Understanding the Teradata Architecture
The architecture for the Teradata distribution of the Data Warehouse Protector is depicted in the image below.
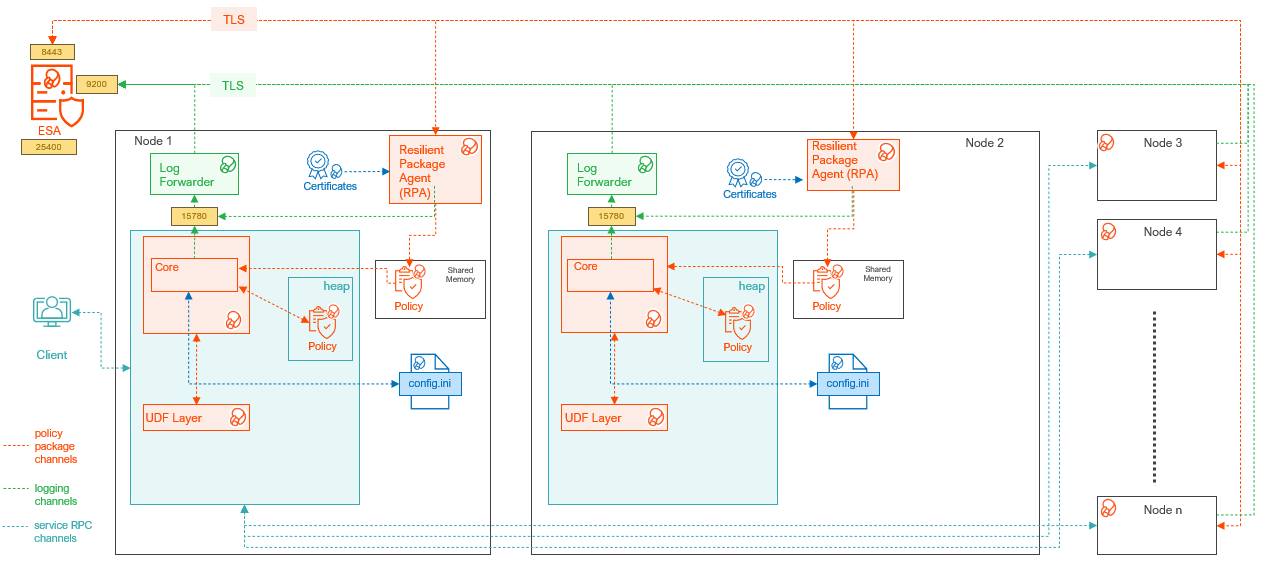
| Component Name | Description |
|---|---|
| Access Module Processor | Stores and retrieves all the protector data. It is also called as the Virtual Processor (vproc). |
| config.ini | Contains the set of configuration parameters to modify the protector behavior. |
| Core | Is the set of various libraries that provide the Protegrity Core functionality. |
| Log Forwarder | Forwards the protector logs to Insight. |
| Node | Serves as a central processing unit where the database operations are executed using a single operating system. |
| Resilient Package (RP) Agent | Is a daemon running on each node that downloads the Policy from the ESA over a TLS channel using the installed Certificates. |
| UDF Layer | Contains the Data Warehouse Protector UDFs and APIs executing in the Teradata service process. |
Feedback
Was this page helpful?