifacts are part of the same deployment package as the one used for protect and policy agent services. Follow the steps below to ensure the right artifacts are available for log forwarder installation.
Verify that the Protegrity deployment package is available on your local system, if not, you can download it from the Protegrity portal.
Note
If you maintain multiple Protegrity Cloud Protectors, make sure that the deployment package downloaded for Audit Log Forwarder is the same as the one used for Protect service installation.Extract the pty_log_forwarder_cf.json cloud formation file from the deployment package.
Check the S3 deployment bucket identified in section Create S3 bucket for Installing Artifacts. Make sure that all Protegrity deployment zip files are uploaded to the S3 bucket.
Install through CloudFormation
The following steps describe the deployment of the Audit Log Forwarder AWS cloud components.
Access CloudFormation and select the target AWS Region in the console.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_log_forwarder_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in the pre-configuration steps.
Parameter | Description | Default Value | Required |
|---|---|---|---|
LogForwarderSubnets | Subnets where the Log Forwarder will be hosted. |
|
|
LogForwarderSecurityGroups | Security Groups, which allow communication between the Log Forwarder and ESA. |
| X |
LambdaExecutionRoleArn | The ARN of Lambda role created in the prior step. |
| X |
ArtifactS3Bucket | Name of S3 bucket created in the pre-configuration step. |
| X |
LogDestinationEsaIp | IP or FQDN of the ESA instance or cluster. |
| X |
AuditLogOutput | Audit log processor to target on ESA. Allowed values: audit-store, td-agent | audit-store | X |
PtyEsaClientCertificatesSecretId | AWS Secrets Manager secret id containing client certificates used for authentication with ESA Audit Store. It is expected that the public key will be stored in a field public_key and the private key in a field named private_key. This parameter is optional. If not provided, Log Forwarder will connect to ESA without client certificate authentication. | ||
EsaTlsDisableCertVerify | Disable certificate verification when connecting to ESA if set to 1. This is only for dev purposes, do not disable in production environment. | 0 | X |
PtyEsaCaServerCert | ESA self-signed CA certificate used by log forwarder Lambda to ensure ESA is the trusted server. Recorded in step Certificates on ESA In case ESA is configured with publicly signed certificates, the PtyEsaCaServerCert configuration will be ignored. |
| |
EsaConnectTimeout | Time in seconds to wait for the ESA response. Minimum value: 1. | 5 | X |
EsaVirtualHost | ESA virtual hostname. This configuration is optional and it can be used when proxy server is present and supports TLS SNI extension. |
|
|
KinesisLogStreamRetentionPeriodHours | The number of hours for the log records to be stored in Kinesis Stream in case log destination server is not available. Minimum value: 24. See Log Forwarder Performance section for more details. | 24 | X |
KinesisLogStreamShardCount | The number of shards that the Kinesis log stream uses. For greater provisioned throughput, increase the number of shards. Minimum value: 1. See Log Forwarder Performance section for more details. | 10 | X |
MinLogLevel | Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all | severe | X |
Click Next with defaults to complete CloudFormation.
After CloudFormation is completed, select the Outputstab in the stack.
Record the following values
KinesisLogStreamArn: ________________________________
Add Kinesis Put Record permission to the Protect Function IAM Role
Login to the AWS account that hosts the Protect Lambda Function.
Search for Protect Lambda Function IAM Execution Role Name created in Create Protect Lambda IAM role.
Under Permissions policies, select Add Permissions > Create inline policy.
In Specify permissions view, switch to JSON.
Copy the policy json from below replacing the placeholder value indicated in the following snippet as <Audit Log Kinesis Stream ARN> with the value recorded in the previous step.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "KinesisPutRecords", "Effect": "Allow", "Action": "kinesis:PutRecords", "Resource": "<Audit Log Kinesis Stream ARN>" } ] }When you are finished, choose Next.
On the Review and create page, type a Name, then choose Create policy.
Test Log Forwarder Installation
Testing in this section validates the connectivity between Log Forwarder and ESA. The sample policy included with the initial installation and test event below are not based on your ESA policy. Any logs forwarded to ESA which are not signed with a policy generated by your ESA will not be added to the audit store.
Install Log Forwarder and configure according to previous sections. Log Forwarder configuration MinLogLevel must be at least info level.
Navigate to the log forwarder lambda function.
Select the Test tab.
Copy the json test event into the Event JSON pane.
{ "Records": [ { "kinesis": { "kinesisSchemaVersion": "1.0", "partitionKey": "041e96d78c778677ce43f50076a8ae3e", "sequenceNumber": "49620336010289430959432297775520367512250709822916263938", "data": "eyJpbmdlc3RfdGltZV91dGMiOiIyMDI2LTAzLTI3VDEzOjIzOjEyLjkwNFoiLCJhZGRpdGlvbmFsX2luZm8iOnsiZGVzY3JpcHRpb24iOiJEYXRhIHVucHJvdGVjdCBvcGVyYXRpb24gd2FzIHN1Y2Nlc3NmdWwuIn0sImNsaWVudCI6e30sImNudCI6NCwiY29ycmVsYXRpb25pZCI6InJzLXF1ZXJ5LWlkOjEyMzQiLCJsZXZlbCI6IlNVQ0NFU1MiLCJsb2d0eXBlIjoiUHJvdGVjdGlvbiIsIm9yaWdpbiI6eyJob3N0bmFtZSI6IlBSTy1VUy1QRjNSSEdGOSIsImlwIjoiMTAuMTAuMTAuMTAiLCJ0aW1lX3V0YyI6MTcxMTU1OTEwMH0sInByb2Nlc3MiOnsiaWQiOjJ9LCJwcm90ZWN0aW9uIjp7ImF1ZGl0X2NvZGUiOjgsImRhdGFlbGVtZW50IjoiYWxwaGEiLCJkYXRhc3RvcmUiOiJTQU1QTEVfUE9MSUNZIiwibWFza19zZXR0aW5nIjoiIiwib2xkX2RhdGFlbGVtZW50IjpudWxsLCJvcGVyYXRpb24iOiJVbnByb3RlY3QiLCJwb2xpY3lfdXNlciI6IlBUWURFViJ9LCJwcm90ZWN0b3IiOnsiY29yZV92ZXJzaW9uIjoiMS4yLjErNTUuZzU5MGZlLkhFQUQiLCJmYW1pbHkiOiJjcCIsInBjY192ZXJzaW9uIjoiMy40LjAuMTQiLCJ2ZW5kb3IiOiJyZWRzaGlmdCIsInZlcnNpb24iOiIwLjAuMS1kZXYifSwic2lnbmF0dXJlIjp7ImNoZWNrc3VtIjoiN0VCMkEzN0FDNzQ5MDM1NjQwMzBBNUUxNENCMTA5QzE0OEJGODYwRjE3NEVCMjMxMTAyMEI3RkE1QTY4MjdGQyIsImtleV9pZCI6ImM0MjQ0MzZhLTExMmYtNGMzZi1iMmRiLTEwYmFhOGI1NjJhNyJ9fQ==", "approximateArrivalTimestamp": 1626878559.213 }, "eventSource": "aws:kinesis", "eventVersion": "1.0", "eventID": "shardId-000000000000:49620336010289430959432297775520367512250709822916261234", "eventName": "aws:kinesis:record", "invokeIdentityArn": "arn:aws:iam::555555555555:role/service-role/TestRole", "awsRegion": "us-east-1", "eventSourceARN": "arn:aws:kinesis:us-east-1:555555555555:stream/CloudProtectEventStream" } ] }Note
The data payload is the base64 encoded audit log. See Audit Logging for detail on audit log contents.Select Test to execute the test event.
Test is successful if the Log Output of test results contains the following log:
[INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed recordsIf the log is not present, please consult the Troubleshooting section for common errors and solutions.
Update Protector With Kinesis Log Stream
In this section, Kinesis log stream ARN will be provided to the Protect Function installation.
Note
If the Protector has not been installed, you may provide the KinesisLogStreamArn during protector installation and skip the remainder of this section.Navigate to the Protector CloudFormation stack created in the protector installation section.
Select Update.
Choose Use existing template > Next.
Set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation.
Proceed with Next and Submit the changes.
Continue to the next section once stack status indicates UPDATE_COMPLETE.
Update Policy Agent With Log Forwarder Function Target
Log Forwarder Lambda function requires a policy layer which is in sync with the Protegrity Protector. This section will describe the steps to update the policy agent to include updating Log Forwarder Lambda function.
Note
If the policy agent has not been installed, follow the steps in Policy Agent Installation. Set AWS_PROTECT_FN_NAME to include both protector and log forwarder lambda functions.Navigate to the Policy Agent Function created in Policy Agent Installation
Select Configuration > Environment variables > Edit
Edit the value for environment variable AWS_PROTECT_FN_NAME to include the log forwarder function name/arn in the comma separated list of Lambda functions.
Save the changes and continue when update completes
Navigate to Test tab
Add an event {} and select Test to run the Policy Agent function
Verify Log forwarder function was updated to use the policy layer by inspecting the log output. Logs should include the following:
[INFO] 2024-07-09 18:58:04,793.793Z 622d374b-1f73-4123-9a38-abc61973adef iap_agent.policy_deployer:Updating lambda [Protegrity_LogForwarder_<stack ID>] to use layer version [arn:aws:lambda:<aws region>:<aws account number>:layer:Protegrity_Layer_<layer name>:<layer version>]
Test Full Log Forwarder Installation
Install and configure Protegrity Agent, Protector, and Log Forwarder components.
Send a protect operation to the protector using a data element or user which will result in audit log generation
Navigate to the CloudWatch log group for the Protect function
Select the log stream for the test operation and scroll to the latest logs
Expect to see a log similar to the below:
[2024-07-09T19:28:23.158] [INFO] [kinesis-external-sink.cpp:51] Sending 2 logs to Kinesis ... [2024-07-09T19:28:23.218] [INFO] [aws-utils.cpp:206] Kinesis send time: 0.060sNavigate to the CloudWatch log group for the Log Forwarder function
Expect to see a new log stream - it may take several minutes for the stream to start
Select the new stream and scroll to the most recent logs in the stream
Expect to see a log similar to the below:
[2024-07-09T19:32:31.648] [INFO] [kinesis-log-aggregation-format.cpp:77] Aggregated 1 records into 0 aggregated, 1 forwarded and 0 failed records
Troubleshooting
Error | Action |
|---|---|
Log forwarder log contains severe level secrets permissions error: |
|
When testing log forwarder as described in Test Log Forwarder Installation, response contains policy decryption error: |
|
Cloudformation stack creation fails with error: |
|
Severe level kinesis permissions log message in protector function: |
|
TLS errors reported in log forwarder function logs: |
|
3.3.6 -
Prerequisites
| Requirements | Description |
|---|---|
| Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
| Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
| AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
| Redshift cluster (Enterprise Edition) | Must be in the same region as Protegrity Protect Lambda |
3.3.7 -
AWS Services
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials. |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
3.3.8 -
Required Skills and Abilities
| Requirements | Description |
|---|---|
| AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
| Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
| Redshift Administrator | Account Admin access required to setup access |
| Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
3.4 - Understanding Redshift Objects
External Functions
Redshift provides an External Function capability that is used to call out to a process external to Redshift. In this solution, the external service is Protegrity Redshift Protector, an AWS Lambda for re-identification operations.
Function Naming Convention
The request payload header indicates the current user context making the Protegrity operation through an SQL request. Protegrity also requires the type of operation and the security policy element name. Protegrity Serverless provides a UDF function naming convention to provide this additional context.
The function name convention requires the prefix pty, the type of operation (protect or unprotect), and the ESA policy element name. The three tokens are separated by underscores. Additional underscores are interpreted as part of the element name. (e.g. pty_protect_tok_deSSN).
The UDF naming convention is as follows.
| Token | Description | Valid Options |
|---|---|---|
| Prefix | Required to indicate this method | pty |
| operation | Type of operation | protect, unprotect |
| Element name | ESA element name | Valid ESA element name (can contain additional underscores) |
For example, the following UDF will perform an unprotect using the alpha element policy.
CREATE OR REPLACE EXTERNAL FUNCTION pty_unprotect_alpha(varchar)
RETURNS varchar VOLATILE lambda '<replace_with_protect_function_name>:Production' iam_role 'arn:aws:iam::<you-aws-account-number>:role/<role-name>'
Mapping File
Protegrity Serverless provides an additional method for mapping UDF function names to operations and security policy elements through a JSON mapping file. This method is recommended when either custom naming conventions are needed or element names do not conform to Redshift’s function naming validation rules. Here is an example.
The mapping file must be provided in the same S3 bucket as policy export: AWS_POLICY_S3_BUCKET
{
"myudf_unp_city":
{
"Operation": "unprotect",
"Element": "deCity”
},
"myudf_pro_dob": {
"Operation": "protect",
"Element": "deBirthdate"
},
...
}
The example mapping above would cause Protegrity Serverless to perform an unprotect on the deCity security element for the requests made from the myudf_unp_city UDF function within Redshift.
Note
The prefix pty is reserved for the method described in Function Naming Convention. The Policy Agent must be triggered to load the load the mapping files.3.4.1 -
External Functions
Redshift provides an External Function capability that is used to call out to a process external to Redshift. In this solution, the external service is Protegrity Redshift Protector, an AWS Lambda for re-identification operations.
3.4.2 -
Function Naming Convention
The request payload header indicates the current user context making the Protegrity operation through an SQL request. Protegrity also requires the type of operation and the security policy element name. Protegrity Serverless provides a UDF function naming convention to provide this additional context.
The function name convention requires the prefix pty, the type of operation (protect or unprotect), and the ESA policy element name. The three tokens are separated by underscores. Additional underscores are interpreted as part of the element name. (e.g. pty_protect_tok_deSSN).
The UDF naming convention is as follows.
| Token | Description | Valid Options |
|---|---|---|
| Prefix | Required to indicate this method | pty |
| operation | Type of operation | protect, unprotect |
| Element name | ESA element name | Valid ESA element name (can contain additional underscores) |
For example, the following UDF will perform an unprotect using the alpha element policy.
CREATE OR REPLACE EXTERNAL FUNCTION pty_unprotect_alpha(varchar)
RETURNS varchar VOLATILE lambda '<replace_with_protect_function_name>:Production' iam_role 'arn:aws:iam::<you-aws-account-number>:role/<role-name>'
3.4.3 -
Mapping File
Protegrity Serverless provides an additional method for mapping UDF function names to operations and security policy elements through a JSON mapping file. This method is recommended when either custom naming conventions are needed or element names do not conform to Redshift’s function naming validation rules. Here is an example.
The mapping file must be provided in the same S3 bucket as policy export: AWS_POLICY_S3_BUCKET
{
"myudf_unp_city":
{
"Operation": "unprotect",
"Element": "deCity”
},
"myudf_pro_dob": {
"Operation": "protect",
"Element": "deBirthdate"
},
...
}
The example mapping above would cause Protegrity Serverless to perform an unprotect on the deCity security element for the requests made from the myudf_unp_city UDF function within Redshift.
Note
The prefix pty is reserved for the method described in Function Naming Convention. The Policy Agent must be triggered to load the load the mapping files.3.5 - Performance
Performance Considerations
The following factors may cause variation in real performance versus benchmarks:
- Cold startup: The Lambda spends additional time on the initial invocation to decrypt and load the policy into memory. This time can vary between 400 ms and 1200 ms depending on the policy size. Once the Lambda is initialized, subsequent “warm executions” should process quickly.
- Size of policy: The size of the policy impacts cold start performance. Larger policies take more time to initialize.
- Lambda memory: AWS provides more virtual cores based on the memory configuration. The initial configuration of 1728 MB provides a good tradeoff between performance and cost with the benchmarked policy. Memory can be increased to optimize for your individual cases.
- Cluster size: Cluster size may make a significant difference depending on the workload.
- Number of security operations (protect or unprotect).
- Lambda concurrency and burst quotas: AWS limits the number of concurrent executions and how quickly lambda can scale to meet demand. This is discussed in an upcoming section of the document.
- Size of data element: Operations on larger text consume time.
Sample Benchmarks
The following benchmarks were performed against different cluster sizes. These are median times of approximately five runs each. The query unprotected six columns per row (first_name, last_name, email, postal_code, ssn, iban):
| Rows x Cols | # Ops | dc2.large (24 nodes) | ra3.4xl (3 nodes) | ra3.4xl (7 nodes) | ra3.16xl (7 nodes) |
|---|---|---|---|---|---|
| 1M x 6 cols | 6M | 1.6 | 1.7 | 1.5 | 1.2 |
| 10M x 6 cols | 60M | 6.0 | 6.3 | 2.8 | 3.3 |
| 100M x 6 cols | 600M | 44.3 | 49.8 | 23.4 | 15.1 |
Lambda Tuning
AWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region:

The Concurrent executions quota cap is the maximum number of Lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket.
The Burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. After the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a 429 Too Many Requests response. Redshift will generally retry until all requests succeed but may abort if a high percentage of failed responses occur.
The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended to select a Redshift AWS region with the highest burst limits.
Concurrency Troubleshooting
Hitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a Redshift query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your Lambda services in the region.
Redshift is tolerant of a certain ratio of failed requests and automatically retries. If a high percentage of requests fail, then the query may abort and the last error code will display in the console. For example, 429 Too Many Requests.
CloudWatch Metrics can be manually enabled on the Lambda to reveal if quotas are being reached. Metrics aggregate errors into two buckets that are 4xx. CloudWatch logs can be used to access the actual error code.
Log Forwarder Performance
Log forwarder architecture is optimized to minimize the amount of connections and reduce the overall network bandwidth required to send audit logs to ESA. This is achieved with batching and aggregation taking place on two levels. The first level is in protect function instances, where audit logs from consecutive requests to an instance are batched and aggregated. The second level of batching takes place in Amazon Kinesis Stream where log records from different protect function instances are additionally batched and sent to log forwarder function where they are aggregated. This section shows how to configure the deployment to accommodate different patterns of anticipated audit log stream. It also shows how to monitor deployment resources to detect problems before audit records are lost.
Protector Cloud Formation Parameters
AuditLogFlushInterval: Determines the minimum amount of time required for the audit log to be sent to Amazon Kinesis. Changing flush interval may affect the level of aggregation, which in turn may result in different number of connections and different data rates to Amazon Kinesis. Default value is 30 seconds.
Increasing the flush interval may result in higher aggregation of audit logs, in fewer connections to Amazon Kinesis, in higher latency of audit logs arriving to ESA and in higher data throughput.
Lowering the flush interval may result in lower aggregation of audit logs, in more connections to Amazon Kinesis, in lower latency of audit logs arriving to ESA and in lower data throughput.
It is not recommended to reduce the flush interval from default value in production environment as it may overload the Amazon Kinesis service. However, it may be beneficial to reduce flush interval during testing to make audit records appear on ESA faster.
Log Forwarder Cloud Formation Parameters
Amazon KinesisLogStreamShardCount: The number of shards represents the level of parallel streams in the Amazon Kinesis and it is proportional to the throughput capacity of the stream. If the number of shards is too low and the volume of audit logs is too high, Amazon Kinesis service may be overloaded and some audit records sent from protect function may be lost.
Default value is 10, however you are advised to test with a production-like load to determine whether this is sufficient or not.
Amazon KinesisLogStreamRetentionPeriodHours: The time for the audit records to be retained in Amazon Kinesis log stream in cases where log forwarder function is unable to read records from the Kinesis stream or send records to ESA, for example due to a connectivity outage. Amazon Kinesis will retain failed audit records and retry periodically until connectivity with ESA is restored or retention period expires.
Default value is 24 hours, however you are advised to review this value to align it with your Recovery Time Objective and Recovery Point Objective SLAs.
Monitoring Log Forwarder Resources
Amazon Kinesis Stream Metrics: Any positive value in Amazon Kinesis PutRecords throttled records metric indicates that audit logs rate from protect function is too high. The recommended action is to increase the Amazon KinesisLogStreamShardCount or optionally increase the AuditLogFlushInterval.
Log Forwarder Function CloudWatch Logs: If log forwarder function is unable to send logs to ESA, it will log the following message:
[SEVERE] Dropped records: x.Note
When the error message above occurs, the dropped audit records will be preserved in the Amazon Kinesis data stream and retried again according to Amazon Kinesis retry schedule. Records will be retried until Amazon KinesisLogStreamRetentionPeriodHours expires.Protect Function CloudWatch Logs: If protect function is unable to send logs to Amazon Kinesis, it will log the following message:
[SEVERE] Amazon Kinesis error, retrying in x ms (retry: y/z) ..."Any dropped audit log records will be reported with the following log message:
[SEVERE] Failed to send x/y audit logs to Amazon Kinesis.
3.5.1 -
Concurrency Troubleshooting
Hitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a Redshift query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your Lambda services in the region.
Redshift is tolerant of a certain ratio of failed requests and automatically retries. If a high percentage of requests fail, then the query may abort and the last error code will display in the console. For example, 429 Too Many Requests.
CloudWatch Metrics can be manually enabled on the Lambda to reveal if quotas are being reached. Metrics aggregate errors into two buckets that are 4xx. CloudWatch logs can be used to access the actual error code.
3.5.2 -
Lambda Tuning
AWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region:

The Concurrent executions quota cap is the maximum number of Lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket.
The Burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. After the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a 429 Too Many Requests response. Redshift will generally retry until all requests succeed but may abort if a high percentage of failed responses occur.
The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended to select a Redshift AWS region with the highest burst limits.
3.5.3 -
Sample Benchmarks
The following benchmarks were performed against different cluster sizes. These are median times of approximately five runs each. The query unprotected six columns per row (first_name, last_name, email, postal_code, ssn, iban):
| Rows x Cols | # Ops | dc2.large (24 nodes) | ra3.4xl (3 nodes) | ra3.4xl (7 nodes) | ra3.16xl (7 nodes) |
|---|---|---|---|---|---|
| 1M x 6 cols | 6M | 1.6 | 1.7 | 1.5 | 1.2 |
| 10M x 6 cols | 60M | 6.0 | 6.3 | 2.8 | 3.3 |
| 100M x 6 cols | 600M | 44.3 | 49.8 | 23.4 | 15.1 |
3.5.4 -
Performance Considerations
The following factors may cause variation in real performance versus benchmarks:
- Cold startup: The Lambda spends additional time on the initial invocation to decrypt and load the policy into memory. This time can vary between 400 ms and 1200 ms depending on the policy size. Once the Lambda is initialized, subsequent “warm executions” should process quickly.
- Size of policy: The size of the policy impacts cold start performance. Larger policies take more time to initialize.
- Lambda memory: AWS provides more virtual cores based on the memory configuration. The initial configuration of 1728 MB provides a good tradeoff between performance and cost with the benchmarked policy. Memory can be increased to optimize for your individual cases.
- Cluster size: Cluster size may make a significant difference depending on the workload.
- Number of security operations (protect or unprotect).
- Lambda concurrency and burst quotas: AWS limits the number of concurrent executions and how quickly lambda can scale to meet demand. This is discussed in an upcoming section of the document.
- Size of data element: Operations on larger text consume time.
3.6 - Audit Logging
Audit Logging
Audit records and application logs stream to Amazon CloudWatch Logs or optionally be sent to ESA. Cloud Protect uses a JSON format for audit records that is described in the following sections.
You can analyze and alert on audit records using Protegrity ESA or Amazon CloudWatch. Third-party solutions may be used if they are supported by Amazon Cloudwatch or AWS Lambda logging extensions. For more information about forwarding your audit records to ESA, contact Protegrity. For more information about Amazon CloudWatch, refer to the Amazon CloudWatch User Guide.
For more information about audit records, refer to the Protegrity Analytics Guide.
Audit record fields
The audit record format has been altered in version 3.1 of the protector to provide more information.
| Field | Description |
|---|---|
| additional_info.deployment_id | The deployment_id contains the name of the Protect Function. It is automatically set based on the cloud-specific environment variables assigned to the Protect Function. This allows identifying the Cloud Protect deployment responsible for generating audit log. |
| additional_info.cluster | (Optional) Redshift cluster ARN |
| additional_info.description | A human-readable message describing the operation |
| additional_info.query_id | (Optional) Identifies the query that triggered the operation |
| additional_info.request_id | (Optional) AWS Lambda request identifier |
| cnt | Number of operations, may be aggregated |
| correlationid | (Deprecated) Use additional_info instead |
| level | Log severity, one of: SUCCESS, WARNING, ERROR, EXCEPTION |
| logtype | Always “Protection” |
| origin.ip | The private IP address of the compute resource that operates the Protect Function and is responsible for generating the log entry.NoteThe IP address is private, meaning it is used for internal network communication and is not accessible directly from the public internet.When Log Forwarding is enabled the IP address may be aggregated into minimal CIDR blocks. |
| origin.hostname | Hostname of the system that generated the log entry |
| origin.time_utc | UTC timestamp when the log entry was generated |
| protection.audit_code | Audit code of the protect operation; see the log return codes table in the Protegrity Troubleshooting Guide |
| protection.dataelement | Data element used for the policy operation |
| protection.datastore | Name of the data store corresponding to the deployed policy |
| protection.mask_setting | (Optional) Mask setting from policy management |
| protection.operation | Operation type, one of: Protect, Unprotect, Reprotect |
| protection.policy_user | User that performed the operation |
| protector.core_version | Internal core component version |
| protector.family | Always “cp” for Cloud Protect |
| protector.lambda_version | Protector Lambda application version. |
| protector.pcc_version | Internal pcc component version |
| protector.vendor | Identifies the cloud vendor and the database vendor |
| protector.version | Protector version number |
| signature.checksum | Hash value of the signature key ID used to sign the log message when the log is generated |
| signature.key_id | Key used to sign the log message when the log is generated |
Example Audit Records
The following are sample audit messages:
Protect Success:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "Data protect operation was successful.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "SUCESS",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 6,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "B324AF7C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
User permission denied:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The user does not have the appropriate permissions to perform the requested operation.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 3,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "A216797C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
Data element not found:
{
"additional_info": {
"deployment_id": "Protegrity-Protect-function-deployment-id",
"description": "The data element could not be found in the policy.",
"query_id": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"request_id": "8476a536-e9f4-11e8-9739-2dfe598c3fcd"
},
"cnt": 4000,
"correlationid": "sf-query-id:01978dbc-0582-d7e4-0000-002a3603a20d",
"logtype": "Protection",
"level": "ERROR",
"origin": {
"hostname": "localhost",
"ip": "127.0.0.1",
"time_utc": 1635363966
},
"protection": {
"dataelement": "deAddress",
"operation": "Protect",
"audit_code": 2,
"datastore": "SAMPLE_POLICY",
"policy_user": "test_user"
},
process":{
"name":"protect",
"id":"13",
"module":"coreprovider",
"thread_id":"573580544",
"user":"sbx_user1051",
"platform":"\"Linux_x64\"",
"version":"UNKNOWN"
},
"client": {
"ip":"169.254.62.117"
},
"protector": {
"family": "cp",
"version": "4.0.0.102",
"vendor": "aws.snowflake",
"datastore":"SAMPLE_POLICY",
"pcc_version": "4.0.0.9",
"core_version": "2.1.4+0.g93016.2.1",
"lambda_version":"4.0.1"
},
"signature": {
"key_id": "95f5a194-b0a4-4351-a",
"checksum": "AF09217C56944D91C47847A77C0367C594C0B948E7E75654B889571BD4F60A71"
}
}
3.7 - No Access Behavior
No Access Behavior
The security policy maintains a No Access Operation, configured in an ESA, which determines the response for unauthorized unprotect requests.
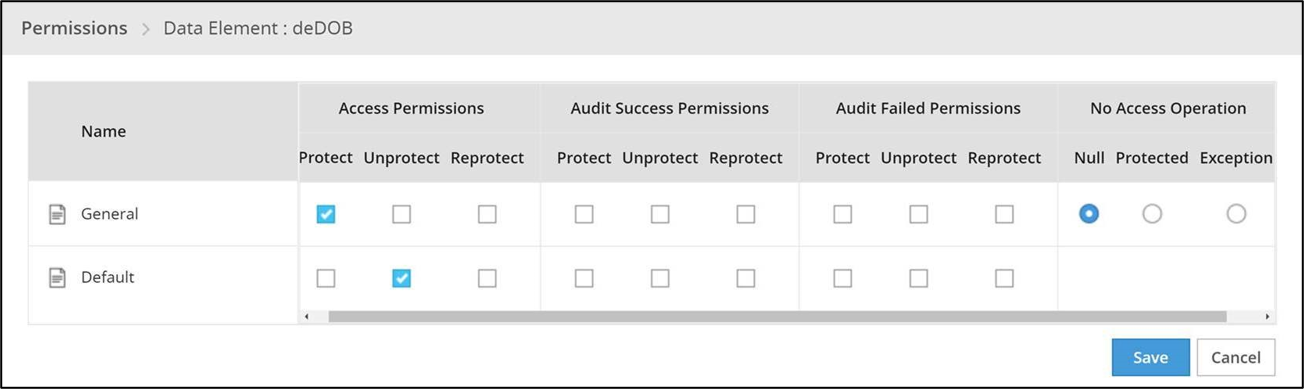
The following table describes the result returned in the response for the various no access unprotect permissions.
| No Access Operation | Data Returned |
|---|---|
| Null | null |
| Protected | (protected value) |
| Exception | Query will fail with an exception |
Note
An unauthorized protect will throw an exception.3.8 - Known Limitations
Known Limitations
Known product limitations:
- FPE is supported only for ASCII values.
- Only the protect and unprotect operations are supported. The reprotect operation is not currently supported.
- The BIGINT data types are not protected/unprotected accurately. Use String instead.
- The FLOAT8 (8-byte float) data type is not supported. Use String instead.
- The timestamp data type is not supported.
3.9 - Upgrading To The Latest Version
Download the Latest Version
You can download the latest version of the deployment package from https://my.protegrity.com. Navigate to Data Protection > Cloud Protect to download the latest version.
After downloading the deployment package from the Protegrity Portal, unzip the package to extract the artifact files. In the AWS Console, navigate to the S3 bucket that was previously created to upload deployment artifacts (see: Create S3 bucket for Installing Artifacts).
Note
Only extract the deployment package and not the files in it.Upload the following artifacts to the S3 bucket:
- -- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
- protegrity-athena-protect-udfs-<version>.jar
- protegrity-external-extension-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-sample-policy-<version>.zip
If the release version matches your existing deployment, you don’t need to upload it again. Save the following artifacts on your local system so that you have them available during the next steps:
- -- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_cf.json
- pty_agent_cf.json
- pty_protect_api_cf.json
- pty_agent_cf.json
- pty_log_forwarder_cf.json
- pty_athena_protect_cf.json
- pty_agent_cf.json
Perform the following steps to upgrade the Agent Lambda and Protect Lambda separately.
Important
If new versions are available for both Agent and Protect Lambdas, Agent Lambda must be upgraded first.Disable Protegrity Agent Function CloudWatch Event Rule
Cloud Watch Event Rule is used to periodically run Protegrity Agent Function to synchronize policy from ESA. This functionality is optional when deploying Protegrity Serverless Solution. If the Event Rule is enabled, it must be disabled temporarily for the time of the upgrade process.
Follow the steps below to determine if your deployment uses Event Rule and disable it.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Resources tab from the top portion of the screen.
Check if there is a resource with ScheduledRule LogicalID. If there is no such resource you can skip to Upgrading Policy Agent Lambda section. If the scheduled rule is there, continue with the next steps in this section.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Disable from the top-right portion of the screen. This will disable the rule. You will re-enable it after the upgrade process is complete.
Upgrading Policy Agent Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Agent Lambda upgrade.Go to AWS Lambda console and select existing Protegrity Agent Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish. The version of Agent Lambda you just created will serve as restore point in the case you needed to rollback the upgrade.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonGo to AWS Cloud Formation and select existing Protegrity Agent deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_agent_cf.json file and select Next.
Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Navigate back to Agent Lambda Function.
Note
Make sure you are viewing the latest Lambda Function, not the published version.Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current agent installation version is lower than 3.0.12, make sure you set the following function configuration variables:
- PTY_ADDIPADDRESSHEADER
- PTY_ESA_CA_SERVER_CERT You can read more about these variables in section Policy Agent Lambda Configuration.
If you are upgrading from versions prior to v3.0, backup and remove existing policy from the bucket defined by AWS_POLICY_S3_BUCKET property, so that the policy can be re-downloaded and re-encrypted with new ‘key commitment’ feature.
If you are upgrading from version prior to 1.6.1 please follow the steps below, otherwise the upgrade process is completed.
From AWS Console, navigate to IAM > Policies
Search for the Agent Lambda IAM Policy created in Create Agent Lambda IAM policy
Click on the policy, then select Edit Policy. Select JSON tab.
Add the following statement to the list of policy statements.
{ "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }Click Review Policy, then Save Changes. Wait for the changes to save.
Upgrading Log Forwarder Lambda
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], skip this section and follow instruction to install new Log Forwarder Audit Log Forwarder Installation.Publish Log Forwarder Lambda Version
Publishing a version of the Log Forwarder Lambda allows to roll-back to pre-existing version if upgrade fails
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Click Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Log Forwarder Lambda version number for roll-backs: ___________________
Disable Kinesis Trigger
Disabling Kinesis trigger ensures there are no unprocessed or re-processed events while function is upgraded.
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Uncheck Activate trigger and click Save
- Wait for function to stop processing events by monitoring function in Monitor tab
Upgrade Forwarder Lambda Version
Upgrade Log Forwarder function with new code
- Go to AWS Cloud Formation and select existing Protegrity Log Forwarder deployment stack.
- Select Update Stack > Make a direct update.
- Select Replace existing template > Upload a template file.
- Upload pty_log_forwarder_cf file and select Next.
- Click Next until Review window and then select Update stack.
- Wait for the Cloud Formation to complete.
Enable Kinesis Trigger
- Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
- Select Configuration tab > Triggers
- Check Kinesis trigger and click Edit button
- Check Activate trigger and click Save Log Forwarder function will now start processing events from where it left off when Kinesis trigger was disabled.
Monitor and roll-back
Monitor Log Forwarder function for errors in its CloudWatch logs and in Montior tab. To roll back function to the previous version if any errors occur follow these steps:
Go to AWS Lambda console and select existing Protegrity Log Forwarder Lambda.
Select Configuration tab > Triggers
Expand Details section of Kinesis trigger and record UUID value
Execute the following AWS CLI command to move Kinesis trigger to previous version of Log Forwarder Lambda that was created earlier and recorded as Log Forwarder Lambda version number for roll-backs. Substitute kinesis-mapping-uuid, log-forwarder-function-name, version-for-roll-backs with your values:
aws lambda update-event-source-mapping --uuid <kinesis-mapping-uuid> --function-name <log-forwarder-function-name>:<version-for-roll-backs>Find Kinesis trigger attached to previous version of Log Forwarder Lambda by navigating Versions tab > Version number link in the Versions column Kinesis trigger is now moved to previous version of Log Forwarder Lambda function.
Upgrading Protect Lambda
Note
If the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Diagram below illustrates upgrade steps.
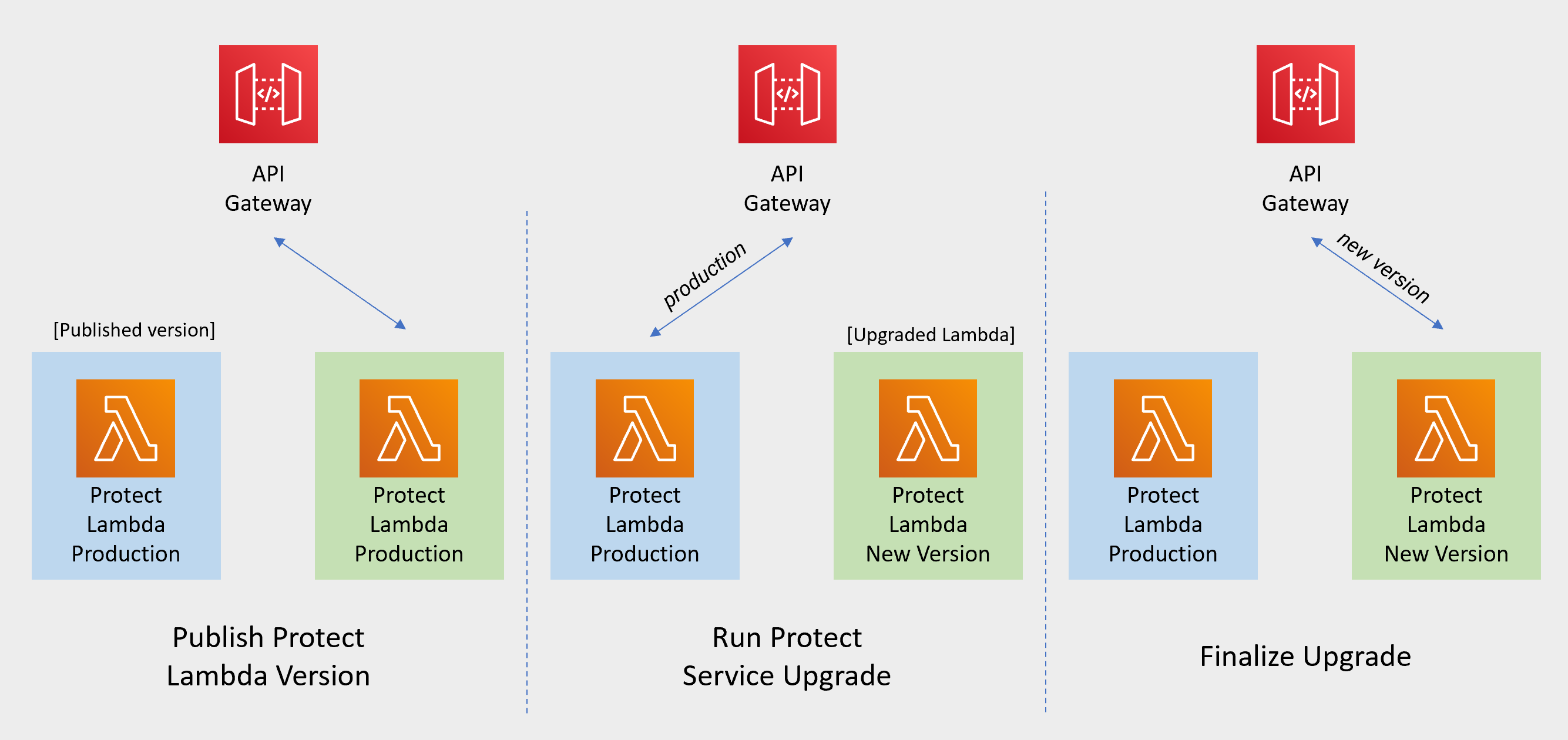
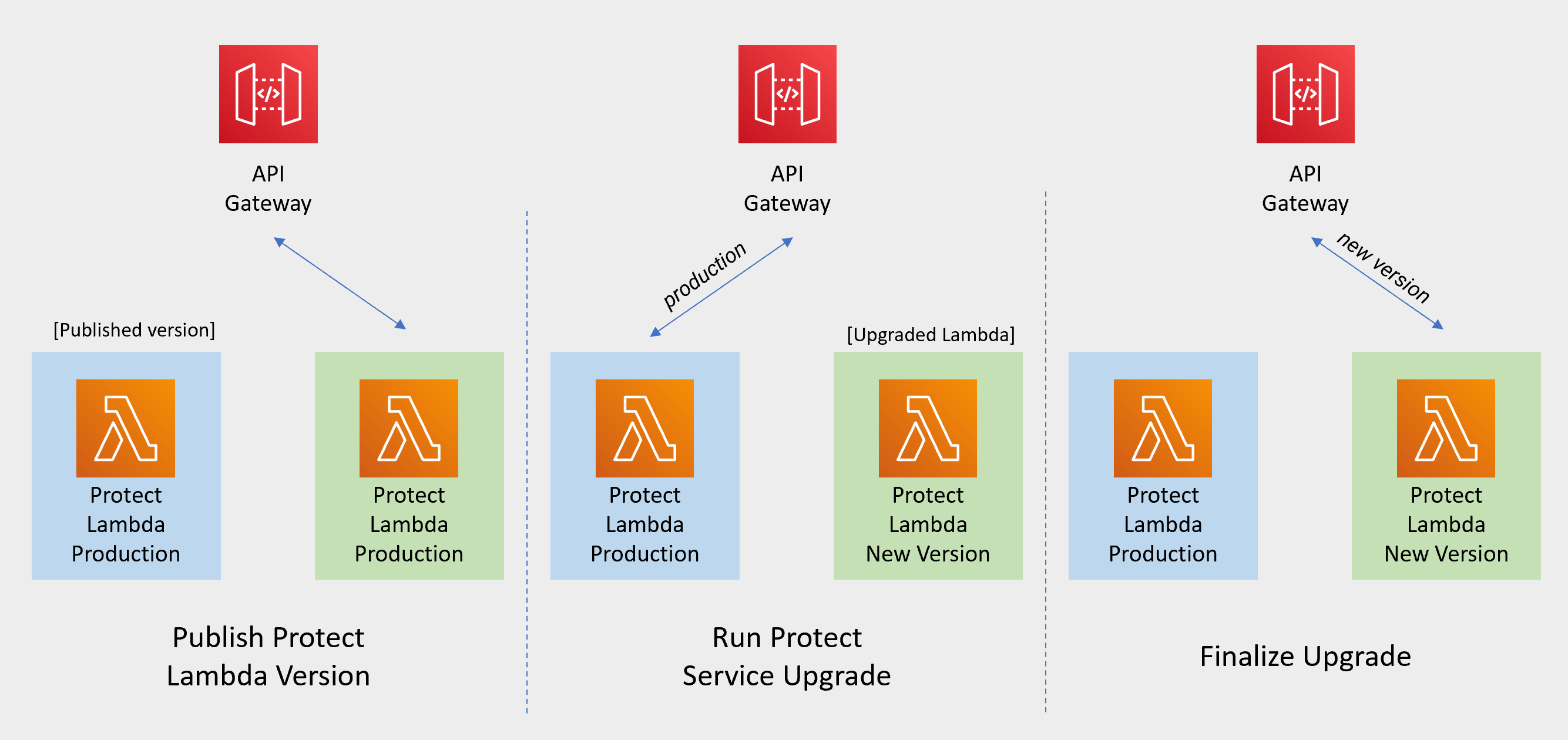
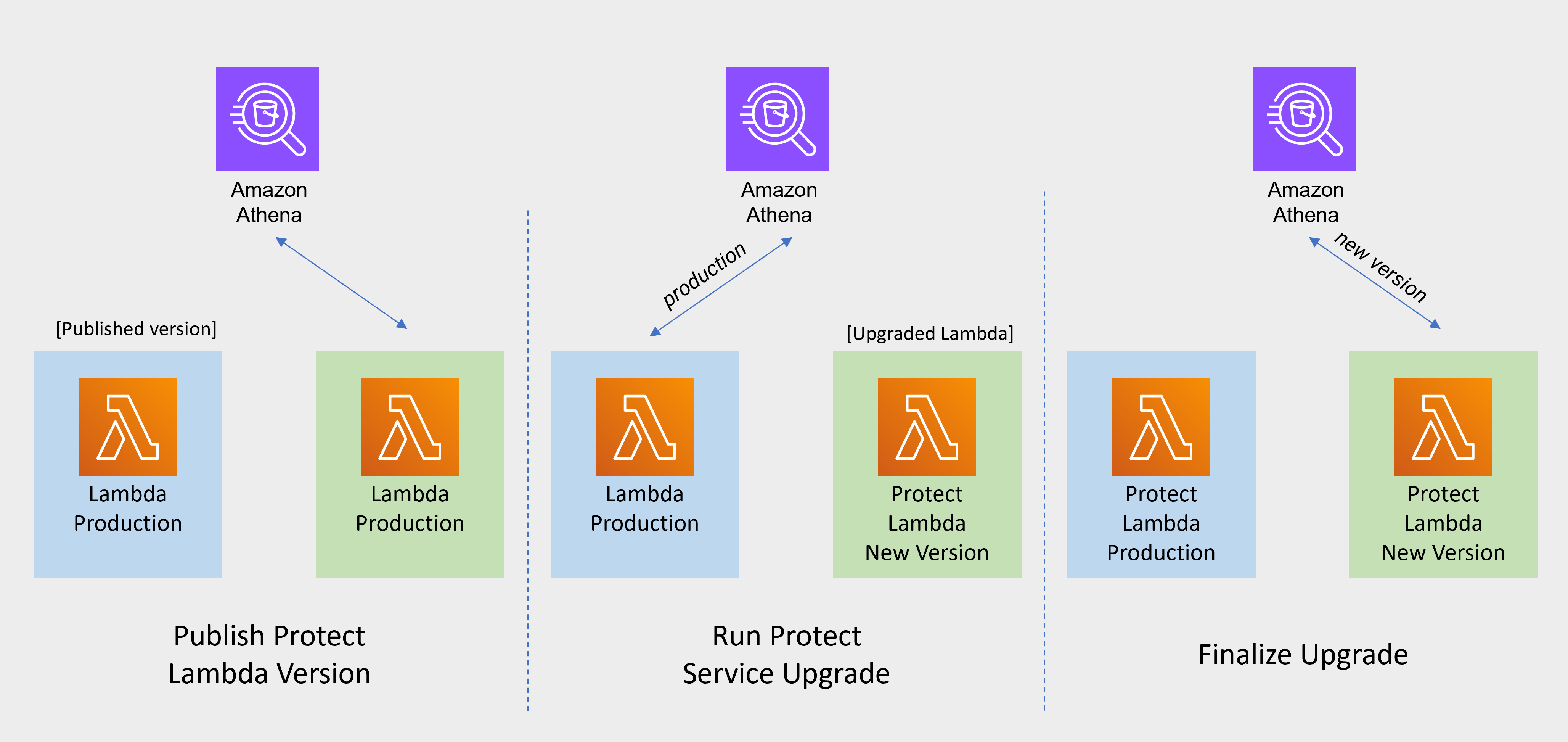
Publish Protect Lambda Version
Publishing a version of the Protect Lambda allows updating it without interruptions to the existing traffic.
Go to AWS Lambda console and select existing Protegrity Protect Lambda.
Go to Lambda Configuration > Environment variables.
Record environment variables values. You will use them later to configure upgraded Lambda Function. You can use the aws cli command below to save the function variables into the local json file:
aws lambda get-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --query Environment > <function_name>_env_config.jsonClick Actions in top right portion of the screen. Select Publish new version. Click Publish.
Record the Lambda version number. It will be displayed at the top of the screen. You can also retrieve it from the Lambda function view, under Versions tab.
Protect Lambda version number: ___________________
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:<protect_lambda_version_number>' iam_role 'arn:aws:iam::123456789212:role/example_role';
Run protect service upgrade
In this step, the Protect service including Lambda $LATEST version will be updated using Cloud Formation template. The Lambda version created in previous step will be used to serve existing traffic during the upgrade process.
Go to AWS Cloud Formation and select existing Protegrity deployment stack.
Select Update. Check Replace current template > Upload a template file.
Upload pty_protect_cf.json file and select Next.
Update ProtectFunctionProductionVersion parameter with Protect Lambda version number recorded in step 3.
Note
If you are upgrading protector to one of these versions: [3.2.2, 3.2.3], set parameter KinesisLogStreamArn to the output value recorded in Install through CloudFormation for the newly deployed log forwarder.Click Next until Review window and then select Update stack.
Wait for the Cloud Formation to complete.
Go back to Lambda console and select Protect Lambda.
Go to Configuration > Environment variables. Replace placeholder values with values recorded in previous step. Alternatively, you can run the following aws cli command to update function configuration using json file saved in the previous steps:
aws lambda update-function-configuration --function-name \ arn:aws:lambda:<aws_region>:<aws_account>:function:<function_name> \ --environment file://./<function_name>_env_config.jsonNote
If your current protect installation version is lower than 3.0.14, you can optionally set the following variable:
- LOG_REDSHIFT_CLUSTER_ARN You can read more about this configuration in section Protect Lambda Configuration.
Navigate to Aliases tab. Verify that Production alias points to the lambda version you specified in the cloud formation template.
The upgraded Protect Lambda is configured with a sample policy. Run Agent Lambda Function before continuing with next steps.
Finalize upgrade
In this step, the Protect Lambda will be configured to serve traffic using $LATEST version upgraded in the previous step.
Go back to Protegrity AWS Cloud Formation deployment stack.
Select Update. Check Use Current template.
Update ProtectFunctionProductionVersion parameter with the following value: $LATEST.
Click Next until Review window and then select Update stack.
Go back to Lambda console and select Protect Lambda.
From the Lambda console, verify that Latest alias points to $LATEST version.
Test your function to make sure it works as expected.
If you are upgrading a Cloud Protect Redshift version 1.x to 2.x/3x, you must recreate your Redshift external function definitions with Protect Lambda Function version appended to the Lambda Function name. See example below.
CREATE OR REPLACE EXTERNAL FUNCTION PTY_PROTECT_TEST ( val varchar ) RETURNS varchar VOLATILE lambda 'Protegrity_Protect_test:Production' iam_role 'arn:aws:iam::123456789212:role/example_role';If you need to rollback to older version of Protect Lambda, you can re-run the cloud formation with ProtectFunctionProductionVersion parameter set to the previous version of Protect Lambda.
Re-enable Protegrity Agent Function CloudWatch Event Rule
If the Event Rule was disabled at the beginning of the upgrade process, you must re-enabled it. Follow the steps below to re-enable Policy Agent Event rule.
Go to the Protegrity Agent Cloud Formation Stack.
Select Resources tab from the top portion of the screen.
Click on the Physical ID link in the ScheduledRule row. The link opens Policy Agent Event Rule configuration.
Select Enable from the top-right portion of the screen. This will enable the rule. You will re-enable it after the upgrade process is complete.
3.10 - Appendices
3.10.1 - Installing the Policy Agent and Protector in Different AWS Accounts
The Policy Agent Lambda function and Protect Lambda functions can be installed in separate AWS accounts. However, additional configuration is required to authorize the Policy Agent to provision the security policy to a remote Protect Lambda function.
Note
The Policy Agent will deploy an encrypted security policy file to an S3 bucket in the Protect function’s AWS Account.Create Agent Lambda IAM policy
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following snippet.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "LambdaUpdateFunction", "Effect": "Allow", "Action": [ "lambda:UpdateFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] }, { "Sid": "LambdaReadLayerVersion", "Effect": "Allow", "Action": [ "lambda:GetLayerVersion", "lambda:ListLayerVersions" ], "Resource": "*" }, { "Sid": "LambdaDeleteLayerVersion", "Effect": "Allow", "Action": "lambda:DeleteLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*:*" }, { "Sid": "LambdaPublishLayerVersion", "Effect": "Allow", "Action": "lambda:PublishLayerVersion", "Resource": "arn:aws:lambda:*:*:layer:*" }, { "Sid": "S3GetObject", "Effect": "Allow", "Action": [ "s3:GetObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "S3PutObject", "Effect": "Allow", "Action": [ "s3:PutObject" ], "Resource": "arn:aws:s3:::*/*" }, { "Sid": "LambdaGetConfiguration", "Effect": "Allow", "Action": [ "lambda:GetFunctionConfiguration" ], "Resource": [ "arn:aws:lambda:*:*:function:*" ] } ] }Replace the wildcards (*) with the region, account, and resource name information where required.
Select Review policy, type in the policy name, and confirm. Record policy name:
Agent Lambda Cross Account Policy Name: ___________________
Create Policy Agent cross-account IAM Role
Login to the AWS account that hosts the Protect Lambda function.
From the AWS IAM console, select Roles > Create Role
Select AWS Service > Lambda . Proceed to Permissions.
Select Policy created in the step above. Proceed to Tags.
Specify Tag, proceed to the final screen. Type in policy name and confirm. Record the name.
Policy Agent Cross Account IAM Role Name: ___________________
Allow the Policy Agent Cross-Account Role to be Assumed by the Policy Agent IAM Role
Login to the AWS account that hosts the Protect Lambda function.
Navigate to the previously created IAM Role (Agent Lambda Cross-Account IAM Role Name).
Navigate to Trust Relationships > Edit Trust Relationships.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda IAM Execution Role ARN> with ARN of Agent Lambda IAM Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Click Update Trust Policy.
Add Assume Role to the Policy Agent Execution IAM Role
Login to the AWS account that hosts the Policy Agent.
Navigate to the Agent Lambda IAM Execution Role that was created in Agent Installation.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<Agent Lambda IAM Execution Role Name>" }, "Action": "sts:AssumeRole" } ] }Add Inline Policy.
Modify the Policy Document, replacing the placeholder value indicated in the following snippet as <Agent Lambda Cross-Account IAM ARN> with the value recorded in Create Policy Agent cross-account IAM Role.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "sts:AssumeRole" ], "Resource": "<Agent Lambda Cross-Account IAM ARN>." } ] }When you are finished, choose Review Policy.
On the Review policy page, type a Name, then choose Create Policy.
Update the Policy Agent Lambda Configuration
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select Configuration tab | Environment variables.
Select Edit and add the following environment variables with the value from Agent Lambda Cross-Account IAM ARN:
Parameter Value AWS_ASSUME_ROLE Agent Lambda Cross-Account IAM ARN Ensure the values in the Parameters AWS_POLICY_S3_BUCKET, AWS_PROTECT_FN_NAME and AWS_POLICY_LAYER_NAME are all in the Protect Lambda Function AWS Account.
In case custom VPC hostname configuration is used, you will need to set the ENDPOINT_URL. Refer to Policy Agent - Custom VPC Endpoint Hostname Configuration.
AWS_VPC_ENDPOINT_URL
<AWS_VPC_ENDPOINT>
Click Save and Run the Lambda. The Lambda will now assume the Role in Protect Lambda Function AWS Account and update the policy cross accounts.
3.10.2 - Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)
This guide describes how to configure the Protegrity Policy Agent and Log Forwarder to connect to a Protegrity Provisioned Cluster (PPC), highlighting the differences from connecting to ESA.
Key Differences: PPC vs ESA
| Feature | ESA 10.2 | PPC (this guide) |
|---|---|---|
| Datastore Key Fingerprint | Optional/Recommended | Required |
| CA Certificate on Agent | Optional/Recommended | Optional/Recommended |
| CA Certificate on Log Forwarder | Optional/Recommended | Not supported |
| Client Certificate Authentication from Log Forwarder | Optional/Recommended | Not supported |
| IP Address | ESA IP address | PPC address |
Prerequisites
- Access to PPC and required credentials.
- Tools:
curl,kubectlinstalled.
Policy Agent Setup with PPC
Important
When connecting to PPC, the Policy Agent requires thePTY_DATASTORE_KEY fingerprint. For ESA 10.2, the fingerprint is optional but recommended. See Policy Agent Installation for general setup steps.Follow these instructions as a guide for understanding specific inputs for Policy Agent integrating with PPC:
Obtain the Datastore Key Fingerprint
To retrieve the fingerprint for your Policy Agent:
curl -k -H "Authorization: Bearer ${TOKEN}" -X POST https://${HOST}/pty/v2/pim/datastores/1/export/keys -H "Content-Type: application/json" --data '{ "algorithm": "RSA-OAEP-256", "description": "example-key-from-kms", "pem": "-----BEGIN PUBLIC KEY-----\nABC123... ...890XYZ\n-----END PUBLIC KEY-----" }'Sample Output:
{"uid":"1","algorithm":"RSA-OAEP-256","fingerprint":"4c:46:d8:05:35:2e:eb:39:4d:39:8e:6f:28:c3:ab:d3:bc:9e:7a:cb:95:cb:b1:8e:b5:90:21:0f:d3:2c:0b:27","description":"example-key-from-kms"}Record the
fingerprintvalue and configure it as thePTY_DATASTORE_KEYfor the Policy Agent.Retrieve the PPC CA Certificate
To obtain the CA certificate from PPC:
kubectl -n api-gateway get secret ingress-certificate-secret -o jsonpath='{.data.ca\.crt}' | base64 -d > CA.pemUse the
CA.pemthat was returned as described in Policy Agent Installation.Configure the PPC Address
Use the PPC address in place of the ESA IP address wherever required in your configuration.
Log Forwarder Setup with PPC
Note
When using PPC, certificate authentication and CA validation are not supported for the Log Forwarder. Configuration steps related to certificates in Log Forwarder Installation do not apply to PPC. If you attempt to use certificates provided by PPC, the Log Forwarder will not function correctly.- The Log Forwarder will proceed without certificates and will print a warning if
PtyEsaCaServerCertandPtyEsaClientCertificatesSecretIdare not provided. - No additional certificate or CA configuration is needed for PPC.
Troubleshooting
Protector Lambda fails with “AWS KMS Decrypt failed”
Symptom:
After a successful Policy Agent run and layer update, the Protector Lambda returns:
{
"body": "{\"error_msg\":\"Failed to open decoder: rpdecode decrypt failure: dek callback failed: AWS KMS Decrypt failed: \",\"success\":false}",
"isBase64Encoded": false,
"statusCode": 400
}
The Protector Lambda logs show:
[SEVERE] [utils.cpp:185] AWS KMS Decrypt failed:
Cause:
The public key configured in the PPC/ESA datastore does not match the KMS key pair used by the Policy Agent. The policy package is encrypted with the public key stored in the datastore. If that key does not correspond to the KMS key pair whose private key is used for decryption, the Protector Lambda will fail to decrypt the policy.
Resolution:
- Identify the KMS key pair used by the Policy Agent (the key ARN configured during pre-configuration).
- Export the public key from that KMS key pair.
- In PPC/ESA, ensure the datastore’s export key is configured with the public key from that same KMS key pair. See Obtain the Datastore Key Fingerprint above.
- Re-run the Policy Agent to generate a new policy package encrypted with the correct key.
- Test the Protector Lambda again.
Important
Always verify that the public key registered in the PPC/ESA datastore belongs to the same KMS key pair referenced by the Policy Agent. A mismatch between these keys is a common cause of AWS KMS Decrypt failed errors.
The KMS key must be an asymmetric key with the Encrypt and decrypt key usage type. Symmetric keys or asymmetric keys configured for signing will not work.
Additional Notes
- For troubleshooting, consult the Protegrity Documentation.
3.10.3 - Policy Agent - Custom VPC Endpoint Hostname Configuration
The Policy Agent uses default endpoint hostnames to communicate with other AWS services (for example, secretsmanager.amazonaws.com). This configuration will only work in VPCs where Amazon-provided DNS is available (default VPC configuration with private DNS option enabled for the endpoint). If your VPC uses custom DNS, follow the instructions below to configure the Policy Agent Lambda to use custom endpoint hostnames.
Note
This configuration is only available with the Cloud Protect version 1.5.0 or higher. For more information about the upgrade instructions, refer to Upgrading to the Latest Version.Identify DNS Hostnames
To identify DNS hostnames:
From AWS console, select VPC > Endpoints.
Select Secrets Manager endpoint from the list of endpoints.
Under Details > DNS Names, note the private endpoint DNS names adding https:// at the beginning of the endpoint name.
For example, https://vpce-1234-4pzomrye.kms.us-west-1.vpce.amazonaws.com
Note down DNS names for the KMS and Lambda endpoints:
AWS_SECRETSMANAGER_ENDPOINT: https://_________________
AWS_KMS_ENDPOINT: https://_________________
AWS_LAMBDA_ENDPOINT: https://_________________
Update the Policy Agent Lambda configuration
To update policy agent lambda configuration:
From the AWS console, navigate to Lambda, and select the Policy Agent Lambda function.
Select the Configuration section and choose Environment variables.
Select Edit and add the following environment variables with the corresponding endpoint URLs recorded in steps 3-4:
Parameters Value AWS_SECRETSMANAGER_ENDPOINT_URL <AWS_SECRETS_ENDPOINT> AWS_KMS_ENDPOINT_URL <AWS KMS ENDPOINT> AWS_LAMBDA_ENDPOINT_URL <AWS LAMBDA ENDPOINT> Click Save and Run the Lambda. The Lambda will now use endpoints you have just configured.
3.10.4 - Redshift Cross-Account Configuration
Cross-Account Configuration
Important
These steps are only required IF the Protegrity solution is installed in a separate AWS account from the Amazon Redshift cluster.The following figure illustrates the Protegrity Redshift Integration architecture when Protegrity Solution is installed on separate from Amazon Redshift Cluster Account.
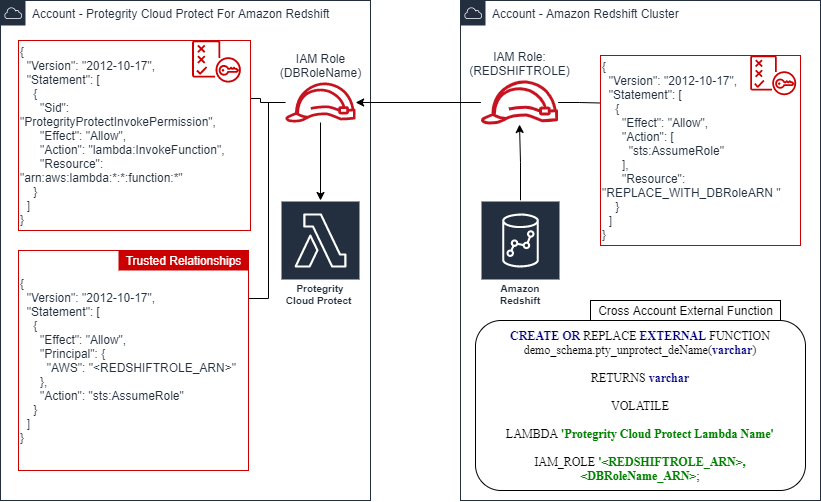
Redshift Account IAM Configuration
This step creates Redshift IAM role with permissions to assume role in separate account.
Create Redshift IAM policy:
Login to the AWS account that hosts the Amazon Redshift cluster.
In the AWS console, access Services > IAM and click Policies.
Click Create Policy.
Select the JSON tab and paste the following JSON snippet:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "sts:AssumeRole" ], "Resource": "<DBRoleARN>" } ] }Replace the resource value with DBRoleARN recorded in Create IAM Account Role
Click Review policy to continue.
Enter a name for the policy.
Click Create Policy.
Record the policy name.
Redshift IAM Policy Name: ___________________
Create Redshift IAM Role
This step creates Redshift IAM role with permissions to assume role in separate account.
Create Redshift IAM Role:
Login to the AWS account that hosts the Amazon Redshift cluster.
In the AWS console, access Services > IAM and click Roles.
Click Create Role.
Select AWS Service as the trusted entity type, then select Redshift use case from the list of services.
Select Redshift – Customizable from the use case section.
Continue by clicking Next:Permissions.
Filter the list and search for the policy recorded in the step above (Redshift IAM Policy Name).
Click the Next:Tags button to continue to the next step.
Click the Next:Review button to continue.
Enter a role name, such as Redshift2ProtegrityRole.
Click Create Role.
Record role ARN:
RedshiftIAMRoleARN: ____________________
Attach IAM Role to Redshift Cluster
This step creates Redshift IAM role with permissions to assume role in separate account.
Attach IAM role to the Redshift cluster:
Login to AWS Console.
Access Amazon Redshift and select your cluster.
Select Properties > Cluster Permissions > Manage IAM Roles.
Select RedshiftIAMRoleARN configured in the step above and click Associate IAM role.
Save the changes.
After saving the changes it may take couple of minutes until the cluster IAM role is fully configured.
You can check configuration status by navigating back to the cluster IAM role settings.
The status field next to the IAM role will show in-sync once the role is configured.
Defining Redshift External Functions
The external function for cross-account differs slightly from the reference material in this document. The function requires two roles to be specified. The following is an example of the modified function definition.
CREATE OR REPLACE EXTERNAL FUNCTION demo_schema.pty_unprotect_deName(varchar)
RETURNS varchar
VOLATILE
LAMBDA 'ProtectFunctionProductionAlias'
IAM_ROLE '<RedshiftIAMRoleARN>,<DBRoleARN>;
Replace <ProtectFunctionProductionAlias> with the value recorded in Install through CloudFormation Replace <RedshiftIAMRoleARN> with the value recorded in Create Redshift IAM Role Replace <DBRoleARN> with the value recorded in Create IAM Account Role
3.10.5 - Sample Redshift External Function
Sample Redshift External Function
Method: Tokenization | ||
Type: ALPHA | ||
| ||
Redshift Data Types | Redshift Max Size | Protegrity Max Size |
VARCHAR | 4K (4,096 bytes) | 4K (4,096 bytes) |
CHAR | ||
| ||
| ||
| ||
External Function Sample Definitions: | ||
| ||
| ||
Sample EF Calls: | ||
| ||
| ||
| ||
| ||
Method: Tokenization | ||
Type: NUMERIC | ||
| ||
Redshift Data Types | Redshift Max Size | Protegrity Max Size |
DECIMAL | 4K (4,096 bytes) | 4K (4,096 bytes) |
INTEGER | ||
BIGINT | ||
| ||
| ||
External Function Sample Definitions: | ||
| ||
| ||
Sample EF Calls: | ||
| ||
| ||
3.10.6 - Configuring Regular Expression to Extract Policy Username
Configuring Regular Expression to Extract Policy Username
Cloud Protect Lambda Function exposes USERNAME_REGEX configuration to allow extraction of policy username from user in the request.
USERNAME_REGEX Lambda Environment configuration
The USERNAME_REGEX configuration can be used to extract policy username from user in the request. The following are allowed values for USERNAME_REGEX:
1 - Default build-in regular expression is used:
^arn:aws:(?:iam|sts)::[0-9]{12}:(?:role|user|group|assumed\-role|federated\-user)\/([\w\/+=,.\-]{1,1024}|[\w\/+=,.\-@]{1,1024})(?:@[a-zA-Z0-9\-]{1,320}(?:\.\w+)+)?$^User regex$ - Custom regex with one capturing group. This group is used to extract the username. Examples below show different regular expression values and the resulting policy user.
USERNAME_REGEX | User in the request | Effective Policy User |
|---|---|---|
Not Set | arn:aws:iam::123456789012:user/juliet.snow | arn:aws:iam::123456789012:user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | arn:aws:sts::123456789012:assumed-role/TestSaml | |
1 | arn:aws:iam::123456789012:user/juliet.snow | juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | TestSaml | |
| arn:aws:iam::123456789012:user/juliet.snow | user/juliet.snow |
arn:aws:sts::123456789012:assumed-role/TestSaml | assumed-role/TestSaml |
3.10.7 - Associating ESA Data Store With Cloud Protect Agent
Associating ESA Data Store With Cloud Protect Agent
ESA controls which policy is deployed to protector using concept of data store. A data store may contain a list of IP addresses identifying servers allowed to pull the policy associated with that specific data store. Data store may also be defined as default data store, which allows any server to pull the policy, provided it does not belong to any other data stores. Node registration occurs when the policy server (in this case the policy agent) makes a policy request to ESA, where the agent’s IP address is identified by ESA.
Note
For more information about ESA data store refer to Policy Management Guide which is part of Protegrity ESA documentation.Policy agent lambda source IP address used for node registration on ESA depends on ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP and the PTY_ADDIPADDRESSHEADER configuration exposed by the agent lambda.
The Lambda service uses multiple network interfaces, internal network interface with ephemeral IP range of 169.254.x.x and external network interface with IP range of the VPC subnet the Lambda is associated with. By default, when agent lambda is contacting ESA to register node for policy download, ESA uses agent Lambda VPC IP address. This default behavior is caused by the default ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP=false and agent default configuration PTY_ADDIPADDRESSHEADER=yes.
In some cases, when there is a proxy server between the ESA and agent lambda, the desirable ESA configuration is ASSIGN_DATASTORE_USING_NODE_IP=true. and PTY_ADDIPADDRESSHEADER=no which will cause the ESA to use proxy server IP address.
The table below shows how the hubcontroller and agent settings will affect node IP registration on ESA.
| Agent source IP | Agent VPC subnet IP | Proxy IP | ESA config - ASSIGN_DATASTORE_USING_NODE_IP | Agent lambda config - PTY_ADDIPADDRESSHEADER | Agent node registration IP |
|---|---|---|---|---|---|
| 169.254.144.81 | 10.1.2.173 | No Proxy | true | yes | 169.254.144.81 |
| true | no | 10.1.2.173 | |||
| false | yes | ||||
| false | no | ||||
| 169.254.144.81 | 10.1.2.173 | 34.230.42.110 | true | yes | 169.254.144.81 |
| true | no | 34.230.42.110 | |||
| false | yes | ||||
| false | no |
4 - Snowflake
This section describes the high-level architecture of the product for integration with Snowflake, the installation procedures, and provides guidance on performance. This section focuses on Protegrity-specific aspects and should be consumed with the corresponding Snowflake documentation.
This guide may also be used with the Protegrity Enterprise Security Administrator Guide, which explains the mechanism for managing the data security policy.
4.1 - Overview
Solution Overview
Snowflake Protector on AWS is a cloud native, serverless product for fine-grained data protection with Snowflake™, a managed Cloud data warehouse. This enables invocation of the Protegrity data protection cryptographic methods from the Snowflake SQL execution context. The benefits of serverless include rapid auto-scaling, performance, low administrative overhead, and reduced infrastructure costs compared to a server-based solution.
This product provides data protection services invoked by External User Defined Functions (UDFs) within Snowflake. The UDFs act as a client transmitting micro-batches of data to the serverless Protegrity Lambda function. User queries may generate hundreds or thousands of parallel requests to perform security operations. Protegrity’s serverless function is designed to scale and yield reliable query performance under such load.
Snowflake Protector on AWS utilizes a data security policy maintained by an Enterprise Security Administrator (ESA), similar to other Protegrity products. Using regular SQL database queries or tools, such as, Tableau™, authorized users can perform de-identification (protect) and re-identification (unprotect) operations on data within the managed Cloud data warehouse. A user’s individual capabilities are subject to privileges and policies defined by the Enterprise Security Administrator.
The following data ingestion patterns are available with your managed Cloud data warehouse:
- Data protection at source applications: In this case, sensitive data is already de-identified (protected) across the enterprise wherever it resides, including the managed data warehouse. Protected data can be ingested directly into your managed Cloud data warehouse. Depending on usage patterns, this ensures that your managed data warehouse is not brought into scope for PCI, PII, GDPR, HIPPA, and other compliance policies.
- Data protection using the Extract-Transform-Load (ETL) pattern: In this case, sensitive data may be transformed with a Protegrity protector either on-premise or in the Cloud before it is ingested into Snowflake.
- Data protection using the Extract-Load-Transform (ELT) pattern: In this case, sensitive data is protected after it lands into the target system typically through a temporary landing table. It uses the native data warehouse’s compute engine with Protegrity to protect incoming data at very high throughput rates. After the data is protected, the intermediate loading tables are dropped as part of the ingestion workflow.
Analytics on Protected Data
Protegrity’s format and length preserving tokenization scheme make it possible to perform analytics directly on protected data. Tokens are join-preserving so protected data can be joined across datasets. Often statistical analytics and machine learning training can be performed without the need to re-identify protected data. However, a user or service account with authorized security policy privileges may re-identify subsets of data using the Snowflake Protector on AWS service.
Features
Snowflake Protector on AWS incorporates Protegrity’s patent-pending vaultless tokenization capabilities into cloud-native serverless technology. Combined with an ESA security policy, the protector provides the following features:
- Role-based access control (RBAC) to protect and unprotect (re-identify) data depending on the user privileges.
- Policy enforcement features of other Protegrity application protectors.
For more information about the available protection options, such as, data types, Tokenization or Encryption types, or length preserving and non-preserving tokens, refer to Protection Methods Reference.
Deployment Architecture
The Protegrity product should be deployed in the customer’s Cloud account within the same AWS region as the Snowflake cluster. The product incorporates Protegrity’s vaultless tokenization engine within an AWS Lambda Function. The encrypted data security policy from an ESA is deployed periodically as a static resource through an AWS Lambda Layer. The policy is decrypted in memory at runtime within the Lambda. This architecture allows Protegrity to be highly available and scale very quickly without direct dependency on any other Protegrity services.
The product exposes a remote data protection service invoked from external User Defined Functions (UDFs), a native feature of specific Cloud databases. The UDFs can be invoked through direct SQL queries or database views. The external UDF makes parallel API calls to the serverless Protegrity Lambda function via the AWS API Gateway to perform protect and unprotect data operations. Each network REST request includes a micro-batch of data to process and a secure context header generated by the database with the username and a Protegrity context header with the data element type, and operation to perform. The product applies the ESA security policy including user authorization and returns a corresponding response. Security operations on sensitive data performed by protector can be audited. The product can be configured to send audit logs to ESA for reporting and alerting purposes via optional component called Log Forwarder explained in details in the next section of this guide.
The security policy is synchronized through another serverless component called the Protegrity Policy Agent. The agent operates on a configurable schedule, fetches the policy from the ESA, performs additional envelope encryption using Amazon KMS, and deploys the policy into the Lambda Layer used by the serverless product. This solution can be configured to automatically provision the static policy or the final step can be performed on-demand by an administrator. The policy takes effect immediately for all new requests. There is no downtime for users during this process.
The following diagram shows the high-level architecture described above.
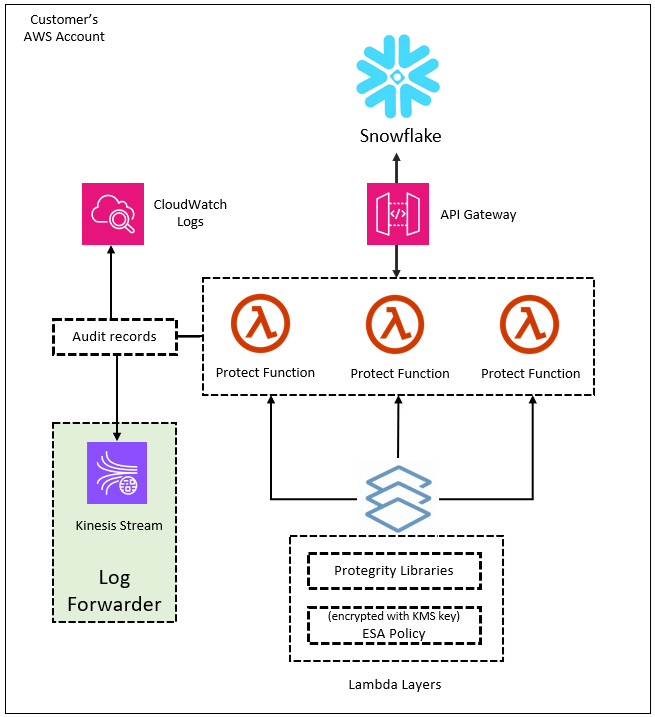
The following diagram shows a reference architecture for synchronizing the security policy from ESA.
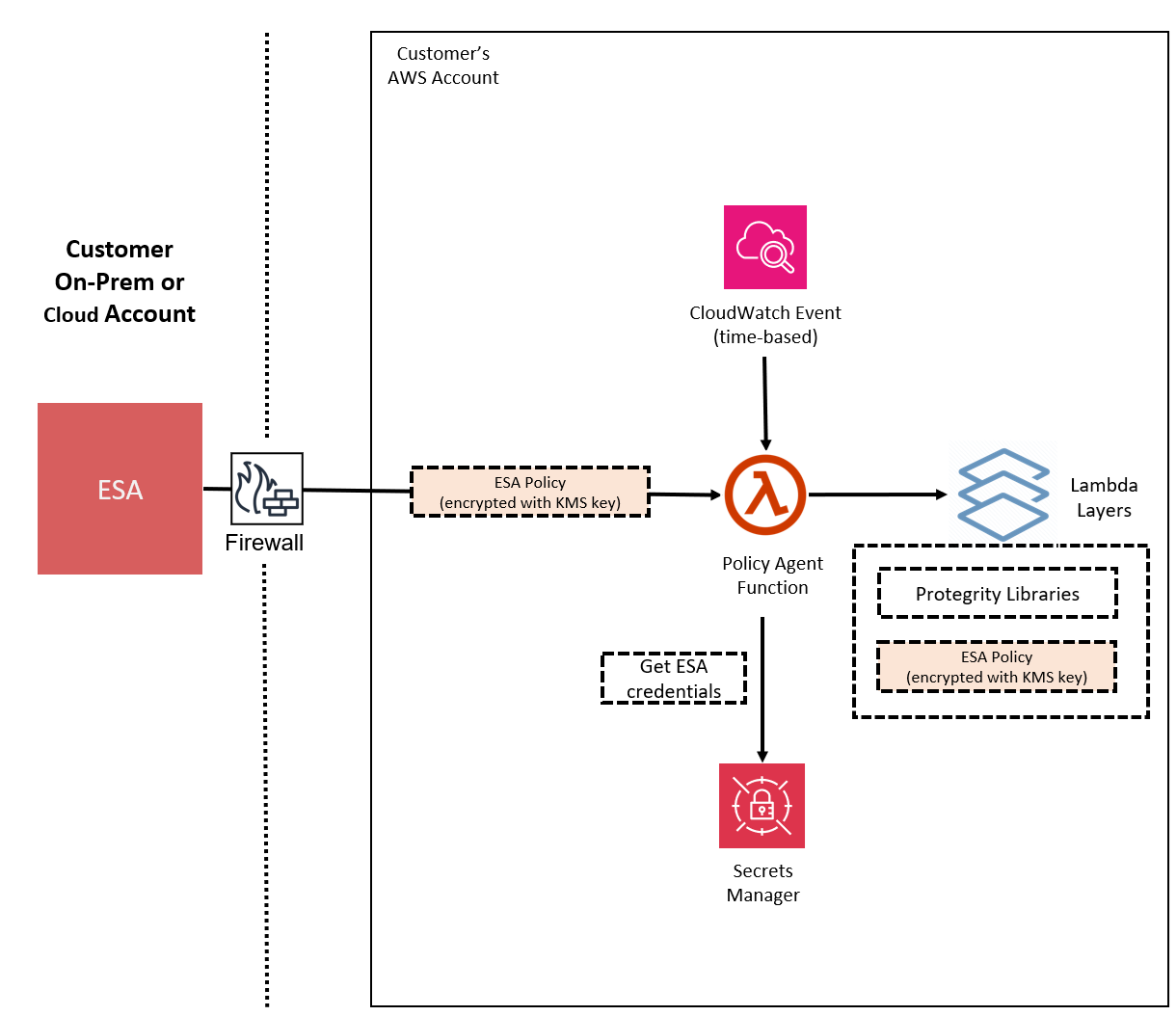
The Protegrity Policy Agent requires network access to an Enterprise Security Administrator (ESA). Most organizations install the ESA on-premise. Therefore, it is recommended that the Policy Agent is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
The ESA is a soft appliance that must be pre-installed on a separate server. It is used to create and manage security policies.
For more information about installing the ESA, and creating and managing policies, refer the Policy Management Guide.
Log Forwarding Architecture
Audit logs are by default sent to CloudWatch as long as the function’s execution role has the necessary permissions. The Protegrity Product can also be configured to send audit logs to ESA. Such configuration requires deploying Log Forwarder component which is available as part of Protegrity Product deployment bundle. The diagram below shows additional resources deployed with Log Forwarder component.
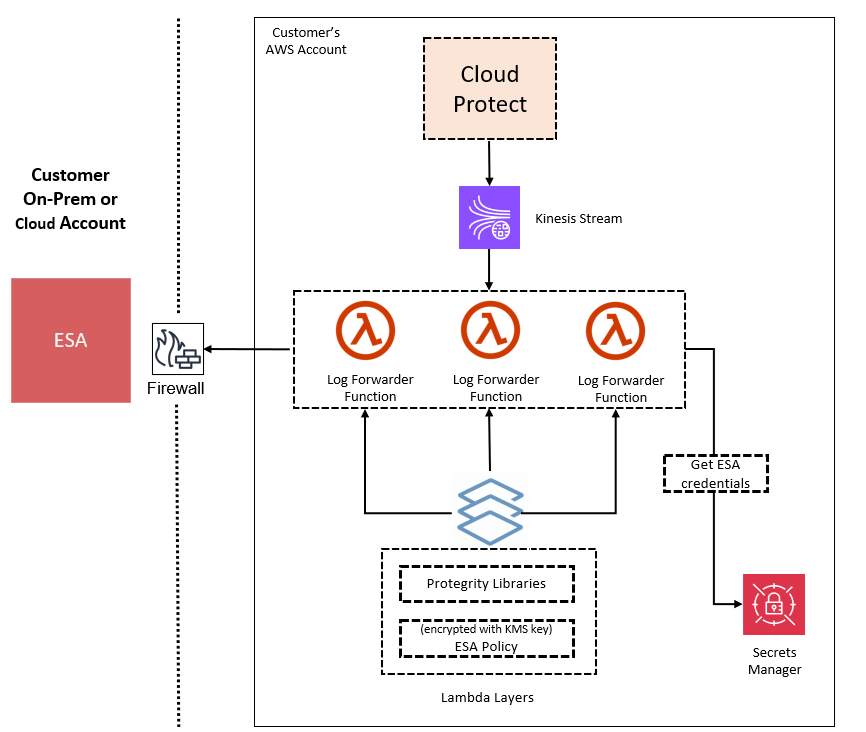
The log forwarder component includes Amazon Kinesis data stream and the forwarder Lambda function. Amazon Kinesis stream is used to batch audit records before sending them to forwarder function, where similar audit logs are aggregated before sending to ESA. Aggregation rules are described in the Protegrity Log Forwarding guide. When the protector function is configured to send audit logs to log forwarder, audit logs are aggregated on the protector function before sending to Amazon Kinesis. Due to specifics of the Lambda runtime lifecycle, audit logs may take up to 15 minutes before being sent to Amazon Kinesis. Protector function exposes configuration to minimize this time which is described in the protector function installation section.
The security of audit logs is ensured by using HTTPS connection on each link of the communication between protector function and ESA. Integrity and authenticity of audit logs is additionally checked on log forwarder which verifies individual logs signature. The signature verification is done upon arrival from Amazon Kinesis before applying aggregation. If signature cannot be verified, the log is forwarded as is to ESA where additional signature verification can be configured. Log forwarder function uses client certificate to authenticate calls to ESA.
To learn more about individual audit log entry structure and purpose of audit logs, refer to Audit Logging section in this document. Installation instructions can be found in Audit Log Forwarder installation.
The audit log forwarding requires network access from the cloud to the ESA. Most organizations install the ESA on-premise. Therefore, it is recommended that the Log Forwarder Function is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall.
Snowflake Connectivity
Request authorization between Snowflake’s AWS VPC to the customer’s AWS API-Gateway occurs using a Snowflake integration enabled by an AWS cross-account IAM role created within the customer’s AWS account. The API Gateway authorizes each request, limiting access to the Snowflake AWS IAM user and external ID established through a Snowflake API Integration object. The following figure illustrates the Protegrity Snowflake Integration architecture.
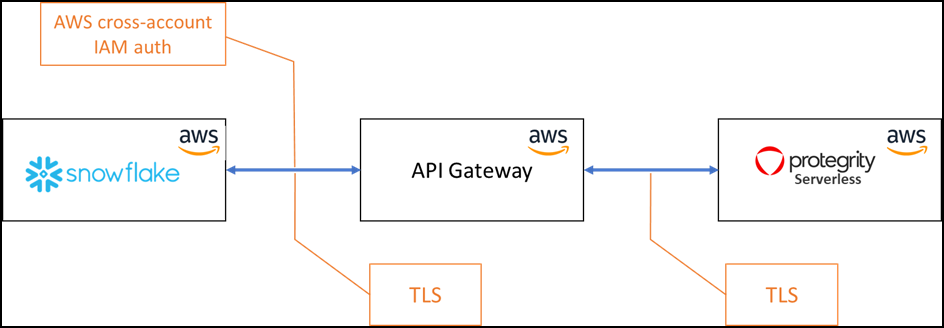
Snowflake’s API Integration Object
The Snowflake API Integration Object provides a connection between your Snowflake VPC and your AWS account where the Protegrity product is hosted. Creating this connection requires setting up the API Gateway and the IAM shared account role. These steps are provided in the installation.
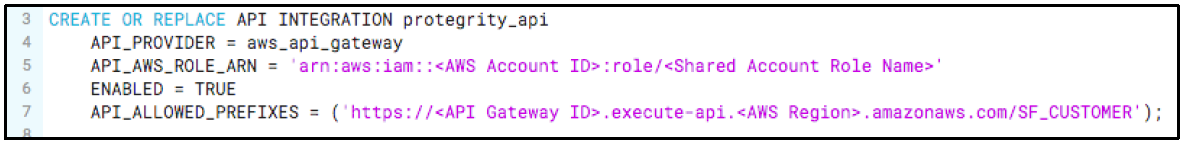
The following figure shows how trust is established between Snowflake and the product.
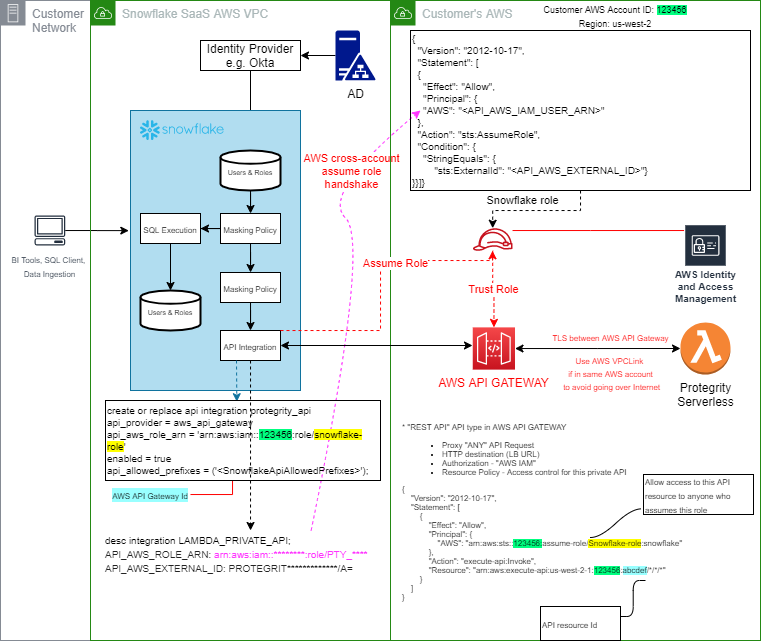
4.2 - Installation
4.2.1 - Pre-Configuration
Determine AWS Region
Query the AWS region where the Snowflake cluster is running. This is the region in which Protegrity Serverless must be installed.
To determine AWS region:
Login to Snowflake
In the SQL console, run the following query.
select current_region();Record the AWS region (e.g. us-east-1).
AWS Region: ___________________
Provide AWS sub-account
Identify or create an AWS account where the Protegrity solution will be installed. It is recommended that a new AWS sub-account be created. This can provide greater security controls and help avoid conflicts with other applications that might impact regional account limits. An individual with the Cloud Administrator role will be required for some subsequent installation steps.
AWS Account ID: ___________________
AWS Region (AwsRegion): ___________________
Create S3 bucket for Installing Artifacts
This S3 bucket will be used for the artifacts required by the CloudFormation installation steps. This S3 bucket must be created in the region that is defined in Provide AWS sub-account
Sign in to the AWS Management Console and open the Amazon S3 console.
Change region to the one determined in Provide AWS sub-account
Click Create Bucket.
Enter a unique bucket name:
For example, protegrity-install.us-west-2.example.com
Upload the installation artifacts to this bucket. Protegrity will provide the following three artifacts:
- protegrity-protect-<version>.zip
- protegrity-agent-<version>.zip
- protegrity-external-extension-<version>.zip
- protegrity-sample-policy-<version>.zip
Important
The deployment package you receive from Protegrity must be extracted to reveal the Protegrity artifacts. CloudFormation requires them in the provided .zip format. Do not extract the individual Protegrity artifacts. Upload these artifacts to the S3 bucket created.
S3 Bucket name (ArtifactS3Bucket): ___________________
Create KMS Key
The Amazon Key Management Service (KMS) provides the ability for the Protegrity Serverless solution to encrypt and decrypt the Protegrity Security Policy.
Note
It is recommended to host the KMS key in a separate AWS sub-account. This allows dual control, separating the responsibility between the key administrator and the Protegrity Serverless account administrator.To create KMS key:
In the AWS sub-account where the KMS key will reside, select the region.
Navigate to Key Management Service > Create Key.
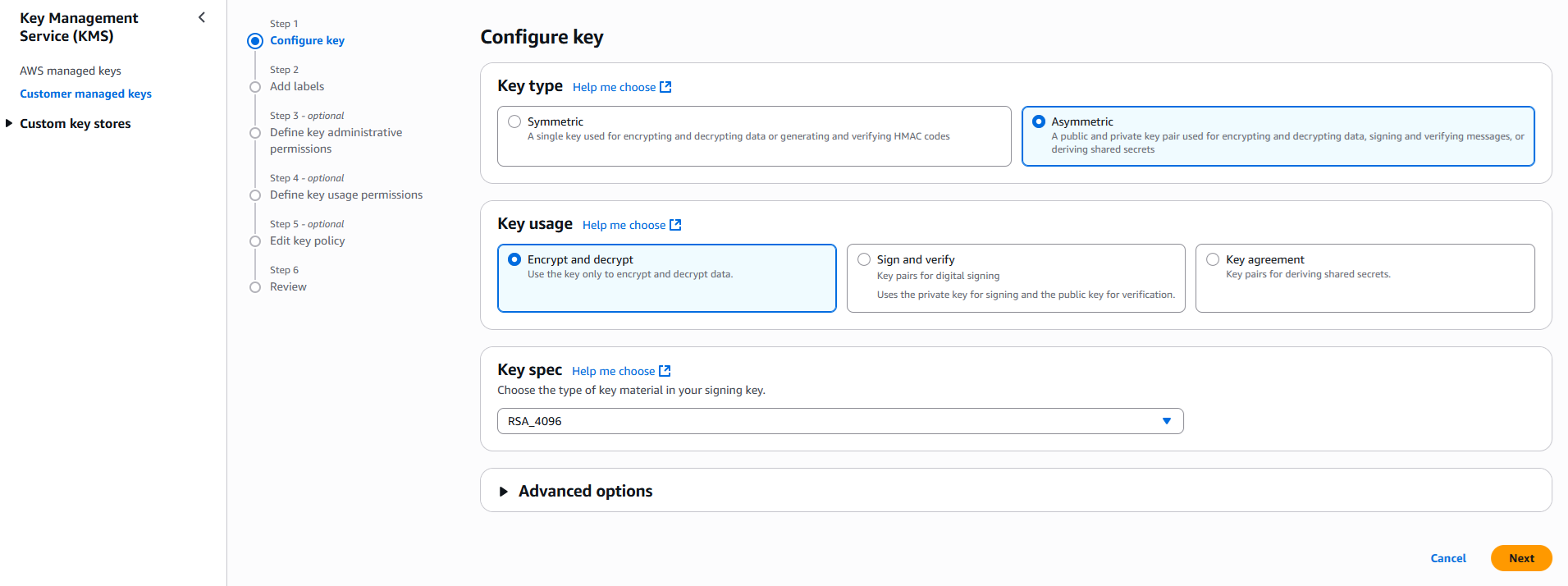
Configure the key settings:
- Key type: Asymmetric
- Key usage: Encrypt and decrypt
- Key spec: RSA_4096
- Click Next
Create alias and optional description, such as, Protegrity-Serverless and click Next.
Define key administrative permissions, the IAM user who will administrate the key.
Note
It is recommended the administrator be different than the administrator of the Protegrity Serverless accountClick Next.
Define the key usage permissions.
In Other AWS accounts, enter the AWS account id used for the Protegrity Serverless installation.
Continue on to create the key. If there is a concern this permission is overly broad, then you can return later to restrict access to the role of two Protegrity Serverless Lambda as principals. Click to open the key in the list and record the ARN.
KMS Key ARN (AWS_KMS_KEY_ID): ___________________
Download the public key from the KMS key. Navigate to the key in KMS console, select the Public key tab, and click Download. Save the PEM file. This public key will be added to the ESA data store as an export key. Refer to Exporting Keys to Datastore for instructions on adding the public key to the data store.
Note
This step is not applicable for ESA versions lower than 10.2.KMS Public Key PEM file: ___________________
Create IAM Account Role
An IAM role is used to authorize Snowflake to access the future Protect Lambda resource.
To create IAM account role:
From the AWS console, login to the AWS sub-account where Protegrity will be hosted.
Access IAM, select roles and then Create Role.
Select AWS account from the list of trusted entities types.
Select your AWS Account Id as a placeholder value. You will update this field later when configuring Snowflake access.
Select Require external ID and enter the following placeholder value.
REPLACE_ME_WITH_EXTERNAL_ID
Click Next.
Continue and click Next
Enter a Role name, for example, Snowflake.
After the role is created, click on the role. Record the following information:
- Role Name (DBRoleName): ____________________
- Role ARN: ____________________
4.2.2 - Prerequisites
AWS Services
The following table describes the AWS services that may be a part of your Protegrity installation.
Service | Description |
|---|---|
Lambda | Provides serverless compute for Protegrity protection operations and the ESA integration to fetch policy updates or deliver audit logs. |
API Gateway | Provides the endpoint and access control. |
KMS | Provides secrets for envelope policy encryption/decryption for Protegrity. |
Secrets Manager | Provides secrets management for the ESA credentials . |
S3 | Intermediate storage location for the encrypted ESA policy layer. |
Kinesis | Required if Log Forwarder is to be deployed. Amazon Kinesis is used to batch audit logs sent from protector function to ESA. |
VPC & NAT Gateway | Optional. Provides a private subnet to communicate with an on-prem ESA. |
CloudWatch | Application and audit logs, performance monitoring, and alerts. Scheduling for the policy agent. |
ESA Version Requirements
The Protector and Log Forwarder functions require a security policy from a compatible ESA version.
The table below shows compatibility between different Protector and ESA versions.
Note
For the latest up-to-date information refer to: Protegrity Compatibility Matrix| Protector Version | ESA Version | |||
|---|---|---|---|---|
| 8.x | 9.0 | 9.1 & 9.2 | 10.0 | |
| 2.x | No | Yes | * | No |
| 3.0.x & 3.1.x | No | No | Yes | No |
| 3.2.x | No | No | Yes | * |
| 4.0.x | No | No | No | Yes |
Legend | |
|---|---|
Yes | Protector was designed to work with this ESA version |
No | Protector will not work with this ESA version |
* | Backward compatible policy download supported:
|
Prerequisites
Requirement | Detail |
|---|---|
Protegrity distribution and installation scripts | These artifacts are provided by Protegrity |
Protegrity ESA 10.0+ | The Cloud VPC must be able to obtain network access to the ESA |
| AWS Account | Recommend creating a new sub-account for Protegrity Serverless |
| Snowflake cluster (Enterprise Edition) |
Required Skills and Abilities
Role / Skillset | Description |
|---|---|
AWS Account Administrator | To run CloudFormation (or perform steps manually), create/configure a VPC and IAM permissions. |
Protegrity Administrator | The ESA credentials required to extract the policy for the Policy Agent |
| Network Administrator | To open firewall to access ESA and evaluate AWS network setup |
| Snowflake Administrator | Account Admin access required to setup access |
4.2.3 - Protect Service Installation
Preparation
Ensure that all the steps in Pre-Configuration are performed.
Login to the AWS account console where - Snowflake Protector on AWS will be installed.
Ensure that the required CloudFormation templates provided by Protegrity are available on your local computer.
Create Protect Lambda IAM Execution Policy
This task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy.
Perform the following steps to create the Lambda execution role and required policies:
From the AWS IAM console, select Policies > Create Policy.
Select the JSON tab and copy the following sample policy.
{ "Version": "2012-10-17", "Statement": [ { "Sid": "CloudWatchWriteLogs", "Effect": "Allow", "Action": [ "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" }, { "Sid": "KmsDecrypt", "Effect": "Allow", "Action": [ "kms:Decrypt" ], "Resource": [ "arn:aws:kms:*:*:key/*" ] } ] }For the KMS policy, replace the Resource with the ARN for the KMS key created in a previous step.
Select Next, type in a policy name, for example, ProtegrityProtectLambdaPolicy and Create Policy. Record the policy name:
ProtectLambdaPolicyName:__________________
Create Protect Lambda IAM Role
The following steps create the role to utilize the policy defined in Create Protect Lambda IAM Execution Policy.
To create protect lambda IAM execution role:
From the AWS IAM console, select Roles > Create Role.
Select AWS Service > Lambda > Next.
In the list, search and select the policy created in Create Protect Lambda IAM Execution Policy.
Click Next
Type the role name, for example, ProtegrityProtectRole
Click Create role
Record the role ARN.
Role ARN (LambdaExecutionRoleArn): ___________________
Installing through CloudFormation
The following steps describe the deployment of the Lambda function.
To install through CloudFormation:
Access CloudFormation and select the target AWS Region.
Click Create Stack and choose With new resources.
Specify the template.
Select Upload a template file.
Upload the Protegrity-provided CloudFormation template called pty_protect_cf.json and click Next.
Specify the stack details. Enter a stack name.
Note
The stack name will be appended to all the services created by the template.Enter the required parameters. All the values were generated in Pre-Configuration.
Parameter Description DBRoleName Name of the account role created in the pre-configuration step ArtifactS3Bucket Name of S3 bucket created in the pre-configuration step LambdaExecutionRoleArn The ARN of Lambda role created in the prior step MinLogLevel Minimum log level for protect function. Allowed Values: off, severe, warning, info, config, all The log forwarder parameters can be provided later after log forwarder is deployed. If you are not planning to deploy log forwarder you can skip this step.
Parameter Description KinesisLogStreamArn The ARN of the AWS Kinesis stream where audit logs will be sent for aggregation AuditLogFlushInterval Time interval in seconds used to accumulate audit logs before sending to Kinesis. Default value: 30. See Log Forwarder Performance section for more details. Click Next with defaults to complete CloudFormation.
After CloudFormation is completed, select the Outputs tab in the stack.
Record the following values:
- ApiGatewayId: ________________________________
- ProtectFunctionName: __________________________
- ProtectFunctionProductionAlias: __________________________
- ProtectLayerName: _____________________________
- SnowflakeApiAllowedPrefixes: ____________________
- SnowflakeApiAwsRoleARN: _______________________
Snowflake Configuration
The following sections will configure Snowflake to access the API Gateway. The CloudFormation installation installed a sample policy that can be used to smoke test the installation.
Login to Snowflake as ACCOUNTADMIN
Ensure that the current user can assume the Account Administrator role. This role must be created.
Create the Snowflake API Integration Object
From the Snowflake console worksheet, select the role ACCOUNTADMIN.
Paste the following text and replace the two parameters <SnowflakeApiAwsRoleARN> and <SnowflakeApiAllowedPrefixes> with values recorded in the last installation step of Installing through CloudFormation, then run the following Data Definition Language (DDL) in the console to create API integration object:
create or replace api integration protegrity_api api_provider = aws_api_gateway api_aws_role_arn = '<SnowflakeApiAwsRoleARN>' enabled = true api_allowed_prefixes = ('<SnowflakeApiAllowedPrefixes>');
Note
The name of the object protegrity_api can be replaced with a name of your choice, however the name you choose must be used consistently throughout the installation steps below.Describe the API Integration Object
We require values generated by the Snowflake integration object to complete configuring the API Gateway resource policy.
To describe API integration objects:
Run the following query in the console.
DESCRIBE API INTEGRATION protegrity_api;Record the following output values from the resulting query:
- API_AWS_IAM_USER_ARN: ___________________
- API_AWS_EXTERNAL_ID: ___________________
Update IAM Access Role Policy
This step allows the Snowflake IAM account to assume the role required to invoke the API Gateway resource.
To update API Integration Objects:
Return to theAWS Console > IAM > Roles and find the IAM role created earlier. For example, Snowflake.
Navigate to Trust Relationships > Edit trust policy.
Modify the Policy Document replacing the placeholder values indicated in the following snippet as API_AWS_IAM_USER_ARN and API_AWS_EXTERNAL_ID with the values recorded from the Snowflake integration object in Describe the API Integration Object.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "AWS": "<API_AWS_IAM_USER_ARN>" }, "Action": "sts:AssumeRole", "Condition": { "StringEquals": { "sts:ExternalId": "<API_AWS_EXTERNAL_ID>" } } } ] }
Test Connectivity
Perform the following steps to verify if Snowflake is working correctly with the Protegrity product.
Access the Snowflake SQL console.
Copy and paste the following snippet into a worksheet.
CREATE OR REPLACE SECURE EXTERNAL FUNCTION PTY_UNPROTECT_SAMPLE_POLICY(VAL VARCHAR) RETURNS VARCHAR(16777216) IMMUTABLE API_INTEGRATION = PROTEGRITY_API HEADERS = ( 'X-Protegrity-HCoP-Rules'= '{"jsonpaths":[{"op_type":"unprotect","data_element":"alpha"}]}' ) CONTEXT_HEADERS = (CURRENT_USER,CURRENT_TIMESTAMP,CURRENT_ACCOUNT) COMMENT='Unprotects text using an alpha token type.' AS '<SnowflakeApiAllowedPrefixes>';Replace the placeholder value indicated substituting your API Gateway URL captured in the stack outputs (SnowflakeApiAllowedPrefixes).
Run the following protect in the console:
select pty_unprotect_sample_policy('UtfVk UHgcD!');Verify that the string hello world! is returned.
Troubleshooting
Error | Action | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
Snowflake: 403 unauthorized |
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Snowflake: 5xx error | Try running the Lambda directly. Open the Lambda function and create the following test case:``` { “body”: “{ "data":[ [0," ‘UtfVk UHgcD!’"] ] }”, “headers”: { “sf-context-current-user”: “test”, “sf-custom-x-protegrity-hcop-rules”: “{"jsonpaths":[{"op_type":"unprotect","data_element":"alpha"}]}”, “sf-external-function-current-query-id”: “test-id” } } 4.2.4 - Policy Agent InstallationInstall the policy agent. The following sections will install the Policy Agent. The Policy Agent polls the ESA and deploys the policy to Protegrity Serverless as a static resource. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. Contact Protegrity Professional Services for further guidance on configuration alternatives in the Cloud. ImportantIf you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), refer to the PPC Appendix: Policy Agent Certificate and Key Guidance for specific instructions on obtaining and using the CA certificate and datastore key fingerprint. The steps in this section are specific to ESA and may differ for PPC. Be sure to follow the PPC documentation for the most accurate and up-to-date setup guidance.ESA ServerPolicy Agent Lambda requires ESA server running and accessible on TCP port 443. Note down ESA IP address: ESA IP Address (EsaIpAddress): ___________________ Certificates on ESANoteIf you are deploying Policy Agent with Protegrity Provisioned Cluster (PPC), see PPC Appendix: Policy Agent Certificate Guidance for specific instructions on obtaining and using the CA certificate. The steps in this section are specific to ESA and may differ for PPC.Whether your ESA is configured with default self-signed certificate or your corporate CA certificate, Policy Agent can validate authenticity of ESA connection using CA certificate. The process for both scenarios is the same:
To obtain self-signed CA certificate from ESA:
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation. Identify or Create a new VPCEstablish a VPC where the Policy Agent will be hosted. This VPC will need connectivity to the ESA. The VPC should be in the same account and region established in Pre-Configuration. VPC name: ___________________ VPC Subnet ConfigurationIdentify or create a new subnet in the VPC where tha Lambda function will be connected to. It is recommended to use a private subnet. Subnet name: ___________________ NAT Gateway For ESA Hosted Outside AWS NetworkIf ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well. VPC Endpoints ConfigurationIf an internal VPC was created, then add VPC Endpoints, which will be used by the Policy Agent to access AWS services. Policy Agent needs access to the following AWS services:
Identify or Create Security GroupsPolicy Agent and cloud-based ESA appliance use AWS security groups to control traffic that is allowed to leave and reach them. Policy Agent runs on schedule and is mostly concerned with allowing traffic out of itself to ESA and AWS services it depends on. ESA runs most of the time and it must allow Policy Agent to connect to it. Policy Agent security group must allow outbound traffic using rules described in the table below. To edit security group navigate: From VPC > Security Groups > Policy Agent Security Group configuration.
Record Policy Agent security group ID: Policy Agent Security Group Id: ___________________ Policy Agent will reach out to ESA on port 443. Create following inbound security group rule for cloud-based ESA appliance to allow connections from Policy Agent:
Creating ESA CredentialsPolicy Agent Lambda requires ESA credentials to be provided as one of the three options. NoteThe username and password of the ESA user requires role with Export Resilient Package and Can Create JWT Token permissions. Security Administrator is one of the predefined roles which contains the above permissions, however for separation of duties it is recommended to create custom role.Option 1: Secrets ManagerCreating secrets manager secret with ESA username and password.
Option 2: KMS Encrypted PasswordESA password is encrypted with AWS KMS symmetric key.
Option 3: Custom AWS Lambda functionWith this option ESA username and password are returned by a custom AWS Lambda function. This method may be used to get the username and password from external vaults.
Create Agent Lambda IAM PolicyFollow the steps below to create Lambda execution policies. Create Agent Lambda IAM policy
Create Agent Lambda IAM RolePerform the following steps to create Agent Lambda execution IAM role. To create agent Lambda IAM role:
Corporate Firewall ConfigurationIf an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access from the NAT Gateway IP to ESA via port 443 and 443. CloudFormation InstallationCreate the Policy Agent in the VPC using the CloudFormation script provided by Protegrity.
Policy Agent Lambda ConfigurationAfter the CloudFormation stack is deployed, the Policy Agent Lambda must be configured with parameters recorded in earlier steps. From your AWS Console, navigate to lambda and select the following Lambda. Protegrity_Agent<STACK_NAME>_ Select Configuration tab and scroll down to the Environment variables section. Select Editand replace all entries with the actual values.
Test InstallationOpen the Lambda and configure Test to execute the lambda and specify the default test event. Wait for around 20 seconds for the Lambda to complete. If policy is downloaded successfully, then a success message appears. Navigate to the AWS_POLICY_S3_BUCKET bucket and verify that the AWS_POLICY_S3_FILENAME file was created. Troubleshooting
Additional ConfigurationStrengthen the KMS IAM policy by granting access only to the required Lambda function(s). Finalize the IAM policy for the Lambda Execution Role. Ensure to replace wildcard * with the region, account, and resource name information where required. For example, Policy Agent ScheduleIf specified in CloudFormation Installation, the agent installation created a CloudWatch event rule, which checks for policy update on an hourly schedule. This schedule can be altered to the required frequency. Under CloudWatch > Events > Rules, find Protegrity_Agent_{stack_name}. Click Action > Edit Set the cron expression. A cron expression can easily be defined using CronMaker, a free online tool. Refer to http://www.cronmaker.com. 4.2.5 - Audit Log Forwarder InstallationInstall the audit log forwarder. The following sections show steps how to install Audit Log Forwarder component in the AWS Cloud. The Log Forwarder deployment allows for the audit logs generated by Protector to be delivered to ESA for auditing and governance purposes. Log Forwarder component is optional and is not required for the Protector Service to work properly. See Log Forwarding Architecture section in this document for more information. Some of the installation steps are not required for the operation of the software but recommended for establishing a secure environment. C ontact Protegrity for further guidance on configuration alternatives in the Cloud. NoteThe installation steps below assume that the Log Forwarder is going to be installed in the same AWS account as the corresponding Protect Lambda service. For instructions on how to install Log Forwarder in the AWS account separate than the Protect Lambda, please contact Protegrity.ESA Audit Store ConfigurationESA server is required as the recipient of audit logs. Verify the information below to ensure ESA is accessible and configured properly.
Certificates on ESANoteThis section is optional. If CA certificate is not provided, the Log Forwarder will skip server certificate validation and will connect to ESA without verifying that it is a trusted server. If you are deploying Log Forwarder with Protegrity Provisioned Cluster (PPC), certificate authorization and CA validation are not supported. Configuration steps related to certificates in this section do not apply to PPC. See Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster): Log Forwarder Setup with PPC for details. By default, ESA is configured with self-signed certificates, which can optionally be validated using a self-signed CA certificate supplied in the Log Forwarder configuration. If no CA certificate is provided, the Log Forwarder will skip server certificate validation. NoteCertificate Validation can be bypassed for testing purposes, see section: Install through CloudFormationIf ESA is configured with publicly signed certificates, this section can be skipped since the forwarder Lambda will use the public CA to validate ESA certificates. To obtain the self-signed CA certificate from ESA:
For more information about ESA certificate management refer to Certificate Management Guide in ESA documentation. AWS VPC ConfigurationLog forwarder Lambda function requires network connectivity to ESA, similar to Policy Agent Lambda function. Therefore, it can be hosted in the same VPC as Policy Agent. Separate VPC can be used, as long as it provides network connectivity to ESA. NoteAWS Lambda service uses permissions in log forwarder function execution role to create and manage network interfaces. Lambda creates a Hyperplane ENI and reuses it for other VPC-enabled functions in your account that use the same subnet and security group combination. Each Hyperplane ENI can handle thousands of connections/ports as the Lambda function scales up. If more connections are needed AWS Lambda service creates additional Hyperplane ENIs. There’s no additional charge for using a VPC or a Hyperplane ENI. Refer to AWS official Lambda Hyperplane ENIs docs for more information.VPC Name: ___________________ VPC Subnet ConfigurationLog Forwarder can be connected to the same subnet as Policy Agent or separate one as long as it provides connectivity to ESA. Subnet Name: ___________________ NAT Gateway For ESA Hosted Outside AWS NetworkIf ESA server is hosted outside of the AWS Cloud network, the VPC configured for Lambda function must ensure additional network configuration is available to allow connectivity with ESA. For instance if ESA has a public IP, the Lambda function VPC must have public subnet with a NAT server to allow routing traffic outside of the AWS network. A Routing Table and Network ACL may need to be configured for outbound access to the ESA as well. VPC Endpoint ConfigurationLog Forwarder Lambda function requires connectivity to Secrets Manager AWS service. If the VPC identified in the steps before has no connectivity to public internet through the NAT Gateway, then the following service endpoint must be configured:
Security Group ConfigurationSecurity groups restrict communication between Log Forwarder Lambda function and the ESA appliance. The following rules must be in place for ESA and Log Forwarder Lambda function. From VPC > Security Groups > Log Forwarder Security Group configuration.
Record the name of Log Forwarder security group name. Log Forwarder Security Group Id: ___________________ The following port must be open for the ESA. If the ESA is running in the Cloud, then create the following security. NoteIf an on-premise firewall is used, then the firewall must allow access from the NAT Gateway to an ESA. The firewall must allow access the NAT Gateway IP access to ESA via port 9200.ESA Security Group configuration
Configure ESA Audit Store CredentialsNoteThis section is optional. If client certificate authentication is not set up, the Log Forwarder will connect to ESA without authentication credentials.Audit Log Forwarder can optionally authenticate with ESA using certificate-based authentication with a client certificate and certificate key. If used, both the certificate and certificate key will be stored in AWS Secrets Manager. Download the following certificates from the /etc/ksa/certificates/plug directory of the ESA:
After certificates are downloaded, open each PEM file in text editor and replace all new lines with escaped new line: \n. To escape new lines from command line, use one of the commands below depending on your operating system. Linux Bash: Windows PowerShell: For more information on how to configure client certificate authentication for Audit Store on ESA refer to Audit Store Guide. To create secret with ESA client certificate/key pair in AWS Secrets Manager.
NoteIf you are deploying Log Forwarder with PPC, do not configure client certificate authentication. See PPC Appendix: Log Forwarder Certificate Guidance for details.Create Audit Log Forwarder IAM Execution PolicyThis task defines a policy used by the Protegrity Log Forwarder Lambda function to write CloudWatch logs, access the KMS encryption key to decrypt the policy and access Secrets Manager for log forwarder user credentials. Perform the following steps to create the Lambda execution role and required policies:
Create Log Forwarder IAM RolePerform the following steps to create Log Forwarder execution IAM role. To create Log Forwarder IAM role:
Installation ArtifactsAudit Log Forwarder installation artifacts are part of the same deployment package as the one used for protect and policy agent services. Follow the steps below to ensure the right artifacts are available for log forwarder installation.
Install through CloudFormationThe following steps describe the deployment of the Audit Log Forwarder AWS cloud components.
Add Kinesis Put Record permission to the Protect Function IAM Role
Test Log Forwarder InstallationTesting in this section validates the connectivity between Log Forwarder and ESA. The sample policy included with the initial installation and test event below are not based on your ESA policy. Any logs forwarded to ESA which are not signed with a policy generated by your ESA will not be added to the audit store. Install Log Forwarder and configure according to previous sections. Log Forwarder configuration MinLogLevel must be at least info level.
Update Protector With Kinesis Log StreamIn this section, Kinesis log stream ARN will be provided to the Protect Function installation. NoteIf the Protector has not been installed, you may provide the KinesisLogStreamArn during protector installation and skip the remainder of this section.
Update Policy Agent With Log Forwarder Function TargetLog Forwarder Lambda function requires a policy layer which is in sync with the Protegrity Protector. This section will describe the steps to update the policy agent to include updating Log Forwarder Lambda function. NoteIf the policy agent has not been installed, follow the steps in Policy Agent Installation. Set AWS_PROTECT_FN_NAME to include both protector and log forwarder lambda functions.
Test Full Log Forwarder InstallationInstall and configure Protegrity Agent, Protector, and Log Forwarder components.
Troubleshooting
4.2.6 -Prerequisites
4.2.7 -Required Skills and Abilities
4.2.8 -AWS ServicesThe following table describes the AWS services that may be a part of your Protegrity installation.
4.3 - Understanding Snowflake ObjectsKey concepts in understanding the Protegrity Serverless with Snowflake. 4.3.1 - External FunctionsCall out to a process external to Snowflake through a REST API. External FunctionsSnowflake provides an External Function capability used to call out to a process external to Snowflake through a REST request over TLS encryption. In the Protegrity Serverless for Snowflake solution, this external service is the Protegrity Endpoint for data re-identification operations. 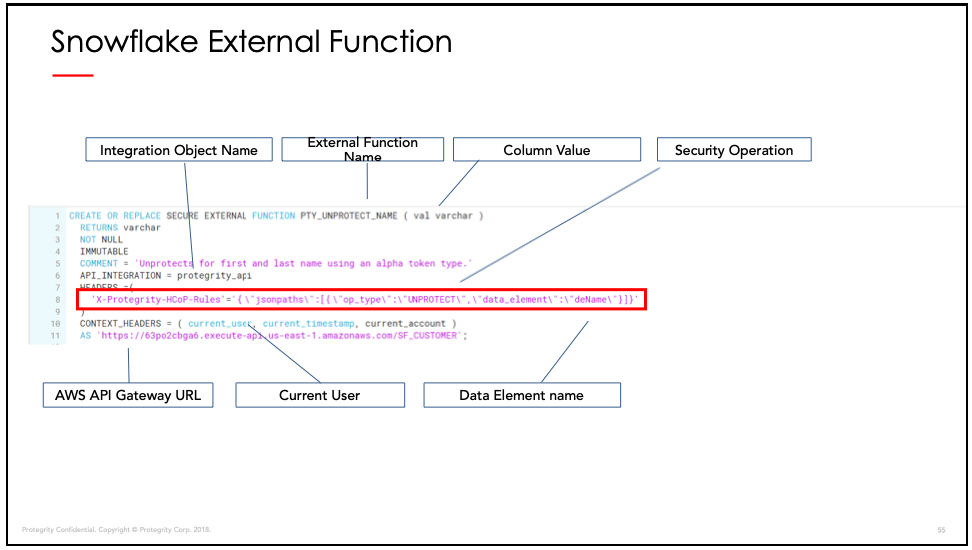 Security Operation ParametersThe following table describes optional and required security operation parameters.
4.3.2 - Snowflake Masking PoliciesOptimize REST requests to the Protegrity endpoint. Masking Policies in the Sample Application are used to optimize REST requests to the Protegrity endpoint and to prevent integration of External Functions into queries.
4.4 - PerformancePerformance benchmarks and considerations. 4.4.1 - Performance ConsiderationsPerformance benchmarks and considerations. Performance ConsiderationsThe following factors may cause variation in real performance versus benchmarks:
4.4.2 - Sample BenchmarksSample benchmarks for different cluster sizes. Sample BenchmarksThe following benchmarks were performed against different cluster sizes. These are median times of approximately five runs each. The query unprotected six columns per row (first_name, last_name, email, postal_code, ssn, iban):
4.4.3 - ConcurrencyGuidance on concurrency. ConcurrencySnowflake provides guidance on the maximum concurrent requests to the Protegrity API. However, reaching this maximum request depends on additional factors, such as, cluster use and available resources. In addition, depending on the query plan, individual batches may be processed serially across different UDFs. The formula for theoretical maximum Snowflake concurrency is N * C * M * E * P:
The following table shows this calculation for a single query.
Note* theoretical maximum concurrent requests based on engineering guidance from Snowflake.4.4.4 - Concurrency TuningConcurrency tuning considerations. Lambda TuningAWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region:
The concurrent executions quota cap is the maximum number of Lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket. The Burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. After the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended to select a Snowflake AWS region with the highest burst limits. API Gateway TuningAWS maintains a Throttle quota for the API Gateway. By default, API Gateway limits concurrent requests to 10,000 requests per second and throttles subsequent traffic with a 429 Too Many Requests error response. This quota applies across all APIs in an account and region. The API Gateway default quota may need to be increased based on the Concurrency table in Lambda Tuning. Keep in mind that hitting quota limits effectively throttles any other API services in the region. The API Gateway also limits burst. Burst is the maximum number of concurrent requests that API Gateway can fulfill at any instant without returning 429 Too Many Requests error responses. This limit can be increased by AWS, but is not normally an adjustable. Enable CloudWatch metrics within the API Gateway to monitor max concurrency and investigate throttling errors. See the Concurrency Troubleshooting section on interpreting CloudWatch metrics. Quotas adjustments are applied for region and account. Throttling is also enabled by default in the API Gateway stage used by the Protegrity Lambda function. The stage configuration throttling must be adjusted if the quota is modified. Stage throttling is shown in the following image.
For example, a test query was executed against a 274 million record table on a 2X-Large Snowflake cluster using a query with 10 UDF columns. Using the reference table in the Concurrency table, the cluster would theoretically generate over 20,000 requests/sec to execute the given query. Using API Gateway’s default settings, the requests exceeding 10,000 requests/sec will be throttled. Therefore, this query may fail intermittently due to a high number of throttling errors. After requesting a quota increase, AWS modified the account’s API Gateway throttling quota from 10,000 to 24,000, this same query succeeded without throttles. In addition, 8 concurrent queries also succeeded. Eight concurrent queries did not generate 8x the concurrent load due to the cluster’s own resource limitations. This indicates the cluster peaked. Concurrency TroubleshootingHitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a Snowflake query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your API Gateway or Lambda services in the region. Snowflake is tolerant of a certain ratio of failed requests and automatically retries. If a high percentage of requests fail, then the query may abort and the last error code will display in the console. For example, 429 Too Many Requests. CloudWatch Metrics can be manually enabled on the API Gateway to reveal if quotas are being reached. Metrics aggregate errors into two buckets that are 4xx and 5xx. CloudWatch logs can be used to access the actual error code. The following table describes how to interpret the CloudWatch metrics.
NoteThe API Gateway Lambda proxy maps 429 errors from the Lambda service to 500 errors.The following screenshot shows an example of searching CloudWatch Logs using Log Insights:
Cold-Start PerformanceCold-start vs warm execution refers to the state of the Lambda when a request is received. A cold-start undergoes additional initialization, such as, loading the security policy. Warm execution applies to all subsequent requests served by the Lambda. The following table shows an example how these states impact latency and performance.
Note
4.4.5 - Log Forwarder Performance TuningGuidance on concurrency. Log Forwarder PerformanceLog forwarder architecture is optimized to minimize the amount of connections and reduce the overall network bandwidth required to send audit logs to ESA. This is achieved with batching and aggregation taking place on two levels. The first level is in protect function instances, where audit logs from consecutive requests to an instance are batched and aggregated. The second level of batching takes place in Amazon Kinesis Stream where log records from different protect function instances are additionally batched and sent to log forwarder function where they are aggregated. This section shows how to configure the deployment to accommodate different patterns of anticipated audit log stream. It also shows how to monitor deployment resources to detect problems before audit records are lost.
4.4.6 -API Gateway TuningAWS maintains a Throttle quota for the API Gateway. By default, API Gateway limits concurrent requests to 10,000 requests per second and throttles subsequent traffic with a 429 Too Many Requests error response. This quota applies across all APIs in an account and region. The API Gateway default quota may need to be increased based on the Concurrency table in Lambda Tuning. Keep in mind that hitting quota limits effectively throttles any other API services in the region. The API Gateway also limits burst. Burst is the maximum number of concurrent requests that API Gateway can fulfill at any instant without returning 429 Too Many Requests error responses. This limit can be increased by AWS, but is not normally an adjustable. Enable CloudWatch metrics within the API Gateway to monitor max concurrency and investigate throttling errors. See the Concurrency Troubleshooting section on interpreting CloudWatch metrics. Quotas adjustments are applied for region and account. Throttling is also enabled by default in the API Gateway stage used by the Protegrity Lambda function. The stage configuration throttling must be adjusted if the quota is modified. Stage throttling is shown in the following image.
For example, a test query was executed against a 274 million record table on a 2X-Large Snowflake cluster using a query with 10 UDF columns. Using the reference table in the Concurrency table, the cluster would theoretically generate over 20,000 requests/sec to execute the given query. Using API Gateway’s default settings, the requests exceeding 10,000 requests/sec will be throttled. Therefore, this query may fail intermittently due to a high number of throttling errors. After requesting a quota increase, AWS modified the account’s API Gateway throttling quota from 10,000 to 24,000, this same query succeeded without throttles. In addition, 8 concurrent queries also succeeded. Eight concurrent queries did not generate 8x the concurrent load due to the cluster’s own resource limitations. This indicates the cluster peaked. 4.4.7 -Cold-Start PerformanceCold-start vs warm execution refers to the state of the Lambda when a request is received. A cold-start undergoes additional initialization, such as, loading the security policy. Warm execution applies to all subsequent requests served by the Lambda. The following table shows an example how these states impact latency and performance.
Note
4.4.8 -Concurrency TroubleshootingHitting up against quota limits may indicate that quota adjustments are required. Exceeding quota limits may cause a Snowflake query to fail or reduce performance. In the worst case, significant throttling can impact the performance of all your API Gateway or Lambda services in the region. Snowflake is tolerant of a certain ratio of failed requests and automatically retries. If a high percentage of requests fail, then the query may abort and the last error code will display in the console. For example, 429 Too Many Requests. CloudWatch Metrics can be manually enabled on the API Gateway to reveal if quotas are being reached. Metrics aggregate errors into two buckets that are 4xx and 5xx. CloudWatch logs can be used to access the actual error code. The following table describes how to interpret the CloudWatch metrics.
NoteThe API Gateway Lambda proxy maps 429 errors from the Lambda service to 500 errors.The following screenshot shows an example of searching CloudWatch Logs using Log Insights:
4.4.9 -Lambda TuningAWS maintains quotas for Lambda concurrent execution. Two of these quotas impact concurrency and compete with other Lambdas in the same account and region:
The concurrent executions quota cap is the maximum number of Lambda instances that can serve requests for an account and region. The default AWS quota may be inadequate based on peak concurrency based on the table in the previous section. This quota can be increased with an AWS support ticket. The Burst concurrency quota limits the rate at which Lambda will scale to accommodate demand. This quota is also per account and region. The burst quota cannot be adjusted. AWS will quickly scale until the burst limit is reached. After the burst limit is reached, functions will scale at a reduced rate per minute (e.g. 500). If no Lambda instances can serve a request, the request will fail with a The burst limit is a fixed value and varies significantly by AWS region. The highest burst (3,000) is currently available in the following regions: US West (Oregon), US East (N.Virginia), and Europe (Ireland). Other regions can burst between 500 and 1,000. It is recommended to select a Snowflake AWS region with the highest burst limits. 4.5 - Audit LoggingAudit log description/formatting Audit LoggingAudit records and application logs stream to Amazon CloudWatch Logs or optionally be sent to ESA. Cloud Protect uses a JSON format for audit records that is described in the following sections. You can analyze and alert on audit records using Protegrity ESA or Amazon CloudWatch. Third-party solutions may be used if they are supported by Amazon Cloudwatch or AWS Lambda logging extensions. For more information about forwarding your audit records to ESA, contact Protegrity. For more information about Amazon CloudWatch, refer to the Amazon CloudWatch User Guide. For more information about audit records, refer to the Protegrity Analytics Guide. Audit record fieldsThe audit record format has been altered in version 3.1 of the protector to provide more information.
Example Audit RecordsThe following are sample audit messages: Protect Success: User permission denied: Data element not found: 4.6 - No Access BehaviorUnauthorized unprotect requests behaviour. No Access BehaviorThe security policy maintains a No Access Operation, configured in an ESA, which determines the response for unauthorized unprotect requests.
The following table describes the result returned in the response for the various no access unprotect permissions.
NoteAn unauthorized protect will throw an exception.4.7 - Upgrading To The Latest VersionInstructions for upgrading the protector. Download the Latest VersionYou can download the latest version of the deployment package from https://my.protegrity.com. Navigate to Data Protection > Cloud Protect to download the latest version. After downloading the deployment package from the Protegrity Portal, unzip the package to extract the artifact files. In the AWS Console, navigate to the S3 bucket that was previously created to upload deployment artifacts (see: Create S3 bucket for Installing Artifacts). NoteOnly extract the deployment package and not the files in it.Upload the following artifacts to the S3 bucket: - -
If the release version matches your existing deployment, you don’t need to upload it again. Save the following artifacts on your local system so that you have them available during the next steps: - -
Perform the following steps to upgrade the Agent Lambda and Protect Lambda separately. ImportantIf new versions are available for both Agent and Protect Lambdas, Agent Lambda must be upgraded first.Disable Protegrity Agent Function CloudWatch Event RuleCloud Watch Event Rule is used to periodically run Protegrity Agent Function to synchronize policy from ESA. This functionality is optional when deploying Protegrity Serverless Solution. If the Event Rule is enabled, it must be disabled temporarily for the time of the upgrade process. Follow the steps below to determine if your deployment uses Event Rule and disable it.
Upgrading Policy Agent LambdaNoteIf the release version of the artifact zip file has not changed since the previous installation, you can skip the Agent Lambda upgrade.
NoteMake sure you are viewing the latest Lambda Function, not the published version.
Upgrading Log Forwarder LambdaNoteIf you are upgrading protector to one of these versions: [3.2.2, 3.2.3], skip this section and follow instruction to install new Log Forwarder Audit Log Forwarder Installation.
Upgrading Protect LambdaNoteIf the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Diagram below illustrates upgrade steps.
Re-enable Protegrity Agent Function CloudWatch Event RuleIf the Event Rule was disabled at the beginning of the upgrade process, you must re-enabled it. Follow the steps below to re-enable Policy Agent Event rule.
4.8 - Known LimitationsKnown product limitations. Known LimitationsKnown product limitations:
4.9 - AppendicesAdditional references for the protector. 4.9.1 - Sample Snowflake External FunctionA collection of sample Snowflake functions. Sample Snowflake External Function
Cutover Dates of the Proleptic Gregorian Calendar: no issues (no conversions performed by Snowflake)
**Recommended approach for protecting whole numbers fields in Snowflake
When in doubt, use DECIMAL for any numeric range. 4.9.2 - Installing the Policy Agent and Protector in Different AWS AccountsExample steps to install Agent in a different AWS account than the Protector The Policy Agent Lambda function and Protect Lambda functions can be installed in separate AWS accounts. However, additional configuration is required to authorize the Policy Agent to provision the security policy to a remote Protect Lambda function. NoteThe Policy Agent will deploy an encrypted security policy file to an S3 bucket in the Protect function’s AWS Account.Create Agent Lambda IAM policy
Create Policy Agent cross-account IAM Role
Allow the Policy Agent Cross-Account Role to be Assumed by the Policy Agent IAM Role
Add Assume Role to the Policy Agent Execution IAM Role
Update the Policy Agent Lambda Configuration
4.9.3 - Integrating Cloud Protect with PPC (Protegrity Provisioned Cluster)Concepts for integrating with PPC (Protegrity Provisioned Cluster) This guide describes how to configure the Protegrity Policy Agent and Log Forwarder to connect to a Protegrity Provisioned Cluster (PPC), highlighting the differences from connecting to ESA. Key Differences: PPC vs ESA
Prerequisites
Policy Agent Setup with PPCImportantWhen connecting to PPC, the Policy Agent requires thePTY_DATASTORE_KEY fingerprint. For ESA 10.2, the fingerprint is optional but recommended. See Policy Agent Installation for general setup steps.Follow these instructions as a guide for understanding specific inputs for Policy Agent integrating with PPC:
Log Forwarder Setup with PPCNoteWhen using PPC, certificate authentication and CA validation are not supported for the Log Forwarder. Configuration steps related to certificates in Log Forwarder Installation do not apply to PPC. If you attempt to use certificates provided by PPC, the Log Forwarder will not function correctly.
TroubleshootingProtector Lambda fails with “AWS KMS Decrypt failed”Symptom: After a successful Policy Agent run and layer update, the Protector Lambda returns: The Protector Lambda logs show: Cause: The public key configured in the PPC/ESA datastore does not match the KMS key pair used by the Policy Agent. The policy package is encrypted with the public key stored in the datastore. If that key does not correspond to the KMS key pair whose private key is used for decryption, the Protector Lambda will fail to decrypt the policy. Resolution:
ImportantAlways verify that the public key registered in the PPC/ESA datastore belongs to the same KMS key pair referenced by the Policy Agent. A mismatch between these keys is a common cause of The KMS key must be an asymmetric key with the Encrypt and decrypt key usage type. Symmetric keys or asymmetric keys configured for signing will not work. Additional Notes
4.9.4 - Policy Agent - Custom VPC Endpoint Hostname ConfigurationCustom vpc endpoint hostname configuration The Policy Agent uses default endpoint hostnames to communicate with other AWS services (for example, secretsmanager.amazonaws.com). This configuration will only work in VPCs where Amazon-provided DNS is available (default VPC configuration with private DNS option enabled for the endpoint). If your VPC uses custom DNS, follow the instructions below to configure the Policy Agent Lambda to use custom endpoint hostnames. NoteThis configuration is only available with the Cloud Protect version 1.5.0 or higher. For more information about the upgrade instructions, refer to Upgrading to the Latest Version.Identify DNS HostnamesTo identify DNS hostnames:
Update the Policy Agent Lambda configurationTo update policy agent lambda configuration:
4.9.5 - Protection MethodsCloud API supported protection methods Protection MethodsFor more information about the protection methods supported by Protegrity, refer to the Protection Methods Reference.
4.9.6 - Configuring Regular Expression to Extract Policy UsernameExtract the policy username from the AWS identity. Configuring Regular Expression to Extract Policy UsernameCloud Protect Lambda Function exposes USERNAME_REGEX configuration to allow extraction of policy username from user in the request.
4.9.7 - Associating ESA Data Store With Cloud Protect AgentConfigure ESA data store for Policy Agent. Associating ESA Data Store With Cloud Protect AgentESA controls which policy is deployed to protector using concept of data store. A data store may contain a list of IP addresses identifying servers allowed to pull the policy associated with that specific data store. Data store may also be defined as default data store, which allows any server to pull the policy, provided it does not belong to any other data stores. Node registration occurs when the policy server (in this case the policy agent) makes a policy request to ESA, where the agent’s IP address is identified by ESA. NoteFor more information about ESA data store refer to Policy Management Guide which is part of Protegrity ESA documentation.Policy agent lambda source IP address used for node registration on ESA depends on ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP and the PTY_ADDIPADDRESSHEADER configuration exposed by the agent lambda. The Lambda service uses multiple network interfaces, internal network interface with ephemeral IP range of 169.254.x.x and external network interface with IP range of the VPC subnet the Lambda is associated with. By default, when agent lambda is contacting ESA to register node for policy download, ESA uses agent Lambda VPC IP address. This default behavior is caused by the default ESA hubcontroller configuration ASSIGN_DATASTORE_USING_NODE_IP=false and agent default configuration PTY_ADDIPADDRESSHEADER=yes. In some cases, when there is a proxy server between the ESA and agent lambda, the desirable ESA configuration is ASSIGN_DATASTORE_USING_NODE_IP=true. and PTY_ADDIPADDRESSHEADER=no which will cause the ESA to use proxy server IP address. The table below shows how the hubcontroller and agent settings will affect node IP registration on ESA.
5 - Amazon S3Cloud Storage Protector - Amazon. This document describes high-level architecture of the Cloud Storage Protector on AWS, the installation procedures and provides guidance on performance. This document should be used in conjunction with the Cloud API on AWS Protegrity documentation. This guide may also be used with the Protegrity Enterprise Security Administrator Guide, which explains the mechanism for managing the data security policy. 5.1 - OverviewSolution overview and features. Solution OverviewThe S3 Protector provides an automated solution for protecting files on Amazon S3 at-scale. The product integrates with the Amazon S3 Event Notification feature to trigger data protection when new files are created or modified. The notifications are consumed asynchronously by S3 Protector Lambda Function which breaks up files into batches, transmitting them securely to Cloud API Protector on AWS. The Cloud API Protector applies Protegrity cryptographic methods and sends back processed data. Processed file is saved to an output S3 bucket after all batches of the input file are processed. The serverless nature of the S3 protector solution allows scaling up automatically to accommodate for increasing volume of files and scale completely down during idle time, providing significant savings in Cloud compute fees. The solution requires installation of Protegrity Cloud Protector, Cloud API. The Cloud API Protector provides an endpoint for performing Protegrity operations within Amazon AWS for integration with Cloud-based ETL workflows. Protected files can be used as source for a data lake or downstream database ingestion. For example:
Similar to other Protegrity products, the S3 Protector utilizes data security policy maintained on Enterprise Security Appliance (ESA). The existing ESA policy user must be supplied as part of the S3 Protector configuration. The user acts as a service account user for the S3 Protector deployment. For more information about policy user configuration refer to Enterprise Security Administrator Guide. Analytics on Protected DataProtegrity’s format and length preserving tokenization scheme make it possible to perform analytics directly on protected data. Tokens are join-preserving so protected data can be joined across datasets. Often statistical analytics and machine learning training can be performed without the need to re-identify protected data. However, a user or service account with authorized security policy privileges may re-identify subsets of data using the Cloud Storage Protector - Amazon S3 service. FeaturesProtegrity S3 Protector provides the following features:
For more information about the available protection options, such as data types, Tokenization or Encryption types, or length-preserving and non-preserving tokens, refer to Protection Methods Reference. 5.2 - ArchitectureDeployment architecture and connectivity Deployment ArchitectureThe Protegrity S3 solution should be deployed in the customer’s Cloud account within the same AWS region as the Protegrity Cloud Protect API. The Cloud Protect API is required. Two S3 Buckets are required for processing data with S3 Protector:
The following diagram shows the high-level architecture of the S3 Protector.
The ruleset for processing a type of input dataset is defined by a metadata file called mapping.json. A dedicated folder with a mapping.json must be created in the S3 input bucket for each distinct file schema. The mapping.json provides:
Input and output data file specifications are passed to Pandas library as arguments, offering flexibility to handle diverse data file structures. Column instructions define the protect operation and data element to apply for each column. The Protegrity S3 protector invokes the Cloud Protect API to execute the policy on the data. The processed data is saved to the specified target S3 bucket. The target bucket can be the basis of a data lake or a staging area to load databases. For example, Snowflake Snowpipe can be used to automatically ingest the processed (ie. Protected) data into Snowflake. Amazon Redshift provides a similar mechanism for bulk loading data from Amazon S3. For more information about installing and managing the Cloud API component, refer to the Cloud API on AWS Protegrity documentation. AWS Lambda TimeoutS3 Protector is an AWS Lambda function. Every AWS Lambda function has a maximum execution time called a ’timeout’. When you install this product with supplied CloudFormation template its timeout is set to 5 minutes. A maximum timeout of 15 minutes may be set. Function timeout puts a restriction on the size of the file that this product may process. If S3 Protector runs out of time while processing a file, it will fail with ‘Status: timeout’, which will appear in the logs similar to the following: When S3 Protector runs out of time, it does not have an opportunity to mark file upload as completed. Incomplete uploads do not appear in S3 console, however you are still charged for them. Review AWS documentation on how to manage incomplete multi-part file uploads, for example: There is no way to automatically re-start this product from where it has timed out while processing a file. To reduce the likelihood of a timeout error, consider the following:
Parquet TimestampParquet files define file schema with a data type for each column. S3 Protector uses Pandas library to process data in the source file. Pandas library represents timestamps as 64-bit integers representing microseconds since the UNIX epoch. The supported date range for this representation is between ‘1677-09-21 00:12:43.145224’ and ‘2262-04-11 23:47:16.854775’. To correctly handle timestamps outside of this range, S3 Protector will treat every timestamp column in a source file as a string column. The schema of protected file will differ from the source file, where every protected timestamp column will be converted to a string column. 5.3 - InstallationInstructions for installing Cloud Storage Protector Service. 5.3.1 - PrerequisitesRequirements before installing the protector. AWS ServicesThe following table describes the AWS services that may be a part of your Protegrity installation.
Prerequisites
Required Skills and Abilities
What’s Next5.3.2 - Pre-ConfigurationConfiguration steps before installing the protector. Provide AWS sub-accountIdentify or create an AWS account where the Protegrity solution will be installed. The installation instructions assume the same AWS account and region are used for Cloud Protect API deployment. AWS Account ID: ___________________ AWS Region: ___________________ Create S3 bucket for Installing ArtifactsThis S3 bucket will be used for the artifacts required by the CloudFormation installation steps. This S3 bucket must be created in the region that is defined in Provide AWS sub-account. To create S3 bucket for installing artifacts:
Cloud Protect API functionProtegrity Cloud Protect API on AWS is required for the S3 Protector installation. See the Cloud Protect API on AWS documentation to create a new installation if one is not already available in your account/region. With Cloud Protect API on AWS installed, follow the below instructions to obtain the ARN of the protector lambda function. Follow these steps to obtain Cloud API Lambda ARN.
Cloud Protect API function ARN: ____________________ S3 Buckets For Input And Output DataTwo S3 buckets are required. One bucket is used for incoming files. The second bucket is used for files processed by the S3 Protector. The buckets must be different. The S3 buckets should be created in the region that is defined in Provide AWS sub-account. NoteBefore continuing it is critical to understand Amazon S3 security concepts and best practices. You can refer to AWS S3 Best Practices for the list of recommend S3 security configuration, however it is strongly recommended to check the AWS official documentation for more details.Identify existing bucket names or follow the steps below to create new buckets.
Input S3 Bucket Name: ____________________ Output S3 Bucket Name: ____________________ What’s Next5.3.3 - S3 Protector Service InstallationInstall the S3 protector service. PreparationEnsure that all the steps in Pre-Configuration are performed.
Create S3 Protector Lambda IAM Execution PolicyThe below steps create an IAM policy for use by the Protegrity Lambda function. The policy grants permissions to:
Steps
Create S3 Protector Lambda IAM RoleThe following steps create the role to utilize the policy defined in the previous section. Steps
Install through CloudFormationThe following steps describe deployment of the S3 Protector Lambda Function using CloudFormation.
CloudFormation Parameters
Test S3 Protector Function ConfigurationPerform the following steps to verify that S3 Protector Function can read files from input S3 bucket, call Cloud API protector and write data to output S3 bucket. NoteSteps described in this section require read/write permissions for S3 data buckets. Data bucket names were recorded in prerequisites section.Before you begin:
data.csv:
Execute S3 Protector Function in AWS console:With the input data file and mapping file uploaded, follow the steps below to trigger the S3 Protect Function.
Verify execution results:
If the expected output is not present, please consult the Troubleshooting section for common errors and solutions.
Restore production configuration:After S3 Protector Function configuration has been verified, make sure that the following configuration was restored for production environment:
Configure S3 Lambda TriggersFollow the steps below to configure Amazon S3 event notification on the input bucket. This will allow Amazon S3 to send an event to S3 Protector Lambda function when an object is created or updated. NoteThe steps below require an AWS Administrator permissions to modify the resource-based Lambda policy. When new S3 trigger is added from the Lambda console, the console modifies the resource-based policy to allow Amazon S3 to invoke the function if the bucket name and account ID match.NoteWhen uploading multiple files or folders to S3, AWS S3 Lambda Trigger will generate one event per file. As expected, this will result in multiple S3 Protector instances running concurrently, one S3 Protector instance per file.Steps to Add S3 Lambda trigger:
Example UsageThis section describes typical usage of S3 Protector. Prepare data for testing:Sample datasets and mapping.json files are provided in appendix sections:
Create a new folder in the input S3 bucket:A new folder must be created in the S3 input bucket for each distinct file schema. Each folder can have a mapping.json file corresponding to the dataset type expected. It is recommended that input folders use S3 encryption:
Upload the mapping.json and dataset to the folder:The appropriate mapping.json file must be uploaded to the folder prior to uploading the dataset.
Verify output:Verify the output file was created:
Troubleshooting / Logs:Logs are written to CloudWatch. This could provide helpful information if the results are not as expected:
TroubleshootingBy default S3 Protector is set to log minimal information. It is beneficial to increase S3 Protector log level to either ‘config’ or ‘all’ while troubleshooting any error conditions. Use the CloudFormation installation steps to increase ‘MinLogLevel’ function configuration. S3 Protector Error States
Restarting S3 ProtectorIf S3 Protector fails, it is possible to start S3 Protector for existing source file without re-uploading the file again by using AWS Lambda console. With the input data file and mapping file uploaded, follow the steps below to trigger the S3 Protect Function. Steps
5.3.4 -Prerequisites
5.3.5 -AWS ServicesThe following table describes the AWS services that may be a part of your Protegrity installation.
5.3.6 -Required Skills and Abilities
5.4 - Mapping File ConfigurationKey concepts for defining the mapping.json file 5.4.1 - Mapping FileThe mapping.json is used for configuring how S3 Protector Function transforms the input data. The mapping file must be uploaded to the input S3 bucket before any files can be processed. OverviewAt minimum, one mapping.json file must be uploaded to the S3 bucket in the root folder. If multiple folders exist in the S3 bucket then each folder can have it’s own mapping.json. When nested folders exist in the bucket, S3 protector will look for a mapping file starting with the same folder as the data file and moving up the directory tree until root folder is reached. Configuration StructureThe mapping.json file must be formatted in valid JSON with the key-values configuration pairs described below: Data Columns TransformationEvery source file column must appear in either ‘columns’ or ‘ignored-columns’.
Input Data ConfigurationThe “input” optional configuration contains the following key-values pairs: formatSpecifies the format of the input data files. If format is not provided in the mapping json, the format will be inferred from the file extension. specProvides additional configuration for input file processing. This allows processing of non-default file formats. For example, pipe delimited files, header-less files, and various JSON record structures. ImportantSupplying custom arguments might result in an unexpected S3 Protector behavior. Protegrity is not responsible for any damages caused due to the use of custom Pandas configuration. Use this option at your own risk.The properties within the input spec block correspond with the Python Pandas reader functions arguments. For more information about supported format arguments refer to the Pandas documentation. Below you can find a list of links to Pandas official online documentation for each format supported by S3 Protector:
Output Data ConfigurationThe “output” optional configuration contains the following key-values pairs: formatSpecifies the format of the output data files. The format in the mapping json is only used when S3 Protector Function deployment parameter OutputFileFormat is set to use_mapping_spec. See the CloudFormation installation section for the full list of the output format configuration. specProvides additional configuration for the output file processing. ImportantSupplying custom arguments might result in an unexpected S3 Protector behavior. Protegrity is not responsible for any damages caused due to the use of custom Pandas configuration. Use this option at your own risk.The properties within the output spec block correspond with the Python Pandas DataFrame output function arguments. For more information about supported format arguments refer to the Pandas documentation. Below you can find a list of links to Pandas official online documentation for each format supported by S3 Protector:
5.4.2 - Column Mapping RulesIn order to ensure highest level of security, the S3 Protector requires users to define processing rules for all data columns. Every column that appears in a source file must be mentioned in the ‘mapping.json’ file. A column may appear in either ‘columns’ section or ‘ignored-columns’ section, but not both. Common Error ConditionsThe table below summaries common error conditions that may occur when creating a ‘mapping.json’ file:
NoteThe column names in the mapping file are case sensitive.5.5 - PerformanceBenchmarks and performance tuning Performance ConsiderationsThe following factors may affect S3 Protector performance:
BenchmarksThe following table shows throughput and latency for three different files. Each file has 21 columns, 6 of which were protected by S3 Protector with tokenization data elements. The remaining 15 columns were configured to pass through without applying protection. Two of the default S3 Protector settings were updated for this benchmark:
Performance Results
5.6 - Known LimitationsKnown product limitations. Known LimitationsKnown product limitations:
5.7 - Upgrading To The Latest VersionUpgrading S3 Protector Lambda Upgrade Process OverviewThe diagram below illustrates upgrade steps:
NoteIf the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Publish S3 Protector Lambda VersionPublishing a version of the S3 Protector Lambda allows updating it without interruptions to the existing traffic. Procedure
S3 Protector Lambda version number: ___________________ Run Protect Service UpgradeIn this step, the Protect service including Lambda $LATEST version will be updated using Cloud Formation template. The Lambda version created in previous step will be used to serve existing traffic during the upgrade process. Procedure
Finalize UpgradeIn this step, the S3 Protector Lambda will be configured to serve traffic using $LATEST version upgraded in the previous step. Procedure
5.8 - AppendicesAdditional references for the protector. 5.8.1 - Sample ConfigurationA dataset snippet and corresponding mapping.json file are provided. CSV Format - No HeaderDatasetMapping.json - Header Specified In Input Spec SectionCSV Format - Pipe DelimiterDatasetMapping.jsonJSON FormatDatasetMapping.json5.8.2 - Amazon S3 Security Best Practices ExamplesAmazon S3 Security Best Practices Examples NoteThe list below is not a comprehensive list of S3 configuration best practices. Refer to AWS documentation for more details.Block Public Access to Your Amazon S3 StorageEnabling Block Public Access helps protect your resources by preventing public access from being granted through the resource policies or access control lists (ACLs) that are directly attached to S3 resources. In addition to enabling Block Public Access, carefully inspect the following policies to confirm that they don’t grant public access:
Review Bucket Access Using IAM Access Analyzer for S3IAM Access Analyzer helps you identify the resources in your organization and accounts, such as Amazon S3 buckets or IAM roles, shared with an external entity. This lets you identify unintended access to your resources and data, which is a security risk. IAM Access Analyzer for S3 is available at no extra cost on the Amazon S3 console. IAM Access Analyzer for S3 is powered by AWS Identity and Access Management (IAM) IAM Access Analyzer. To use IAM Access Analyzer for S3 in the Amazon S3 console, you must visit the IAM console and enable IAM Access Analyzer on a per-Region basis. Enable Server-Side EncryptionAll Amazon S3 buckets have encryption configured by default, and all new objects that are uploaded to an S3 bucket are automatically encrypted at rest. Server-side encryption with Amazon S3 managed keys (SSE-S3) is the default encryption configuration for every bucket in Amazon S3. Amazon S3 also provides these server-side encryption options:
6 -The following diagram shows a reference architecture for synchronizing the security policy from ESA.
The Protegrity Policy Agent requires network access to an Enterprise Security Administrator (ESA). Most organizations install the ESA on-premise. Therefore, it is recommended that the Policy Agent is installed into a private subnet with a Cloud VPC using a NAT Gateway to enable this communication through a corporate firewall. The ESA is a soft appliance that must be pre-installed on a separate server. It is used to create and manage security policies. For more information about installing the ESA, and creating and managing policies, refer the Policy Management Guide. 7 -This guide describes how to configure the Protegrity Policy Agent and Log Forwarder to connect to a Protegrity Provisioned Cluster (PPC), highlighting the differences from connecting to ESA. Key Differences: PPC vs ESA
Prerequisites
Policy Agent Setup with PPCImportantWhen connecting to PPC, the Policy Agent requires thePTY_DATASTORE_KEY fingerprint. For ESA 10.2, the fingerprint is optional but recommended. See Policy Agent Installation for general setup steps.Follow these instructions as a guide for understanding specific inputs for Policy Agent integrating with PPC:
Log Forwarder Setup with PPCNoteWhen using PPC, certificate authentication and CA validation are not supported for the Log Forwarder. Configuration steps related to certificates in Log Forwarder Installation do not apply to PPC. If you attempt to use certificates provided by PPC, the Log Forwarder will not function correctly.
TroubleshootingProtector Lambda fails with “AWS KMS Decrypt failed”Symptom: After a successful Policy Agent run and layer update, the Protector Lambda returns: The Protector Lambda logs show: Cause: The public key configured in the PPC/ESA datastore does not match the KMS key pair used by the Policy Agent. The policy package is encrypted with the public key stored in the datastore. If that key does not correspond to the KMS key pair whose private key is used for decryption, the Protector Lambda will fail to decrypt the policy. Resolution:
ImportantAlways verify that the public key registered in the PPC/ESA datastore belongs to the same KMS key pair referenced by the Policy Agent. A mismatch between these keys is a common cause of The KMS key must be an asymmetric key with the Encrypt and decrypt key usage type. Symmetric keys or asymmetric keys configured for signing will not work. Additional Notes
8 -Create Protect Lambda IAM Execution PolicyThis task defines a policy used by the Protegrity Lambda function to write CloudWatch logs and access the KMS encryption key to decrypt the policy. Perform the following steps to create the Lambda execution role and required policies:
9 -Create Protect Lambda IAM RoleThe following steps create the role to utilize the policy defined in Create Protect Lambda IAM Execution Policy. To create protect lambda IAM execution role:
10 -Upgrading Policy Agent LambdaNoteIf the release version of the artifact zip file has not changed since the previous installation, you can skip the Agent Lambda upgrade.
NoteMake sure you are viewing the latest Lambda Function, not the published version.
11 -Upgrading Log Forwarder LambdaNoteIf you are upgrading protector to one of these versions: [3.2.2, 3.2.3], skip this section and follow instruction to install new Log Forwarder Audit Log Forwarder Installation.
12 -Upgrading Protect LambdaNoteIf the release version of the artifact zip file has not changed since the previous installation, you can skip the Protect Lambda upgrade.Diagram below illustrates upgrade steps.
13 -Re-enable Protegrity Agent Function CloudWatch Event RuleIf the Event Rule was disabled at the beginning of the upgrade process, you must re-enabled it. Follow the steps below to re-enable Policy Agent Event rule.
14 -Disable Protegrity Agent Function CloudWatch Event RuleCloud Watch Event Rule is used to periodically run Protegrity Agent Function to synchronize policy from ESA. This functionality is optional when deploying Protegrity Serverless Solution. If the Event Rule is enabled, it must be disabled temporarily for the time of the upgrade process. Follow the steps below to determine if your deployment uses Event Rule and disable it.
15 -Download the Latest VersionYou can download the latest version of the deployment package from https://my.protegrity.com. Navigate to Data Protection > Cloud Protect to download the latest version. After downloading the deployment package from the Protegrity Portal, unzip the package to extract the artifact files. In the AWS Console, navigate to the S3 bucket that was previously created to upload deployment artifacts (see: Create S3 bucket for Installing Artifacts). NoteOnly extract the deployment package and not the files in it.Upload the following artifacts to the S3 bucket: - -
If the release version matches your existing deployment, you don’t need to upload it again. Save the following artifacts on your local system so that you have them available during the next steps: - -
Perform the following steps to upgrade the Agent Lambda and Protect Lambda separately. ImportantIf new versions are available for both Agent and Protect Lambdas, Agent Lambda must be upgraded first. | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||