Protegrity Encryption
Encryption is the conversion of data into a ciphertext using an algorithmic scheme.
Encryption algorithms vary by input and output data types they support. Some preserve length, while others do not.
Table: Encryption Algorithms - Supported Length
*1 - All CUSP are length preserving as long as no CRC or Key ID is configured.
Encryption Algorithms for Protectors
Application Protector
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Application Protectors
*1 - If the input and output types of the API are BYTE [], the customer application should convert the input to a byte array. Then, call the API and convert the output from the byte array.
*2 - The output type is BYTE[] only. The input type String or Char is supported with the API that provides BYTE[] output type.
*3 - You must pass the encrypt_to=bytes keyword argument to the AP Python protect API for encrypting data. However, if you are encrypting or re-encrypting data already in bytes format, you do not need to pass the encrypt_to=bytes argument to the protect and reprotect APIs.
Big Data Protector
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Big Data Protectors
*1 - The customer application should convert the input to and output from byte array.
*2 - The input type STRING is supported with the API that provides the BYTE[] output type.
*3 - The string encryption UDFs for Hive and SparkSQL are limited to accept 2 GB data size at maximum as input. Ensure that the file size for the protected binary data after the required encoding does not exceed the 2 GB input limit.
*4 - The input type VARCHAR is supported by AES-128 and AES-256.
Data Warehouse Protector
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Data Warehouse Protectors
Database Protector
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Database Protectors
1 - Encryption Algorithms
An encryption algorithm is a process to convert data into ciphertext.
1.1 - AES-128 and AES-256
List details about AES-128 and AES-256 encryption algorithms.
The Protegrity solutions work with AES-128 and AES-256 encryption algorithms. The Advanced Encryption Standard (AES) is an encryption algorithm for electronic data that was established by the U.S. National Institute of Standards and Technology (NIST) in 2001.
AES is based on a substitution-permutation network design principle, and is fast in both software and hardware.
AES is used in three versions, such as, AES-128, AES-192, and AES-256. These numbers represent the encryption key sizes, 128 bits, 192 bits, and 256 bits. The number of rounds based on the encryption key sizes are 10, 12, and 14 respectively.
AES-128 and AES-256
AES-128 is a version of AES encryption algorithm that has a fixed block size of 16 bytes and a key size of 128 bit. AES-256 is a version of AES encryption algorithm that has a fixed block size of 16 bytes and a key size of 256 bit.
Table: AES-128 and AES-256 Encryption Algorithm Properties
| Properties | Values |
|---|
| Name | AES-128
AES-256 |
| Operation Mode | CBC – Cipher Block Chaining |
| Encryption Properties | IV, CRC, Key ID |
| Length Preservation with padding formula for non-length preserving algorithms | No
For explanation on calculating data length, refer to the section Data Length and Padding in Encryption. |
| Minimum Length | None |
| Maximum Length | 2147483610 bytes |
| Specifics of algorithm | AES-128 - A block cipher with 128 bit key
AES-256 - A block cipher with 256 bit key |
The table shows examples of the way in which the value “Protegrity” will be encrypted with the AES-128 and AES-256 encryption algorithm.
Table: Examples of AES-128 and AES-256 Encryption
| Encryption Algorithm | Output Value | Comments |
|---|
| AES-128 | 0xA2EA9C9BC53D77BA7F8E85C124296BF3 | The input value, which is 10 bytes long, is padded to become 16 bytes. This represents one block of 16 bytes. The output value consists of 16 bytes. |
| AES-128-CRC | 0x86315F21FA70F7AC1A7D9DB04B22C87A | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to become 16 bytes. This represents one block of 16 bytes. The output value consists of 16 bytes. |
| AES-128-IV | 0x0560F196024CCD1CD8213C6657B1BB58CE3047C316EC300BB0BF3C3F5949C157 | 16 bytes IV is added. The output value consists of 32 bytes. This represents two blocks of 16 bytes. |
| AES-128-KeyID | 0x2002E3DE3D7AB6CCBEB96A6A60248559C094 | 2 bytes are added for the Key ID. The output value consists of 18 bytes. |
| AES-128-IV-CRC-KeyID | 0x20031F55A327AFD11DA9E0FEA2499484825E2EABC2B28D162737E867BE0726E7131F | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to a total length of 16 bytes. Additionally, 16 bytes IV and 2 bytes of Key ID are added to the output. The final output value consists of 34 bytes. |
| AES-256 | 0x0A4771DAD552DA29512BE13BCCF2538A | The input value, which is 10 bytes long, is padded to become 16 bytes. This represents one block of 16 bytes. The output value consists of 16 bytes. |
| AES-256-CRC | 0x29445B1AEED293D341E9634BD7B7BA4C | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to become 16 bytes. This represents one block of 16 bytes. The output value consists of 16 bytes. |
| AES-256-IV | 0x2C9D5D8AF80C4614F2C6D063A94BB624C19B14EB40C919F7053DA636ACAE3BEE | 16 bytes IV is added. The output value consists of 32 bytes. This represents two blocks of 16 bytes. |
| AES-256-KeyID | 0x20157C0E98A1C9E4E6F4D1DCB6FE72B2DA69 | 2 bytes are added for the Key ID. The output value consists of 18 bytes. |
| AES-256-IV-CRC-KeyID | 0x200AA6570EBA6A866F985839C4C189038705C6FC48B2459650940904E76009E300D2 | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to a total length of 16 bytes. Additionally, 16 bytes IV and 2 bytes of Key ID are added to the output. The final output value consists of 34 bytes. |
AES-128 and AES-256 Encryption Properties for Protectors
The Application Protector, Big Data Protector, and Database Protector can use AES-128 and AES-256 encryption algorithms.
All protectors support encryption properties, such as, IV, CRC, and Key ID. The Key ID is a part of the encrypted data.
The AES-128 and AES-256 encryption algorithms can also be used with File Protectors.
For the protect operation, the Input type / Character set can be any value depending upon the DB, then the Output type / Character set is Binary.
For the unprotect operation, the Input type / Character set is binary and the Output type / Character set can be any value depending upon the DB.
Application Protector
For the Input type / Character set property, refer to Supported Input Data Types by Application Protectors for supported data types.
Big Data Protector
For the Input type / Character set property, refer to Supported Input Data Types by Big Data Protectors for supported data types.
1.2 - CUSP
List details about CUSP encryption algorithm.
Protegrity supports CUSP encryption. Cryptographic Unit Service Provider (CUSP) is used for handling data with length that is not a multiple of the key block length. It is often used when you want to maintain the original length of the data. The length of encrypted data in CUSP mode will always equal the length of clear text data.
CUSP is best suited for varying types of environments and usage scenarios. For very small-sized data, encrypting with a stream cipher such as CUSP could result in reduced security because it may not include an initialization vector (IV). CUSP is appropriate if the data is greater than one block in size. Larger amounts of data encrypted with CUSP are secure because the CUSP algorithm uses standard chaining block ciphering for the cipher block size pieces of data. For the final data piece less than a cipher block, the CUSP algorithm uses a generated IV only.
The CUSP mode of encryption is not certified by NIST. It is therefore not a part of the NIST standards, or of any other generally accepted body of standards, and has not been formally reviewed by the cryptographic community. Therefore, the use of CUSP mode would be outside the scope of most data security regulations.
Protegrity supports three types of CUSP encryption: CUSP 3DES, CUSP AES-128, and CUSP AES-256.
CUSP AES-128 and CUSP AES-256
CUSP AES-128 and CUSP AES-256 CBC encrypt data in 16 byte blocks using AES key. Any remaining data is ciphered using the same AES key. The IV for this encryption is derived from the double encrypted last full block. AES-128 uses a 128 bit key and AES-256 uses a 256 bit key.
Table: CUSP Encryption Algorithm Properties
| Properties | Values |
|---|
| Name | CUSP AES-128
CUSP AES-256 |
| Operation Mode | CBC – Cipher Block Chaining, combined with ECB - Electronic codebook |
| Encryption Properties | CRC, Key ID |
| Length Preservation with padding formula for non-length preserving algorithms | Yes
No, if CRC or Key ID are used. |
| Minimum Length | None |
| Maximum Length | 2147483610 bytes (2 GB) |
| Specifics of algorithm | A modified block algorithm mainly used in environments where an IBM mainframe is present. |
The following table shows examples of the way in which the value “Protegrity” will be encrypted with the CUSP algorithm.
Table: Examples of CUSP Encryption
| Encryption Algorithm | Output Value |
|---|
| CUSP AES-128 | 0x1D95BEFC71590AA7B5C3 |
| CUSP AES-256 | 0x1C7244BB85827D36435D |
CUSP Encryption Properties for Protectors
The Application Protector, Big Data Protector, and Database Protector can use CUSP encryption algorithm.
For the protect operation, the Input type / Character set can be any value depending upon the DB, then the Output type / Character set is Binary.
For the unprotect operation, the Input type / Character set is binary and the Output type / Character set can be any value depending upon the DB.
Application Protector
For the Input type / Character set property -
Big Data Protector
For the Input type / Character set property, refer to Supported Input Data Types by Big Data Protectors for supported data types.
1.3 - 3DES
List details about 3DES encryption algorithm.
Deprecated
Starting from v10.0.x, the 3DES protection method is deprecated based on NIST recommendations around weak ciphers.
It is recommended to use the AES-128 and AES-256 protection method instead of the 3DES protection method.
The 3DES algorithm applies the DES algorithm. It is the first USA national standard of block ciphering, three times to each data block.
The Triple Data Encryption Standard (3DES) cipher key size is 168 bits, compared to 56 bits key of DES. The 3DES algorithm, using the DES cipher algorithm, provides a simple method of data protection.
Table: 3DES Encryption Algorithm Properties
| Properties | Values |
|---|
| Name | 3DES |
| Operation Mode | EDE3 CBC - triple CBC DES encryption with three keys.
- CBC = Cipher Block Chaining
- EDE = E(ks3,D(ks2,E(ks1,M)))
- E=Encrypt
- D=Decrypt |
| Encryption Properties | IV, CRC, Key ID |
| Length Preservation with padding formula for non-length preserving algorithms | No
For explanation on calculating data length, refer to Data Length and Padding in Encryption. |
| Minimum Length | None |
| Maximum Length | 2147483610 bytes (2 GB) |
| Specifics of algorithm | A block cipher with 168 bit key |
The following table shows examples of the way in which the value “Protegrity” will be encrypted with the 3DES algorithm.
Table: Examples of 3DES Encryption
| Encryption Algorithm | Output Value | Comments |
|---|
| 3DES | 0x4AA7402C77808D80D093A15A51318D19 | The input value, which is 10 bytes long, is padded to become 16 bytes. This represents two blocks of 8 bytes. The output value consists of 16 bytes. |
| 3DES-CRC | 0xF1B7EFD118D27E5568AB192CE2A12E35 | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to become 16 bytes. This represents two blocks of 8 bytes. The output value consists of 16 bytes. |
| 3DES-IV | 0x5126D8EB02A213922FB7E6DEDA861ABF661A01AEF7CAEC86 | 8 bytes IV is added. The output value consists of 24 bytes. This represents three blocks of 8 bytes. |
| 3DES-KeyID | 0x200479E1CC7983040987362DA49DD68B6E16 | 2 bytes are added for the Key ID. The output value consists of 18 bytes. |
| 3DES-IV-CRC-KeyID | 0x20055B72BF6E9B55B799A9DF51587E93ED8CF42E48A80F9474C0 | The input value, which is 10 bytes long with a checksum of 4 bytes, is padded to a total length of 16 bytes. Additionally, 8 bytes IV and 2 bytes of Key ID are added to the output. The final output value consists of 26 bytes. |
CUSP 3DES
Deprecated
Starting from v10.0.x, the CUSP 3DES protection method is deprecated based on NIST recommendations around weak ciphers.
It is recommended to use the CUSP AES-128 and CUSP AES-256 protection method instead of the CUSP 3DES protection method.
CUSP 3DES uses a 3DES key with the CUSP expansion to the 3DES algorithm. Data is CBC encrypted in 8 byte blocks. Any remaining data is stream ciphered using the same 3DES key with an IV of a double encrypted last full block.
Table: CUSP 3DES Encryption Algorithm Properties
| Properties | Values |
|---|
| Name |
CUSP 3DES |
| Operation Mode | CBC – Cipher Block Chaining, combined with ECB - Electronic codebook |
| Encryption Properties | CRC, Key ID |
| Length Preservation with padding formula for non-length preserving algorithms | Yes
No, if CRC or Key ID are used. |
| Minimum Length | None |
| Maximum Length | 2147483610 bytes (2 GB) |
| Specifics of algorithm | A modified block algorithm mainly used in environments where an IBM mainframe is present. |
The following table shows examples of the way in which the value “Protegrity” will be encrypted with the CUSP 3DES algorithm.
| Encryption Algorithm | Output Value | Comments |
|---|
| CUSP 3DES | 0xD7DE903612B29BA825B4 | Length of the output value is the same as input value - 10 bytes as CUSP preserves length. |
| CUSP 3DES - CRC | 0x7920A9AF0CEE96E1C4EDB8F5E9EF | 4 bytes checksum is added. The output value consists of 14 bytes. |
| CUSP 3DES - KeyID | 0x200525200D62B05DCB17E8DB | 2 bytes Key ID is added. The output value consists of 12 bytes. |
| CUSP 3DES - CRC-KeyID | 0x20068C2A54ACB80DB3C3332421B8851B | 4 bytes checksum and 2 bytes of Key ID are added. The output value consists of 16 bytes. |
3DES Encryption Properties for Protectors
The Application Protector, Big Data Protector, and Database Protector can use 3DES encryption algorithm.
All protectors support encryption properties, such as, IV, CRC, and Key ID. The Key ID is a part of the encrypted data.
The 3DES encryption algorithm can also be used with File Protectors.
For the protect operation, the Input type / Character set can be any value depending upon the DB, then the Output type / Character set is Binary.
For the unprotect operation, the Input type / Character set is binary and the Output type / Character set can be any value depending upon the DB.
Application Protector
For the Input type / Character set property, refer to Supported Input Data Types by Application Protectors for supported data types.
Big Data Protector
For the Input type / Character set property, refer to Supported Input Data Types by Big Data Protectors for supported data types.
2 - Encryption Properties - IV, CRC, Key ID
List details about Encryption properties.
The encryption properties include Initialization Vector (IV), Integrity Check (CRC), and Key ID.
For encrypting Unstructured Data using File Protector, you can enable the Key ID property in the encryption data element to be used with unstructured policy.
The following table describes encryption properties.
Table: Encryption Properties
| Feature | Description |
|---|
| Initialization Vector (IV) | Encrypting the same value with the IV property will result in different crypto text for the same value. |
| Integrity Check (CRC) | A type of function that takes as input a data stream of any length and produces as output a value of a certain fixed size.
A CRC can be used as a checksum to detect alteration of data during transmission or storage. |
| Key ID | A Key ID is an identifier that associates encrypted data with the protection method so that the data can be decrypted regardless of where it ultimately resides.
A data element can have multiple instances of key IDs associated with it.
When the Key ID property is turned on there will be an extra 2 bytes in the beginning of the cipher text. This piece of information contains the reference to the Key ID that was used to produce the cipher text.
Caution: It is recommended not to create a large number of keys. All Data Encryption Keys (DEKs) are generated and decrypted using the configured Key Store. This process might take some time and incur costs. |
Key IDs
Key IDs are a way to correlate a data element key with its encrypted data. Data elements can have multiple key IDs associated with them. The Key IDs facilitate tasks related to the management of sensitive data such as archiving and key rotation. It is important to note that you can create a maximum number of 8191 keys.
Caution: It is recommended not to create a large number of keys. All Data Encryption Keys (DEKs) are generated and decrypted using the configured Key Store. This process might take some time and incur costs.
The following table describes the key ID states.
Table: Key ID States
| Feature | Description |
|---|
| Pre-Active | The initial state of a key that is created by the Create Key option. |
| Active | A key becomes Active once it is distributed to a protector by deploying the data security policy. |
| Deactivated | An Active key becomes automatically Deactivated when the data security policy is redeployed with a new Pre-Active key. |
For more information about key ID states, refer to Working with Keys.
Table: Examples of Encryption Properties for AES-256 algorithm (initial value is “Protegrity”)
| Encryption Property | Encrypted Values | Comments |
|---|
| AES-256-IV | 0x1361D69E18A692507895780C2FB26DD7869979CC1BB6612A994B5EA5585FCF0B
0xE2D579E937EE92C67167749151B30809A538CC6A6871B8D9B0C17FBA6F1A8D94 | Encrypting the same value with the IV property resulted in different output values. Decrypt will be performed correctly for both values. |
| AES-256-CRC | 0x7A0C701B4B30E6BF141196FE44F125BD
0x3964DD0ACAF5B39D159BE7518B46D84A8DCC0B62F2183B3888FEF82B65C7F87D | The first value is a result of encryption of “Protegrity1” along with a CRC checksum of 4-bytes. The resulting input is 15-bytes which fit a single AES block. The second value is a result of encryption of “Protegrity12” along with a CRC checksum of 4-bytes. The resulting input is 16-bytes which requires two AES blocks. |
| AES-256-KeyID | 0x200936F85C3BD86F008A57C3DF33F200BC42
0x20157C0E98A1C9E4E6F4D1DCB6FE72B2DA69 | Key ID of the first value equals to 9 (0x2009 in HEX), key ID of the second value equals to 21 (0x2015 in HEX). |
Key IDs in Protectors
For all protectors, the Key IDs can only be used with data elements that use AES, CUSP, or 3DES algorithms. The Key ID is included in the encrypted value.
For more information on the format of encrypted data, refer to Data Length and Padding in Encryption.
3 - Data Length and Padding in Encryption
Data length and padding in encryption refers to the padding used to fill the blocks of data with padding bytes in a block cipher.
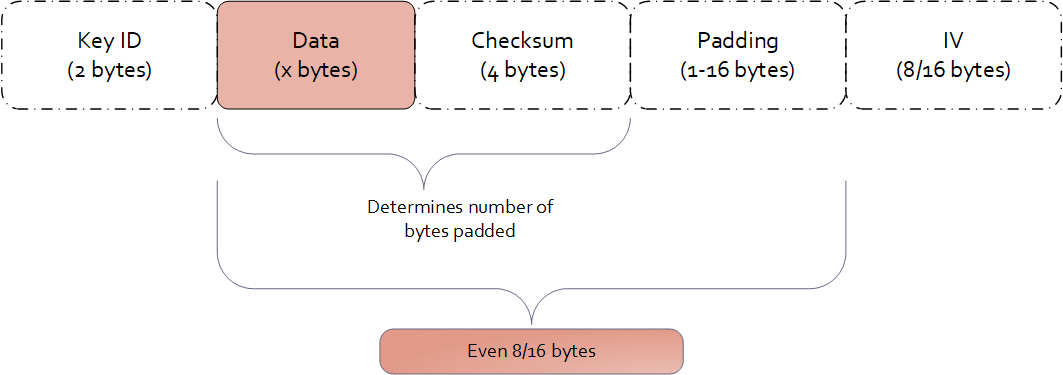
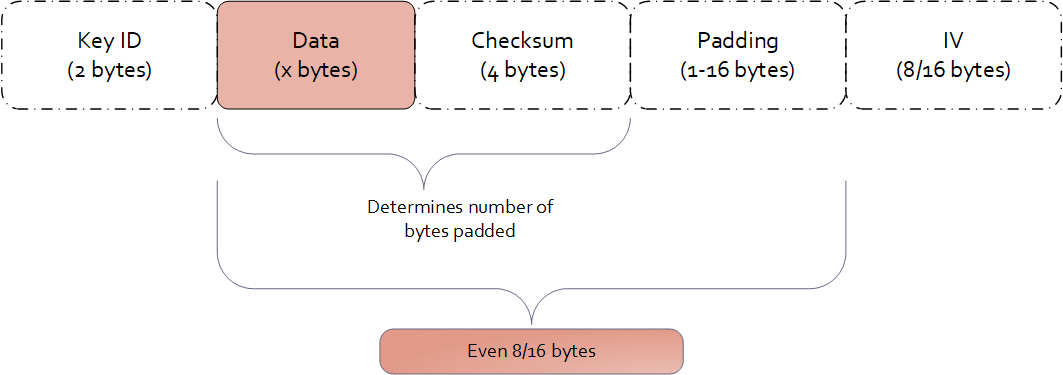
Cipher text are formatted in a specific way depending on which encryption properties are being used.
The block ciphers operate on blocks of data. These encryption algorithms require padding. The block size for AES is 16 bytes, and for 3DES it is 8 bytes. The input is always padded, even if it is already a multiple of the block size. Padding ensures that the input data, along with the checksum, if enabled, equals the algorithm’s block size.
Ciphertext Format
Ciphertext format uses an encryption algorithm to convert the plaintext into encrypted text. The length of an encrypted value for a non-length-preserving encryption method, such as 3DES, AES-128, or AES-256, depends on the block size and the length of the input data. The encryption properties used, including Key ID, CRC, and IV also influence the encrypted value’s length.
Examples of data length calculation by column types are provided in Examples of Column Sizes Calculation for Encryption.
4 -
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Database Protectors
5 -
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Data Warehouse Protectors
6 -
The Protegrity solutions can encode data with the following encryption algorithms:
Table: Input Data Types Supported by Application Protectors
*1 - If the input and output types of the API are BYTE [], the customer application should convert the input to a byte array. Then, call the API and convert the output from the byte array.
*2 - The output type is BYTE[] only. The input type String or Char is supported with the API that provides BYTE[] output type.
*3 - You must pass the encrypt_to=bytes keyword argument to the AP Python protect API for encrypting data. However, if you are encrypting or re-encrypting data already in bytes format, you do not need to pass the encrypt_to=bytes argument to the protect and reprotect APIs.